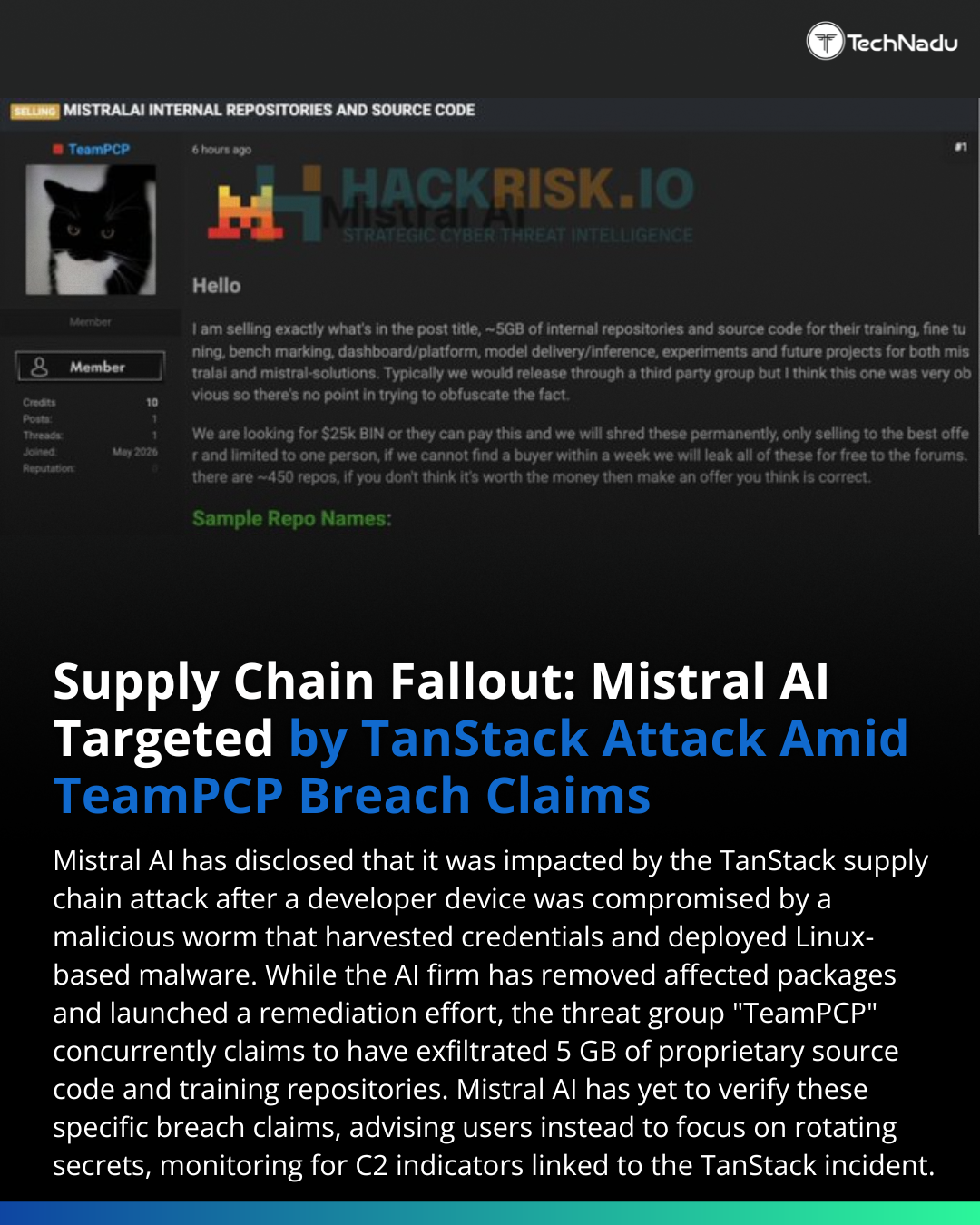
Security News Digest - 2026-05-14 5 updates from 4 sources: BleepingComputer: Cyber-Enabled Cargo Crime: How Cybercrime Tradecraft is Used to Steal Freight https://www.bleepingcomputer.com/news/security/cyber-enabled-cargo-crime-how-cybercrime-tradecraft-is-used-to-steal-freight/ BleepingComputer: 18-year-old NGINX vulnerability allows DoS, potential RCE https://www.bleepingcomputer.com/news/security/18-year-old-nginx-vulnerability-allows-dos-potential-rce/ The Hacker News: ThreatsDay Bulletin: PAN-OS RCE, Mythos cURL Bug, AI Tokenizer Attacks, and 10+ Stories https://thehackernews.com/2026/05/threatsday-bulletin-pan-os-rce-mythos.html Security News | TechCrunch: OpenAI says hackers stole some data after latest code security issue https://techcrunch.com/2026/05/14/openai-says-hackers-stole-some-data-after-latest-code-security-issue/ darkreading: 'FrostyNeighbor' APT Carefully Targets Govt Orgs in Poland, Ukraine https://www.darkreading.com/cyberattacks-data-breaches/frostyneighbor-apt-govt-orgs-poland-ukraine#InfoSec #SecurityNews
 1
1
 1
1
 1
1
 1
1
 1
1
 1
1
 1
1
 1
1
 1
1


