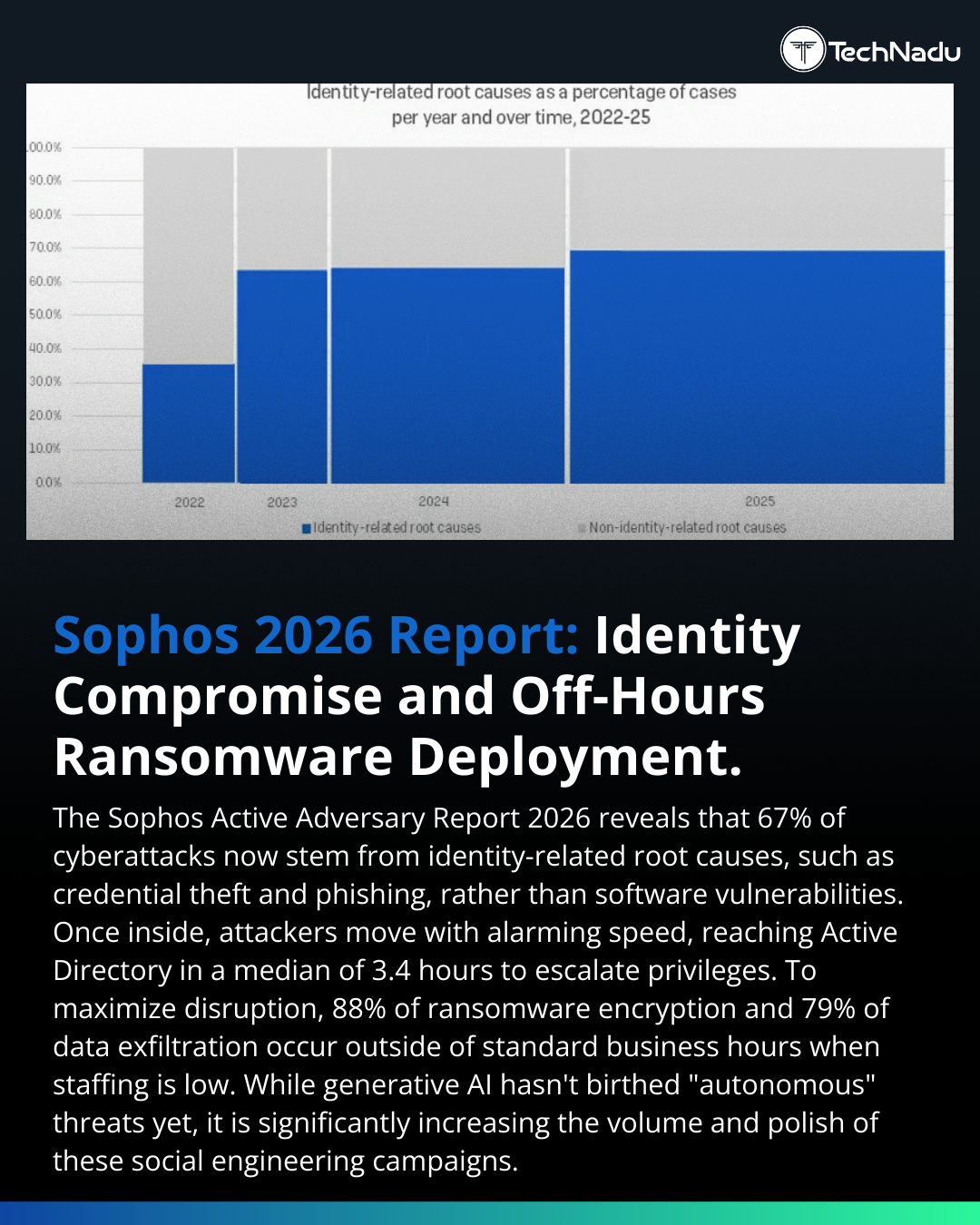
Identity compromise continues to dominate intrusion chains
-
Identity compromise continues to dominate intrusion chains.
From the Sophos Active Adversary Report 2026:
• 67% of initial access attributed to identity abuse
• 3.4-hour median to Active Directory pivot
• 3-day median dwell time
• 88% ransomware deployment off-hours
• 79% data exfiltration off-hours
Directory services remain high-value assets — authentication, authorization, policy control, privilege mapping.
The compressed timeline from credential misuse to directory-level access underscores the need for:
– Continuous identity monitoring
– Behavioral analytics
– After-hours SOC coverage
– Conditional access enforcement
– Least-privilege architecture
Generative AI is functioning as a force multiplier — improving phishing quality and campaign scale - not yet delivering autonomous attack chains.Is identity governance keeping pace with adversary dwell time compression?
Engage below.Follow TechNadu for high-signal infosec analysis.
Repost to strengthen industry awareness.
#Infosec #IdentityThreats #RansomwareDefense #ActiveDirectorySecurity #ThreatModeling #GenAI #SecurityOperations #CyberRisk #ZeroTrustArchitecture #DetectionEngineering #EnterpriseSecurity #ThreatHunting
-
R relay@relay.infosec.exchange shared this topic
