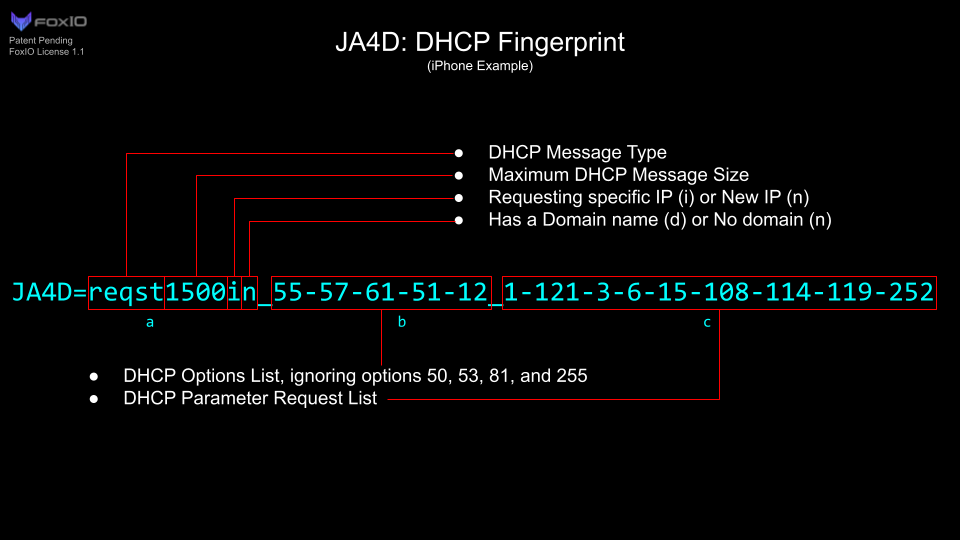
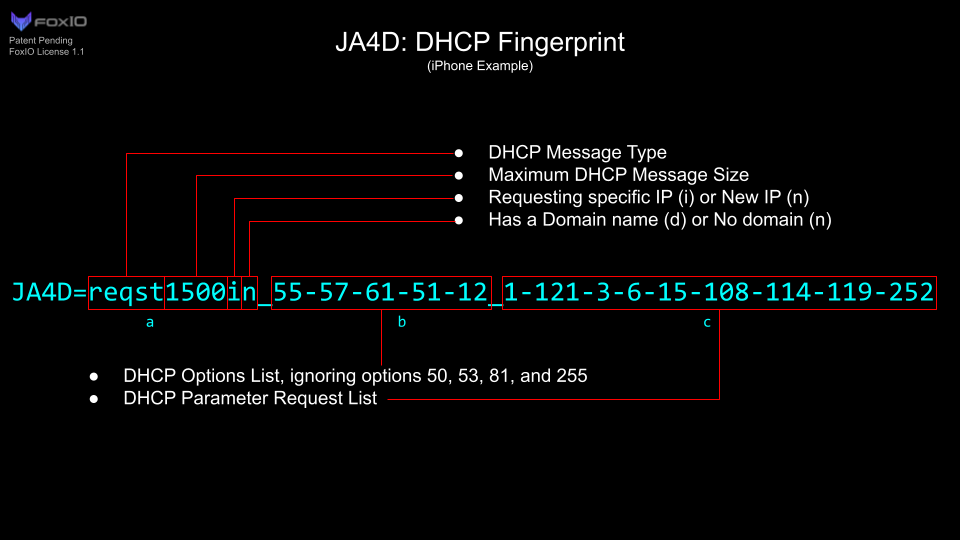
ICYMI: Seth's walkthrough on JA4 fingerprinting in Zeek covers JA4, JA4S, JA4H, JA4T, JA4SSH, and JA4D with installation and use cases.
-
ICYMI: Seth's walkthrough on JA4 fingerprinting in Zeek covers JA4, JA4S, JA4H, JA4T, JA4SSH, and JA4D with installation and use cases.
Zeek: How to Use JA4 Network Fingerprints in Zeek
Learn how to use JA4 network fingerprinting in Zeek to identify client and server software, detect malware, and track behavior across encrypted connections without requiring decryption. Network fingerprinting helps identify client and server software without decrypting traffic or relying on IP addresses that rotate constantly. JA4, a family of fingerprinting methods released by FoxIO, expands…

Zeek (zeek.org)
#Zeek #NetworkSecurity #OpenSource
-
R relay@relay.infosec.exchange shared this topic
-
ICYMI: Seth's walkthrough on JA4 fingerprinting in Zeek covers JA4, JA4S, JA4H, JA4T, JA4SSH, and JA4D with installation and use cases.
Zeek: How to Use JA4 Network Fingerprints in Zeek
Learn how to use JA4 network fingerprinting in Zeek to identify client and server software, detect malware, and track behavior across encrypted connections without requiring decryption. Network fingerprinting helps identify client and server software without decrypting traffic or relying on IP addresses that rotate constantly. JA4, a family of fingerprinting methods released by FoxIO, expands…

Zeek (zeek.org)
#Zeek #NetworkSecurity #OpenSource
@zeek While JA4 is a valuable addition, its effectiveness can be limited by widespread TLS encryption of the initial Client Hello.
-
R relay@relay.mycrowd.ca shared this topicR relay@relay.publicsquare.global shared this topicSystem shared this topic
