This semester, I'm teaching my class on System Administration / Internet Operations once again.
-
System Administration: Week 5: Networking I: Layers
In this video, we begin our longer discussion on the topic of "networking". We're using tcpdump(8) to capture a single TCP SYN packet and start looking at the MAC and IP information, teasing out each individual byte. And don't worry, we dunk on the OSI stack model as needed and popular these days.
System Administration: Week 5: Networking I: IPv4 Basics & CIDR subnetting
In this video, we cover the basics of the 32-bit IPv4 address and how we organize networks using Classless Inter-Domain Routing or CIDR subnetting. (Don't worry, we'll get to #IPv6 in the next video.)
-
System Administration: Week 5: Networking I: IPv4 Basics & CIDR subnetting
In this video, we cover the basics of the 32-bit IPv4 address and how we organize networks using Classless Inter-Domain Routing or CIDR subnetting. (Don't worry, we'll get to #IPv6 in the next video.)
System Administration: Week 5: Networking I: IPv6 Basics
In this video, we get familiar with our Big Hero IPv6, looking at the structure of the IPv6 header and IPv6 address representations.
Since we're using AWS #EC2, remember that we have instructions for how to set up a dual-stack VPC and subnet to launch your instances in:

Creating AWS IPv4/IPv6 Dual Stack EC2 Instances
A quick summary of the AWS EC2 resources needed to create an IPv6-enabled or dualstack instance.
(www.netmeister.org)
-
System Administration: Week 5: Networking I: IPv6 Basics
In this video, we get familiar with our Big Hero IPv6, looking at the structure of the IPv6 header and IPv6 address representations.
Since we're using AWS #EC2, remember that we have instructions for how to set up a dual-stack VPC and subnet to launch your instances in:

Creating AWS IPv4/IPv6 Dual Stack EC2 Instances
A quick summary of the AWS EC2 resources needed to create an IPv6-enabled or dualstack instance.
(www.netmeister.org)
System Administration: Week 5: Networking I: IP Allocation & IPv4 Exhaustion
Mommy, where do IP addresses come from? In this video, we discuss how IANA allocates IP addresses to the Regional Internet Registries and try to illustrate just how large the #IPv6 address space is.
-
System Administration: Week 5: Networking I: IP Allocation & IPv4 Exhaustion
Mommy, where do IP addresses come from? In this video, we discuss how IANA allocates IP addresses to the Regional Internet Registries and try to illustrate just how large the #IPv6 address space is.
System Administration: Week 5: Networking I:The Physical Internet
In this video, we look at the physical structure of the internet, with a focus on submarine internet communications cables. Jumping from the bottom of the OSI stack all the way to Layer 9 ("political"), we then discuss how different countries use their political power to enforce internet blocks on their citizens, leading us to warrantless wiretapping in AT&T's room 641A.
-
System Administration: Week 5: Networking I:The Physical Internet
In this video, we look at the physical structure of the internet, with a focus on submarine internet communications cables. Jumping from the bottom of the OSI stack all the way to Layer 9 ("political"), we then discuss how different countries use their political power to enforce internet blocks on their citizens, leading us to warrantless wiretapping in AT&T's room 641A.
System Administration: Week 5: Networking I: A Network of Networks
In this video, we look at how independent networks connect to one another, how Autonomous Systems numbers allow us to identify network operators, and how peering between independent ASs works.
-
System Administration: Week 5: Networking I: A Network of Networks
In this video, we look at how independent networks connect to one another, how Autonomous Systems numbers allow us to identify network operators, and how peering between independent ASs works.
System Administration: Week 6: Networking II: A Simple Request
In this video, we trace a simple HTTP request made via telnet to find out just how exactly our application knows how to connect to the remote server. In the process we learn about the ktrace(1) utility, as well as the nsswitch.conf(5), hosts(5), and resolv.conf(5) configuration files.
-
System Administration: Week 6: Networking II: A Simple Request
In this video, we trace a simple HTTP request made via telnet to find out just how exactly our application knows how to connect to the remote server. In the process we learn about the ktrace(1) utility, as well as the nsswitch.conf(5), hosts(5), and resolv.conf(5) configuration files.
ooh. the first peek down the rabbit hole that is DNS resolution.

-
ooh. the first peek down the rabbit hole that is DNS resolution.

@paul_ipv6 Yeah. Only on most Linux flavors these days that quickly goes sideways and straight into systemd. 🤮
-
@paul_ipv6 Yeah. Only on most Linux flavors these days that quickly goes sideways and straight into systemd. 🤮
yup. hence my "rabbit hole" description.
DoT/DoH, systemd-resolved, OS level caches in M$/OSX, lying walled garden proxies.
it's much like chess. you can learn the basic rules in an afternoon but still not really master it in a lifetime.
-
R relay@relay.infosec.exchange shared this topic
-
System Administration: Week 6: Networking II: A Simple Request
In this video, we trace a simple HTTP request made via telnet to find out just how exactly our application knows how to connect to the remote server. In the process we learn about the ktrace(1) utility, as well as the nsswitch.conf(5), hosts(5), and resolv.conf(5) configuration files.
System Administration: Week 6: Networking II: ARP and NDP
In this video, we illustrate the functionality of the Address Resolution Protocol (ARP) and it's IPv6 equivalent, the Neighbor Discovery Protocol (NDP).
-
System Administration: Week 6: Networking II: ARP and NDP
In this video, we illustrate the functionality of the Address Resolution Protocol (ARP) and it's IPv6 equivalent, the Neighbor Discovery Protocol (NDP).
System Administration: Week 6: Networking II: ICMP
In this video, we demonstrate the use of the Internet Control Message Protocol or ICMP by tracing and analyzing ping(1) and traceroute(1) invocations.
And in case you're wondering: http://shouldiblockicmp.com
-
System Administration: Week 6: Networking II: ICMP
In this video, we demonstrate the use of the Internet Control Message Protocol or ICMP by tracing and analyzing ping(1) and traceroute(1) invocations.
And in case you're wondering: http://shouldiblockicmp.com
System Administration: Week 7: DNS, Part I
In this video, we are beginning our discussion of the #DNS. We go back to the early days of the internet when copying /etc/hosts from system to system was the way to resolve hosts...
(Hosts file from 1983: https://rscott.org/OldInternetFiles/hosts.19831104.txt)
...and we cover the structure of the domain name space and the creation of the top-level domains.
(Second-level domain inventory from 1987: https://rscott.org/OldInternetFiles/domain-info.19871215.txt)
-
System Administration: Week 7: DNS, Part I
In this video, we are beginning our discussion of the #DNS. We go back to the early days of the internet when copying /etc/hosts from system to system was the way to resolve hosts...
(Hosts file from 1983: https://rscott.org/OldInternetFiles/hosts.19831104.txt)
...and we cover the structure of the domain name space and the creation of the top-level domains.
(Second-level domain inventory from 1987: https://rscott.org/OldInternetFiles/domain-info.19871215.txt)
System Administration: Week 7: DNS, Part II
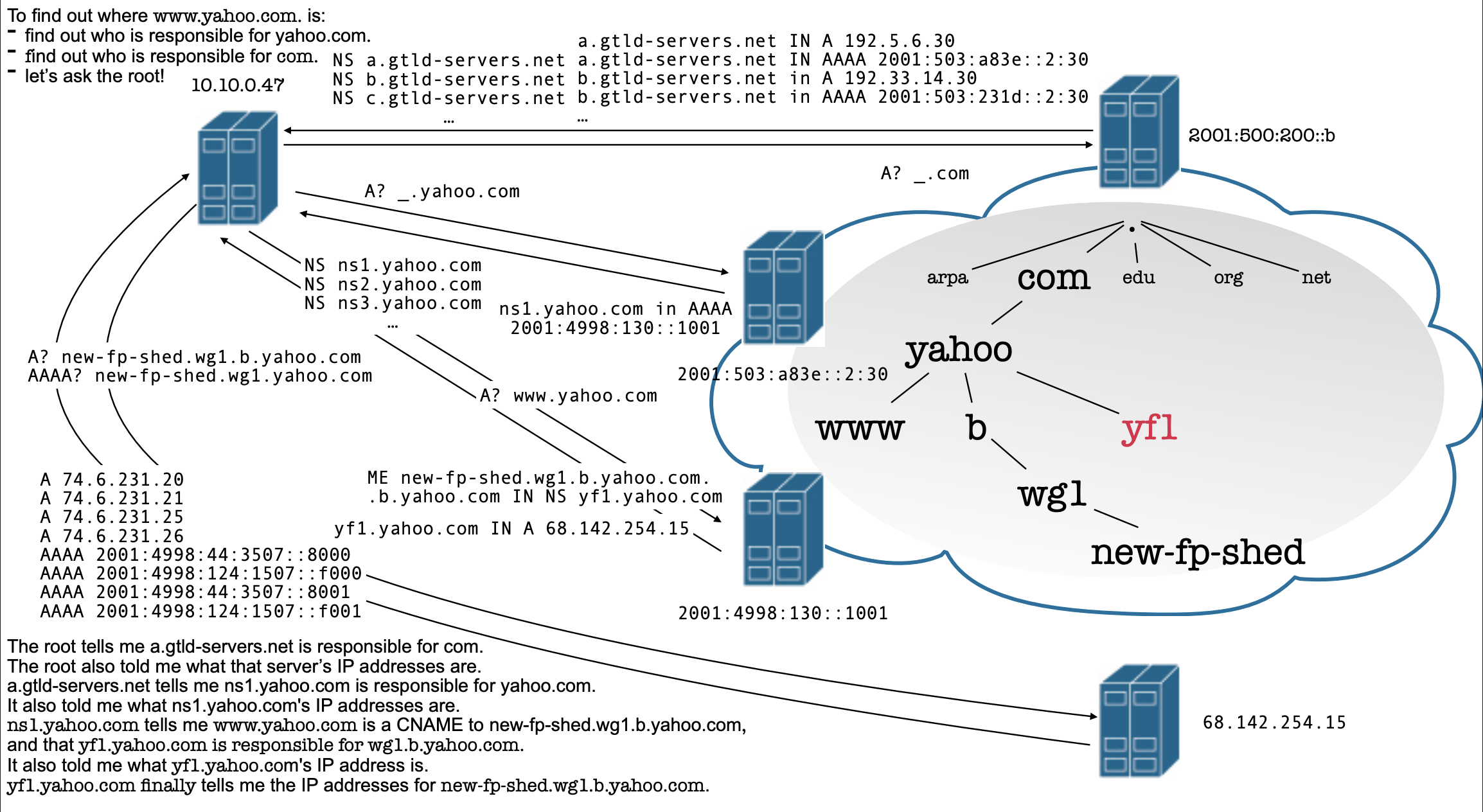
In this video, we dissect DNS lookups performed on our EC2 instance, then discuss just how a caching resolver performs the lookup, moving from "magic happens here" to the below visualization.
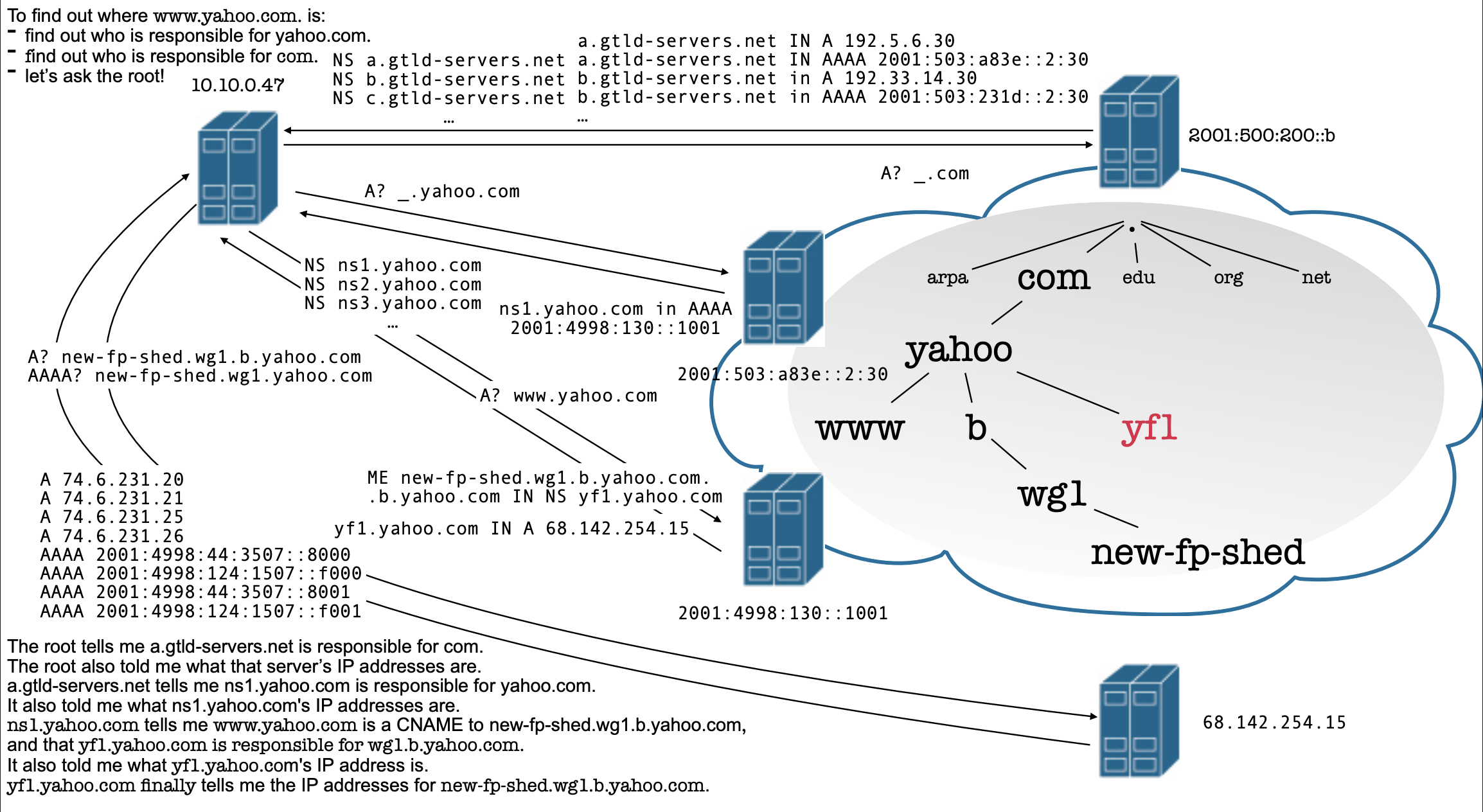
-
System Administration: Week 7: DNS, Part II
In this video, we dissect DNS lookups performed on our EC2 instance, then discuss just how a caching resolver performs the lookup, moving from "magic happens here" to the below visualization.
System Administration: Week 7: DNS, Part III
In this video, we try to wrap up our discussion of the Domain Name System by addressing the nature of the root nameservers, looking at various different resource record types, observing reverse lookups, and thinking about how we can have assurance of authenticity and integrity of the DNS results returned to us via DNSSEC.
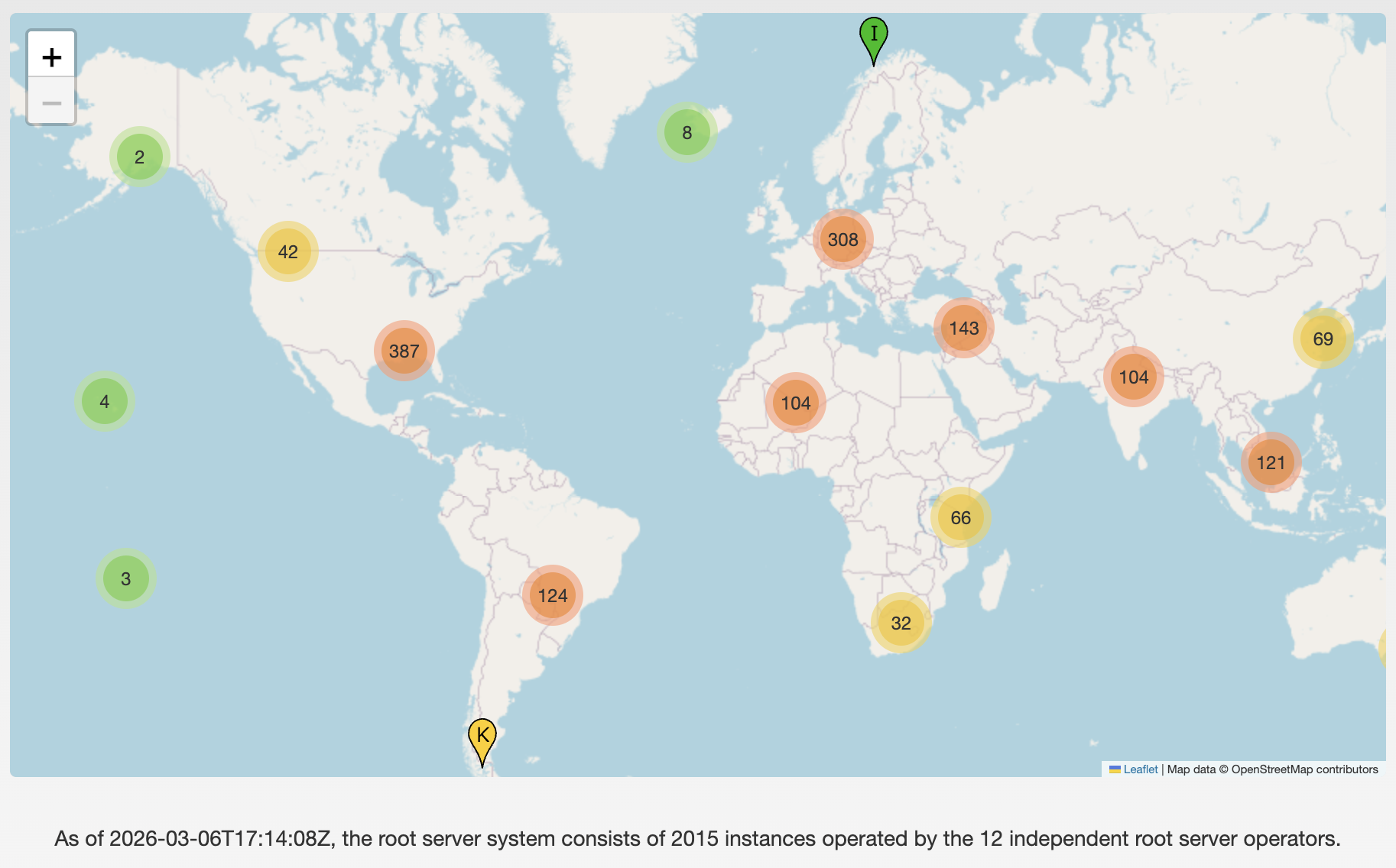
-
System Administration: Week 7: DNS, Part III
In this video, we try to wrap up our discussion of the Domain Name System by addressing the nature of the root nameservers, looking at various different resource record types, observing reverse lookups, and thinking about how we can have assurance of authenticity and integrity of the DNS results returned to us via DNSSEC.
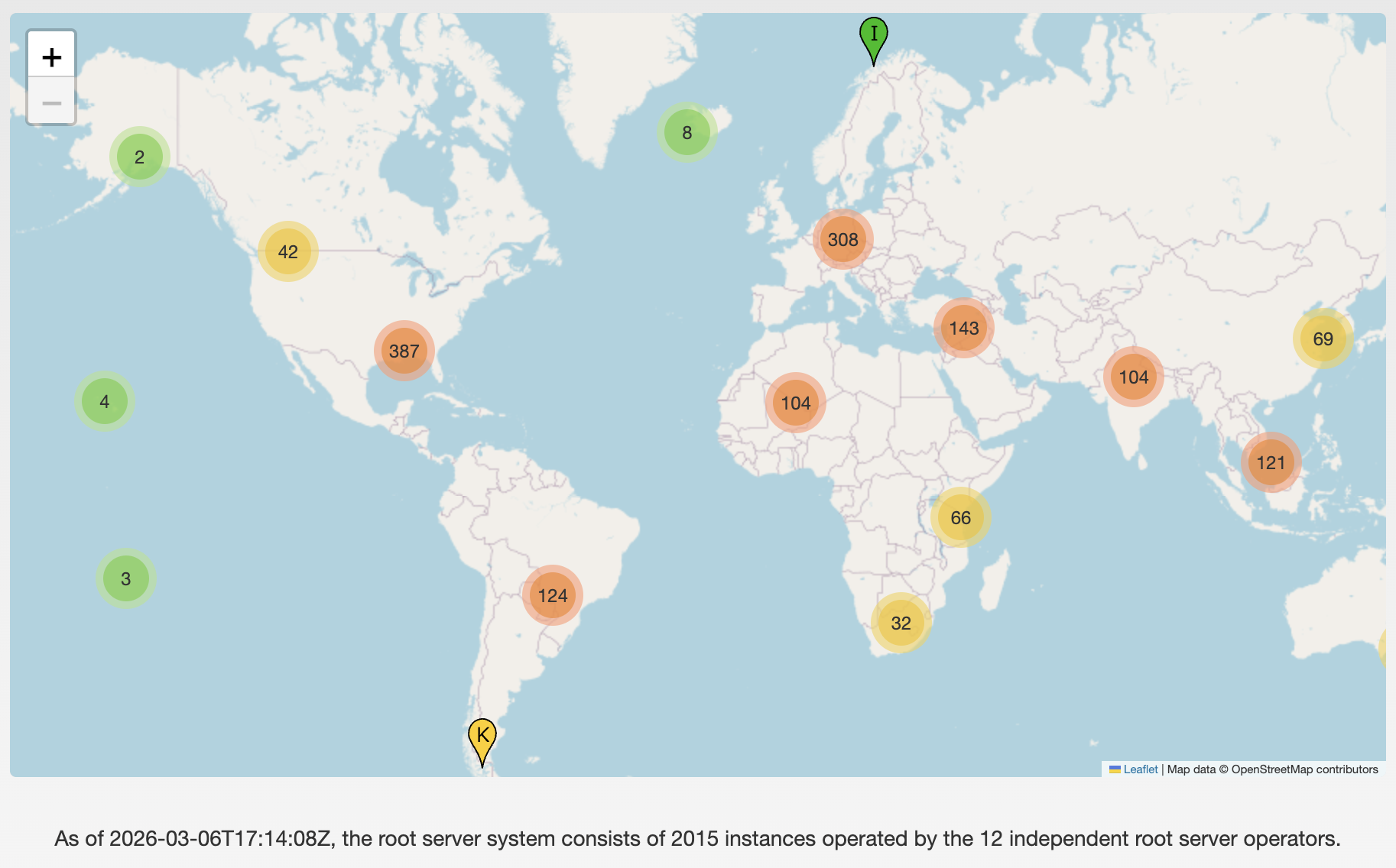
@jschauma do you cover ANYCAST in this lecture?
-
@jschauma do you cover ANYCAST in this lecture?
@peterhoneyman Not in much detail, but we summarize it in class in the context of the DNS root servers and CDN usage.
-
@peterhoneyman Not in much detail, but we summarize it in class in the context of the DNS root servers and CDN usage.
@jschauma i always had trouble with ANYCAST bc i never wanted to talk about BGP
-
@jschauma i always had trouble with ANYCAST bc i never wanted to talk about BGP
yeah... BGP is not for the faint of heart...
it's kind of like politics. you can claim anything you want and more careful folks have to do research or explicitly void your claims. sadly, in BGP and politics, way too many folks just blindly believe, then are surprised at the consequences.

