In today's episode of "Can It Run Doom": DNS fucking TXT records.
-
@k3ym0 new cloud storage just dropped
-
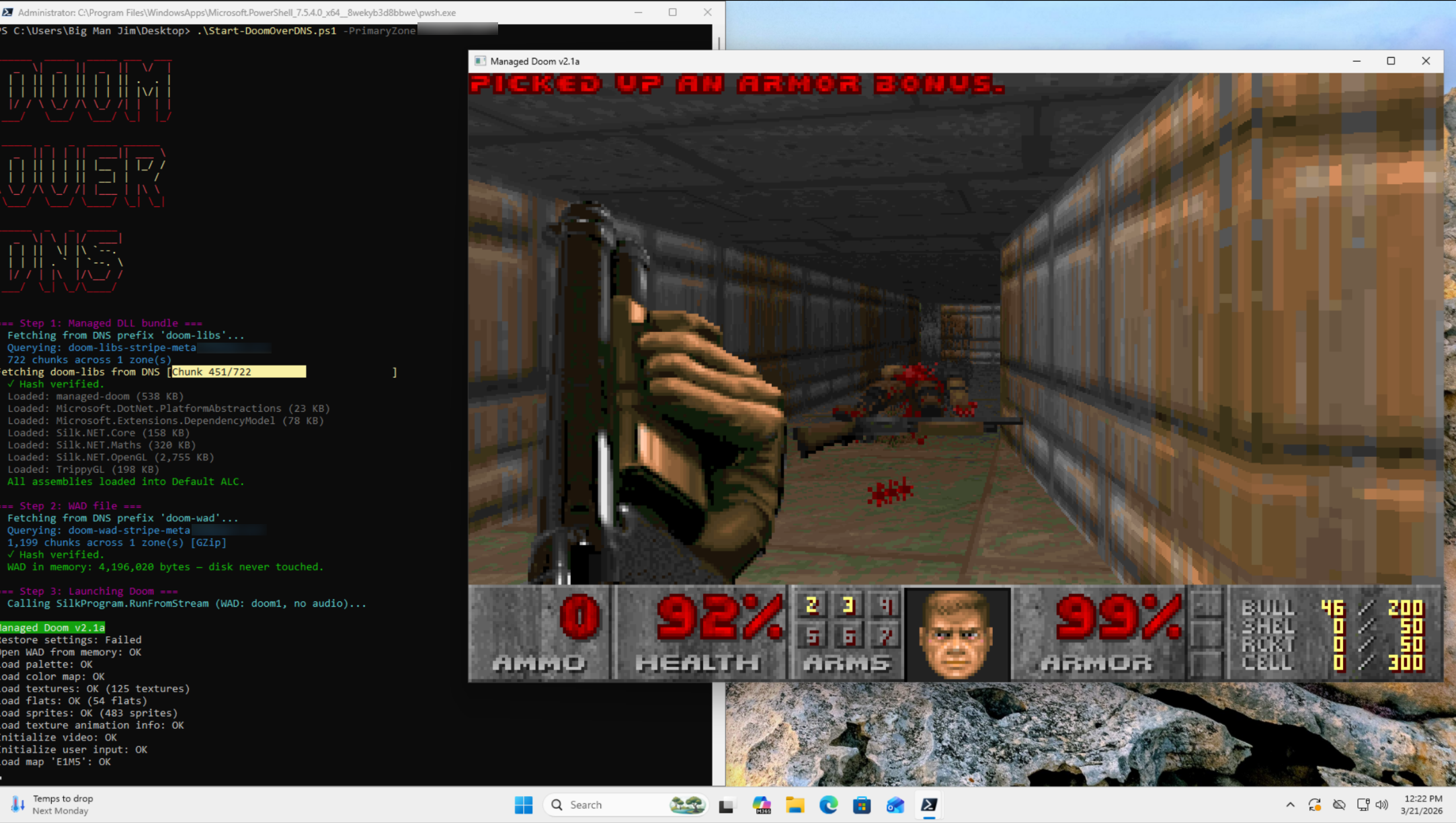
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
-
 M mrmasterkeyboard@mastodon.social shared this topic
M mrmasterkeyboard@mastodon.social shared this topic
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 you may already know this, but on a related note you can tunnel basically any IPv4 traffic over DNS: https://code.kryo.se/iodine/
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0
IP over DNS has been a thing for a while now, sometimes used to bypass captive portals for paid internet access -
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 Doom Network Service

-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 shit. Time to do Bad Apple on DNS.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 The concept is very old, I was using dns2tcp to have free wifi on plane trips in 2010 and even before during pentests. Long TXT replies trigger red alerts on most intrusion detection systems nowadays.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 now... can it do deathmatch over doom over dns? :3
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 For quite a loose definition of "run".
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0
> covert data exfil channelas if iodine wasn't already a thing
-
@k3ym0 Doom Network Service

@simondassow Doom-aaS?
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 "good luck if you're not doing deep DNS inspection"
iodine, dnscat, and literally every other DNS tunneling technique that has existed in the past 20-ish years: lol. lmao, even.
Still, quite impressive, but saying this shit is a hard to detect covert channel is unmitigated bullshit.
-
@k3ym0 "good luck if you're not doing deep DNS inspection"
iodine, dnscat, and literally every other DNS tunneling technique that has existed in the past 20-ish years: lol. lmao, even.
Still, quite impressive, but saying this shit is a hard to detect covert channel is unmitigated bullshit.
@da_667 iodine and dnscat also have 20 years of signatures, known patterns, and detection logic baked into tooling. This doesn't.
But honestly that's beside the point. "Detectable" and "detected" are two very different sentences. iodine has been detectable for 20 years and I've watched it walk right out of enterprise networks that had no idea. Known technique != mature detection coverage in the median org.
SMB's are running Server 2008r2 with a Watchguard FW and a prayer. Mid-market is logging DNS at the firewall level and calling it done.
"Detectable in theory by a mature SOC" and "hard to detect in most real environments" are not mutually exclusive statements.
-
@da_667 iodine and dnscat also have 20 years of signatures, known patterns, and detection logic baked into tooling. This doesn't.
But honestly that's beside the point. "Detectable" and "detected" are two very different sentences. iodine has been detectable for 20 years and I've watched it walk right out of enterprise networks that had no idea. Known technique != mature detection coverage in the median org.
SMB's are running Server 2008r2 with a Watchguard FW and a prayer. Mid-market is logging DNS at the firewall level and calling it done.
"Detectable in theory by a mature SOC" and "hard to detect in most real environments" are not mutually exclusive statements.
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0@infosec.exchange DNS haiku just got a lot bloodier... -
-
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: https://blog.rice.is/post/doom-over-dns/
repo: https://github.com/resumex/doom-over-dns
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
@k3ym0 I used to have the entire text of the Magna Carta in TXT records in a subdomain.
Even during the early 1990's on the Interop show networks we discovered people streaming lewd stuff via DNS-looking UDP packets.
(Another channel that we used, but it only works on a LAN, is to use the space between the end of a short IP packet and the end of the enclosing Ethernet frame. [Short IP packets are smaller than the minimum size of Ethernet frames.] This was largely used for license key exchanges.)
-
@da_667 iodine and dnscat also have 20 years of signatures, known patterns, and detection logic baked into tooling. This doesn't.
But honestly that's beside the point. "Detectable" and "detected" are two very different sentences. iodine has been detectable for 20 years and I've watched it walk right out of enterprise networks that had no idea. Known technique != mature detection coverage in the median org.
SMB's are running Server 2008r2 with a Watchguard FW and a prayer. Mid-market is logging DNS at the firewall level and calling it done.
"Detectable in theory by a mature SOC" and "hard to detect in most real environments" are not mutually exclusive statements.
Yeah, I tend to agree with this take. Reliably catching techniques like DNS tunneling, DGA, etc., looks trivial until you try it on noisy real world networks with all sorts of idiosyncratic constraints, and also when you realize that what we consider "trivial" is often considered "impractical" or "impossible" for most real world orgs.