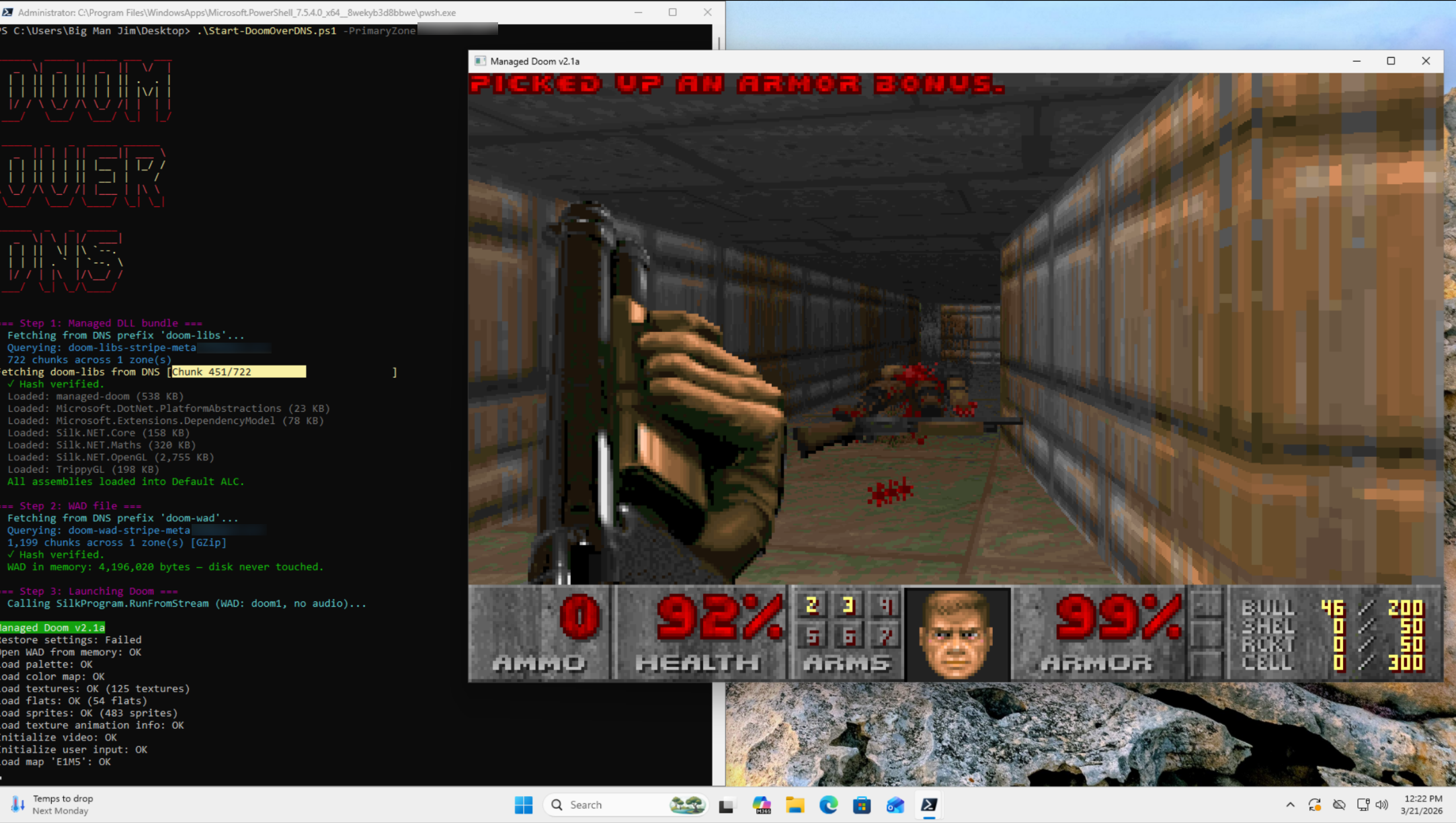
In today's episode of "Can It Run Doom": DNS fucking TXT records.
-
@onedawnconstant @da_667 @DaveMWilburn @k3ym0
Home routers can't (directly (usually)) cause a failure that blows up a gas pipeline, drop a grid, or simply quit monitoring the particulate ratio at the top of a grain silo.
@johntimaeus @da_667 @DaveMWilburn @k3ym0
Not directly, but 300 of them in the default configuration can easily allow for infrastructure attacks through botnets, spearphishing, etc. Smear that stuff around and somethings bound to go wrong.
Someone always has something they shouldn't, and that's how stuff croaks.
-
@DaveMWilburn @k3ym0 I'm well aware that trying to base your detection on shannon entropy is an exercise in futility, as most cloud providers have the "malware to ops DGA that looks like its very malicious" down pat. But I will still say, if you suddenly are getting assloads of TXT records with the same domain in common, so long as you have DNS logs at all, you can probably do some form of statistical analysis and notice that this number of DNS TXT records from one place looks really fucking jank.
@da_667 @DaveMWilburn @k3ym0 If I wanted to avoid detection, I’d send the information in AAAA records, not TXT.
-
R relay@relay.infosec.exchange shared this topic