FakeWallet cryptostealer propagating via iOS App Store applications
Uncategorized
1
Posts
1
Posters
0
Views
-
FakeWallet cryptostealer propagating via iOS App Store applications
FakeWallet cryptostealer propagating via iOS App Store applications
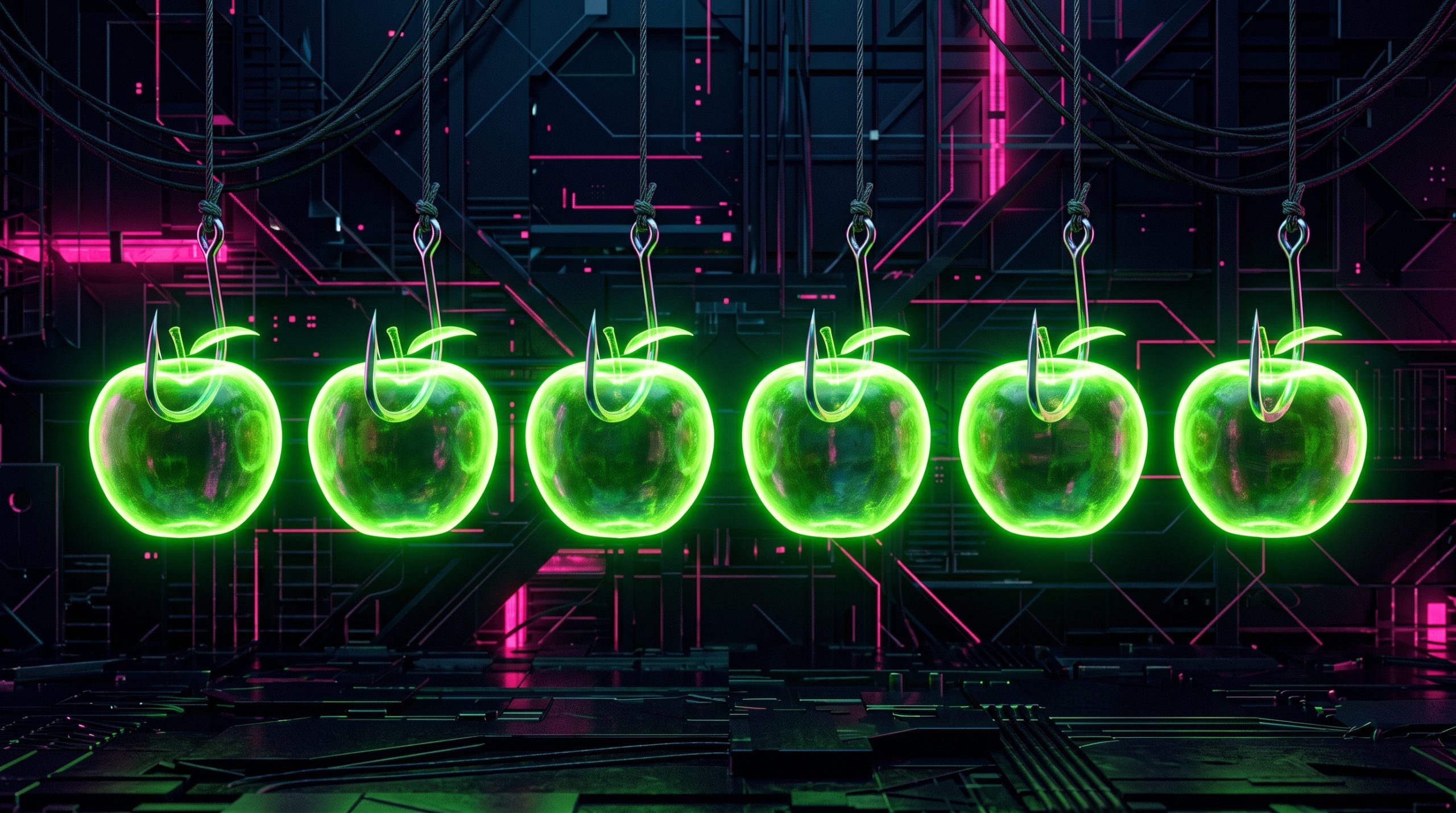
In March 2026, we uncovered more than twenty phishing apps in the Apple App Store masquerading as popular crypto wallets.

Securelist (securelist.com)
Read on HackerWorkspace: https://hackerworkspace.com/article/fakewallet-cryptostealer-propagating-via-ios-app-store-applications
-
R relay@relay.infosec.exchange shared this topic
