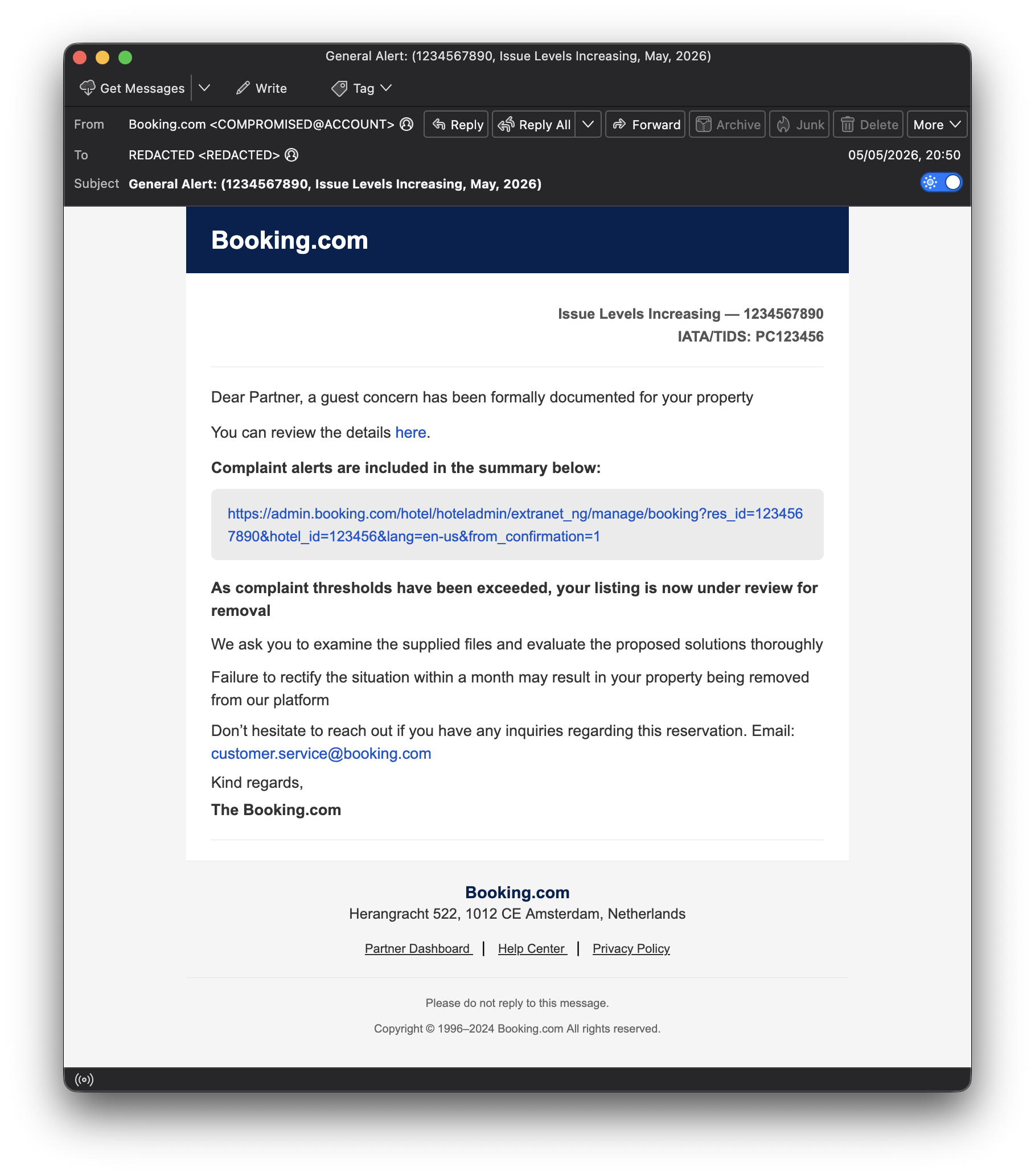
⚠️ 🎣 We’re seeing an ongoing phishing campaign targeting hotels and hosts, impersonating messages from 'Booking.com' - see sample image below.
-
 ️
️  We’re seeing an ongoing phishing campaign targeting hotels and hosts, impersonating messages from 'Booking.com' - see sample image below.
We’re seeing an ongoing phishing campaign targeting hotels and hosts, impersonating messages from 'Booking.com' - see sample image below.Here’s what we know so far:
 ️ Emails appear to target actual 'Booking.com' host email addresses, which may indicate that recipient data was obtained from a previous breach - the timing is particularly relevant given the 'Booking.com' data breach last month (see article - https://www.bbc.co.uk/news/articles/cly00jnnxypo).
️ Emails appear to target actual 'Booking.com' host email addresses, which may indicate that recipient data was obtained from a previous breach - the timing is particularly relevant given the 'Booking.com' data breach last month (see article - https://www.bbc.co.uk/news/articles/cly00jnnxypo).
 ️ While the emails appear to come from 'Booking.com', they are actually sent via compromised accounts.
️ While the emails appear to come from 'Booking.com', they are actually sent via compromised accounts.
 ️ Messages typically reference a “complaint” or “special request” requiring urgent action.
️ Messages typically reference a “complaint” or “special request” requiring urgent action.
 ️ Links often use URL shorteners or services like 'share.google' to hide phishing pages
️ Links often use URL shorteners or services like 'share.google' to hide phishing pages
 ️ Goal is to steal login credentials or payment details through fake portals
️ Goal is to steal login credentials or payment details through fake portalsThese phishing emails are very convincing, so extra caution is prudent - here are some steps you can take to reduce risk:
 Be cautious of urgency or pressure in booking-related emails
Be cautious of urgency or pressure in booking-related emails Avoid clicking shortened or unfamiliar links
Avoid clicking shortened or unfamiliar links Verify requests by logging into the platform directly
Verify requests by logging into the platform directly Report suspicious emails internally or to the platform provider
Report suspicious emails internally or to the platform provider -
R relay@relay.infosec.exchange shared this topic