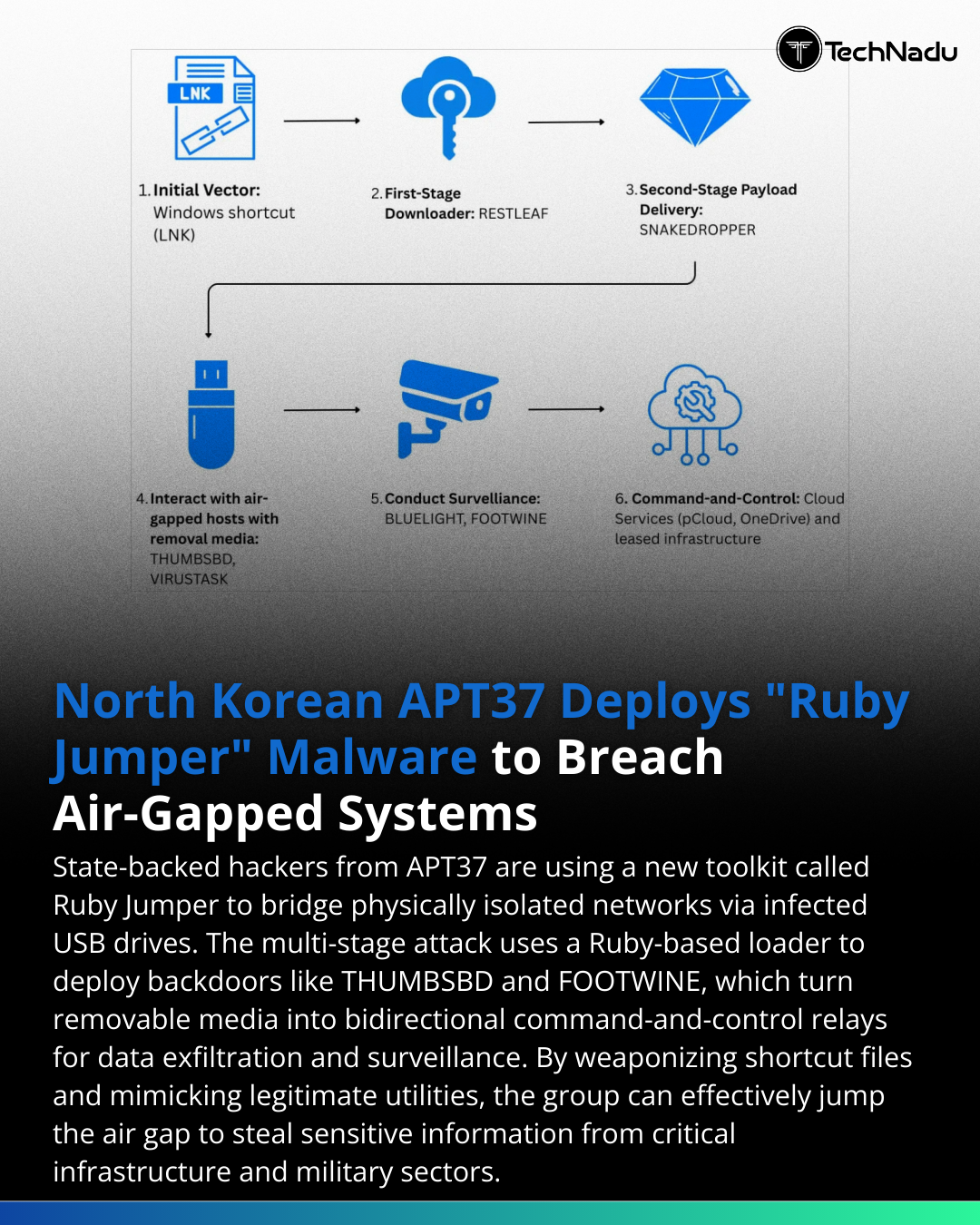
APT37’s Ruby Jumper campaign demonstrates a mature approach to air-gap traversal.Observed tradecraft includes:• LNK-based initial execution• Embedded PowerShell payload extraction• Ruby interpreter abuse (v3.3.0)• Scheduled task persistence (5-minute interval)• USB-based covert bidirectional C2• Multi-stage backdoor deploymentToolset: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, FOOTWINE, BLUELIGHT.The removable media relay model enables:– Command staging offline– Data exfiltration without internet access– Lateral spread across isolated systems– Surveillance via Windows spywareThis reinforces a critical point:Air-gap controls must extend beyond physical disconnection — including USB governance, device auditing, behavioral monitoring, and strict runtime execution policies.Are critical infrastructure operators prepared for USB-mediated C2 relays?Source: https://www.bleepingcomputer.com/news/security/apt37-hackers-use-new-malware-to-breach-air-gapped-networks/Engage below.Follow TechNadu for high-signal threat intelligence insights.Repost to elevate awareness.#Infosec #APT37 #AirGapSecurity #ThreatModeling #MalwareAnalysis #NationStateThreats #USBExfiltration #SOC #DetectionEngineering #CyberDefense #OperationalSecurity #ThreatHunting #ZeroTrustArchitecture
 1
0 Votes1 Posts0 Views
1
0 Votes1 Posts0 Views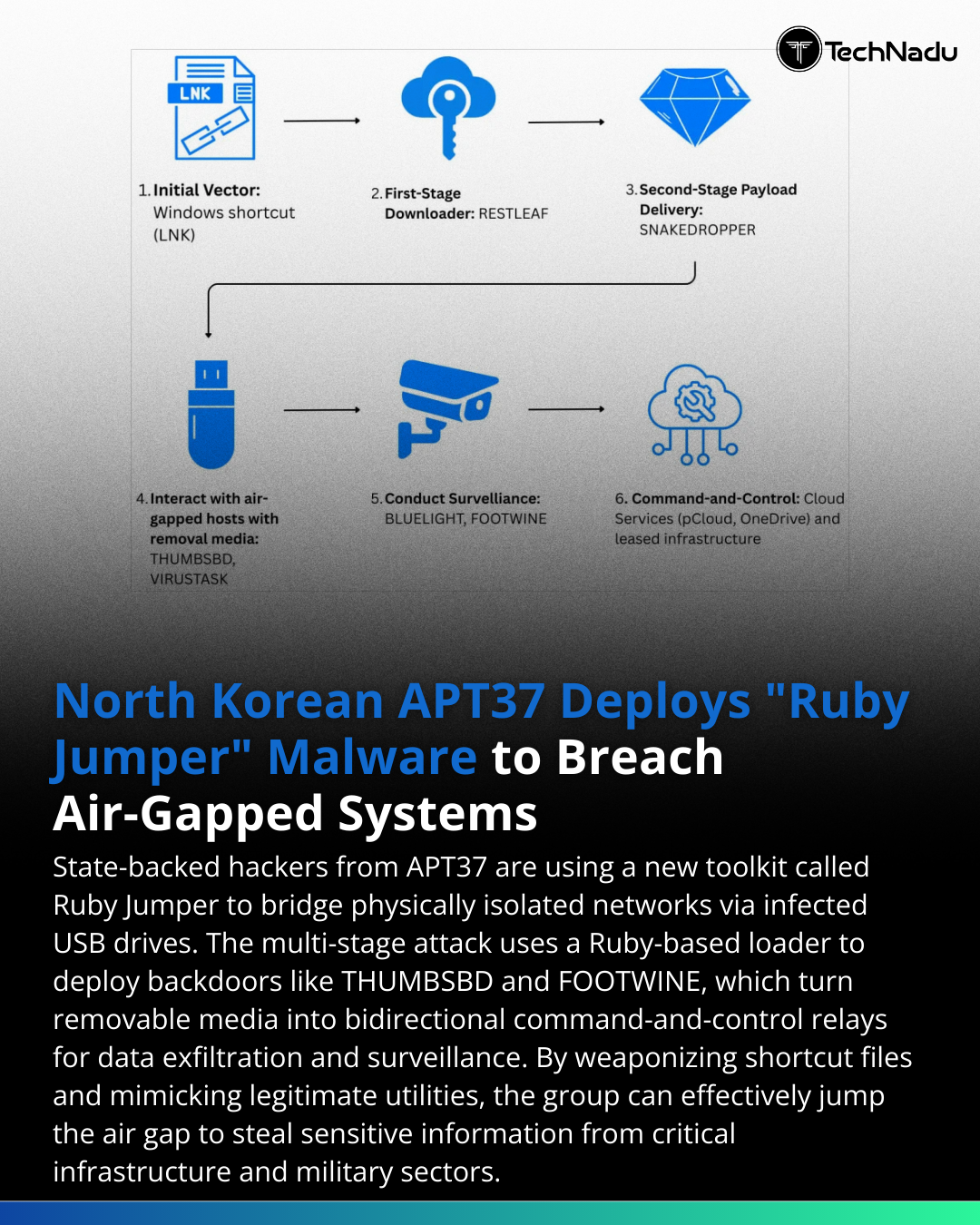 1
1
