-
(socket.dev) Large-Scale npm Supply Chain Attack Targets TanStack Packages with Credential-Stealing Malware
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
🛡 THREAT INTEL | https://sibillacapital.com/
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized darkweb databreach threatintel cybersecurity infosec0 Votes1 Posts0 Views -
(bishopfox.com) Confused Deputy Attacks in AI Agents: Mechanics, Case Studies, and Layered Mitigations
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
(medium.com) From Image Trading to Sextortion: How Minor Communities Become Entry Points for Child Exploitation
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
(akamai.com) Akamai Mitigates Local Privilege Escalation Vulnerability in Guardicore Platform Agent for macOS and Linux
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
Threat Intelligence people who follow this type of thing:How creditable is 313 Team in your experience
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity 313team iran threatintel0 Votes2 Posts0 Views -
(malwarebytes.com) Security Risks of Browser Password Managers: Why Microsoft Edge's Design Raises Concerns
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
🛡 THREAT INTEL | Soprolux
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized darkweb databreach threatintel cybersecurity infosec0 Votes1 Posts0 Views -
🚨 New security advisory:
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cve zeroday threatintel0 Votes1 Posts0 Views -
(socket.dev) Critical Sandbox Escape Vulnerability in vm2 JavaScript Library Exposes Node.js Applications to Arbitrary Command Execution
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
(huntress.com) Threat Actors Exploit Tiflux RMM in Phishing Campaigns for Stealthy Persistence and Privilege Escalation
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
(wordfence.com) Weekly WordPress Vulnerability Report: Analysis of 87 Newly Disclosed Plugin and Theme Vulnerabilities
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
We want to see urlDNA in more tools.
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized urldna cti infosec threatintel secops0 Votes1 Posts0 Views -
(pushsecurity.com) Inside the Phishing Panels: How ShinyHunters and BlackFile Operators Leverage Real-Time Vishing and AITM Attacks
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
⚠️ 🎣 We’re seeing an ongoing phishing campaign targeting hotels and hosts, impersonating messages from 'Booking.com' - see sample image below.
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity phishing threatintel infosec bookingcom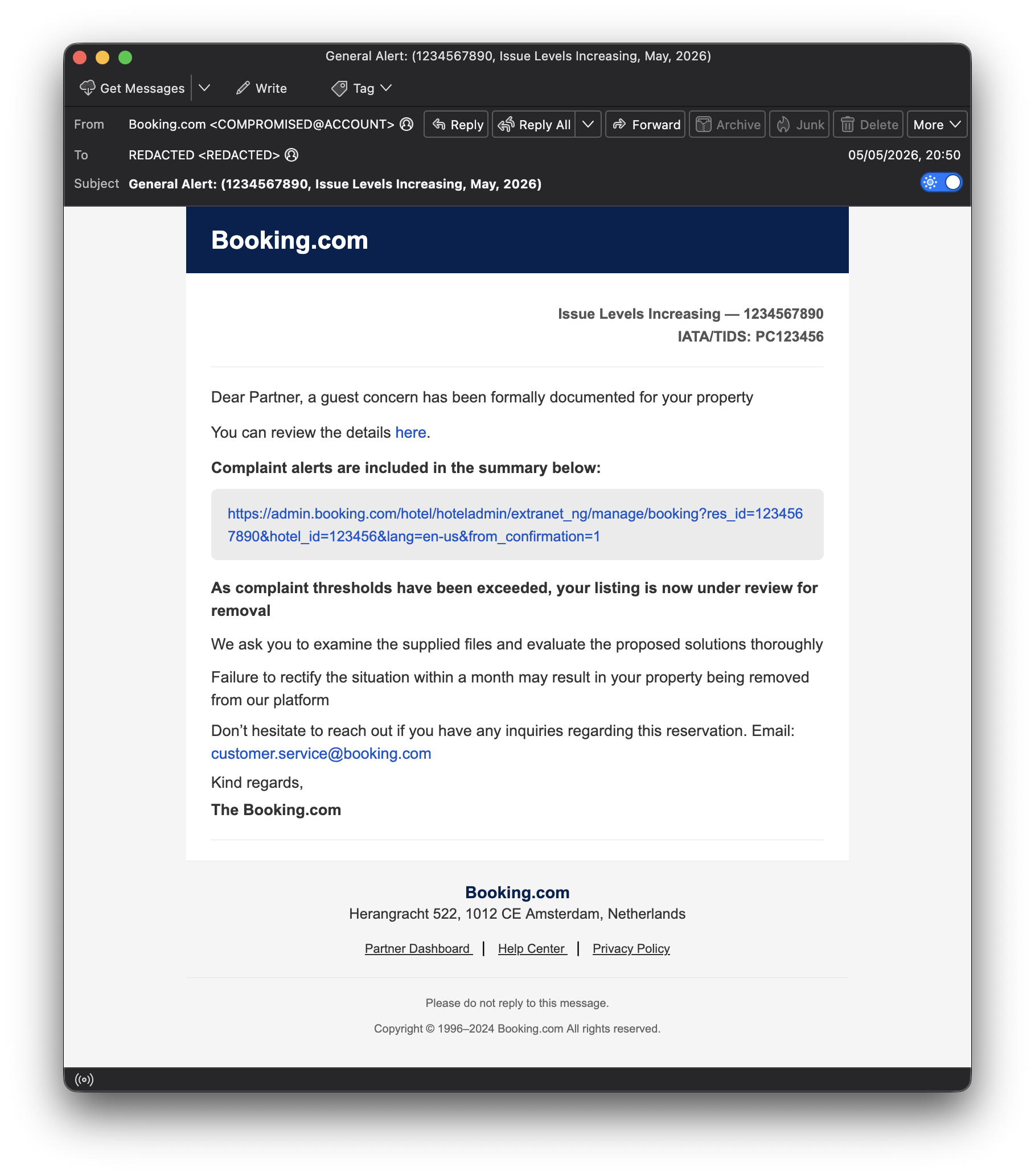 1
0 Votes1 Posts0 Views
1
0 Votes1 Posts0 Views -
(hackerone.com) Exposure Debt: The Growing Gap Between Vulnerability Discovery and Remediation in the AI Era
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
Another AI service that's dangerous when exposed to the internet?
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cve threatintel threatintellige ifin0 Votes2 Posts2 Views -
(wordfence.com) Critical Authenticated Arbitrary File Upload Vulnerability Patched in Slider Revolution WordPress Plugin
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
(microsoft.com) Evolution of ClickFix: How Threat Actors Exploit macOS Terminal Commands to Distribute Infostealers
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized cybersecurity threatintel0 Votes1 Posts0 Views -
New.
Watching Ignoring Scheduled Pinned Locked Moved Uncategorized infoec threatintel threatintellige0 Votes1 Posts0 Views
