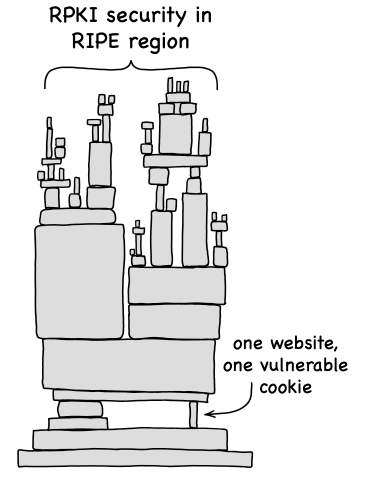
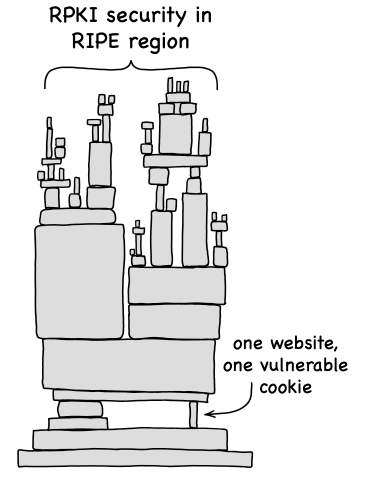
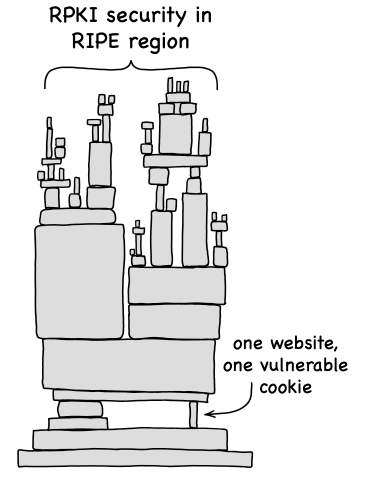
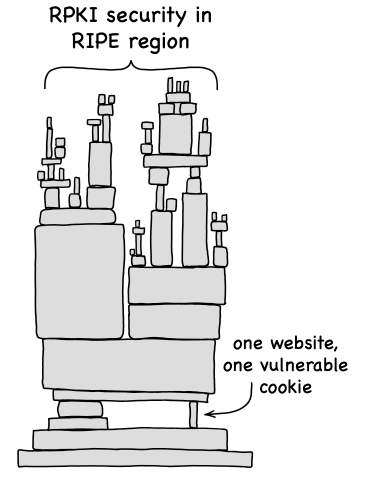
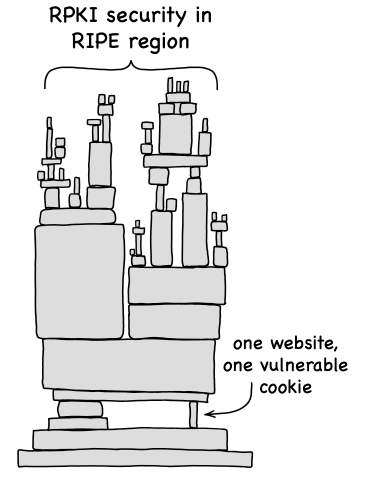
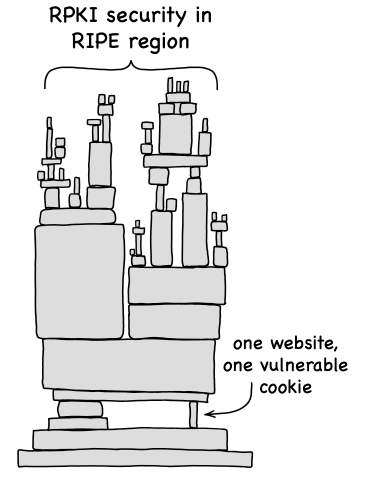
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors.
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
My disclosure process with RIPE NCC took 14 months, 26 messages, and included two incorrect fixes for the same vulnerability. I wrote about the process, with thoughts on what better would look like for RIPE NCC and others: https://mxsasha.eu/posts/ripe-ncc-disclosure-retrospective/
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash amazing work!
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash this is very cool & absolutely gets me thinking about the need for separating standard sessions/identities from administrative sessions again
-
@sash this is very cool & absolutely gets me thinking about the need for separating standard sessions/identities from administrative sessions again
@nyanbinary yes, although in this case, "administrative" includes almost any RIPE NCC platform, like e-learning courses, the blog (RIPE Labs), running an Atlas measurement, submitting a talk to a RIPE meeting, and so on. The same session token covers all services.
-
@nyanbinary yes, although in this case, "administrative" includes almost any RIPE NCC platform, like e-learning courses, the blog (RIPE Labs), running an Atlas measurement, submitting a talk to a RIPE meeting, and so on. The same session token covers all services.
@sash ye, thats where the identity separation would come into play for me - the account that can nuke your RPKI shouldn't be the one that you do for e-learning. Though I haven't worked with RIPE NCC so I dont know how feasible that is.
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash Great work Sasha (as many other things you have done! :), and thank you for responsibly disclosing it and patiently working with them to properly resolve it.
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash
 And we live another day
And we live another day -
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash thank you for your service - and a great write up for all on your discovery!
 ️
️
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash « I stumbled into the first vulnerability while debugging the reverse DNS zone for my IPv6 range in RIPEstat, RIPE NCC’s network information tool. A blue marquee started scrolling across the page, from an XSS payload I had put in my DNS server months earlier. »
actual irl lol, excellent work
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash Interesting!
-
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
@sash This is phenomenal! I'm reading this on my lunch break.
-
R relay@relay.infosec.exchange shared this topic
