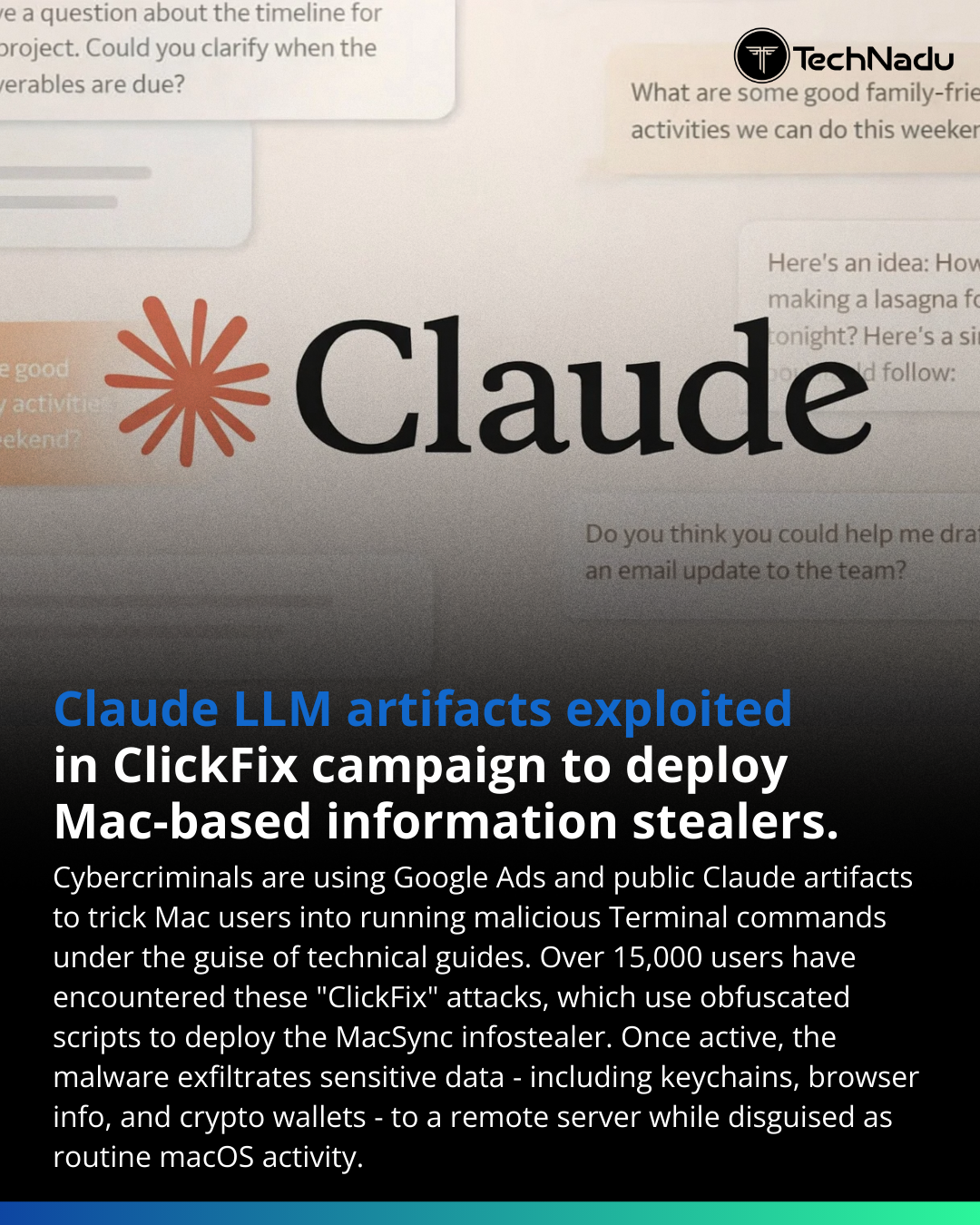
ClickFix campaigns are now leveraging LLM-generated public artifacts for malware distribution.
-
ClickFix campaigns are now leveraging LLM-generated public artifacts for malware distribution.
Per Moonlock Lab and AdGuard:
• Abuse of Claude artifact pages
• Google Ads search poisoning
• Obfuscated shell execution (base64 decode → zsh)
• Second-stage loader for MacSync infostealer
• Hardcoded API key + token-protected C2
• AppleScript (osascript) handling data theft
• Archive staging at /tmp/osalogging.zip
• Multi-attempt POST exfiltrationPrevious campaigns exploited ChatGPT and Grok sharing features.
LLM trust is now an operational risk vector.
Should EDR flag suspicious AI-guided shell patterns?Engage below.
Follow @technadu for deep technical threat analysis.#ThreatIntel #MacOSSecurity #Infostealer #C2Traffic #ClickFix #LLMSecurity #MalwareAnalysis #AppSec #BlueTeam #EDR #ThreatHunting #CyberThreats #ZeroTrust
-
R relay@relay.infosec.exchange shared this topic
