@wwahammy can’t we fork it prior to that commit and maintain a separate fork?
k3ym0@infosec.exchange
Posts
-
A small set of people are merging changes to various Linux components to make sure every application knows your birth date. -
A small set of people are merging changes to various Linux components to make sure every application knows your birth date.@wwahammy wtf… these are current maintainers???
-
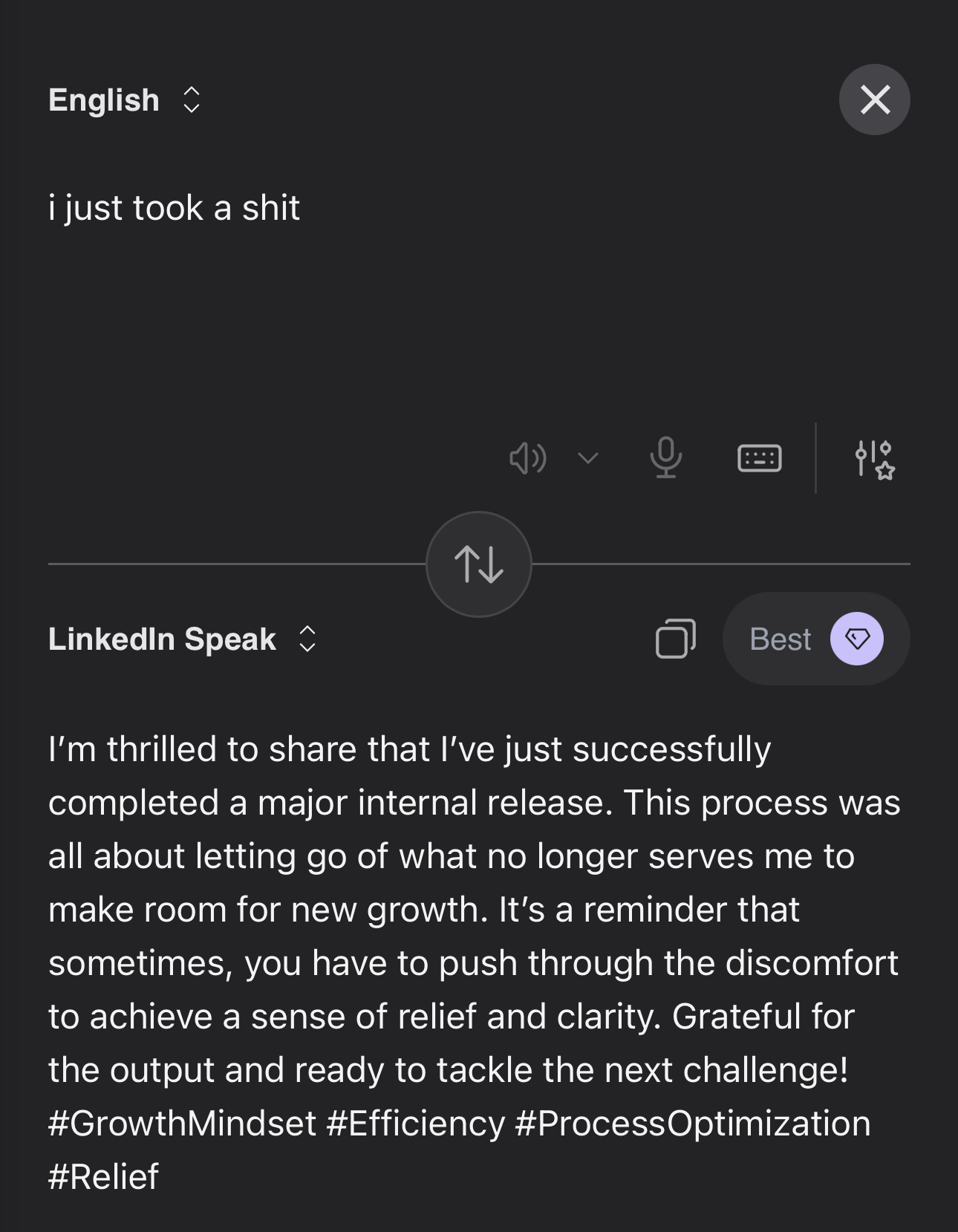
I’m currently navigating a high-friction physical integration challenge with our document reproduction hardware.@alice @catsalad I’m thrilled to share that I’ve just successfully completed a major internal release. This process was all about letting go of what no longer serves me to make room for new growth. It’s a reminder that sometimes, you have to push through the discomfort to achieve a sense of relief and clarity. Grateful for the output and ready to tackle the next challenge! #GrowthMindset #Efficiency #ProcessOptimization #Relief
-
FCC is so secure that they restrict user passwords to a max of 15 charactersFCC is so secure that they restrict user passwords to a max of 15 characters
-
hot take that isn't actually hot:hot take that isn't actually hot:
the difference between conservative privacy advocates and actual privacy advocates is a threat model.
theirs only boots up when the surveillance is pointed at them.
you can test this in real time. mention data brokers selling location data to immigration enforcement and watch the principled fourth amendment stance just... evaporate.
because here's the thing -- mass surveillance doesn't give a fuck about your politics. it gets aimed at whoever the state decides to target next.
privacy rights that don't extend to the most vulnerable people in the room aren't privacy rights - they're a fucking vibe.
-
ProtonMail anonymity speedrun, any%:ProtonMail anonymity speedrun, any%:
step 1: don’t use your real email to sign up, you absolute muppet. use a burner. gorilla mail – free, dies after an hour, leaves no trace.
step 2: free tier is fine. need to upgrade? Monero or cash. do NOT hand them a credit card.
step 3: want ToR? boot Tails OS first, full stop. Tails forgets you exist on shutdown, ToR handles the routing. together they mean something. separately you’re just cosplaying at privacy.
that’s it. that’s the whole guide. it’s not hard. the threat model does the heavy lifting, you just have to put in the work.
stay feral.

-
hot take: @protonprivacy didn’t fail you.RE: https://hachyderm.io/@evacide/116178700239265110
hot take: @protonprivacy didn’t fail you. YOUR OPSEC failed you.
encryption ≠ anonymity. these are not the same thing and never have been.
Proton did exactly what they said they’d do - encrypted your emails and complied with lawful Swiss legal orders. that’s the whole deal. that’s what you signed up for.
the credit card you used to pay for your “anonymous” account was never part of the encryption. that was always traceable. that was always a liability.
and here’s the kicker - Proton literally accepts Monero and cash. they gave you the tools. you chose the Visa.
#infosec #opsec #privacy #ProtonMail #threatmodeling #monero
-
For all the Proton fans@serebit @skinnylatte what got him was paying for his “anonymous” account with his Platinum Visa like a normie buying socks on Amazon.
Proton handed over the payment identifier, Swiss authorities passed it to the FBI, and suddenly your anonymity has a name on it.
if you’re not paying with Monero or cash, you don’t have an anonymous email. you have encrypted email with a billing address. those are very different things.
-
For all the Proton fans@serebit @skinnylatte unless you’re planning on self hosting there is literally no other email service you could jump to that hasn’t done the same thing.
-
For all the Proton fans@boojum @skinnylatte 10000% this.
-
It's awards season! -
Google traces iOS exploit kit from US intelligence contractors to Russian spies, then Chinese criminals.@schuler so basically eternal blue all over again. great.
-
You're paying AI companies a monthly subscription fee to be fingerprinted like a parolee.You're paying AI companies a monthly subscription fee to be fingerprinted like a parolee.
I got bored and ran uBlock across Claude, ChatGPT, and Gemini simultaneously.
Claude:
- Six parallel telemetry pipelines.
- A tracking GIF with 40 browser fingerprint data points baked into the URL, routed through a CDN proxy alias specifically to make it harder to block.
- Intercom running a persistent WebSocket whether you use it or not.
- Honeycomb distributed tracing on a chat UI because apparently your conversation needs the same observability stack as a payments microservice.
ChatGPT:
- proxies telemetry through their own backend to hide the Datadog destination URL from blockers.
- uBlock had to deploy scriptlet injection — actual JS injected into the page to intercept fetch() at the API level — because a network rule wasn't enough.
- Also ships your usage data to Google Analytics. OpenAI. To Google. You cannot make this up.
- Also runs a proof-of-work challenge before you're allowed to type anything.
Gemini:
- play.google.com/log getting hammered with your full session behavior, authenticated with three SAPISIDHASH token variants, piped directly into the Google identity supergraph that correlates everything you've ever done across every Google product since 2004.
- Also creates a Web App Activity record in your Google account timeline. Also has "ads" in one of the telemetry endpoint subdomains.
When uBlock blocks Gemini's requests, the JS exceptions bubble up and Gemini dutifully tries to POST the error details back to Google. uBlock blocks that too. The error messages contain the internal codenames for every upsell popup that failed to load.
KETCHUP_DISCOVERY_CARD.
MUSTARD_DISCOVERY_CARD.
MAYO_DISCOVERY_CARD.Google named their subscription upsell popups after condiments and I found out because their error handler snitched on them.
All three of these products cost money.
One of them is also running ad infrastructure.Touch grass. Install @ublockorigin
-
DHS's Office of Industry Partnership was hacked by a group called "Department of Peace" and info about ICE contracts with over 6,000 companies is now published on @ddosecrets.org!@micahflee oh no, how terrible.

