For anyone else capturing #USB on #macOS on Apple Silicon:It does work, you just have to disable SIP entirely first (individual flags don't work, need csrutil disable)You need to manually set the correct interface up, e.g. sudo ifconfig XHC2 up
-
For anyone else capturing #USB on #macOS on Apple Silicon:
It does work, you just have to disable SIP entirely first (individual flags don't work, needcsrutil disable)
You need to manually set the correct interface up, e.g.sudo ifconfig XHC2 upFor identifying a specific device, the easiest way is to correlate with IORegistryExplorer.
For example:iPhone@02100000
^
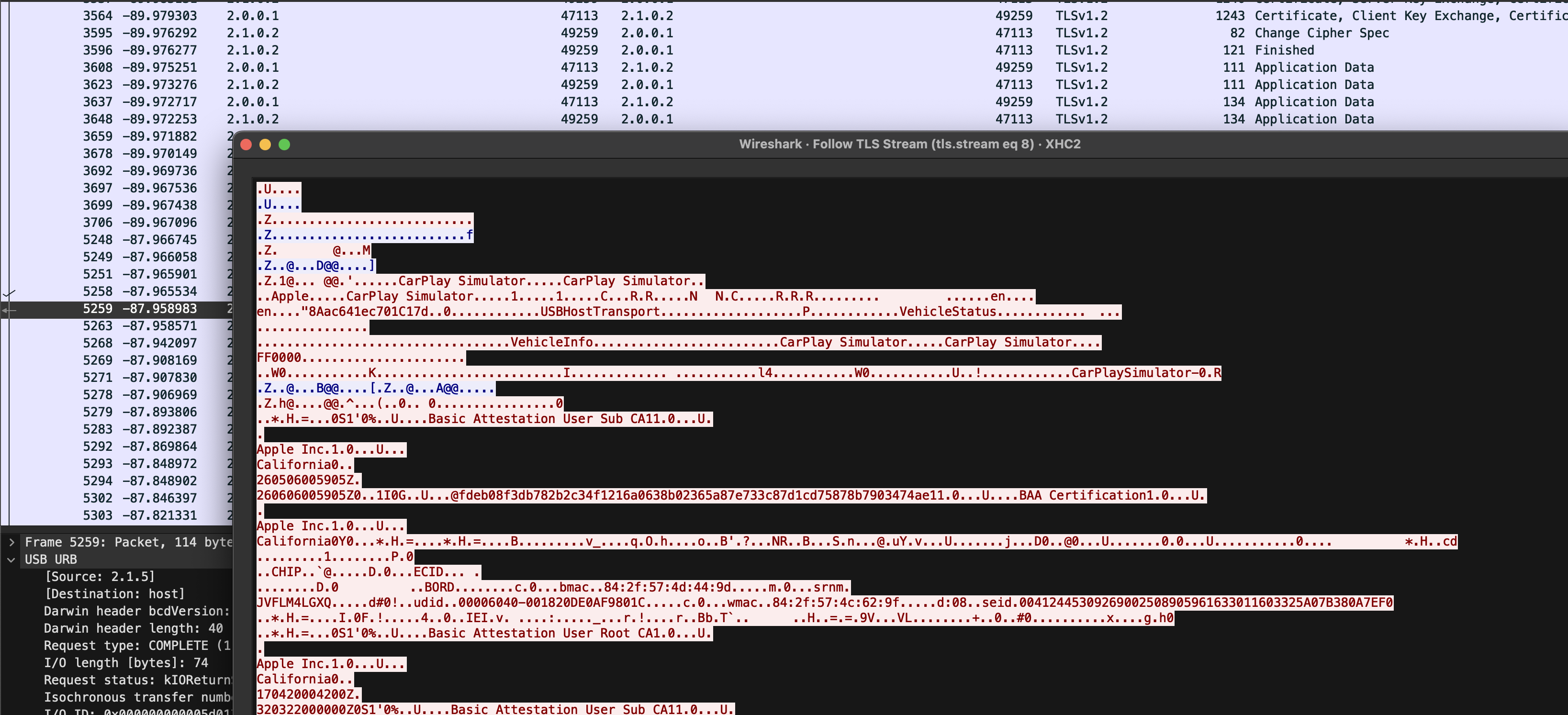
XHC interfaceOnce you start the capture in Wireshark, you can filter to just that device using
usb.darwin.location_id == 0x02100000 -
For anyone else capturing #USB on #macOS on Apple Silicon:
It does work, you just have to disable SIP entirely first (individual flags don't work, needcsrutil disable)
You need to manually set the correct interface up, e.g.sudo ifconfig XHC2 upFor identifying a specific device, the easiest way is to correlate with IORegistryExplorer.
For example:iPhone@02100000
^
XHC interfaceOnce you start the capture in Wireshark, you can filter to just that device using
usb.darwin.location_id == 0x02100000I wanted to use this to decrypt connections made using
MobileDevice.frameworkover lockdownd, so I created the following:Custom #Wireshark dissector for the
usbmuxdTCP encapsulation:
https://gist.github.com/JJTech0130/da77af43269076f6ea78f69471d1df6e
SSL keylog for the version of LibreSSL it links (using #Frida)
https://gist.github.com/JJTech0130/e238798e66fe70abc16f1c6dc6c28ab3Thanks @nicolas17 for the help!
-
R relay@relay.infosec.exchange shared this topic
