In today's episode of "Can It Run Doom": DNS fucking TXT records.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
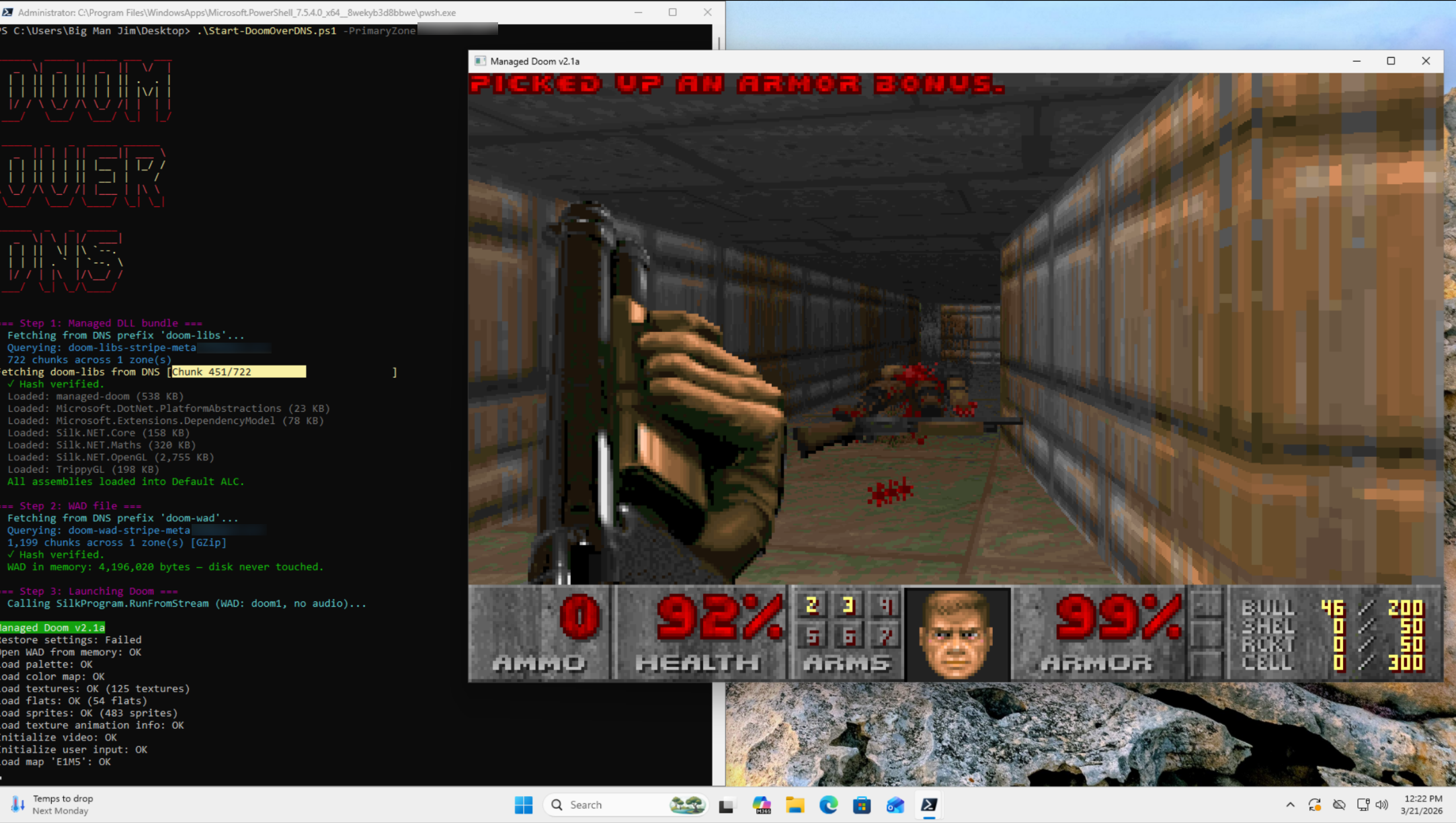
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 I used to have the entire text of the Magna Carta in TXT records in a subdomain.
Even during the early 1990's on the Interop show networks we discovered people streaming lewd stuff via DNS-looking UDP packets.
(Another channel that we used, but it only works on a LAN, is to use the space between the end of a short IP packet and the end of the enclosing Ethernet frame. [Short IP packets are smaller than the minimum size of Ethernet frames.] This was largely used for license key exchanges.)
-
@da_667 iodine and dnscat also have 20 years of signatures, known patterns, and detection logic baked into tooling. This doesn't.
But honestly that's beside the point. "Detectable" and "detected" are two very different sentences. iodine has been detectable for 20 years and I've watched it walk right out of enterprise networks that had no idea. Known technique != mature detection coverage in the median org.
SMB's are running Server 2008r2 with a Watchguard FW and a prayer. Mid-market is logging DNS at the firewall level and calling it done.
"Detectable in theory by a mature SOC" and "hard to detect in most real environments" are not mutually exclusive statements.
Yeah, I tend to agree with this take. Reliably catching techniques like DNS tunneling, DGA, etc., looks trivial until you try it on noisy real world networks with all sorts of idiosyncratic constraints, and also when you realize that what we consider "trivial" is often considered "impractical" or "impossible" for most real world orgs.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 "Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well."
Doesn't work anymore for a decade. Most serious companies don't allow DNS queries to servers outside of their network. The only endpoints allowed to do that are the corporate internal DNS.
With DoH I'm also not sure that will work because of the corporate web proxy.To make data exfiltrations there are so many easy ways to do so ... Why spending time to make something over DNS when you can simply upload the files or exploit USB keys, it's not hard to bypass FW and EDR policies.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 This post is wild but the stuff people are sharing in the comments is great hahaha
-
Yeah, I tend to agree with this take. Reliably catching techniques like DNS tunneling, DGA, etc., looks trivial until you try it on noisy real world networks with all sorts of idiosyncratic constraints, and also when you realize that what we consider "trivial" is often considered "impractical" or "impossible" for most real world orgs.
@DaveMWilburn @k3ym0 I'm well aware that trying to base your detection on shannon entropy is an exercise in futility, as most cloud providers have the "malware to ops DGA that looks like its very malicious" down pat. But I will still say, if you suddenly are getting assloads of TXT records with the same domain in common, so long as you have DNS logs at all, you can probably do some form of statistical analysis and notice that this number of DNS TXT records from one place looks really fucking jank.
-
@DaveMWilburn @k3ym0 I'm well aware that trying to base your detection on shannon entropy is an exercise in futility, as most cloud providers have the "malware to ops DGA that looks like its very malicious" down pat. But I will still say, if you suddenly are getting assloads of TXT records with the same domain in common, so long as you have DNS logs at all, you can probably do some form of statistical analysis and notice that this number of DNS TXT records from one place looks really fucking jank.
@DaveMWilburn @k3ym0 I'm also somewhat aware that, there are some services that use TXT records for validation (SPF), and I've heard that some apple services use them for their messenger programs. I've also seen Sophos doing incredibly dumb things with TXT records, but my point still stands is that if you have any capacity for DNS logs, then shit like this sticks out like a sore thumb.
However, I can acknowledge my experiences and yours are two different things. Thats fine. I can be wrong.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 Jeez. We were abusing DNS as http proxy caches in 1993. Some people were doing chat over DNS. Some of them WERE the engineers who were involved in standardization.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 I have always wondered where the "power source" they are tapping Hell for in DOOM came from. Turns out it was the DNS engineers engineers spinning in their graves all along.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 this is similar to how DeCSS (DVD decryption code) was distributed over 25 years ago when there was an attempt to suppress it online.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 Not DOOM, but this has been one of Infoblox's favorite sales demos for ages.
"Check out all this information we can exfiltrate from your network directly from a web browser via only DNS queries" always gets people's attention
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0@infosec.exchange oh we may be able to make it worse...doom via standards-compliant dns direct content serving (assuming https://datatracker.ietf.org/doc/draft-dns-content-delivery/ goes through)
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 I was at Defcon 12 when Kaminsky demoed sending voice over DNS. Glad to see the tradition continue.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 interesting vector to deploy malware

-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 Think of all the times you've wanted to take a shotgun to DNS. Now you can. Or a chainsaw.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
DNS: "Tell them it was me."

Always Has Been
An Always Has Been meme. Caption your own images or memes with our Meme Generator.
Imgflip (imgflip.com)
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 DOOM over DNS, never thought I'd see the day.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 in today's episode of "this is lazy ai vibe-coded slop":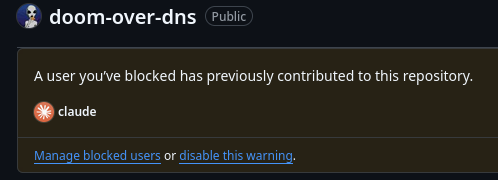
-
@k3ym0 in today's episode of "this is lazy ai vibe-coded slop":
@EeveeEuphoria@translunar.academy @k3ym0@infosec.exchange when i don't know C# i go to msdn.microsoft.com and figure things out instead of doing anything i can to avoid learning. Kids these days

-
@k3ym0 in today's episode of "this is lazy ai vibe-coded slop":
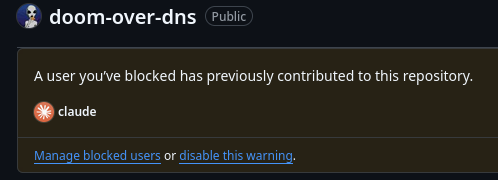
@EeveeEuphoria@social.translunar.academy @k3ym0@infosec.exchange Screams and fades into dust.
-
@k3ym0 in today's episode of "this is lazy ai vibe-coded slop":
@EeveeEuphoria oh noooo