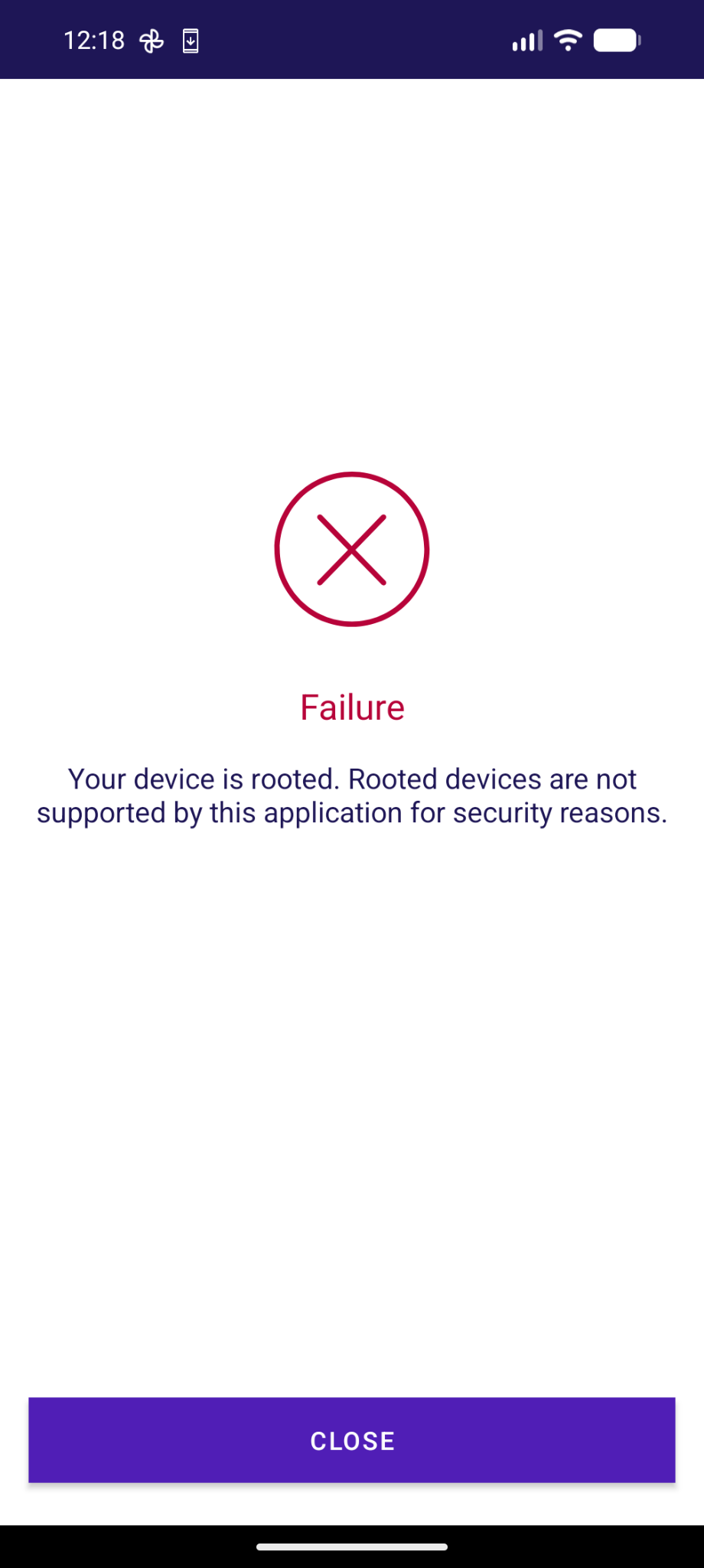
😡 So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht.
-
@toke @adfichter The apps are often region locked on the Play Store which can make it a pain to even obtain them for testing. We often can't trigger the checks because we lack a way to make an account and log into it. The apps are typically extremely obfuscated and doing all kinds of horrific things depending on internal OS implementation details including the layout of libc structs and much more. It's often difficult to determine what the apps are doing wrong and how we could work around it.
@toke @adfichter We've spent an enormous amount of time dealing with this stuff instead of working on improving privacy and security. Adding low-level hardening features for userspace is heavily held back by this since we need to retain near perfect compatibility with horribly written apps doing all kinds of incorrect things. It has substantially slowed down progress on GrapheneOS. Many features have had to be deferred and we have to put a lot of time into resolving rare compatibility issues.
-
@toke @adfichter We've spent an enormous amount of time dealing with this stuff instead of working on improving privacy and security. Adding low-level hardening features for userspace is heavily held back by this since we need to retain near perfect compatibility with horribly written apps doing all kinds of incorrect things. It has substantially slowed down progress on GrapheneOS. Many features have had to be deferred and we have to put a lot of time into resolving rare compatibility issues.
@toke @adfichter We haven't flipped the switch on enabling memory tagging by default for user installed apps since it uncovers an enormous number of memory corruption bugs. That's why that's an opt-in toggle in Settings > Security > Exploit protection instead of the default with reliance on per-app opt-out to deal with it. Memory tagging at least makes nice reports clearly showing it was caught by memory tagging. We could potentially put this into the setup wizard to explain it there.
-
@toke @adfichter We've spent an enormous amount of time dealing with this stuff instead of working on improving privacy and security. Adding low-level hardening features for userspace is heavily held back by this since we need to retain near perfect compatibility with horribly written apps doing all kinds of incorrect things. It has substantially slowed down progress on GrapheneOS. Many features have had to be deferred and we have to put a lot of time into resolving rare compatibility issues.
@GrapheneOS @toke @adfichter it's amazing google even allows this stuff (weird obfuscated security-theatre protection bullshit) in the play store if it constantly breaks on major android version updates -
 So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...
So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...Gestern an der interessanten Konferenz TRANSFORM zu Digital Public Infrastructure haben Bundeskanzlei, BAG-Vertreter:innen betont wie wichtig es sei, dass der Staat wie bei der Eisenbahn eine digitale hoheitliche Infrastruktur schafft (auch wenn sie von Privaten gebaut wird).
Digital ist das natürlich etwas schwieriger zu übersetzen, wegen Datenhaltung, Hardware, Software und technologischen Abhängigkeiten. Dennoch: der Big Tech-Zwang bei der Agov Access App ist eine absolute Frechheit. Nur für iOs und Android.
Zwar gelobt die Bundeskanzlei Besserung und will diese verfügbar machen für alternative Betriebssysteme. Ob die eID am 1.12.2026 für Nicht-iOS/Nicht-Android-Usern zur Verfügung stehen wird, das steht noch in den Sternen.
Es kann nicht sein dass man von digitaler öffentlicher Infrastruktur redet, jedoch alle Einwohner:innen dieses Landes nötigt das Big Tech-Duopol (von den man sich ja ironischerweise allgemein emanzipieren will) zu installieren.
@GrapheneOS One more app to add for your "Wall of Shame".
Mein Text dazu folgt am Montag.
(morgen kommt was zu Überwachung und VÜPF 2.0, kleiner Teaser;))
@adfichter @GrapheneOS I reached out to the agency providing the solution and to my surprise I got a nice reply that they acknowledge the need to support GrapheneOS and that they added it to the backlog of the company developing the app! They couldn't commit to a timeline, however.
Feel free to DM me if you want more details. -
@adfichter @GrapheneOS I reached out to the agency providing the solution and to my surprise I got a nice reply that they acknowledge the need to support GrapheneOS and that they added it to the backlog of the company developing the app! They couldn't commit to a timeline, however.
Feel free to DM me if you want more details.@ridedontslide @adfichter We can likely work around the issue ourselves. We know it's caused by the app being incompatible with our secure spawning feature and we already know the main issue with these anti-tampering SDKs which is causing compatibility issues. We need to figure out how to work around it. There's a high chance working around the issue we know about will solve it. It's possible to disable secure spawning to use the app but we don't recommend that.
GrapheneOS (@GrapheneOS@grapheneos.social)
@adfichter@infosec.exchange This app works on GrapheneOS with the exploit protection compatibility mode disabled and secure spawning disabled. The app does incorrect anti-tampering checks which are incompatible with our secure spawning feature due to it causing small differences in the address space and properties checked by their anti-tampering. The exploit protection compatibility mode has to force enable secure spawning to disable hardened_malloc and the 48-bit address space so it has to be disabled.

GrapheneOS Mastodon (grapheneos.social)
-
@adfichter Disabling secure spawning reverts to the standard Android Zygote-based spawning model where apps start as clones of the Zygote address space and memory. The Zygote spawning model reduces security by sharing the same state for probabilistic exploit protections including hardware memory tagging (MTE), ASLR, heap canaries, heap randomization and more. Android has a workaround to avoid weakening the security of stack canaries (SSP) but the rest can't really be worked around for it.
@GrapheneOS thanks a lot for all the answers. I will wait for the new version which should work on GrapheneOS. What are the risks by disable secure spawning?
-
R relay@relay.infosec.exchange shared this topic
