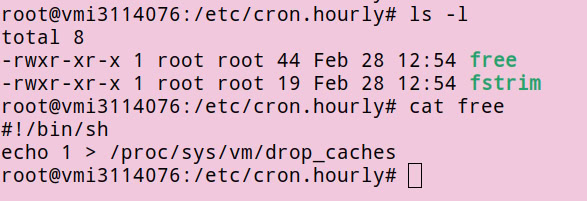
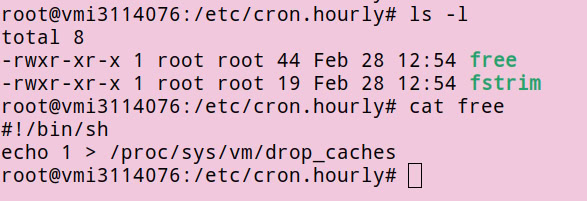
Today I realized that my Linux Contabo VPS has a built-in script in `/etc/cron.hourly` that drops the cache every hour.
-
Today I realized that my Linux Contabo VPS has a built-in script in `/etc/cron.hourly` that drops the cache every hour. I found it when I checked dmesg; there are so many "drop_caches: 1" lines.
I guess the memory is not dedicated, but shared via KVM memory ballooning.
It seems Contabo tries so hard to reclaim physical memory from its customers by dropping page caches every hour. I feel like Contabo is somewhat notorious for aggressive overprovisioning.
I will delete the `free` script.
#linux #contabo #mm #kvm #vps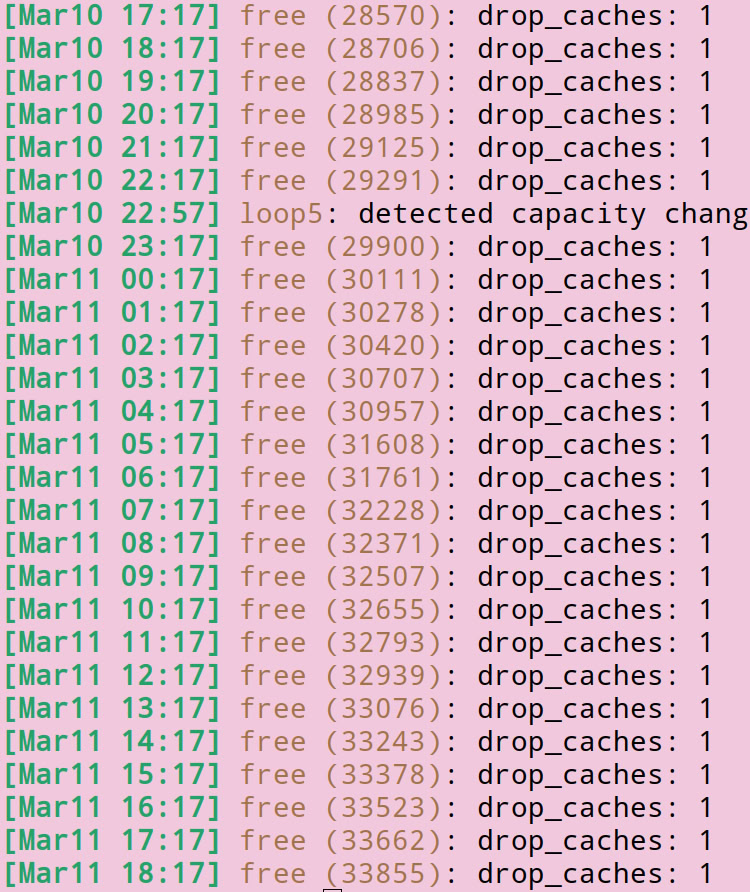
-
R relay@relay.publicsquare.global shared this topicR relay@relay.infosec.exchange shared this topic
-
Today I realized that my Linux Contabo VPS has a built-in script in `/etc/cron.hourly` that drops the cache every hour. I found it when I checked dmesg; there are so many "drop_caches: 1" lines.
I guess the memory is not dedicated, but shared via KVM memory ballooning.
It seems Contabo tries so hard to reclaim physical memory from its customers by dropping page caches every hour. I feel like Contabo is somewhat notorious for aggressive overprovisioning.
I will delete the `free` script.
#linux #contabo #mm #kvm #vps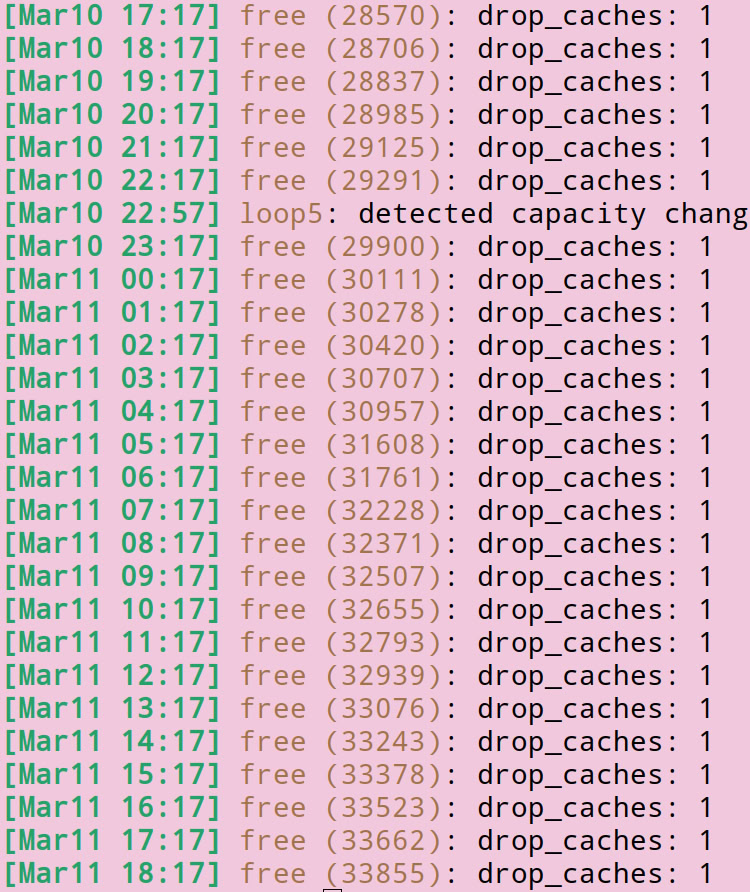
Interesting finding!
BTW, the KVM ballooning requires the host OS to cooperate with the guest OS. If you can modify your kernel so that it does not cooperate with the hypervisor, then the hypervisor can't steal the memory from you.
-
Interesting finding!
BTW, the KVM ballooning requires the host OS to cooperate with the guest OS. If you can modify your kernel so that it does not cooperate with the hypervisor, then the hypervisor can't steal the memory from you.
Try setting kernel cmdline `virtio_balloon.disable=1` or, if you compile your kernel yourself, drop it entirely with `CONFIG_VIRTIO_BALLOON=n`.
-
Try setting kernel cmdline `virtio_balloon.disable=1` or, if you compile your kernel yourself, drop it entirely with `CONFIG_VIRTIO_BALLOON=n`.
@ammarfaizi2@gnuweeb.org I tried to unbind the virtio balloon but hit by this <img class="not-responsive emoji" src="https://s.umeyashiki.org/emoji/stolen/blood_sob.webp" title=":blood_sob:" />
Command:
echo virtio0 > /sys/bus/virtio/drivers/virtio_balloon/unbinddmesg:
[ 264.557828] BUG: kernel NULL pointer dereference, address: 0000000000000008 [ 264.558955] #PF: supervisor read access in kernel mode [ 264.559786] #PF: error_code(0x0000) - not-present page -
@ammarfaizi2@gnuweeb.org I tried to unbind the virtio balloon but hit by this <img class="not-responsive emoji" src="https://s.umeyashiki.org/emoji/stolen/blood_sob.webp" title=":blood_sob:" />
Command:
echo virtio0 > /sys/bus/virtio/drivers/virtio_balloon/unbinddmesg:
[ 264.557828] BUG: kernel NULL pointer dereference, address: 0000000000000008 [ 264.558955] #PF: supervisor read access in kernel mode [ 264.559786] #PF: error_code(0x0000) - not-present pageLmao, you just hit a kernel bug. Can you show the full call trace?
-
Lmao, you just hit a kernel bug. Can you show the full call trace?
@ammarfaizi2@gnuweeb.org
[ 264.557828] BUG: kernel NULL pointer dereference, address: 0000000000000008 [ 264.558955] #PF: supervisor read access in kernel mode [ 264.559786] #PF: error_code(0x0000) - not-present page [ 264.561157] PGD 0 P4D 0 [ 264.561755] Oops: Oops: 0000 [#1] SMP [ 264.562402] CPU: 0 UID: 0 PID: 1345 Comm: bash Not tainted 6.19.3 #8 PREEMPT(none) 125ca1792cd5fca311f47992bbca238807cd563f [ 264.564488] Hardware name: QEMU Standard PC (i440FX + PIIX, 1996), BIOS rel-1.16.3-0-ga6ed6b701f0a-prebuilt.qemu.org 04/01/2014 [ 264.566384] RIP: 0010:__list_del_entry_valid_or_report+0x5/0xf0 [ 264.567431] Code: 89 d3 49 89 f6 e8 3b 6e c3 ff 49 8b 16 48 c7 c7 b3 c6 63 82 48 89 de 4c 89 f1 e8 56 87 91 ff 0f 0b cc cc cc cc 41 57 41 56 53 <48> 8b 1f 48 85 db 74 38 4c 8b 77 08 4d 85 f6 74 40 49 bf 00 01 00 [ 264.570484] RSP: 0018:ffff888147397ce8 EFLAGS: 00010046 [ 264.571511] RAX: 0000000000000246 RBX: ffff888101c8d800 RCX: 0000000000000001 [ 264.572673] RDX: 000000000080007e RSI: ffffea000404d600 RDI: 0000000000000008 [ 264.573930] RBP: ffff888101c8d800 R08: 0000000000000001 R09: 0000000000000a61 [ 264.576526] R10: 000000000000000f R11: 000000000000000a R12: 0000000000000246 [ 264.578620] R13: ffff888101c8db20 R14: 0000000000000000 R15: ffff888101c8db20 [ 264.579679] FS: 00007fc982d0f740(0000) GS:ffff8883a5c3d000(0000) knlGS:0000000000000000 [ 264.580905] CS: 0010 DS: 0000 ES: 0000 CR0: 0000000080050033 [ 264.582218] CR2: 0000000000000008 CR3: 0000000306c67000 CR4: 00000000003506f0 [ 264.583854] Call Trace: [ 264.585550] <TASK> [ 264.585994] vp_del_vqs+0x121/0x230 [ 264.587128] remove_common+0x135/0x150 [ 264.588097] virtballoon_remove+0xee/0x100 [ 264.589029] virtio_dev_remove+0x3b/0x80 [ 264.589895] device_release_driver_internal+0x187/0x2c0 [ 264.591266] unbind_store+0xb9/0xe0 [ 264.592142] kernfs_fop_write_iter.llvm.11660790530567441834+0xf6/0x180 [ 264.594328] vfs_write+0x2a9/0x3b0 [ 264.595265] ksys_write+0x5c/0xd0 [ 264.597236] do_syscall_64+0x54/0x230 [ 264.598679] entry_SYSCALL_64_after_hwframe+0x29/0x31 [ 264.599672] RIP: 0033:0x7fc982b14907 [ 264.600518] Code: 10 00 f7 d8 64 89 02 48 c7 c0 ff ff ff ff eb b7 0f 1f 00 f3 0f 1e fa 64 8b 04 25 18 00 00 00 85 c0 75 10 b8 01 00 00 00 0f 05 <48> 3d 00 f0 ff ff 77 51 c3 48 83 ec 28 48 89 54 24 18 48 89 74 24 [ 264.606759] RSP: 002b:00007fff4dd79878 EFLAGS: 00000246 ORIG_RAX: 0000000000000001 [ 264.608546] RAX: ffffffffffffffda RBX: 0000000000000008 RCX: 00007fc982b14907 [ 264.609910] RDX: 0000000000000008 RSI: 000056309e029220 RDI: 0000000000000001 [ 264.611500] RBP: 000056309e029220 R08: 00007fc982bd1460 R09: 000000007fffffff [ 264.612937] R10: 0000000000000000 R11: 0000000000000246 R12: 0000000000000008 [ 264.614527] R13: 00007fc982c1b780 R14: 00007fc982c17600 R15: 00007fc982c16a00 [ 264.615558] </TASK>
