Shoplifting the jackpot conspiracy Listening Session
Theft World by Lip Critic
#vinyl
https://lipcritic.bandcamp.com/album/theft-world



#electronicpunk #breakbeat #digitalhardcore #noise #noiserock #NewYork
( #Bandcamp )
Shoplifting the jackpot conspiracy Listening Session
Theft World by Lip Critic
#vinyl
https://lipcritic.bandcamp.com/album/theft-world



#electronicpunk #breakbeat #digitalhardcore #noise #noiserock #NewYork
( #Bandcamp )
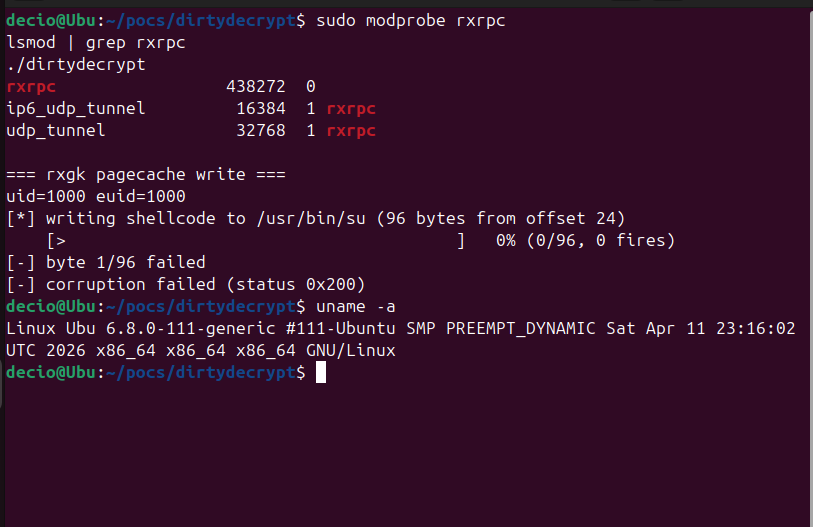
@wdormann Confirmed same experience on recent distros.
Apparently the trick is it needs CONFIG_RXGK compiled in, which most distros don't ship.
Kernel 6.8 on Ubuntu 24.04? Nothing.
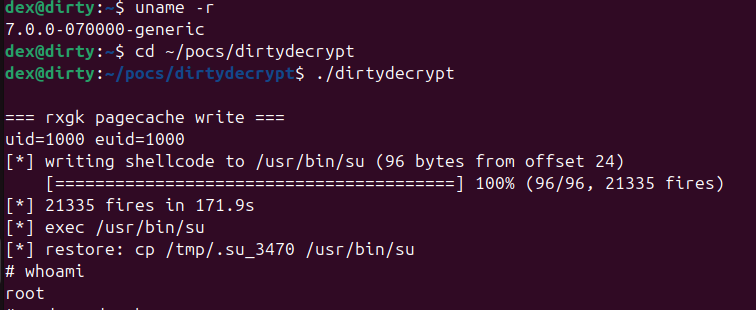
But on mainline kernel 7.0.0 it works (slow but solid):
96/96 bytes  whoami → root
whoami → root 
"Logic bug in the Linux kernel's __ptrace_may_access() function"
https://www.openwall.com/lists/oss-security/2026/05/15/2
 ️ 🤪
️ 🤪 

Nouvelle vuln kernel Linux aujourd'hui : ssh-keysign-pwn 
Pas une LPE cette fois, mais lecture de fichiers root en user non-privilégié :
• Clés privées SSH host (ecdsa/ed25519/rsa)
• /etc/shadow → crack offline
Le bug : ptrace_may_access() saute le check dumpable quand mm=NULL. Race window entre exit_mm() et exit_files(). Flaggé par Jann Horn en 2020... corrigé en 2026. 6 ans.
Confirmé sur : Debian 13, Ubuntu 22/24/26, Arch, CentOS, RPi OS. Pas de prérequis CONFIG spécifique donc cela semblerait bien plus universel que Fragnesia.
Patch mergé dans mainline par Linus aujourd'hui (31e62c2ebbfd), pas encore dans les kernels stables.
Pas de CVE assigné à ce stade.
https://github.com/0xdeadbeefnetwork/ssh-keysign-pwn
"Six-Year-Old Linux Kernel Flaw Lets Unprivileged Users Read Root-Owned Files
" ️
️
https://9to5linux.com/six-year-old-linux-kernel-flaw-lets-unprivileged-users-read-root-owned-files
et effectivement cela fonctionne avec le dernier kernel patché pour copy.fail ( AppArmor off )
et voilà il a reçu son nom de code CVE-2026-46300
@bortzmeyer Effectivement sur Ubuntu 24.04 kernel 6.8 non patché + AppArmor désactivé =
192/192 bytes 
whoami → root 
Exploit confirmé.
AppArmor tient la barrière, ne le désactivez pas 
@bortzmeyer sur ma kali same same !
└─$ grep ESPINTCP /boot/config-$(uname -r)
(6.8.11-amd64 #1 SMP PREEMPT_DYNAMIC Kali 6.8.11-1kali2 (2024-05-30))
c'est explicitement désactivé dans le kernel Kali (et vraisemblablement tout le kernel Debian).
GG Debian 

Cela semble donc Ubuntu-centrique...
@bortzmeyer yep !
XFRM_MSG_NEWSA ack errno=22
Donc Debian rejette la configuration XFRM spécifique
@bortzmeyer Intéressant, tu peux me dire sur quelle distro/version ?
Je n'ai pas encore eu le temps de le tester sur mes conteneurs & Debian/Kali, mais d'après le README pour Ubuntu: AppArmor restricts unprivileged user namespaces by default.
[related]
"Fragnesia: Linux Kernel Local Privilege Escalation via ESP-in-TCP"
https://www.wiz.io/blog/fragnesia-linux-kernel-local-privilege-escalation-via-esp-in-tcp
#Fragnesia #Linux #Kernel
"All versions affected by dirtyfrag are affected."
"Any versions without this patch: https://lists.openwall.net/netdev/2026/05/13/79 , so any Linux kernel before May 13 2026."
🤪 



et c'est reparti pour un tour : #fragnesia le petit frère de DirtyFrag (même famille ESP/XFRM, même mitigation rmmod esp4 esp6 rxrpc, même page cache qui se fait défoncer, just trust me bro).
Bonne nouvelle : si t'avais blocklisté les modules « au cas où », t'es OK.
Mauvaise nouvelle : si t'as "juste" patché DirtyFrag , il te faut le patch Fragnesia aussi.
"Fragnesia is a universal Linux local privilege escalation exploit, discovered by William Bowling with the V12 team. Fragnesia is a member of the Dirty Frag vulnerability class. "
https://github.com/v12-security/pocs/tree/main/fragnesia
...pourquoi pas?
à grand risque, grande responsabilité ️
️
"Linux kernel maintainers pitch emergency killswitch after CopyFail and Dirty Frag chaos"
https://www.theregister.com/oses/2026/05/11/linux-kernel-maintainers-pitch-emergency-killswitch-after-copyfail-and-dirty-frag-chaos/5237801


https://lore.kernel.org/all/20260507070547.2268452-1-sashal@kernel.org/
Tour d'horizon #DirtyFrag du jour :
Bien évidemment Microsoft a sauté sur l'occasion avec un article sur une vuln Linux ...because M love Linux
https://www.microsoft.com/en-us/security/blog/2026/05/08/active-attack-dirty-frag-linux-vulnerability-expands-post-compromise-risk/
L'incontournable FAQ Tenable pour ceux comme moi qui aiment lire les CVE comme un mode d'emploi IKEA
https://www.tenable.com/blog/dirty-frag-cve-2026-43284-cve-2026-43500-frequently-asked-questions-linux-kernel-lpe
Red Hat a mis à jour sa page RHSB-2026-003 avec mitigations et vérifs, en attendant le patch qui arrive "bientôt "
" 
https://access.redhat.com/security/vulnerabilities/RHSB-2026-003
Et chez moi sur ma belle et adorée Debian ? Les canaux security sont patchés pour bullseye, bookworm et trixie.
Bien joué !
https://security-tracker.debian.org/tracker/CVE-2026-43284
Cela dit, effectivement avec l'IA qui accélère la découverte + embargos qui tiennent plus = fenêtre d'exposition qui va pas aller en rétrécissant. Les mainteneurs vont devoir trouver de nouveaux tricks. Live-patch, micro-patch, pipelines accélérés... à suivre.
Nouveaux kernels stables : 7.0.5 / 6.18.28 / 6.12.87 / 6.6.138
Ils embarquent un fix partiel pour #DirtyFrag (CVE-2026-43284) et Copy Fail 2.
Partiel, car Greg Kroah-Hartman a confirmé qu'un second patch est encore en développement et n'a pas encore été mergé.
La mitigation par blacklist des modules reste donc recommandée en attendant.
https://lwn.net/Articles/1071775/
[related]
chez AlmaLinux
"Dirty Frag (CVE-2026-43284) vulnerability fix is ready for testing"
https://almalinux.org/blog/2026-05-07-dirty-frag/
variante peu sympa 
"Unprivileged Linux LPE via xfrm ESP-in-UDP MSG_SPLICE_PAGES no-COW fast path. Page-cache write into any readable file. Overwrites a nologin line in /etc/passwd with sick::0:0:...:/:/bin/bash and sus into it. Same class as Copy Fail (CVE-2026-31431), different subsystem." ️
️
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
[VULN]  ️ "Dirty Frag : cette faille zero-day donne les droits root sur Linux"
️ "Dirty Frag : cette faille zero-day donne les droits root sur Linux"
"Dirty Frag, c’est le nom de la nouvelle faille de sécurité critique qui affecte les machines Linux. Cette faille zero-day est similaire à Copy Fail puisqu’elle permet une élévation de privilèges en tant que root. Voici l’essentiel à savoir sur cette menace potentielle.
La vulnérabilité Dirty Frag a été découverte par le chercheur Hyunwoo Kim, qui avait initialement planifié une divulgation coordonnée pour le 12 mai 2026. Cependant, quelqu’un est parvenu à détecter des informations relatives à cette vulnérabilité, et donc tout a été publié en avance ce jeudi 7 mai 2026."
Hyunwoo Kim a pris la décision de publier tous les détails, notamment pour alerter la communauté : “Parce que l’embargo a été rompu, aucun correctif ni CVE n’existe pour ces vulnérabilités. Après consultation avec les mainteneurs de linux-distros@vs.openwall.org, et à la demande des mainteneurs, je publie publiquement ce document Dirty Frag.”."
https://www.it-connect.fr/dirty-frag-cette-faille-zero-day-donne-les-droits-root-sur-linux/ ️
️
https://www.openwall.com/lists/oss-security/2026/05/07/8
https://github.com/V4bel/dirtyfrag/blob/master/assets/write-up.md