Gawd sometimes I hate passkeys.
-
@karlauerbach One of my parents has arthritis in their hands, and putting in a rotating passkey in 30 seconds is genuinely difficult for them some days. It makes them panic, and they just want to go back to using passwords with no time limit.
@GamesMissed @karlauerbach Those four digit codes aren't passkeys, they're something different. (They're called TOTP authenticator codes, not that you need to know that.) Passkeys - the thing people earlier in the thread are talking about - are a newer thing, kind of like a password that's stored in your computer, and you just have to "unlock" them by doing some simple action like touching a button or scanning your fingerprint or typing in a PIN (which doesn't have to ever change). At least, that's the theoretical idea, though in practice they often wind up being kind of hard to set up.
By the way for the 30-second rotating codes (TOTP), you might want to know that you don't have to enter the code before the next one shows up. There's a grace period where a code is still valid even though it's not showing up on the authenticator app (or whatever). I think it might be another 30 seconds, maybe longer, but I'm not sure offhand.
-
@GamesMissed @karlauerbach Those four digit codes aren't passkeys, they're something different. (They're called TOTP authenticator codes, not that you need to know that.) Passkeys - the thing people earlier in the thread are talking about - are a newer thing, kind of like a password that's stored in your computer, and you just have to "unlock" them by doing some simple action like touching a button or scanning your fingerprint or typing in a PIN (which doesn't have to ever change). At least, that's the theoretical idea, though in practice they often wind up being kind of hard to set up.
By the way for the 30-second rotating codes (TOTP), you might want to know that you don't have to enter the code before the next one shows up. There's a grace period where a code is still valid even though it's not showing up on the authenticator app (or whatever). I think it might be another 30 seconds, maybe longer, but I'm not sure offhand.
@diazona @GamesMissed Thanks for the explanation.
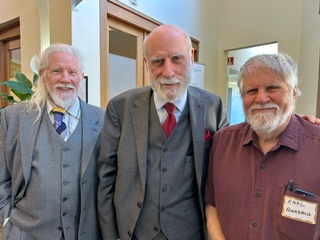
(I was aware that the multiple digit 2FA numbers that come via email or text are not part of passkeys. Same for the six digit things generated my RSA keyfobs and Authenticator apps. I do not know the correct nouns for these things. BTW, I'm somewhat familiar with the workings of things based on public key cryptography - Whit Diffie worked in my computer/network security research group way back when. Here's a somewhat recent photo of me and Whit:
-
@diazona @GamesMissed Thanks for the explanation.
(I was aware that the multiple digit 2FA numbers that come via email or text are not part of passkeys. Same for the six digit things generated my RSA keyfobs and Authenticator apps. I do not know the correct nouns for these things. BTW, I'm somewhat familiar with the workings of things based on public key cryptography - Whit Diffie worked in my computer/network security research group way back when. Here's a somewhat recent photo of me and Whit:
@karlauerbach @GamesMissed Understood, you don't need to prove your credentials to me. It's just that the post I was replying to was conflating passkeys and TOTP codes, and I thought clearing that up would be useful (if not to you, at least to other people reading the thread).
-
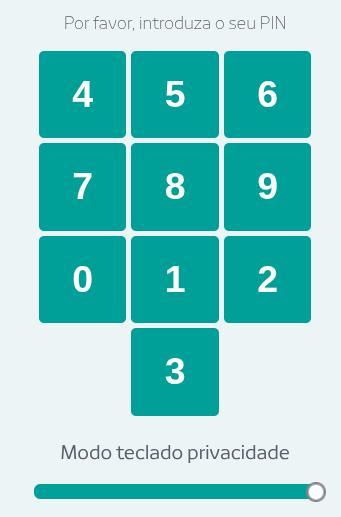
@GhostOnTheHalfShell @karlauerbach @GamesMissed My Novobanco website login takes my username / passcode(*), then requires authenticating me via the app on my phone (which requires only the same passcode). Every time I race to login to the app - because the notification will not show up in the app if I'm already logged in - and approve it within 30 seconds.
(*) The passcode entry screen is a 10 digit keypad. But the numbers are not where you expect them to be. And they move, each time.
@oddhack @karlauerbach @GamesMissed
That sounds more frightening than I want to think about
-
@karlauerbach I still haven’t seen a good concise summary of how to use passkeys in any context, but my vague impression of them is that if I enable them then my access ends when the device fails - and eventually every device will fail, so I’m not using passkeys
@ShadSterling Passkeys are somewhat clever. They use the ability of public/private crypto keys to perform an identity challenge that is unique every time it is used. The private key is stored on your machine(s) and the matching public key is on the website/service. A biometric is usually used to allow the private key to be taken from its storage (which could be a protected, trusted bit of hardware, or not) and a random challenge is sent to the website. That website has to unwrap that challenge using the public key and return the challenge (or a digest of it) back to the client and who can check whether the unwrapped challenge is correct. As with most things cryptographic, there are many devils lurking in the details and there are vulnerabilities in unexpected places - such as in public key systems one has to take care not to accept a bogus "public" key.
Update: I made some errors, particularly with regard to who issues the challenge and how it is processed.
-
@oddhack @karlauerbach @GamesMissed
That sounds more frightening than I want to think about
@GhostOnTheHalfShell @karlauerbach @GamesMissed it is cursed beyond reason. Portugal is not big on accessibility in general, and this design pattern is explicitly hostile towards *everyone* using the website.
-
@GhostOnTheHalfShell @karlauerbach @GamesMissed My Novobanco website login takes my username / passcode(*), then requires authenticating me via the app on my phone (which requires only the same passcode). Every time I race to login to the app - because the notification will not show up in the app if I'm already logged in - and approve it within 30 seconds.
(*) The passcode entry screen is a 10 digit keypad. But the numbers are not where you expect them to be. And they move, each time.
@oddhack @GhostOnTheHalfShell @GamesMissed What you are describing is not a passkey system. What you describe seems to be a name:time-based-authenticator system. Usually passkey systems only require a login name and a biometric (the biometric is processed locally on your machine and not transmitted.)
A lot of financial institutions use this method. Indeed many banks hand out RSA fobs to customers to use. These generate a new 6-digit authentication sequence every 30 seconds or so. There are also software versions, such as the Google Authenticator App.
(When I was working on various things at "the labs" sometimes we had to pass through rotating gates, kinda like jails, and we were physically locked in until we had passed all the identification/authentication tests. I never felt comfortable when locked in that way.)
-
@karlauerbach Dealing with my MIL's tech at her assisted living facility is a nonstop time suck. And it repeats. And nobody on staff is particularly good at helping either. At this point I've just stopped trying. If she can watch tennis on TV and get her texts on her phone, I just am too burned out with it to jump through hoops anymore. BUT I am thinking through how to set things up for ourselves in our old age. How to simplify.
@nomdeb I have similar issues with my mother at a living facility. She regularly destroys the software or hardware of her devices by pushing every button (sometimes at the same time) and pounding on things as if she were on a chain gang breaking rocks.
Most recently she bricked, somehow, her iPhone to the degree that it had to be replaced by a new one. (Fortunately I had set it up to back up pretty much everything important to Apple's iCloud - I trust Apple with things far more than I would were it an Android phone and Google.)
-
@karlauerbach @rodneylives @Bodling
That means that grain is going to get more expensive for the simple reason that it will probably have to travel around the tip of South America.
It’s a real pile of drought in America’s bread basket plus fertilizer constraints at a bad time, plus extreme weather.
Building a supply chain with no tolerance to it. It’s kind of a problem.
2/2
@GhostOnTheHalfShell @rodneylives @Bodling I've heard about the Panama drought problem. But you are right that it is under-reported.
Back during the first trump term China realized that the US has become an unreliable supplier of grain, particularly soy.
So China made investments in grain growing countries, such as Argentina, to create solid product-moving infrastructure, such as good roads, good railroads, and deepwater docking facilities - thus greatly reducing the shipping costs and thus effectively permanently putting US growers at a net price disadvantage vis-a-vis non US growers of soy.
China clearly has strategic long term thinkers and investors, something the US seems to have depleted.
-
@ShadSterling Passkeys are somewhat clever. They use the ability of public/private crypto keys to perform an identity challenge that is unique every time it is used. The private key is stored on your machine(s) and the matching public key is on the website/service. A biometric is usually used to allow the private key to be taken from its storage (which could be a protected, trusted bit of hardware, or not) and a random challenge is sent to the website. That website has to unwrap that challenge using the public key and return the challenge (or a digest of it) back to the client and who can check whether the unwrapped challenge is correct. As with most things cryptographic, there are many devils lurking in the details and there are vulnerabilities in unexpected places - such as in public key systems one has to take care not to accept a bogus "public" key.
Update: I made some errors, particularly with regard to who issues the challenge and how it is processed.
@karlauerbach that’s about how passkeys work, not how to use them
-
@nomdeb I have similar issues with my mother at a living facility. She regularly destroys the software or hardware of her devices by pushing every button (sometimes at the same time) and pounding on things as if she were on a chain gang breaking rocks.
Most recently she bricked, somehow, her iPhone to the degree that it had to be replaced by a new one. (Fortunately I had set it up to back up pretty much everything important to Apple's iCloud - I trust Apple with things far more than I would were it an Android phone and Google.)
@karlauerbach YES!!!!!! Said with feeling. So much feeling. Exactly this. She also refuses any efforts I make to get her occupational therapist help to teach her stuff that she uses frequently like the TV remote control. Or learn to use voice controls. All the deep sighs. I did lol to see a book titled stupid things my parents did that I will avoid.
 but more seriously I am planning as best as I can to keep up with tech that will help in my own old age and try for simplicity.
but more seriously I am planning as best as I can to keep up with tech that will help in my own old age and try for simplicity. -
That's...a thing I worry about. I've started to see "Set up a passkey" as a default page I have to click past. The first time, I nearly started to set it up, but then had a think based on some mutterings I'd heard On Here.
I'm and Old, & a Luddite, & very much •dis•inclined to jump on the latest fad, so I have not set up any passkeys. Sounds like I very much don't want to.
@cavyherd Do consider setting up passkeys. They are a great improvement over passwords and one usually does not forget to carry one's biometrics wherever one might choose to go. Often setting up a passkey is so painless that one might not even notice that it was done. (It is annoying on my Mac Mini because that machine does not have Apple's fingerprint button, so I usually set up passkeys on my other Apple devices and let them be [hopefully securely] propagated via Apple's iCloud sharing.)
One of the weakness of passkey is that you usually need a computer/phone onto which the private key part of the desired passcode has been propagated - so you usually need your smart phone or laptop, you can't expect to be able to walk up to an arbitrary computer, while wearing nothing but your birthday suit, and securely log in. With passwords you could do that - although I rarely see a naked person doing banking.
-
@karlauerbach YES!!!!!! Said with feeling. So much feeling. Exactly this. She also refuses any efforts I make to get her occupational therapist help to teach her stuff that she uses frequently like the TV remote control. Or learn to use voice controls. All the deep sighs. I did lol to see a book titled stupid things my parents did that I will avoid.
 but more seriously I am planning as best as I can to keep up with tech that will help in my own old age and try for simplicity.
but more seriously I am planning as best as I can to keep up with tech that will help in my own old age and try for simplicity.@karlauerbach truly there should be a whole career field of tech for geriatrics including building it into assisted living facilities (or homes) and training people for hire who can be called out. Assisted living IT person is just a hook up the TV sort.
-
@karlauerbach which for transfers is OK, but for paying a bill and setting money aside? ugh
@crystalmoon I live in the Apple world, so for most bank transactions, or paying bills, or even buying something at a store, I find that the most I need is my face (for facial recognition biometric) or my finger (for fingerprint biometric).
My banks seem to have some sort of size/dollar threshold that triggers the use of a time-based authenticator, like an RSA widget or Google Authenticator app. Because we own a business we usually have to do that when dealing with our business accounts.
-
@karlauerbach that’s about how passkeys work, not how to use them
@ShadSterling I'm a techie so I often skip the "how does one use this" and jump to the "how does it work under the skin" mode.
Normally one encounters a passkey when logging into a website or service.
Usually there is the normal "who are you" phase in which enter an email address or user name or something.
Then you simply activate the biometric thingy on your device - on my iPhones it is the camera looking at my face, on my Macbooks it is the fingerprint key. (And on my other devices - I have to cancel out and hope that the service still has a username/password method of getting in.)
Once the biometric is taken then some packets get exchanged (usually quite quickly) via the net and you get let into the service.
It's pretty easy, a lot easier than remember and entering a password.
-
@ShadSterling I'm a techie so I often skip the "how does one use this" and jump to the "how does it work under the skin" mode.
Normally one encounters a passkey when logging into a website or service.
Usually there is the normal "who are you" phase in which enter an email address or user name or something.
Then you simply activate the biometric thingy on your device - on my iPhones it is the camera looking at my face, on my Macbooks it is the fingerprint key. (And on my other devices - I have to cancel out and hope that the service still has a username/password method of getting in.)
Once the biometric is taken then some packets get exchanged (usually quite quickly) via the net and you get let into the service.
It's pretty easy, a lot easier than remember and entering a password.
@karlauerbach what on earth does “encounters a passkey” mean? That sounds like an item I might pick up in a game by stepping on it.
Pasting a password from my manager is trivial. Having multiple passwords for multiple accounts on the same site is easy. Syncing my password file across devices is routine.
With passkeys I’ve never seen a clear statement that using multiple devices is possible, much less whether multiple browsers on the same device get treated as different devices
-
@karlauerbach what on earth does “encounters a passkey” mean? That sounds like an item I might pick up in a game by stepping on it.
Pasting a password from my manager is trivial. Having multiple passwords for multiple accounts on the same site is easy. Syncing my password file across devices is routine.
With passkeys I’ve never seen a clear statement that using multiple devices is possible, much less whether multiple browsers on the same device get treated as different devices
@ShadSterling My passkeys work across my devices (I am within the Apple kingdom of computer and phones.) Apple propagates a lot of this between your machines via iCloud. (My Linux and FreeBsd machines are often operated remotely and without a console/keyboard - so doing a biometric with a passkey on those machines is kinda a pain, but for those I have pre-established SSH keys.)
With the way that HTTP works (with or without TLS - that's the S in HTTPS) each connection from any browser on the same machine begins as a distinct engagement with the service. Should the service bind those together (using cookies or something) that is a matter for the service software, not part of the way that passkeys work.
-
@cavyherd Do consider setting up passkeys. They are a great improvement over passwords and one usually does not forget to carry one's biometrics wherever one might choose to go. Often setting up a passkey is so painless that one might not even notice that it was done. (It is annoying on my Mac Mini because that machine does not have Apple's fingerprint button, so I usually set up passkeys on my other Apple devices and let them be [hopefully securely] propagated via Apple's iCloud sharing.)
One of the weakness of passkey is that you usually need a computer/phone onto which the private key part of the desired passcode has been propagated - so you usually need your smart phone or laptop, you can't expect to be able to walk up to an arbitrary computer, while wearing nothing but your birthday suit, and securely log in. With passwords you could do that - although I rarely see a naked person doing banking.
"One does not forget to carry one's biometrics".
Except they're inaccessible on VERY common use cases like "desktop PC without webcam" or "public kiosk".
So we have to do terrible Rube Goldberg flows for non-smartphone users. I really don't want my digital life centered around a delicate theft-target device that's mostly a vector for funneling personal data to an American bigtech.
TOTP 2FA can be run on a freaking Commodore 64. Emailed codes are tech-agnostic.
-
@GhostOnTheHalfShell @rodneylives @Bodling I've heard about the Panama drought problem. But you are right that it is under-reported.
Back during the first trump term China realized that the US has become an unreliable supplier of grain, particularly soy.
So China made investments in grain growing countries, such as Argentina, to create solid product-moving infrastructure, such as good roads, good railroads, and deepwater docking facilities - thus greatly reducing the shipping costs and thus effectively permanently putting US growers at a net price disadvantage vis-a-vis non US growers of soy.
China clearly has strategic long term thinkers and investors, something the US seems to have depleted.
@karlauerbach @GhostOnTheHalfShell @rodneylives @Bodling China has been around for thousands of years, all their thinking is long term compared to anywhere else. And they invented bureaucracy too, which ensures that a system will be in place to implement and oversee plans that span far beyond any individual's lifetime.
-
"One does not forget to carry one's biometrics".
Except they're inaccessible on VERY common use cases like "desktop PC without webcam" or "public kiosk".
So we have to do terrible Rube Goldberg flows for non-smartphone users. I really don't want my digital life centered around a delicate theft-target device that's mostly a vector for funneling personal data to an American bigtech.
TOTP 2FA can be run on a freaking Commodore 64. Emailed codes are tech-agnostic.
@hakfoo @cavyherd 2FA is good (certainly more secure than a simple password) and, as you point out, requires few resources (apart from the need to have a 2nd communications medium to carry the 2nd factor messages.) But it does have vulnerabilities, particularly if the attacker has ways to affect the routing of the 2nd factor to the user. For instance Telco routing of that 2nd factor via SMS has been a source of attack.
