Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically 👏.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
-
@merill in other words, devices that the users control, instead of controlled by someone in the Epstein files
You can opt out any time by showing documentation that you are in the files (tangentially mentioned because they cited your work in an email does not count sorry)
-
@merill in other words, devices that the users control, instead of controlled by someone in the Epstein files
@fluffykittycat @merill It's kind of a grey area. They are right that open bootloaders are a security issue but then also you can relock it on some devices.
In any case I don't think I would use the Microsoft Authentication app anyway unless I have to. -
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
Hmm, I would never in my life install any M$ crap on my /e/OS ungoogled Fairphone. It's not rooted, but I guess it's also among the undesirables...
For authentication to our goddamn work accounts on M$, I use AEGIS. Or the standard authenticator on Linux Mint. Export/Import between the two works like a charm.
And it could well be that we are moving away from microslob in the not so far future. Unthinkable not so long ago. Halleluja!
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill Thank you for sabotaging my devices.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill I'm gonna go out on a limb here and say that users that jailbreak their own private device wouldn't use MS Authenticator, and on company devices jailbreak wasn't allowed anyway.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill Blanket bans of any sort implemented by large and powerful companies always produce false positives that hurt non-customer that have to interact with their systems no matter how obliquely.
I do not use any Microsoft product or services directly but I am sure I will discover ways that this change will affect me. Likely at a moment I need to do something urgently.
Never forget Scunthorpe!
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill wow cringe -
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill people making a mountain from a molehill? On Mastodon? Never expected it…
Yes, it’s shitty. But:
- You can do non-Authenticator passkeys now, from other apps that you can use on non-Android devices
- If device-bound, Authenticator native passkeys are forced on your work device, you did not had a say in the matter already.
- If device-bound passkeys are mandated on your personal device, reject the use of work apps on your personal devices and get a security key instead!
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
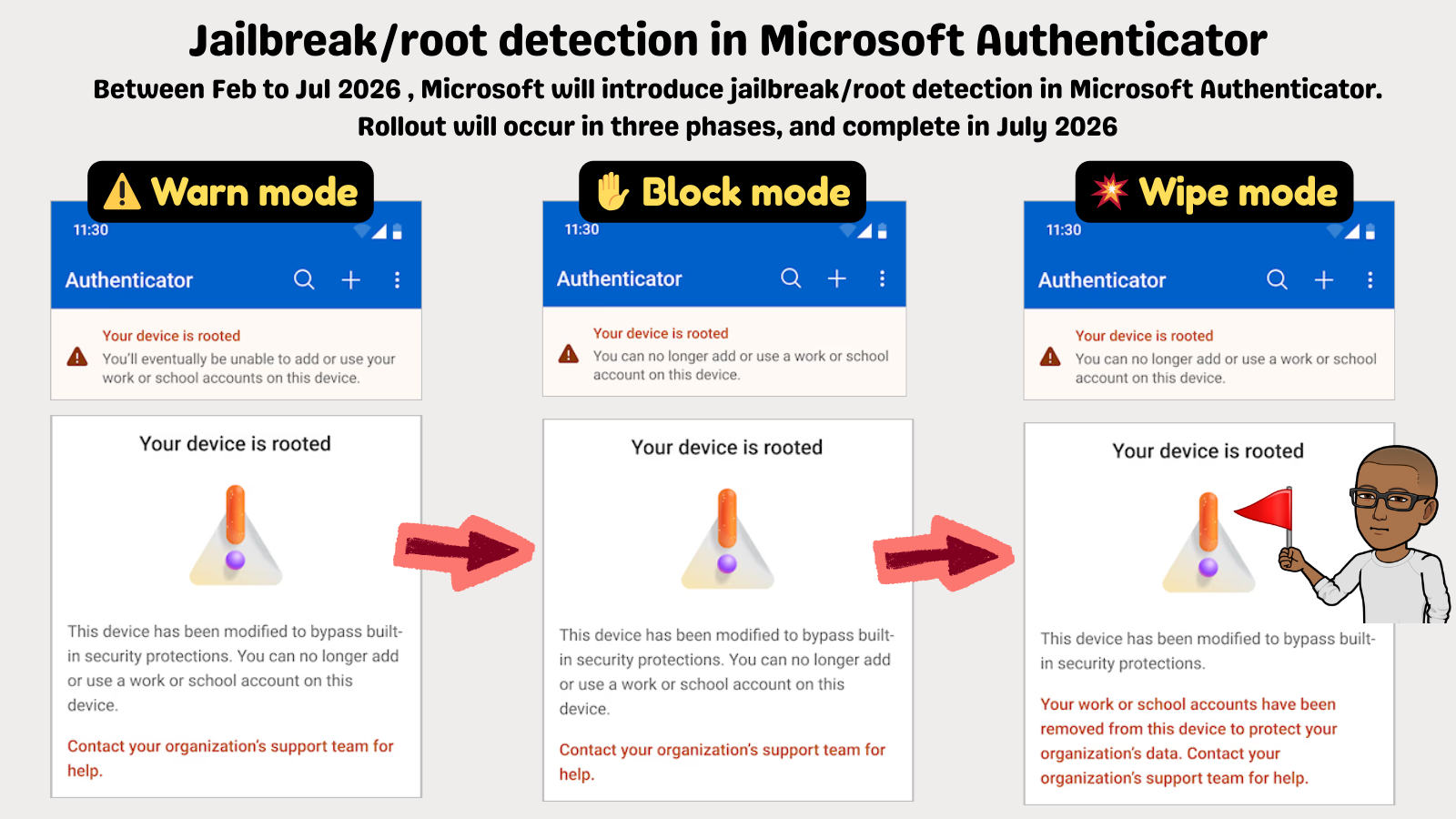
Jailbreak/root detection in Microsoft Authenticator.
Between Feb to Jul 2026, Microsoft will introduce jailbreak/root detection in Microsoft Authenticator. Rollout will occur in three phases, and complete in July 2026.Warn mode:
Your device is rooted.
You'll eventually be unable to add or use your work or school accounts on this device.
This device has been modified to bypass built-in security protections. You can no longer add or use a work or school account on this device
Contact your organization's support team for help.Block mode:
Your device is rooted.
You can no longer add or use a work or school account on this device.
This device has been modified to bypass built-in security protections. You can no longer add or use a work or school account on this device.
Contact your organization's support team for help.Wipe mode:
Your device is rooted.
You can no longer add or use a work or school account on this device.
This device has been modified to bypass built-in security protections.
Your work or school accounts have been removed from this device to protect your organization's data. Contact your organization's support team for help. -
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill TIL people actually use the MS authenticator
-
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
@merill lol!
-
R relay@relay.an.exchange shared this topic
-
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
@merill You just told a bunch of power users they either need to either relinquish control of their personal devices or start carrying a second device. Why did you think they'd be anything other than unhappy?
-
@fluffykittycat @merill It's kind of a grey area. They are right that open bootloaders are a security issue but then also you can relock it on some devices.
In any case I don't think I would use the Microsoft Authentication app anyway unless I have to.@thaodan @fluffykittycat @merill Why?
The keys and such associated with the authenticator app should be in a TPM. Something the bootloader can't touch. It can't get the private key to then send it to whoever.
The bootloader could attack in other ways and get the info you're accessing once logged in, but I don't think it can mess about or bypass the actual security mechanism.
I think they're trying to sell bullshit here so the ignorant support them as they lock us all down.
-
@thaodan @fluffykittycat @merill Why?
The keys and such associated with the authenticator app should be in a TPM. Something the bootloader can't touch. It can't get the private key to then send it to whoever.
The bootloader could attack in other ways and get the info you're accessing once logged in, but I don't think it can mess about or bypass the actual security mechanism.
I think they're trying to sell bullshit here so the ignorant support them as they lock us all down.
@thaodan @fluffykittycat @merill On phones without a TPM that's obviously not the case, but there are fewer and fewer of those and will be fewer still.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill what exactly is the threat model that makes a rooted device risky for an authenticator app?
-
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
@merill The orgs won't allow employees to use anything else, and you know it. Sadly you are not the first to require non rooted devices, but it is still another step back for freedom and privacy. Let us use our general computing pocket device as we wish. Or at least allow orgs to toggle the need for this. Though most will just enable it without question.
-
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
@merill tell that to my org that only allows the authenticator app.
-
@merill what exactly is the threat model that makes a rooted device risky for an authenticator app?
-
@thaodan @fluffykittycat @merill Why?
The keys and such associated with the authenticator app should be in a TPM. Something the bootloader can't touch. It can't get the private key to then send it to whoever.
The bootloader could attack in other ways and get the info you're accessing once logged in, but I don't think it can mess about or bypass the actual security mechanism.
I think they're trying to sell bullshit here so the ignorant support them as they lock us all down.
@crazyeddie @fluffykittycat @merill The bootloader itself isn't the concern but the kernel and what is started afterwards.
It is a factor even if they only use it as an excuse. Most phones don't have a TPM but an ARM trustzone which can run a software TPM. The problem is that modifying or writing isn't possible low level only over the OS or vendor API's provided.