RE: https://infosec.exchange/@teriradichel/116438438680583186
You can architect a solution that uses AI without giving it all your credentials. Here’s how.
RE: https://infosec.exchange/@teriradichel/116438438680583186
You can architect a solution that uses AI without giving it all your credentials. Here’s how.
This post is not about Mythos capabilities because I can’t know until I try it. Opus 4.6 was great until it changed and I presume Mythos is better.
This post is more about the economics of AI models and the risks we face trying to rely on them as business owners.
How do you know if and when the model has changed in some way as you are using it? How do you measure value per token? What if value per token changes?
Using AI has been amazing but there are some serious questions to consider beyond model capabilities when it comes to business and cybersecurity risk with any AI model. I haven’t heard anyone else asking these questions - or answering them.
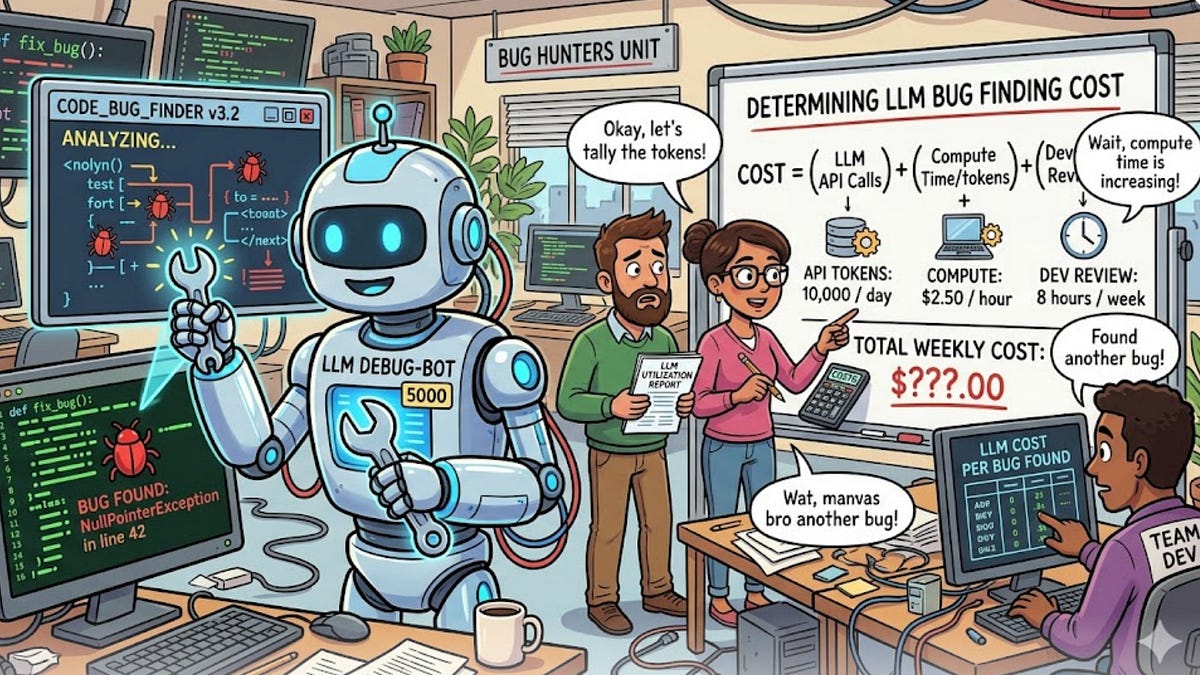
Anthropic released a new model they claim is scary good at finding security vulnerabilities. What questions should we be asking?
(teriradichel.substack.com)
This post is not about Mythos capabilities because I can’t know until I try it. Opus 4.6 was great until it changed and I presume Mythos is better.
This post is more about the economics of AI models and the risks we face trying to rely on them as business owners.
How do you know if and when the model has changed in some way as you are using it? How do you measure value per token? What if value per token changes?
Using AI has been amazing but there are some serious questions to consider beyond model capabilities when it comes to business and cybersecurity risk with any AI model. I haven’t heard anyone else asking these questions - or answering them.
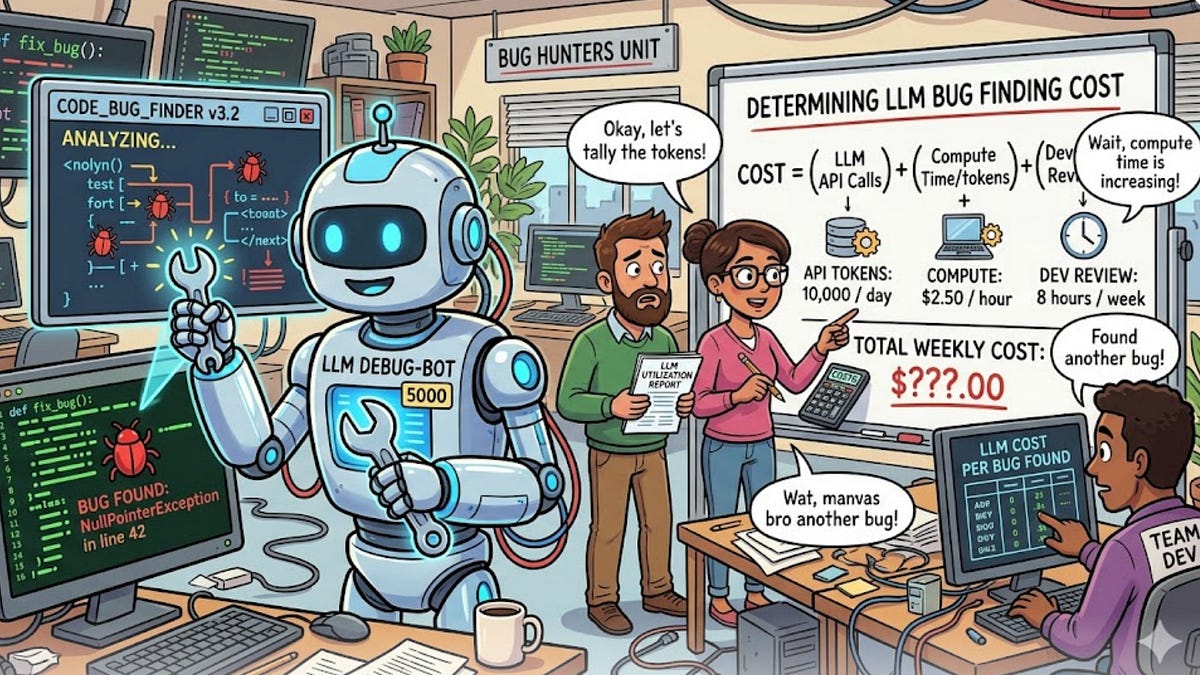
Anthropic released a new model they claim is scary good at finding security vulnerabilities. What questions should we be asking?
(teriradichel.substack.com)