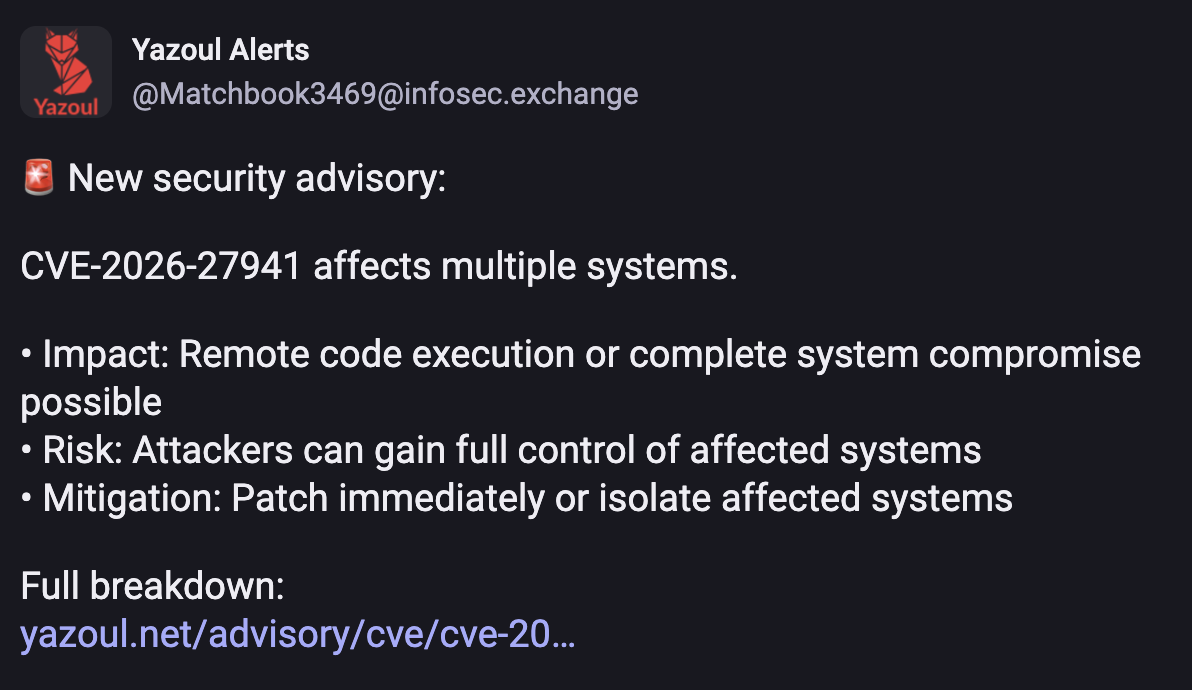
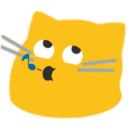
Hey, security vendors.. this is a bullshit anti-pattern.
-
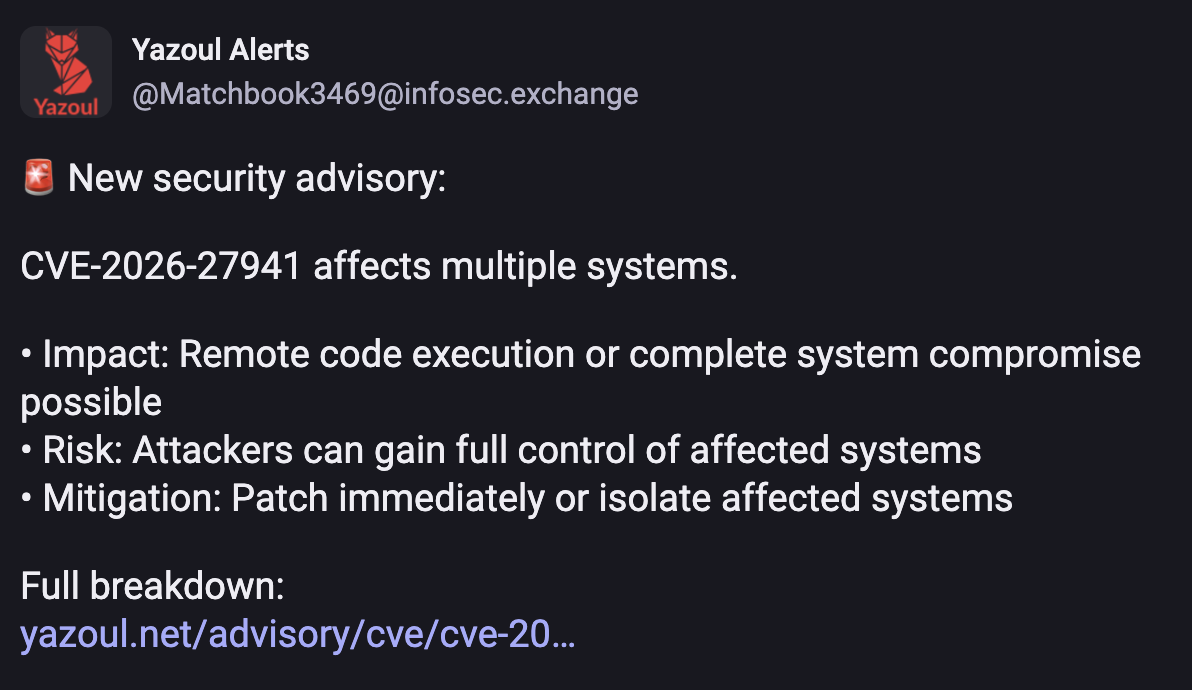
Hey, security vendors.. this is a bullshit anti-pattern. This vendor and others like it intentionally leave out the impacted vendor, products, technologies, and environments. There is zero context here. Readers would need to follow the link or independently research the CVE to see if they care.
Security practitioners see it for what it is: Fear based traffic farming.
It isn't a good look and many of us will never trust anything you say or send you traffic.
A note, I do work for a security vendor. We don't do this and I would absolutely call out our (awesome) marketing or research teams if we did.
#Security #cybersecurity #zeroday #threatintel
-
R relay@relay.infosec.exchange shared this topic
-
Hey, security vendors.. this is a bullshit anti-pattern. This vendor and others like it intentionally leave out the impacted vendor, products, technologies, and environments. There is zero context here. Readers would need to follow the link or independently research the CVE to see if they care.
Security practitioners see it for what it is: Fear based traffic farming.
It isn't a good look and many of us will never trust anything you say or send you traffic.
A note, I do work for a security vendor. We don't do this and I would absolutely call out our (awesome) marketing or research teams if we did.
#Security #cybersecurity #zeroday #threatintel
@TomSellers Yep. That account was an immediate block as soon as I saw it.
-
@TomSellers Yep. That account was an immediate block as soon as I saw it.
bro what if we market our security company like a threat actor and phish prospects!
check your email gateways too. These kinds of vendors tend to spam your executive chains.
Act like a TA, be treated in kind.
-
@TomSellers Yep. That account was an immediate block as soon as I saw it.
Accounts - plural. Also on the main mastodon instance, posting the same stuff.
Just in case you wanted to be extra thorough
-
Accounts - plural. Also on the main mastodon instance, posting the same stuff.
Just in case you wanted to be extra thorough
@Aprazeth @TomSellers Whack-a-mole. Blockity block block.
-
@Aprazeth @TomSellers Whack-a-mole. Blockity block block.

Also, I appreciate the heads up on the account(s).
I get the need to hustle and bustle but not by stooping to this point of buzzfeed. Yeesh
-
Hey, security vendors.. this is a bullshit anti-pattern. This vendor and others like it intentionally leave out the impacted vendor, products, technologies, and environments. There is zero context here. Readers would need to follow the link or independently research the CVE to see if they care.
Security practitioners see it for what it is: Fear based traffic farming.
It isn't a good look and many of us will never trust anything you say or send you traffic.
A note, I do work for a security vendor. We don't do this and I would absolutely call out our (awesome) marketing or research teams if we did.
#Security #cybersecurity #zeroday #threatintel
There, did their job for them. I prefer to be paid in euros
-
Hey, security vendors.. this is a bullshit anti-pattern. This vendor and others like it intentionally leave out the impacted vendor, products, technologies, and environments. There is zero context here. Readers would need to follow the link or independently research the CVE to see if they care.
Security practitioners see it for what it is: Fear based traffic farming.
It isn't a good look and many of us will never trust anything you say or send you traffic.
A note, I do work for a security vendor. We don't do this and I would absolutely call out our (awesome) marketing or research teams if we did.
#Security #cybersecurity #zeroday #threatintel
@TomSellers I've seen it from a couple of accounts now and they both started with "affects multiple systems", I assumed it was a bot

