https://lwn.net/Articles/1071719/
-

Dirty Frag: a zero-day universal Linux LPE
Hyunwoo Kim has announced the Dirty Frag security flaw, a local-privilege-escalation (LPE) vuln [...]

LWN.net (lwn.net)
#DirtyFrag is a broken embargo.
Local Privilege Escalation to root.
Public working exploit. No CVE assigned yet.
No fix in sight.
<Edith> 7.0.5 was just released which has a fix <\Edith>#infosec #cyber #tsunamiofvulns
This is the documentation & exploit of DirtyFrag:
https://github.com/V4bel/dirtyfrag/blob/master/README.md
-

Dirty Frag: a zero-day universal Linux LPE
Hyunwoo Kim has announced the Dirty Frag security flaw, a local-privilege-escalation (LPE) vuln [...]

LWN.net (lwn.net)
#DirtyFrag is a broken embargo.
Local Privilege Escalation to root.
Public working exploit. No CVE assigned yet.
No fix in sight.
<Edith> 7.0.5 was just released which has a fix <\Edith>#infosec #cyber #tsunamiofvulns
This is the documentation & exploit of DirtyFrag:
https://github.com/V4bel/dirtyfrag/blob/master/README.md
It's making for an interesting evening but there is a simple mitigation given in the github (as long as you don't actually need any of the three kernel modules it blocks from loading...)
GitHub - V4bel/dirtyfrag
Contribute to V4bel/dirtyfrag development by creating an account on GitHub.
GitHub (github.com)
-

Dirty Frag: a zero-day universal Linux LPE
Hyunwoo Kim has announced the Dirty Frag security flaw, a local-privilege-escalation (LPE) vuln [...]

LWN.net (lwn.net)
#DirtyFrag is a broken embargo.
Local Privilege Escalation to root.
Public working exploit. No CVE assigned yet.
No fix in sight.
<Edith> 7.0.5 was just released which has a fix <\Edith>#infosec #cyber #tsunamiofvulns
This is the documentation & exploit of DirtyFrag:
https://github.com/V4bel/dirtyfrag/blob/master/README.md
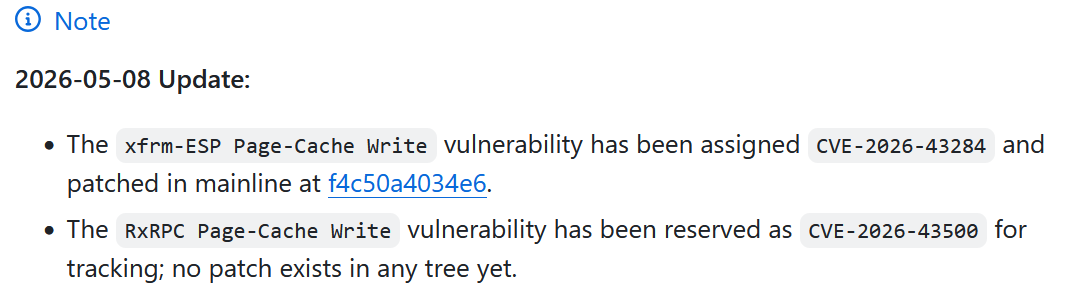
There seen to be a fix in commit https://git.kernel.org/pub/scm/linux/kernel/git/netdev/net.git/commit/?id=f4c50a4034e62ab75f1d5cdd191dd5f9c77fdff4
That fix made it into 7.0.5 which was released 30 mins (?) ago
https://cdn.kernel.org/pub/linux/kernel/v7.x/ChangeLog-7.0.5
-
There seen to be a fix in commit https://git.kernel.org/pub/scm/linux/kernel/git/netdev/net.git/commit/?id=f4c50a4034e62ab75f1d5cdd191dd5f9c77fdff4
That fix made it into 7.0.5 which was released 30 mins (?) ago
https://cdn.kernel.org/pub/linux/kernel/v7.x/ChangeLog-7.0.5
@mcfly What do they mean by "embargo has been broken"? Someone just willy nilly published that exploit before the distro / kernel guys could react?
-
@mcfly What do they mean by "embargo has been broken"? Someone just willy nilly published that exploit before the distro / kernel guys could react?
@miketango from what I can read in the discussion is that someone saw the fix in the commit and asked a LLM too build an exploit and published that.
That someone was not aware of an embargo
-
@miketango from what I can read in the discussion is that someone saw the fix in the commit and asked a LLM too build an exploit and published that.
That someone was not aware of an embargo
@mcfly @miketango may they step on a Lego every day forever.
-
There seen to be a fix in commit https://git.kernel.org/pub/scm/linux/kernel/git/netdev/net.git/commit/?id=f4c50a4034e62ab75f1d5cdd191dd5f9c77fdff4
That fix made it into 7.0.5 which was released 30 mins (?) ago
https://cdn.kernel.org/pub/linux/kernel/v7.x/ChangeLog-7.0.5
@mcfly are you sure? https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo claims:
"Same bug exists in esp6_input and is not covered by the v4 fix f4c50a4034." -
@miketango from what I can read in the discussion is that someone saw the fix in the commit and asked a LLM too build an exploit and published that.
That someone was not aware of an embargo
@mcfly @miketango I guess that's the world we live in now. If fixes are open in the public eventually some vibe-kiddy just publishes an exploits.
But is it feasible keep the fixing work secret in projects like the linux kernel? I doubt.
In this times it really comes to light who has actually good security. Who can quickly apply mitigations and detection.
-
R relay@relay.infosec.exchange shared this topic
-

Dirty Frag: a zero-day universal Linux LPE
Hyunwoo Kim has announced the Dirty Frag security flaw, a local-privilege-escalation (LPE) vuln [...]

LWN.net (lwn.net)
#DirtyFrag is a broken embargo.
Local Privilege Escalation to root.
Public working exploit. No CVE assigned yet.
No fix in sight.
<Edith> 7.0.5 was just released which has a fix <\Edith>#infosec #cyber #tsunamiofvulns
This is the documentation & exploit of DirtyFrag:
https://github.com/V4bel/dirtyfrag/blob/master/README.md