A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished.
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
-
R relay@relay.infosec.exchange shared this topicR relay@relay.mycrowd.ca shared this topicR relay@relay.publicsquare.global shared this topic
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
That's nasty.
I don't like it.
I used to ironically say the internet was a mistake, but some days lately my thoughts have shifted.
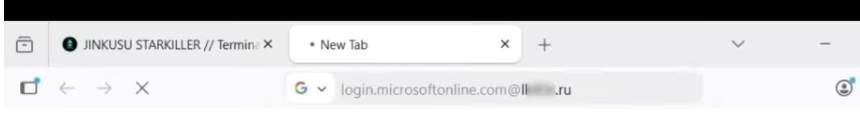
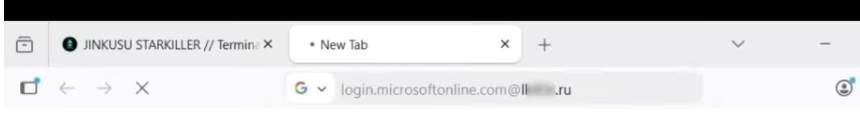
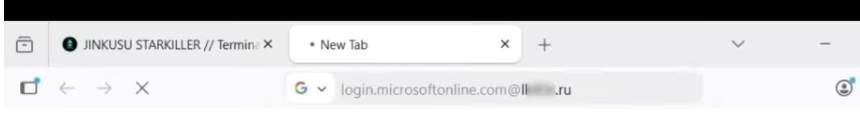
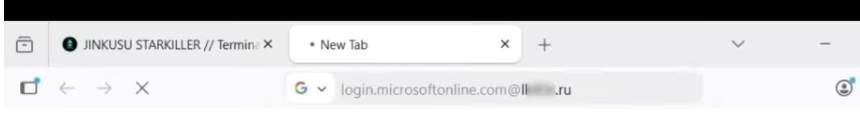
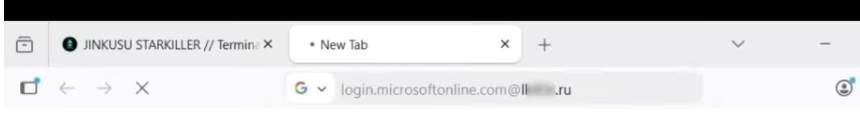
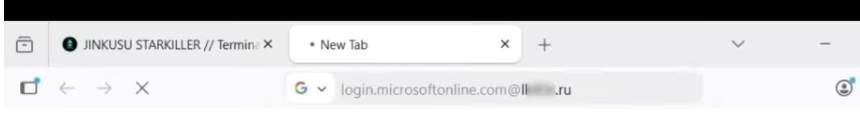
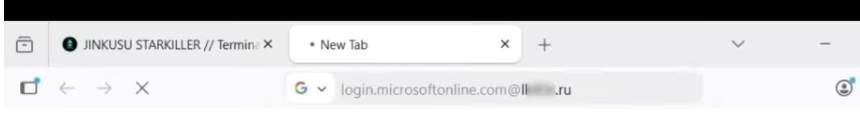
I feel like my browser at a minimum needs a behavior shift: if any @ is in the address bar, maybe the browser gives a warning & gives you a chance to look over the address before continuing.
Uhg, tummy ache activated.
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
@briankrebs I think I just ran into this tactic: I clicked on an MSNow story on youtube and it took me to a third party site that flat-out said "you're giving us your info" so I backed out quickly. The company name was something like 'vesuvis' or similar.
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
@briankrebs We need the list of sites identified as already being compromised with this
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
@briankrebs The term "MFA" is just useless as a metric for the security of a system. Just like 3DES, putting multiple broken auth mechanisms behind each other may work as a stop-gap measure but doesn't address the problem at its core.
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
@briankrebs would hosting our own dns like pihole defend against this?
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
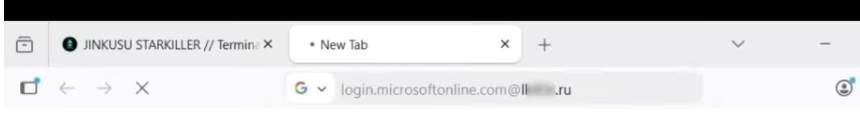
@briankrebs Huh, fascinating, I'm finding StackOverflow comments from 2014 that HTTP Basic Auth credentials in the URL will throw phising warnings in Safari... There was apparently some back and forth ongoing with the removal of this feature in multiple browsers

Can you pass user/pass for HTTP Basic Authentication in URL parameters?
I believe this is not possible, but someone I know insisted that it works. I don't even know what parameters to try, and I haven't found this documented anywhere. I tried http://myserver.com/~user=
Server Fault (serverfault.com)
I'm still a regular user of this feature, I hope it does not get removed.
-
A slick new phishing-as-a-service offering demonstrates just how easily a username+password and a one-time token can be phished. Dubbed "Starkiller," the service uses cleverly disguised links to load the target brand's real website, and then acts as a relay between the victim and the legitimate site -- forwarding the victim's username, password and multi-factor authentication code to the legitimate site and returning its responses.
@briankrebs Running into a sever error on the site, FYI.

