We just launched the Offensive Security Research Hub on Pentest-Tools.com!This isn’t a CVE recap page.Our #offensivesecurity team - led by Matei Badanoiu (CVE Jesus) - publishes original research: newly discovered vulnerabilities, deep technical write-ups, and full exploit chains built from real-world investigation.You’ll see:️ Working PoCs and reproducible exploit paths🧠 The exact reasoning that turned strange behavior into confirmed impact️ Field-tested analysis of edge cases, constraints, and trade-offsNo summaries. No recycled advisories.This is practitioner-grade research from people who _actively_ hunt and validate vulnerabilities.If you want to understand how experienced attackers approach complex targets, start here.Bookmark this link, we're going to update it frequently with new learnings: https://pentest-tools.com/research#vulnerabilityresearch #ethicalhacking #infosec
 1
0 Votes1 Posts0 Views
1
0 Votes1 Posts0 Views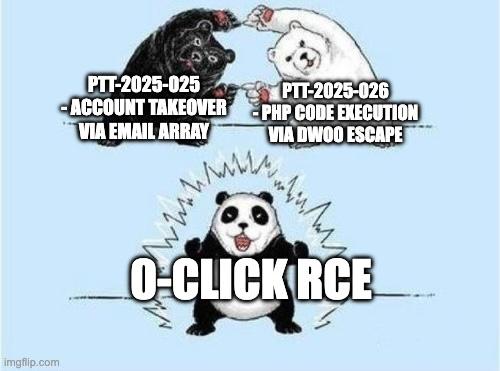 1
0 Votes1 Posts2 Views
1
0 Votes1 Posts2 Views 1
0 Votes1 Posts3 Views
1
0 Votes1 Posts3 Views