I'm putting together a webinar on modern vulnerability management and I'm REALLY trying to drive a point home
-
I'm putting together a webinar on modern vulnerability management and I'm REALLY trying to drive a point home
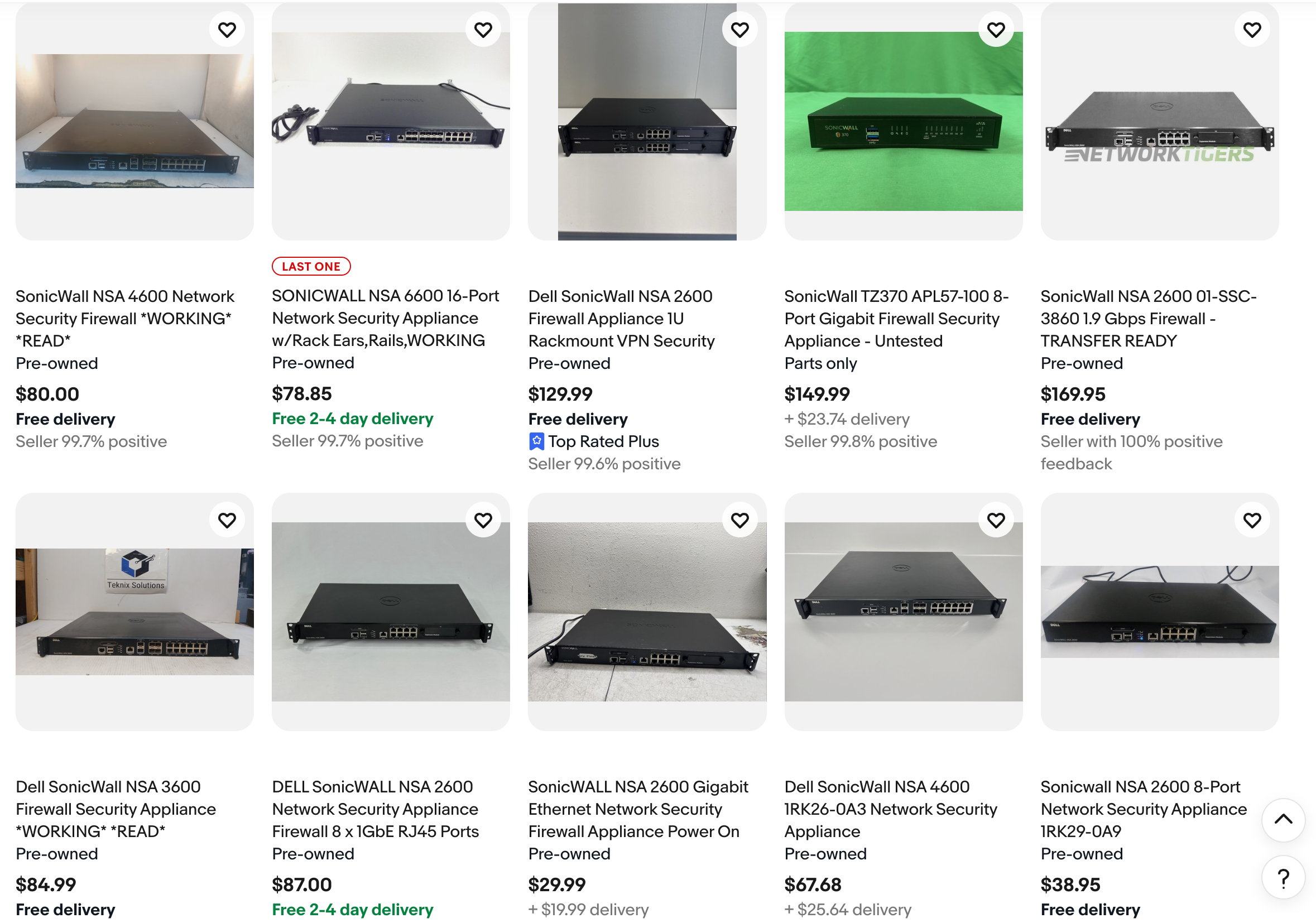
So naturally, I bought 3 old Sonicwall firewalls
-
I'm putting together a webinar on modern vulnerability management and I'm REALLY trying to drive a point home
So naturally, I bought 3 old Sonicwall firewalls
@sawaba confused, yes there will be vulns there, but how does that lead to vuln management process… identification, prioritisation triage, remediation… how does having a “blinkin lights” lead you to a satisfactory outcome? Or is that the point… patches can fail due to badly written patches that don’t fully remediate the problem?
-
R relay@relay.infosec.exchange shared this topic
-
I'm putting together a webinar on modern vulnerability management and I'm REALLY trying to drive a point home
So naturally, I bought 3 old Sonicwall firewalls
@sawaba worst thing is probably that there is a second hand market for these... is someone buying and installing them? IMO they should be treated as the asbestos of the 2000

-
@sawaba confused, yes there will be vulns there, but how does that lead to vuln management process… identification, prioritisation triage, remediation… how does having a “blinkin lights” lead you to a satisfactory outcome? Or is that the point… patches can fail due to badly written patches that don’t fully remediate the problem?
@gordondraper the context you're missing is that a third of ransom payments went to Akira, who is just successfully using one Sonicwall vuln over and over for the past 2 years.
250,000+ vulnerabilities out there, but harm/losses only come from a few dozen every year.
I bought the Sonicwalls to demonstrate how the attackers think:
- find a reliable exploit
- are there lots of exposed targets?
- if yes, start hitting them and profit
- next week: are there still lots of exposed targets?
- if yes, GOTO 3
-
@sawaba confused, yes there will be vulns there, but how does that lead to vuln management process… identification, prioritisation triage, remediation… how does having a “blinkin lights” lead you to a satisfactory outcome? Or is that the point… patches can fail due to badly written patches that don’t fully remediate the problem?
@gordondraper in other words, we're worried about Mythos, but folks aren't patching their network infrastructure and that's one of the main ways they're getting popped