heyyyyyy.
-
please also enjoy this beautiful enumeration
- Smart Auto
- Auto
- Enabled
- Disabled
- Manual
i don't know where to begin. would "Enabled" or "Disabled" not imply "Manual"? what the fuck is the difference between "Auto" and "Smart Auto"??
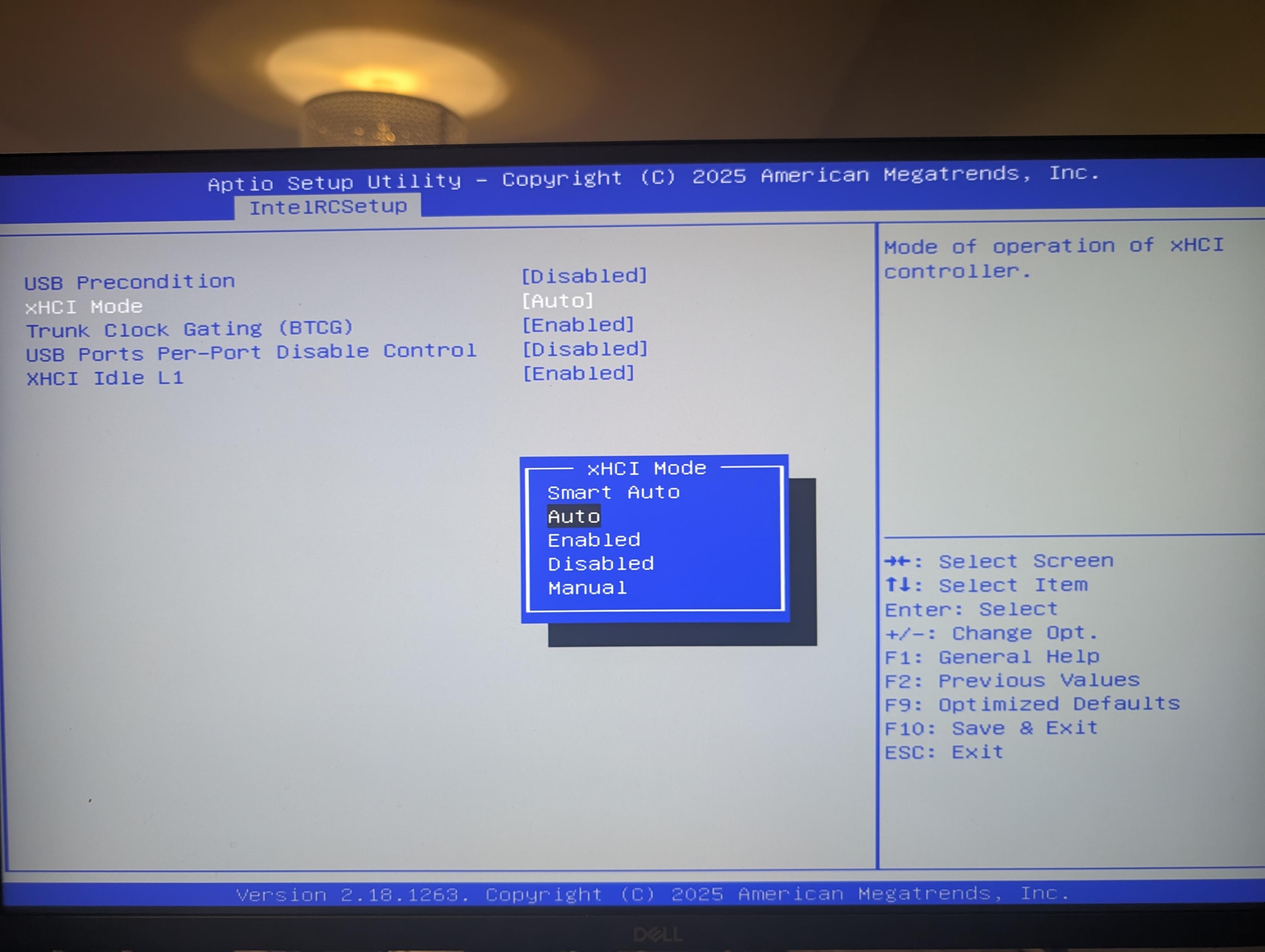
@whitequark dumb auto, obviously
-
@whitequark dumb auto, obviously
@whitequark (i have no idea)
-
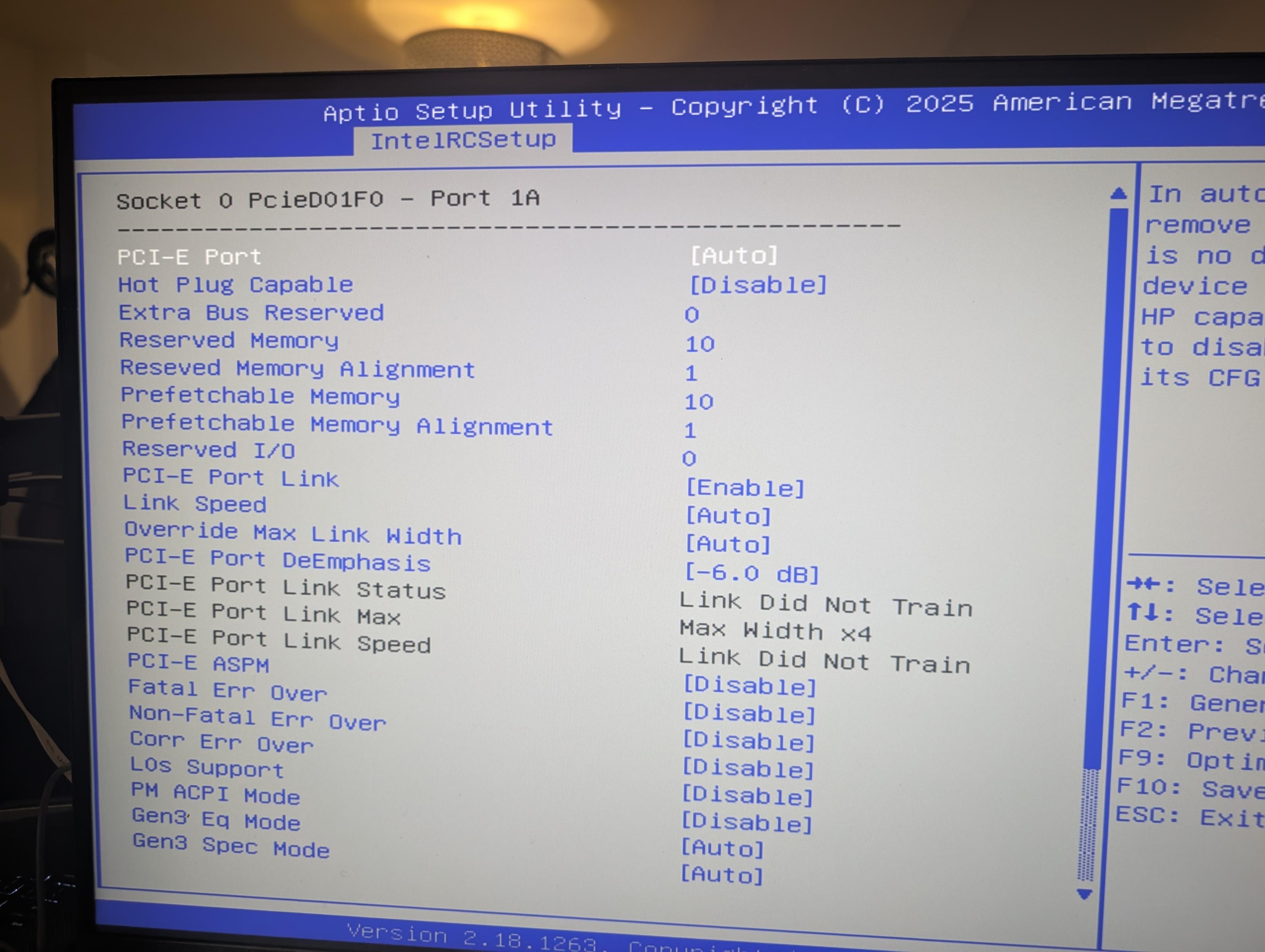
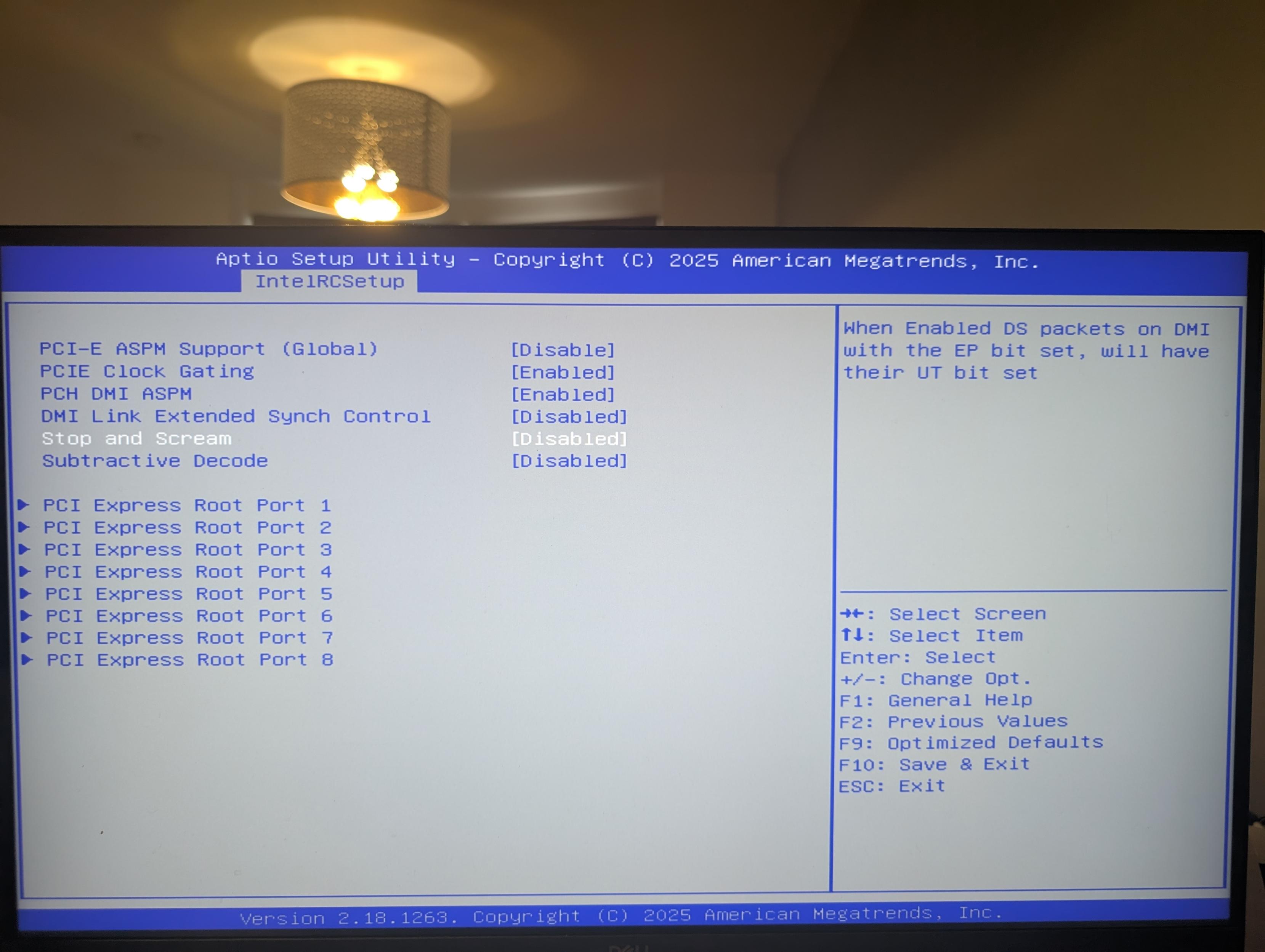
i found an explanation (or what passes for an explanation) for the PCIe Stop & Scream option
what the fuck does this mean? ask someone smarter than I am
@whitequark Isn't that this song by OneRepublic?
-
@whitequark I should start a conspiracy theory that spread spectrum clocking and memory scrambling are evil attempts to decrease your performance by intel, and use this board to "prove" it
@artemist @whitequark need to try this along with gps disciplining the CPU clock like i did on a pi
-
@whitequark yeah i found this after and tbh it doesn't clear much up lol
-
@niconiconi @whitequark but that's Broadwell, just one generation before Skylake, surely its IPC is not _that_ low?
And the one they're giving out isn't even low-end, but 10-core. -
i found an explanation (or what passes for an explanation) for the PCIe Stop & Scream option
what the fuck does this mean? ask someone smarter than I am
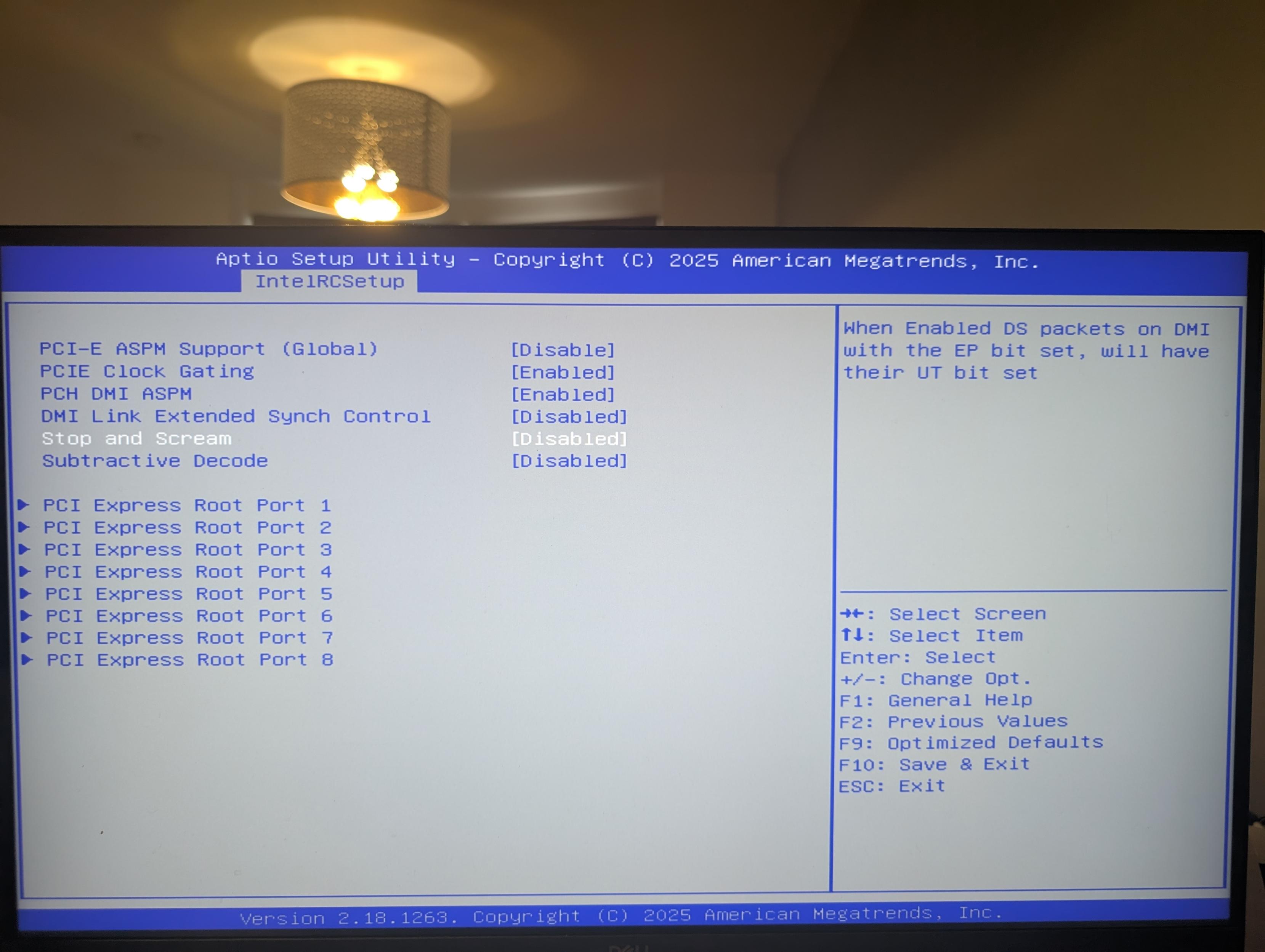
@whitequark The explanation in a random Intel chipset doc I found isn't that much better:
https://www.intel.com/content/dam/doc/datasheet/x58-express-chipset-datasheet.pdf
--
PCIe/DMI “Stop and Scream”
...per PCIe port
...disallow sending of poisoned data onto PCIe and instead convert disable the PCIe port that was the target of poisoned data
...there have been PCIe/DMI devices that have ignored the poison bit, and committed the data which can corrupt the I/O device
--So, disable PCIe port on error, instead of tagging data as poisoned. Nice name.
-
@whitequark The explanation in a random Intel chipset doc I found isn't that much better:
https://www.intel.com/content/dam/doc/datasheet/x58-express-chipset-datasheet.pdf
--
PCIe/DMI “Stop and Scream”
...per PCIe port
...disallow sending of poisoned data onto PCIe and instead convert disable the PCIe port that was the target of poisoned data
...there have been PCIe/DMI devices that have ignored the poison bit, and committed the data which can corrupt the I/O device
--So, disable PCIe port on error, instead of tagging data as poisoned. Nice name.
@jripley oh this makes sense!
-
@jripley oh this makes sense!
@whitequark I have yet to see an example of integrating PCIe, with data poisoning or not, where every edge case of error propagation can be safely accounted for. Presenting high-speed data buses directly to a CPU as addressable memory was a mistake (but we keep using PCIe nevertheless).
-
@whitequark I have yet to see an example of integrating PCIe, with data poisoning or not, where every edge case of error propagation can be safely accounted for. Presenting high-speed data buses directly to a CPU as addressable memory was a mistake (but we keep using PCIe nevertheless).
@jripley @whitequark ohhh I bet RC stands for Root Complex
-
@jripley @whitequark ohhh I bet RC stands for Root Complex
-
@niconiconi @whitequark meanwhile me with C3958 I paid $700 for (including the motherboard)

Although I guess it might be a bit faster than E5-2630 v4 in multi-threading scenarios, and its TDP is also much lower...
-
@niconiconi @whitequark meanwhile me with C3958 I paid $700 for (including the motherboard)

Although I guess it might be a bit faster than E5-2630 v4 in multi-threading scenarios, and its TDP is also much lower...
@niconiconi @whitequark But also, where do you have so many xeons from? It's not like Intel produced billions of them?
-
you can disable GPIO lockdown!
there's a function that prevents malicious UEFI Flash wearout, a type of attack I have not considered before. also you can turn it off
you can set UEFI boot stage breakpoints!@whitequark Flash wearout attacks are something server folks are concerned about. The imagined scenario is someone gains privileged access to your fleet, and turns them into a set of bricks which are impractical to fix at that scale.
This one I always categorized as "threat actor has capabilities conveniently advanced enough to pull this off, but conveniently not advanced enough to bypass your proposed mitigations". Or that there are countless other ways to brick a server.
-
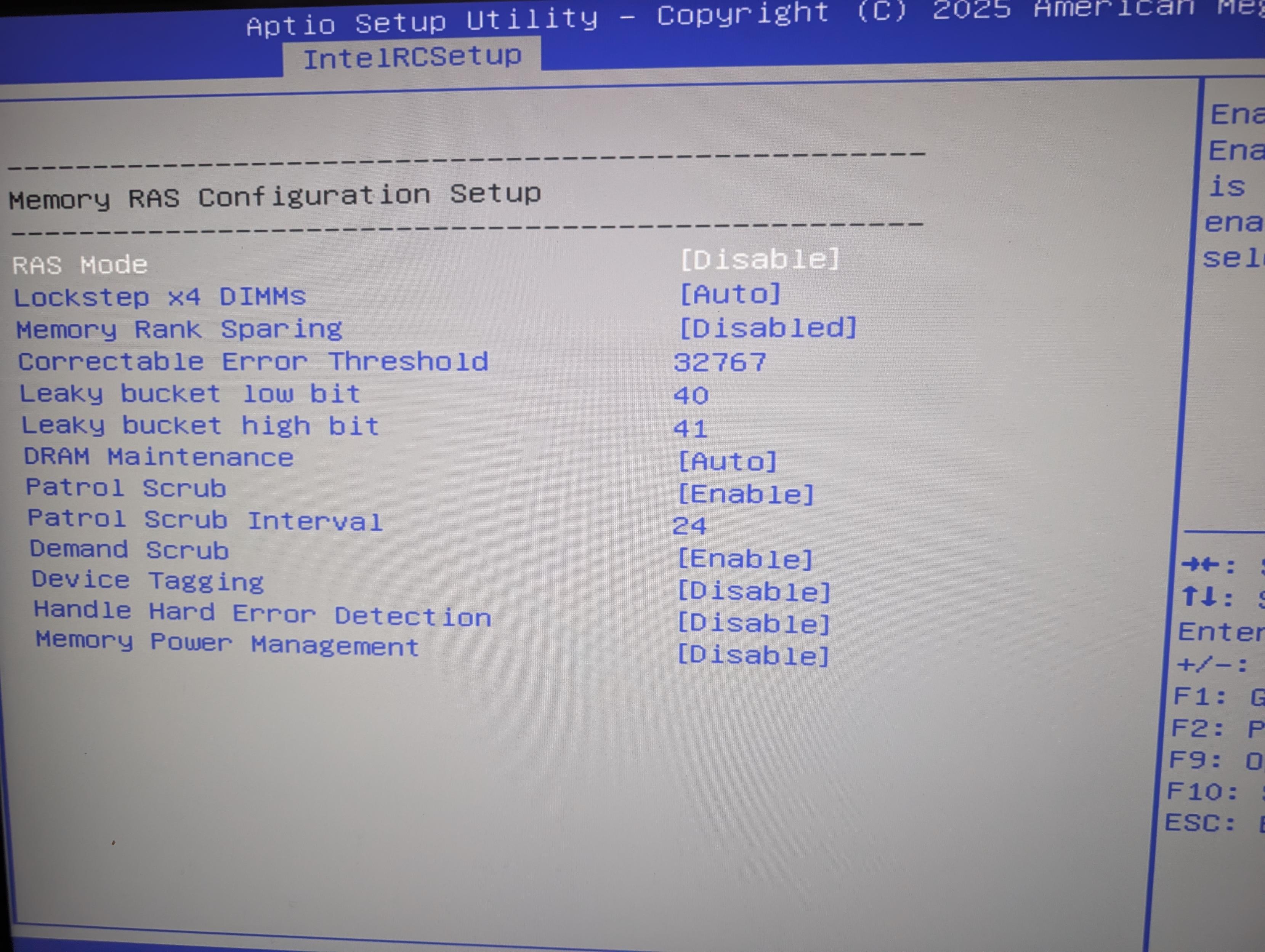
when you open the IntelRCSetup (what's RC?) the setup utility tells you "if you change some of these settings the system may malfunction"
that's an understatement of the year
@whitequark Reference Code, which I suppose means FSP. Which is why I'm pretty sure _all_ boards start out with all those options present, and then the dostawcy go and hide them.
-
@whitequark Reference Code, which I suppose means FSP. Which is why I'm pretty sure _all_ boards start out with all those options present, and then the dostawcy go and hide them.
@vmp_ ahh, makes sense
-
@whitequark Flash wearout attacks are something server folks are concerned about. The imagined scenario is someone gains privileged access to your fleet, and turns them into a set of bricks which are impractical to fix at that scale.
This one I always categorized as "threat actor has capabilities conveniently advanced enough to pull this off, but conveniently not advanced enough to bypass your proposed mitigations". Or that there are countless other ways to brick a server.
@jripley yeah, that's what baffles me
-
@niconiconi @whitequark but that's _a lot_ of them.
-
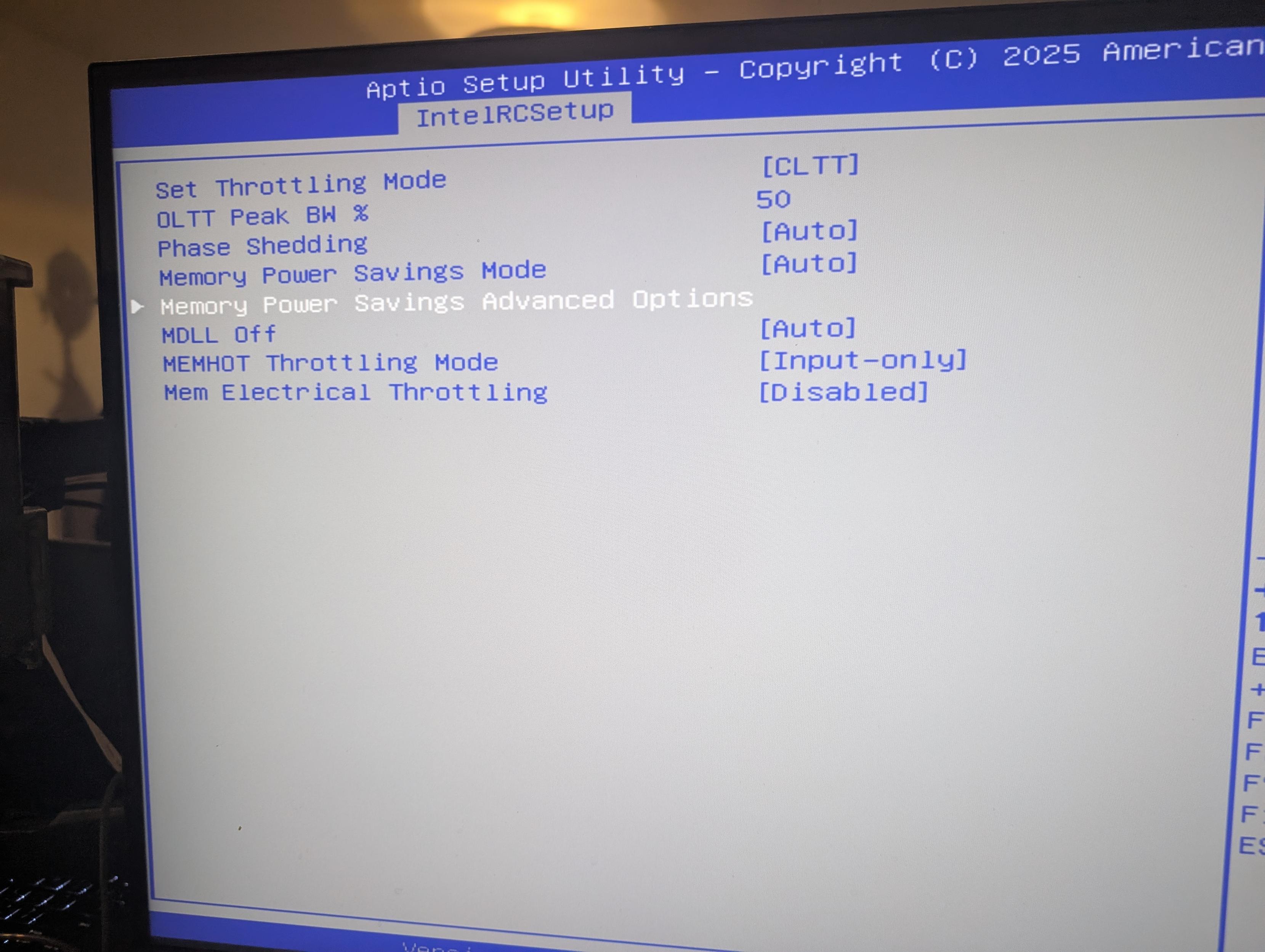
heyyyyyy. check this out
i bought one of those chinese motherboards which get the UEFI package from American Megatrends and then enable options with the guiding principle of "YES."
check out how many juicy bits it has
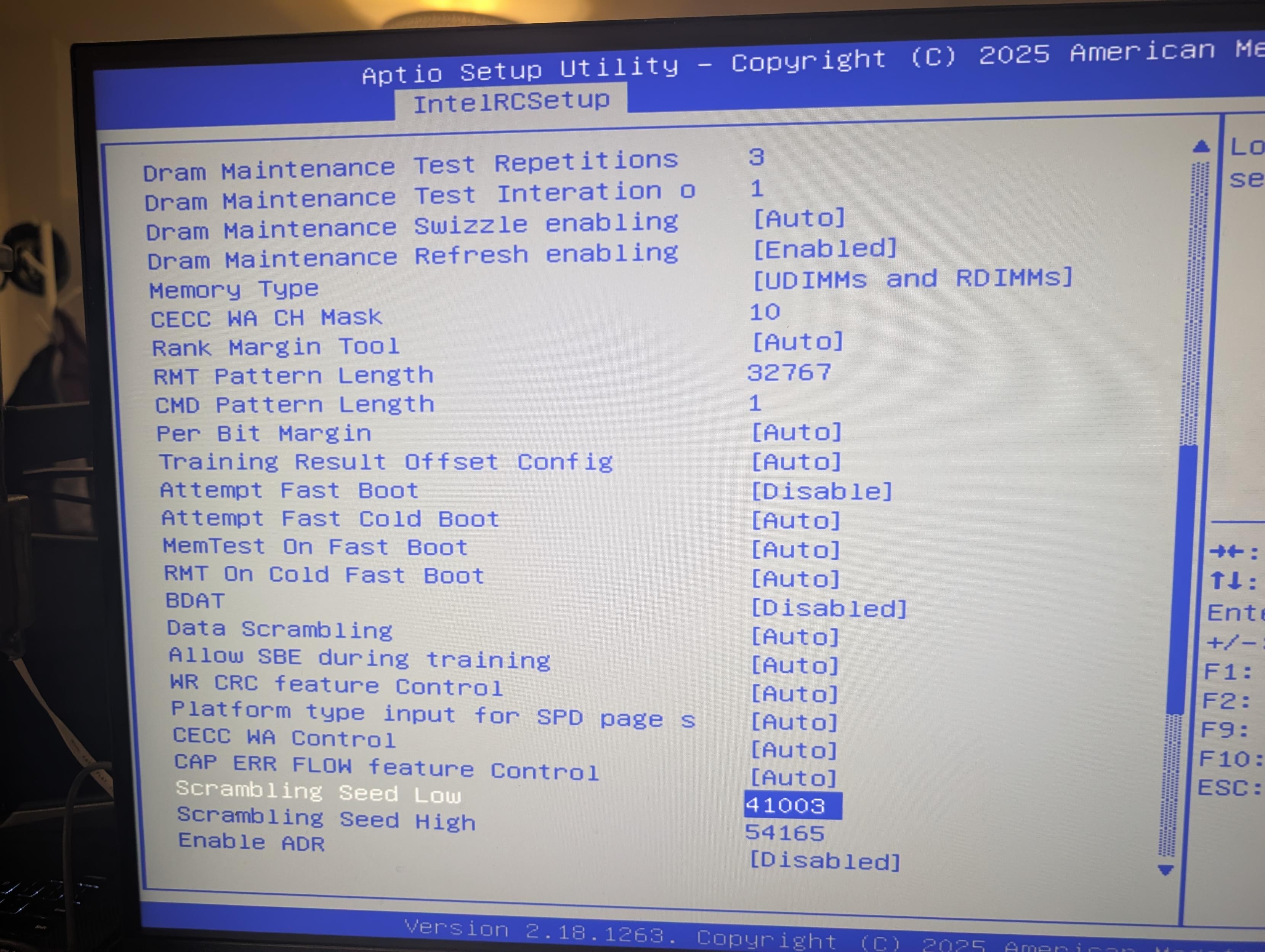
you can turn the memory scrambler on and off! it even tells you the seed it has on, i think, this specific boot?
How much power does it draw idle/loaded?