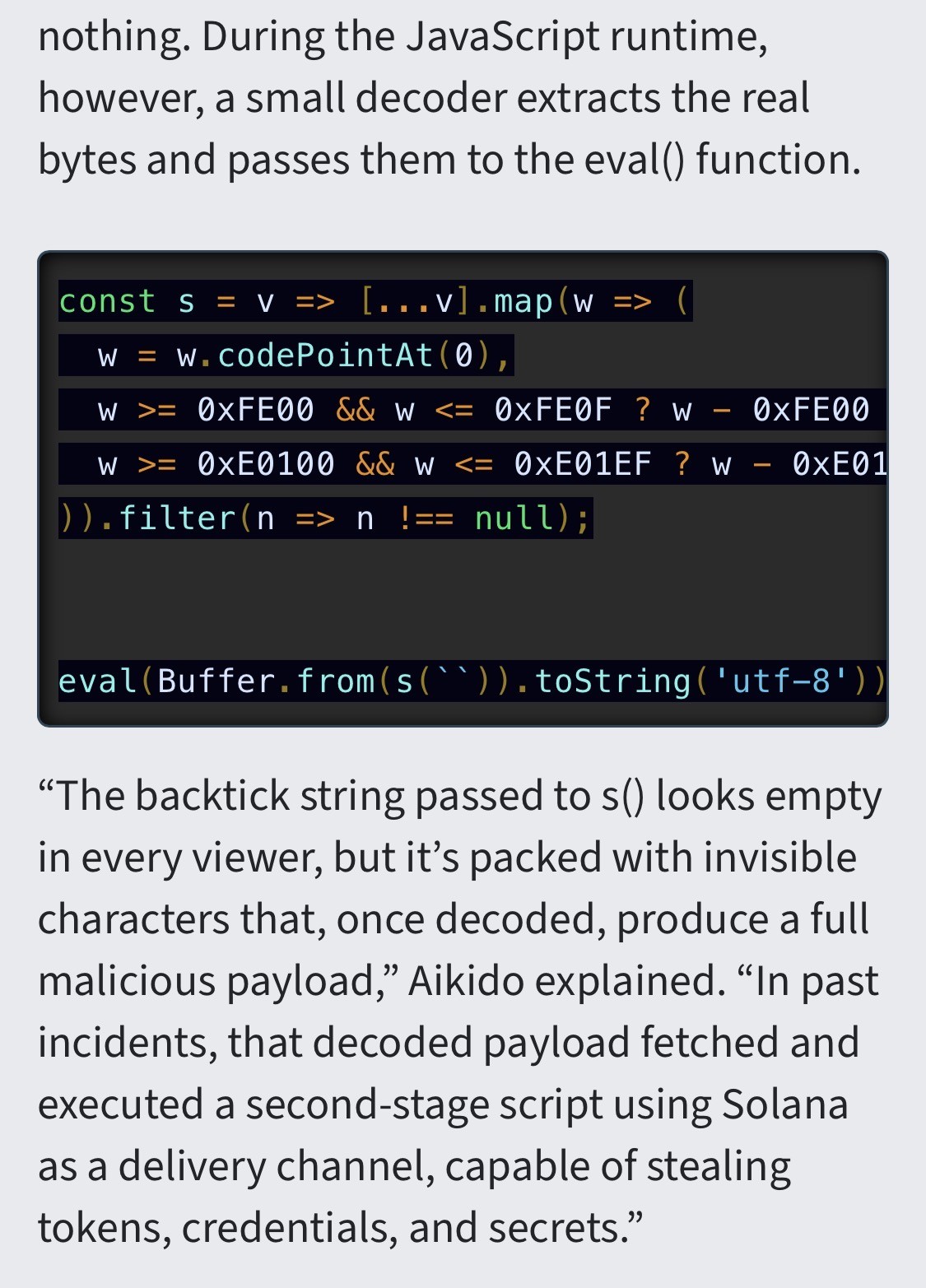
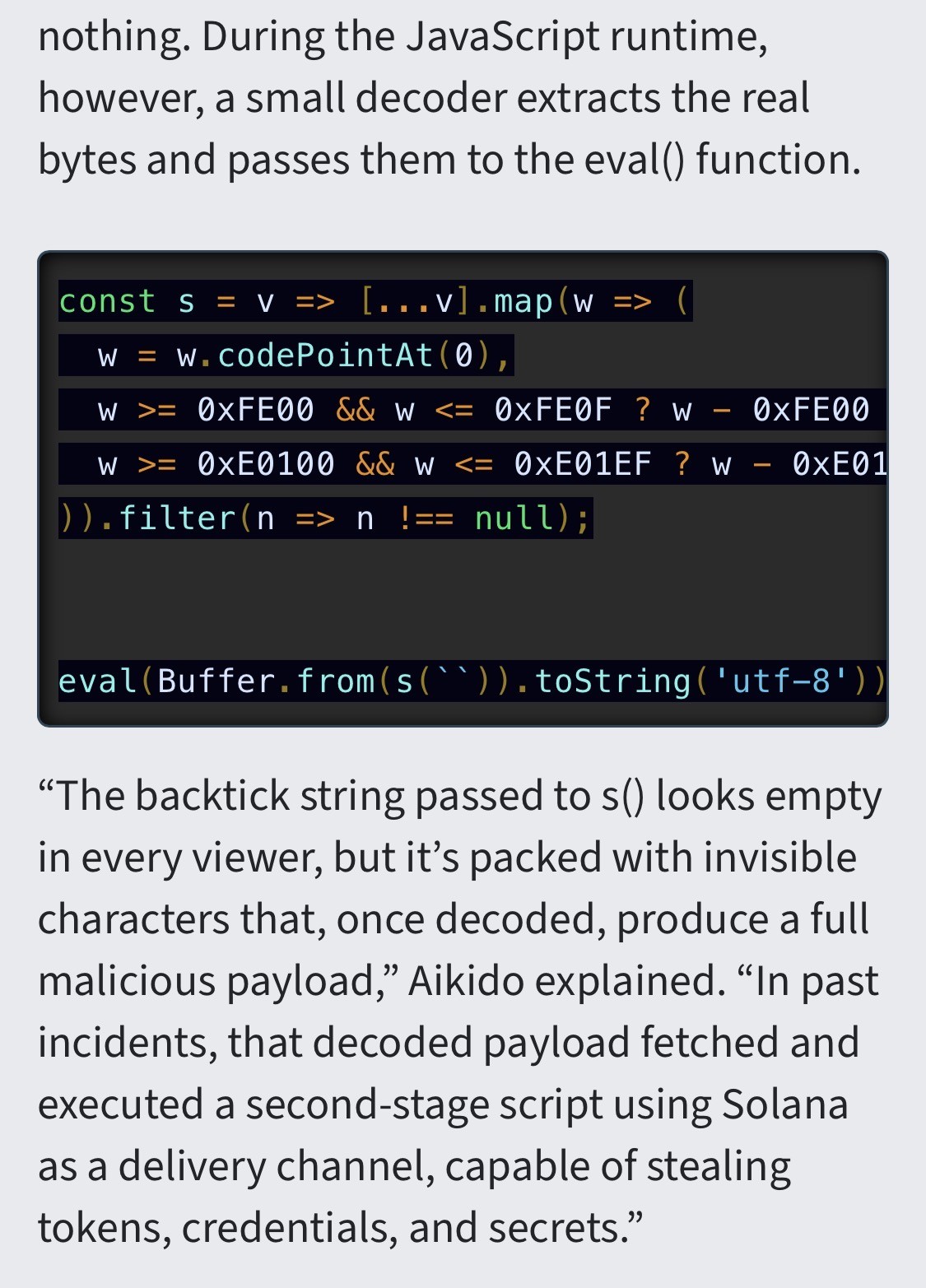
“The researchers suspect that Glassworm—the name they assigned to the attack group—is using LLMs to generate these convincingly legitimate-appearing packages.
-
RE: https://mastodon.scot/@simon_brooke/116232834837623434
“The researchers suspect that Glassworm—the name they assigned to the attack group—is using LLMs to generate these convincingly legitimate-appearing packages. “At the scale we’re now seeing, manual crafting of 151+ bespoke code changes across different codebases simply isn’t feasible,” they explained. Fellow security firm Koi, which has also been tracking the same group, said it, too, suspects the group is using AI.”
-
RE: https://mastodon.scot/@simon_brooke/116232834837623434
“The researchers suspect that Glassworm—the name they assigned to the attack group—is using LLMs to generate these convincingly legitimate-appearing packages. “At the scale we’re now seeing, manual crafting of 151+ bespoke code changes across different codebases simply isn’t feasible,” they explained. Fellow security firm Koi, which has also been tracking the same group, said it, too, suspects the group is using AI.”
@aral
Hello brother Aral, I want to ask you for a favor My name is Omar Ziada, and I live in Gaza It's a very difficult life I'm truly sorry to bother you, but I don't receive any assistance no one donates to me I just want you to post something for me I'm asking my followers to donate to me Please brother help me with this You're a very kind person with a big and wonderful heart Please for my sake and for the sake of my family Please, brother, reply to me, I need you Reply to me and talk to me -
RE: https://mastodon.scot/@simon_brooke/116232834837623434
“The researchers suspect that Glassworm—the name they assigned to the attack group—is using LLMs to generate these convincingly legitimate-appearing packages. “At the scale we’re now seeing, manual crafting of 151+ bespoke code changes across different codebases simply isn’t feasible,” they explained. Fellow security firm Koi, which has also been tracking the same group, said it, too, suspects the group is using AI.”
What I don’t get is how this snippet passed code review regardless.
I mean, it’s clearly dodgy and the last line basically meaningless without the code being evaluated.
The real story here isn’t the invisible Unicode characters, it’s the lack of proper code review on code submissions.
-
What I don’t get is how this snippet passed code review regardless.
I mean, it’s clearly dodgy and the last line basically meaningless without the code being evaluated.
The real story here isn’t the invisible Unicode characters, it’s the lack of proper code review on code submissions.
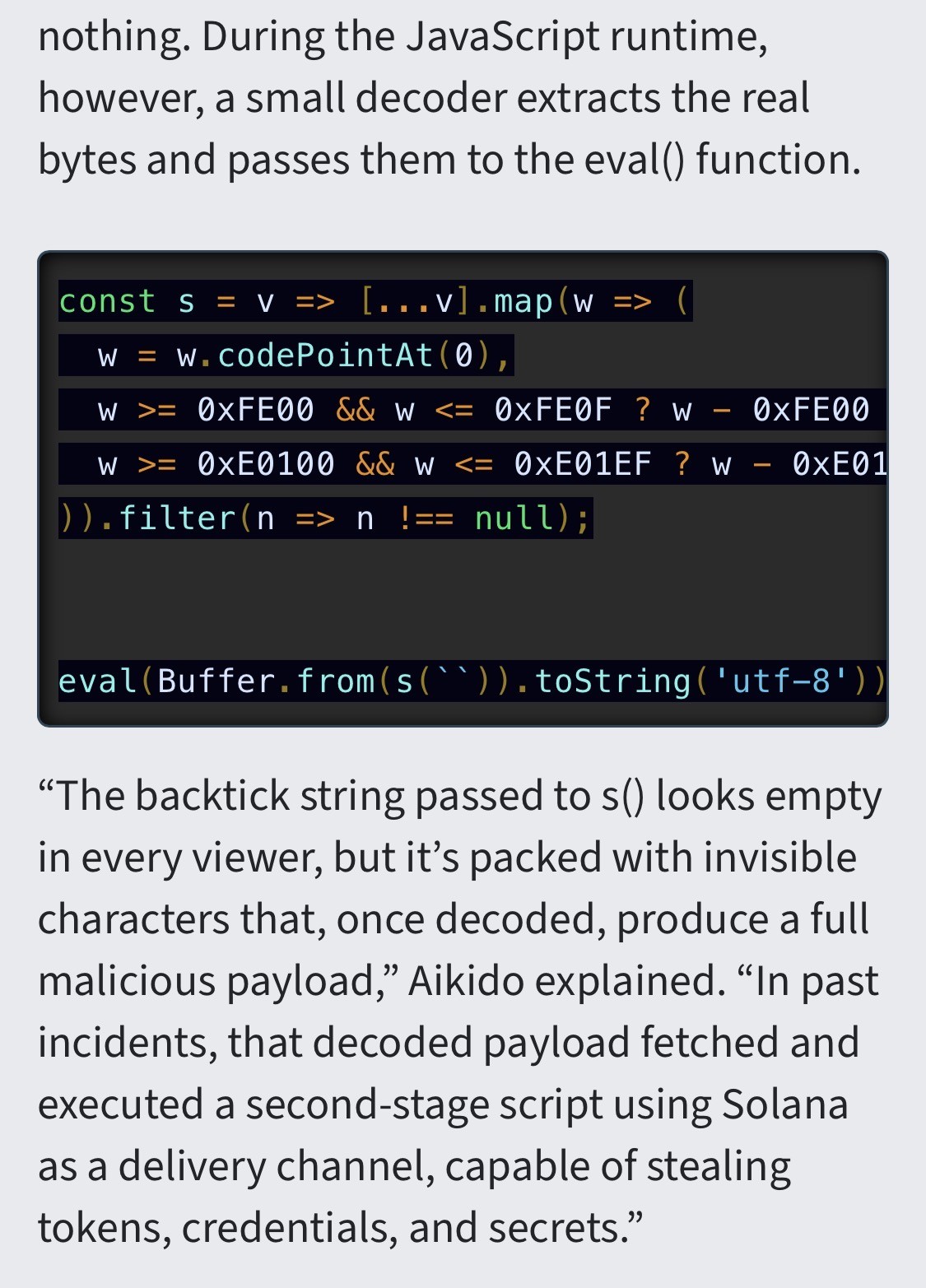
@aral I agree that code reviews should generally be "wtf?! eval?!", but it is always good to remind people that an empty looking string is not necessarily really empty.
-
What I don’t get is how this snippet passed code review regardless.
I mean, it’s clearly dodgy and the last line basically meaningless without the code being evaluated.
The real story here isn’t the invisible Unicode characters, it’s the lack of proper code review on code submissions.
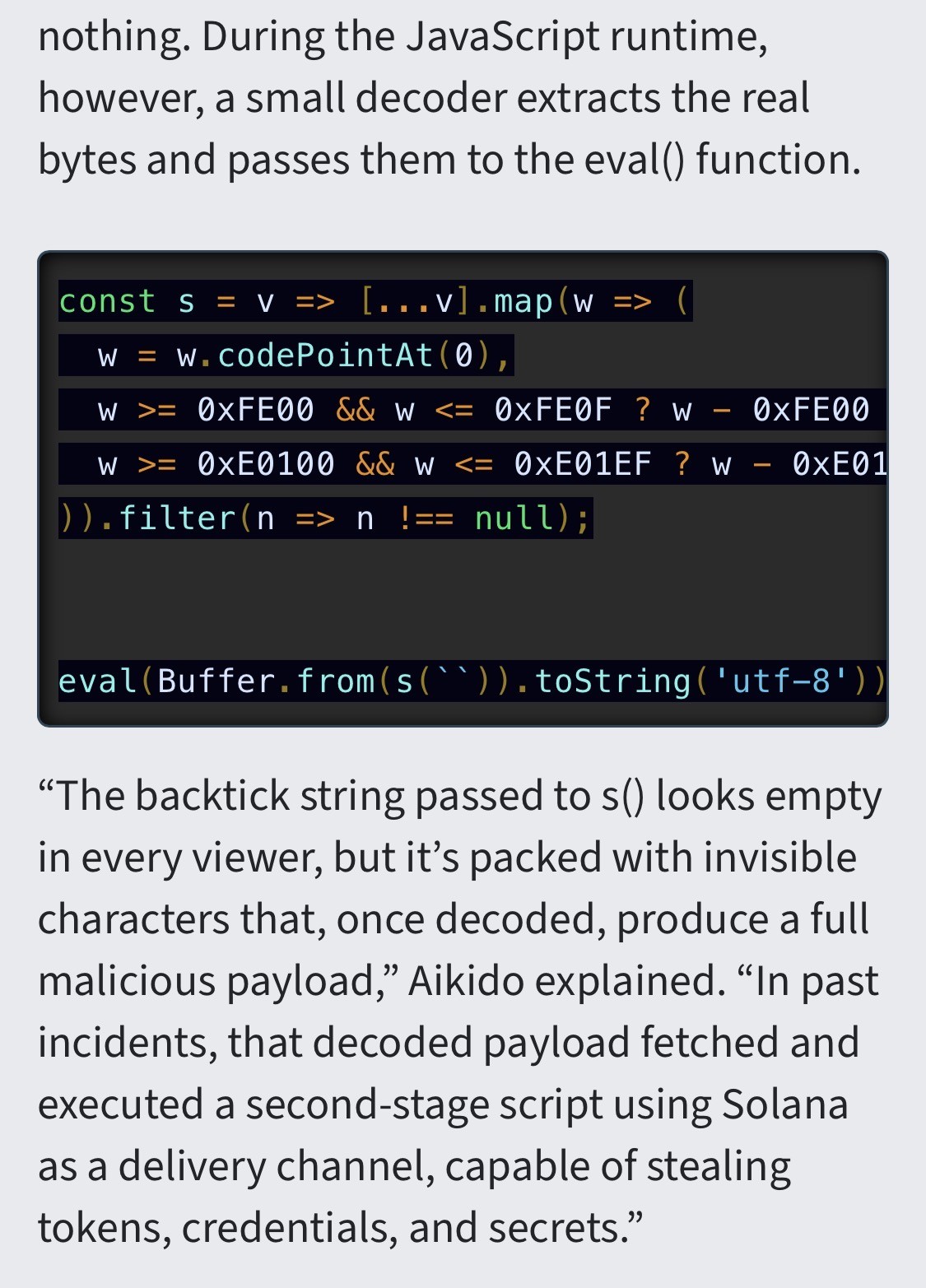
@aral lol, the eval call not even obfuscated
-
What I don’t get is how this snippet passed code review regardless.
I mean, it’s clearly dodgy and the last line basically meaningless without the code being evaluated.
The real story here isn’t the invisible Unicode characters, it’s the lack of proper code review on code submissions.
@aral@mastodon.ar.al
I feel like I need to restate this:
An "empty" string in back ticks not ringing any alarm bells. -
What I don’t get is how this snippet passed code review regardless.
I mean, it’s clearly dodgy and the last line basically meaningless without the code being evaluated.
The real story here isn’t the invisible Unicode characters, it’s the lack of proper code review on code submissions.
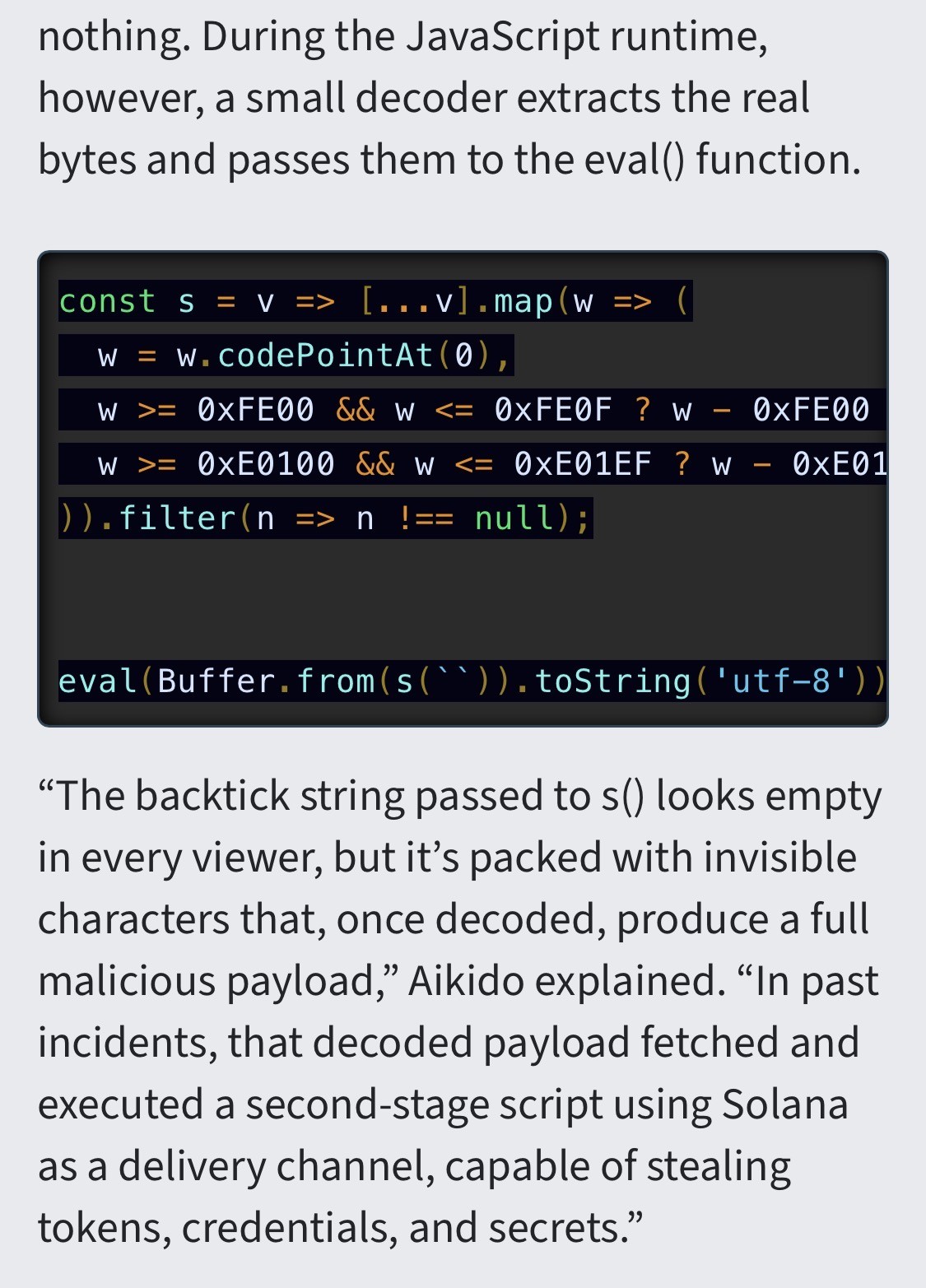
@aral I agree, I had the same thought, first of all an eval function is super suspicious; "eval is evil", on the other hand what the earth is the const s doing there. And in the name of love what is the reviewer thinking about when someone does a PR with this kind of "functionality". I will check but I think that a simple SAST is going to complain about this PR.
On a second thought maybe the snippet provided by the security researchers is just a non realistic example to illustrate the concept. -
R relay@relay.infosec.exchange shared this topic
