I'm not super familiar with Red Hat, but can someone do a sanity check for me?
-
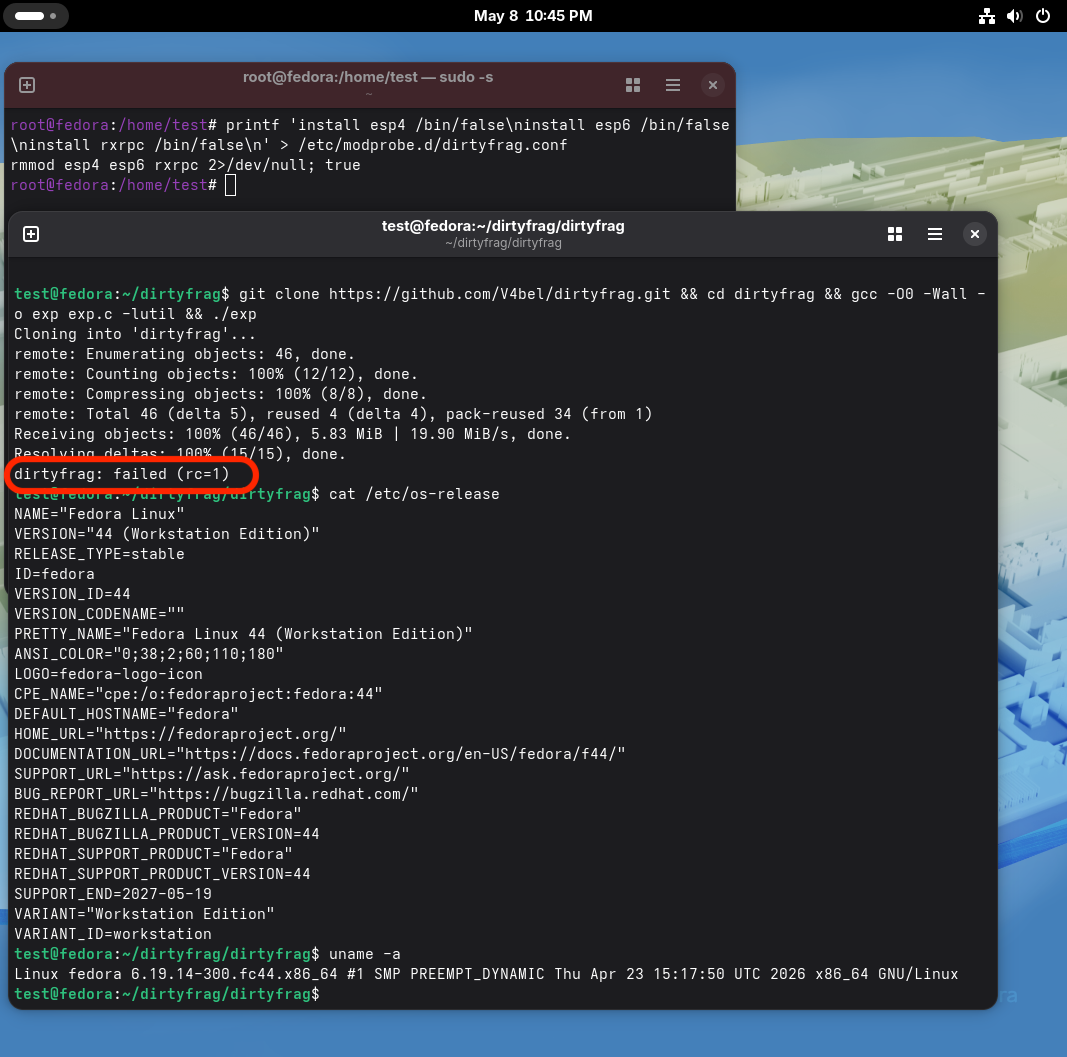
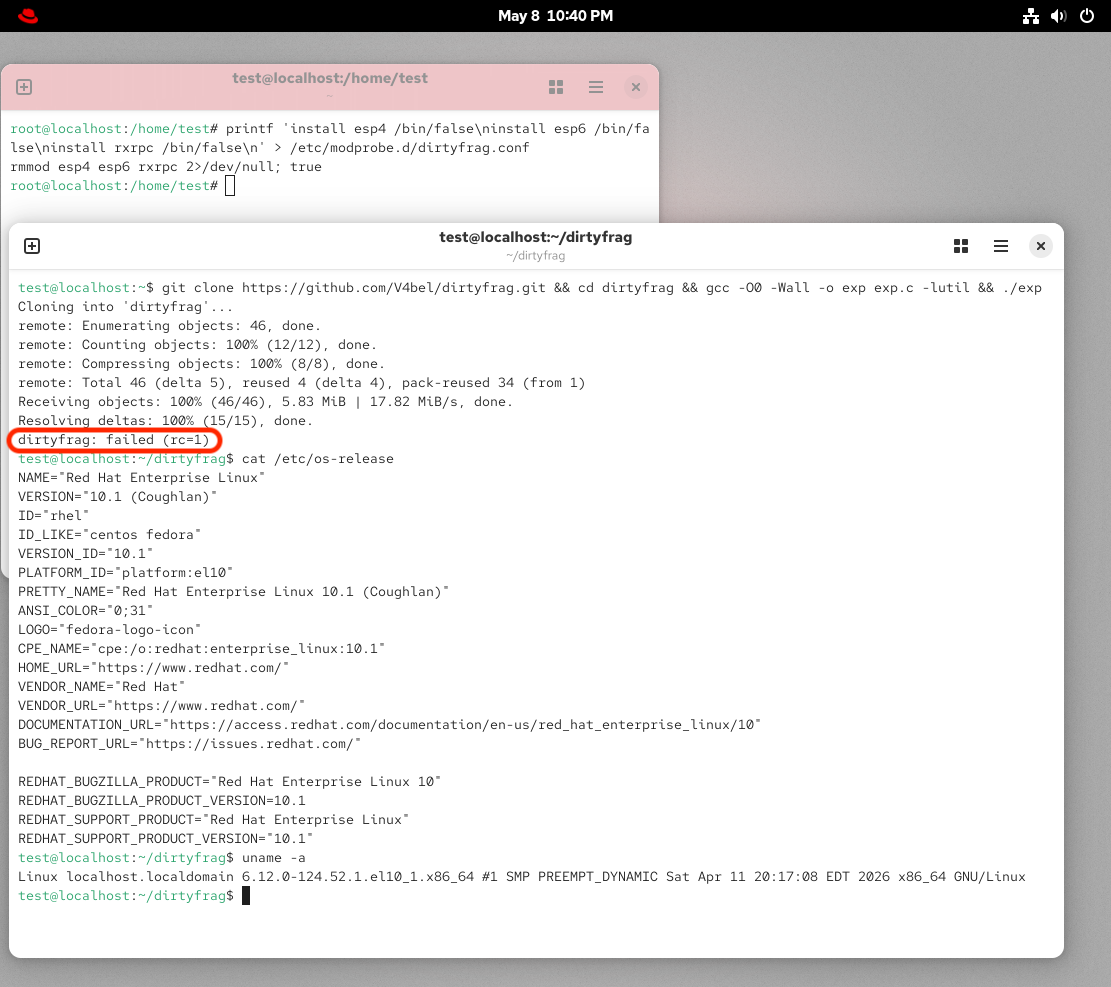
I'm not super familiar with Red Hat, but can someone do a sanity check for me? The recommended mitigation for DirtyFrag is to add the relevant modules to a modprobe blocklist. But...I wasn't aware the modules were loaded dynamically? At least on Fedora, they were not.
I very much want to be wrong about this. And expect I am, but want to be sure.
RHSB-2026-003 Networking subsystem Privilege Escalation - Linux Kernel (CVE-2026-43284, CVE-2026-43500, CVE-2026-46300) - Dirty Frag | Red Hat Customer Portal
Access Red Hat’s knowledge, guidance, and support through your subscription.
Red Hat Customer Portal (access.redhat.com)
-
I'm not super familiar with Red Hat, but can someone do a sanity check for me? The recommended mitigation for DirtyFrag is to add the relevant modules to a modprobe blocklist. But...I wasn't aware the modules were loaded dynamically? At least on Fedora, they were not.
I very much want to be wrong about this. And expect I am, but want to be sure.
RHSB-2026-003 Networking subsystem Privilege Escalation - Linux Kernel (CVE-2026-43284, CVE-2026-43500, CVE-2026-46300) - Dirty Frag | Red Hat Customer Portal
Access Red Hat’s knowledge, guidance, and support through your subscription.
Red Hat Customer Portal (access.redhat.com)
@mttaggart
The Red Hat mitigation works fine for protecting both Red Hat and Fedora.