Seven bugs.
-
Seven bugs. One unauthenticated RCE chain. Zero clicks.
This original research by our offensive security team into FuelCMS (v1.5.2) uncovered seven new vulnerabilities. By chaining some of them, we achieved Remote Code Execution (RCE).
The root causes? A *12-year-old Dwoo templating engine* and *outdated CodeIgniter3 code* still lurking in production systems.
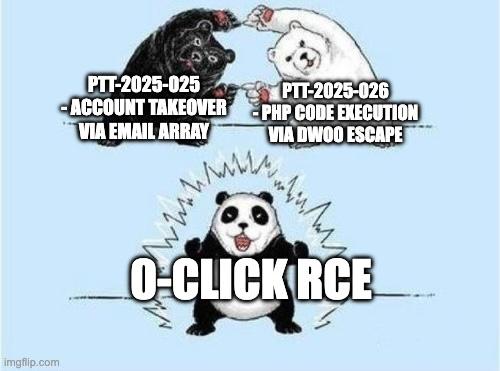
The exploit chain combines:
 Account takeover (PTT-2025-025): reset password tokens leaked by sending them to the attacker's inbox
Account takeover (PTT-2025-025): reset password tokens leaked by sending them to the attacker's inbox SQL injection (PTT-2025-030): usernames extracted during password reset (optional step)
SQL injection (PTT-2025-030): usernames extracted during password reset (optional step) PHP code execution (PTT-2025-026): unsanitized backslashes in the Dwoo parser resulting in RAW PHP CODE EXECUTION
PHP code execution (PTT-2025-026): unsanitized backslashes in the Dwoo parser resulting in RAW PHP CODE EXECUTIONResult: full web app compromise.
We published the full exploit chain on our blogpost so practitioners can reproduce and validate the findings. Read the detailed research here: https://pentest-tools.com/blog/throwing-a-spark-in-fuelcms
Many thanks to Matei Badanoiu, Raul Bledea and Eusebiu Boghici for their contributions.
#offensivesecurity #vulnerabilityresearch #pentesting #infosec
Out of curiosity: how often do you still run into 10+ year-old libraries during engagements?
-
R relay@relay.infosec.exchange shared this topic
