@paco @BenAveling it is just a stupid electronic device
-
@b_cavello I’m glad! I think it’s fun. I’ve been doing it off and on for 20 years. (I lived outside the US for 10). Almost any eligible voter can be an election officer in most jurisdictions. It’s easy to try once, and no big deal if you don’t like it and don’t do it again.
@paco I live in DC, and I feel like they’re overwhelmed with volunteers, but maybe not for special election stuff. I’d like to try it! These quiet moments of democracy in action are really beautiful
-
@shinspiegel @elaine @paco
which doesn't make things any better, though@ki @elaine @paco I did write in my blog on this topic year ago, maybe this could better explain my reasonsing. It can be a little outdated, and I after thought this concept can be improved, but it’s a starting point: https://jeferson.me/blog/2025/06/10/pr0n/
-
@Virginicus Agreed. Speaking to Ms Hanley, she said of working in the general assembly: it’s the kiss of death on an initiative to say it’s being put forward by Fairfax. Everyone rolls their eyes. It’s an interesting story:
VA law says you can’t have a district bigger than 5000 voters. Fairfax has a lot of people, so lots of 2500-3500 voter precincts. But it also has a bunch of 1000-person precincts. Her expression was that the office of elections is “turning into a moving company” because of how many precincts we have and the amount of equipment we have to send to each. But we have to do things according to the law.
Thankfully, she said, Chesterfield County is running into something similar. So THEY can put forward a bill to get some changes and Fairfax can support them.
She wants to do bigger locations with more of the print-on-demand machines. A location might serve 3-5 precincts. You walk up, we figure out what precinct you’re in, and we print the ballot that you should have. This is what they do at the satellite early voting sites. They just want to do more of it and do it in larger precincts on election day. Sounds like a good idea to me. But it sounds like it requires a change to the law.
-
@paco The toilet paper is for fiber.
-
-
@david_chisnall @paco AWS with the Mac Minis -- every time you power them off they wipe storage, takes a couple hours to complete before you can use the server again. Really annoying when you didn't expect it
-
@david_chisnall @paco AWS with the Mac Minis -- every time you power them off they wipe storage, takes a couple hours to complete before you can use the server again. Really annoying when you didn't expect it
@feld @david_chisnall @paco David nails it. Also, encryption at rest makes it possible to retire storage devices after End-of-Life without having to worry about data theft after retirement.
-
@feld @david_chisnall @paco David nails it. Also, encryption at rest makes it possible to retire storage devices after End-of-Life without having to worry about data theft after retirement.
@vinoth @david_chisnall @paco same reason why I FDE all my disks now. I don't have to care what happens if they fail.
Also I never have to worry about ZFS pool issues from moving disks around. Wiping the encryption key and setting a new one is much simpler than trying to scrub all the ZFS metadata off a disk -
@david_chisnall @paco AWS with the Mac Minis -- every time you power them off they wipe storage, takes a couple hours to complete before you can use the server again. Really annoying when you didn't expect it
The Morello cluster we set up at MS was exposed for GitHub Actions runners. We forwarded the GitHub web hook thing to an Azure message queue thing that the head node read. When it received one, it used an exciting pile of expect scripts to talk to the serial console on a node to boot one of the machines. The node then booted with a read-only NFS mount as the root filesystem, generated a random key, and used that for a GELI-encryped read-write filesystem on the (200GB) local SSD. The GitHub Actions runner (actually, the portable Go rewrite) then pulled the job to run. At the end, we rebooted the node and the next job would get a new key for disk encryption.
If a job left any important data on a node, the next user would get the encrypted data and, unless they deleted the GELI layer, would get it decrypted with a different key. We didn't need to bother scrubbing anything between uses.
-
The Morello cluster we set up at MS was exposed for GitHub Actions runners. We forwarded the GitHub web hook thing to an Azure message queue thing that the head node read. When it received one, it used an exciting pile of expect scripts to talk to the serial console on a node to boot one of the machines. The node then booted with a read-only NFS mount as the root filesystem, generated a random key, and used that for a GELI-encryped read-write filesystem on the (200GB) local SSD. The GitHub Actions runner (actually, the portable Go rewrite) then pulled the job to run. At the end, we rebooted the node and the next job would get a new key for disk encryption.
If a job left any important data on a node, the next user would get the encrypted data and, unless they deleted the GELI layer, would get it decrypted with a different key. We didn't need to bother scrubbing anything between uses.
@david_chisnall @paco yes yes yes this is exactly how it should be done (but the use of expect scripts makes me feel like we went back 30 years) -
@david_chisnall @paco yes yes yes this is exactly how it should be done (but the use of expect scripts makes me feel like we went back 30 years)
Yup, experimental hardware. It came in a rackmounted box, but it was really an evaluation board. The bootloader was never meant to do that. We had all of the serial consoles connected via some big USB hubs because the only way of netbooting them was to talk to the serial console and prod it with a bunch of commands.
-
@paco This is often essential for corporates to meet defined security standards.
Yes, it's far more probable that the application will be attacked than the data container, but there you go.
I also seem to remember that certain hacks *have* stolen the entire (virtual) container, so it is a nice to have.
-
@paco what about data-at-rest encrypted on your disk while malware is exfilling all data, the encrypted stuff is safe. imagine all your mails (seperately) encrypted, malware actor can only use the ones that are decrypted while present. limits damages.
-
@paco Groan, yes. Had someone just the other day asking about full disk encryption just after his wordpress had been hacked.
No, you need to fix your website. FDE might satisfy your auditor or other paper tiger box ticking exercise (ta-*dah*, security) but it won’t stop your wordpress being hacked again.
Which it was, a few days later.
-
@paco what about data-at-rest encrypted on your disk while malware is exfilling all data, the encrypted stuff is safe. imagine all your mails (seperately) encrypted, malware actor can only use the ones that are decrypted while present. limits damages.
@stf That is all true. It’s just totally unrelated to the sense in which OpenAI is using “encryption at rest.” It’s also nothing like what a cloud provider means when they say “encryption at rest.”
Can a person take individual actions to protect themselves? Yes. That isn’t the topic.
-
@paco This is often essential for corporates to meet defined security standards.
Yes, it's far more probable that the application will be attacked than the data container, but there you go.
I also seem to remember that certain hacks *have* stolen the entire (virtual) container, so it is a nice to have.
@syllopsium i didn’t say there was no reason to do it. I just said it wasn’t protecting the data. Compliance is the biggest driver. And this is a great example where compliance makes a bunch of people do a bunch of stuff that has limited value in reality.
-
@stf That is all true. It’s just totally unrelated to the sense in which OpenAI is using “encryption at rest.” It’s also nothing like what a cloud provider means when they say “encryption at rest.”
Can a person take individual actions to protect themselves? Yes. That isn’t the topic.
@paco i misunderstood i thought you criticize data-at-rest encryption in general, sounded to me like openai was only the trigger for that.
and the cloud storage thing also was confusing, in that context d-a-r-e also makes sense it all depends who is holding the only copies to the keys.
please excuse my confusion and my blatant off-topicness
-
@paco i misunderstood i thought you criticize data-at-rest encryption in general, sounded to me like openai was only the trigger for that.
and the cloud storage thing also was confusing, in that context d-a-r-e also makes sense it all depends who is holding the only copies to the keys.
please excuse my confusion and my blatant off-topicness
@stf I think what i did badly was compare it to encrypting a laptop hard drive. THAT has a ton of value because laptops are easily stolen. But I can see how it sounds like I didn’t think any of it was worthwhile.
-
My oldest website (1995) got hacked because a company did a shitty thing...but that's not the important bit...
The important bit is that I started rebuilding. Using old, old, older than marquee old html. For giggles, to see if I could remember it.
My site was being pounded thousands of times an hour by AI bots who think my site is the other company.
I now have a single page, explaining why I was hacked, with an email address so the people who stole my name can just buy the site because I can't ever use it again, but it will be a cold day in hell before I just relinquish it.
-
My oldest website (1995) got hacked because a company did a shitty thing...but that's not the important bit...
The important bit is that I started rebuilding. Using old, old, older than marquee old html. For giggles, to see if I could remember it.
My site was being pounded thousands of times an hour by AI bots who think my site is the other company.
I now have a single page, explaining why I was hacked, with an email address so the people who stole my name can just buy the site because I can't ever use it again, but it will be a cold day in hell before I just relinquish it.
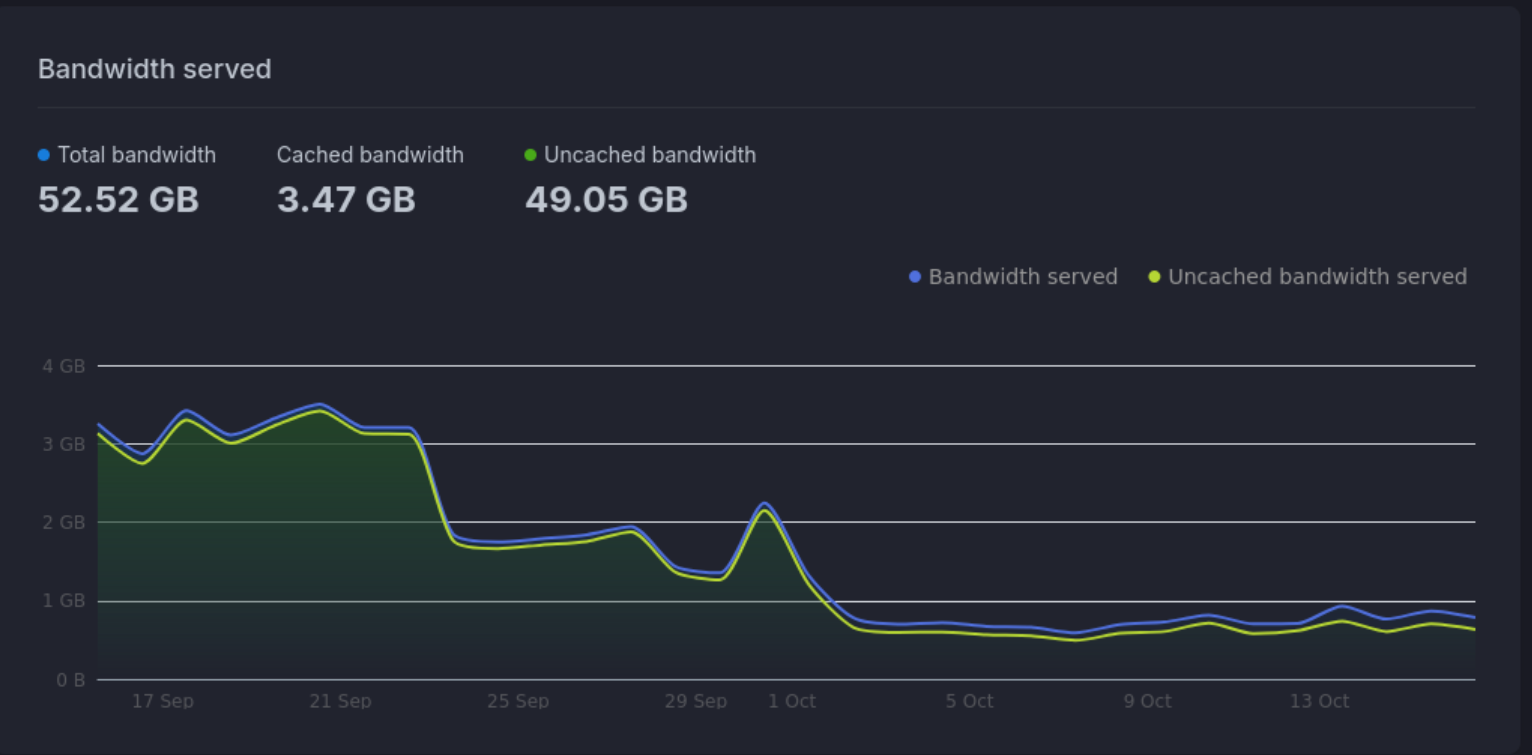
@MissConstrue Grrrr. That sucks. I run a slightly popular, 20-year-old web forum. I ended up paying the $9.50/month to bunny.net to add their anti-bot protections. You can totally see in the graph when I turned that on.

 among other things but we generally stay stocked up on TP and French toast.
among other things but we generally stay stocked up on TP and French toast.