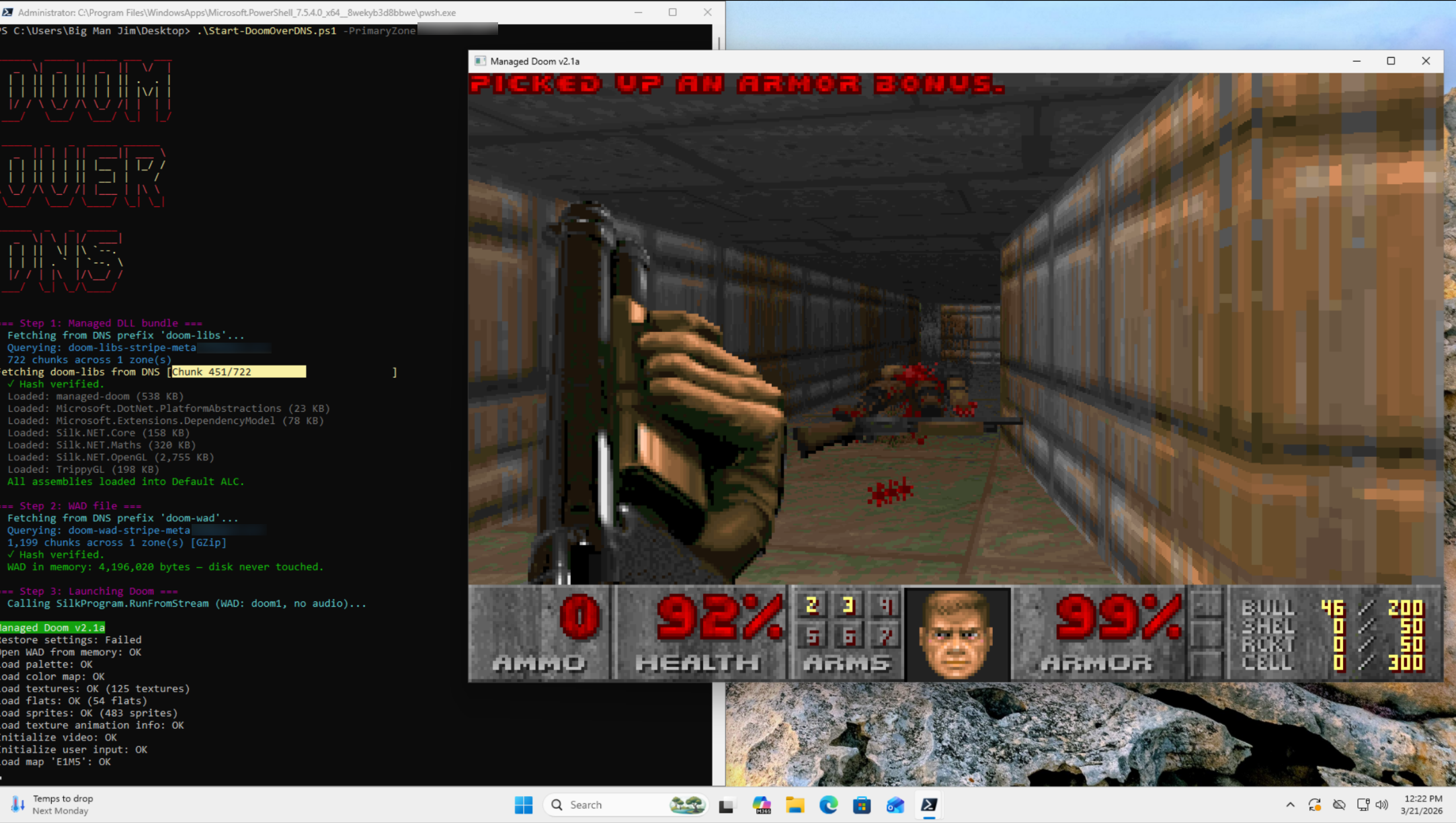
In today's episode of "Can It Run Doom": DNS fucking TXT records.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 holy shit that is next level 'because I could'. Mad props.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0@infosec.exchange
Ho. Lee. Shit
Was it already encoded in morse code?
This clearly HAD to be done, but not by anyone i know. -
Most serious companies don't allow DNS queries to servers outside of their network.
Oh my sweet, sweet, child. If only this were true. I could name-drop several multi-billion $ enterprise orgs that still don’t do this.
-
@DaveMWilburn @k3ym0 I'm also somewhat aware that, there are some services that use TXT records for validation (SPF), and I've heard that some apple services use them for their messenger programs. I've also seen Sophos doing incredibly dumb things with TXT records, but my point still stands is that if you have any capacity for DNS logs, then shit like this sticks out like a sore thumb.
However, I can acknowledge my experiences and yours are two different things. Thats fine. I can be wrong.
DNS logs, a well built forwarding chain, and a properly tuned dashboard will trigger on this in a few hundreds of milliseconds.
But how many enterprises have that? We're still trying to convince people that naked RDP on the Internet is a bad idea, and that industrial control systems shouldn't ship with open telnet and default creds.
-
DNS logs, a well built forwarding chain, and a properly tuned dashboard will trigger on this in a few hundreds of milliseconds.
But how many enterprises have that? We're still trying to convince people that naked RDP on the Internet is a bad idea, and that industrial control systems shouldn't ship with open telnet and default creds.
-
DNS logs, a well built forwarding chain, and a properly tuned dashboard will trigger on this in a few hundreds of milliseconds.
But how many enterprises have that? We're still trying to convince people that naked RDP on the Internet is a bad idea, and that industrial control systems shouldn't ship with open telnet and default creds.
@johntimaeus @da_667 @DaveMWilburn @k3ym0
Industrial controls? They're still shipping household routers with open telnet. Thanks, TP-Link! -
@johntimaeus @da_667 @DaveMWilburn @k3ym0
Industrial controls? They're still shipping household routers with open telnet. Thanks, TP-Link!@onedawnconstant @johntimaeus @DaveMWilburn @k3ym0 ONE DAY, LONG AFTER I PASS, THEY WILL SUMMON ME WITH A D-LINK ROUTER AND CHILI FRIES WITH MUSTARD IN A SUMMONING CIRCLE. I WILL RUN IOT_HUNTER ONCE, AND GO BACK TO CRYPT-SLEEP.
-
@johntimaeus @da_667 @DaveMWilburn @k3ym0
Industrial controls? They're still shipping household routers with open telnet. Thanks, TP-Link!@onedawnconstant @da_667 @DaveMWilburn @k3ym0
Home routers can't (directly (usually)) cause a failure that blows up a gas pipeline, drop a grid, or simply quit monitoring the particulate ratio at the top of a grain silo.
-
@onedawnconstant @da_667 @DaveMWilburn @k3ym0
Home routers can't (directly (usually)) cause a failure that blows up a gas pipeline, drop a grid, or simply quit monitoring the particulate ratio at the top of a grain silo.
@johntimaeus @da_667 @DaveMWilburn @k3ym0
Not directly, but 300 of them in the default configuration can easily allow for infrastructure attacks through botnets, spearphishing, etc. Smear that stuff around and somethings bound to go wrong.
Someone always has something they shouldn't, and that's how stuff croaks.
-
@DaveMWilburn @k3ym0 I'm well aware that trying to base your detection on shannon entropy is an exercise in futility, as most cloud providers have the "malware to ops DGA that looks like its very malicious" down pat. But I will still say, if you suddenly are getting assloads of TXT records with the same domain in common, so long as you have DNS logs at all, you can probably do some form of statistical analysis and notice that this number of DNS TXT records from one place looks really fucking jank.
@da_667 @DaveMWilburn @k3ym0 If I wanted to avoid detection, I’d send the information in AAAA records, not TXT.
-
R relay@relay.infosec.exchange shared this topic