#privacy #compliance
-
R relay@relay.publicsquare.global shared this topic
-
If I understand correctly how this works: There is a small always-on low-power core that is recording everything to a small buffer and doing a small amount of signal processing to see if there's a reasonable chance that you've said the activation phrase. When it detects this trigger, it wakes up the main core, which grabs the buffer and does some more complex signal processing to see if you really (or, at least, with much higher probability) said the activation phrase. If so, it's then forwarded to the thing that processes the command.
If the code on the main core doesn't have microphone access, the core is still woken up, but then the process that tries to check if you really said the activation phrase fails because it can't access the microphone.
There's probably an interesting side channel where a malicious version could (assuming the low-power core doesn't hardcode 'Okay Google') rapidly program different activation phrases to get a reasonably high probability of whether specific things are said.
-
If I understand correctly how this works: There is a small always-on low-power core that is recording everything to a small buffer and doing a small amount of signal processing to see if there's a reasonable chance that you've said the activation phrase. When it detects this trigger, it wakes up the main core, which grabs the buffer and does some more complex signal processing to see if you really (or, at least, with much higher probability) said the activation phrase. If so, it's then forwarded to the thing that processes the command.
If the code on the main core doesn't have microphone access, the core is still woken up, but then the process that tries to check if you really said the activation phrase fails because it can't access the microphone.
There's probably an interesting side channel where a malicious version could (assuming the low-power core doesn't hardcode 'Okay Google') rapidly program different activation phrases to get a reasonably high probability of whether specific things are said.
@david_chisnall @beyondmachines1 yes there is a small wakeup program that always listens for the activation word
-
If I understand correctly how this works: There is a small always-on low-power core that is recording everything to a small buffer and doing a small amount of signal processing to see if there's a reasonable chance that you've said the activation phrase. When it detects this trigger, it wakes up the main core, which grabs the buffer and does some more complex signal processing to see if you really (or, at least, with much higher probability) said the activation phrase. If so, it's then forwarded to the thing that processes the command.
If the code on the main core doesn't have microphone access, the core is still woken up, but then the process that tries to check if you really said the activation phrase fails because it can't access the microphone.
There's probably an interesting side channel where a malicious version could (assuming the low-power core doesn't hardcode 'Okay Google') rapidly program different activation phrases to get a reasonably high probability of whether specific things are said.
@david_chisnall @beyondmachines1 Compare with the Amazon design, who hard connect the "microphone disabled" LED to the microphone input amplifier powerdown pin.
-
@beyondmachines1 Ah I see your problem, this is a techy thing. To disable microphones in Alexa, Google Home, etc, you need to use a hammer and throw everything into the trash bin outside the house. Be careful what you say outside around the trash bin until the trash is picked up.
You are welcome!
-
@beyondmachines1
I mean, there are reasons that when I got myself a new laptop a couple of years back, I got one with *physical switches for the mic and camera*. -
If I understand correctly how this works: There is a small always-on low-power core that is recording everything to a small buffer and doing a small amount of signal processing to see if there's a reasonable chance that you've said the activation phrase. When it detects this trigger, it wakes up the main core, which grabs the buffer and does some more complex signal processing to see if you really (or, at least, with much higher probability) said the activation phrase. If so, it's then forwarded to the thing that processes the command.
If the code on the main core doesn't have microphone access, the core is still woken up, but then the process that tries to check if you really said the activation phrase fails because it can't access the microphone.
There's probably an interesting side channel where a malicious version could (assuming the low-power core doesn't hardcode 'Okay Google') rapidly program different activation phrases to get a reasonably high probability of whether specific things are said.
@david_chisnall @beyondmachines1 yeah, that's pretty much exactly how it works.
It's actually triple stage (DSP hotword + CPU hotword + serverside hotword). Each of the models is larger and more accurate due to RAM requirements.
Programming the DSP with hotword program is a privileged operation though, only built-in apps can do it (among other things, due to the fact that the DSP doesn't have much of its own memory protection).
-
@david_chisnall @beyondmachines1 yeah, that's pretty much exactly how it works.
It's actually triple stage (DSP hotword + CPU hotword + serverside hotword). Each of the models is larger and more accurate due to RAM requirements.
Programming the DSP with hotword program is a privileged operation though, only built-in apps can do it (among other things, due to the fact that the DSP doesn't have much of its own memory protection).
@david_chisnall @beyondmachines1 if I remember correctly, disabling the "Google" app will prevent the DSP configuration service from running and it should leave the DSP offline and without the hotword model.
-
@beyondmachines1 While I understand the privacy issue, I wish there were good privacy aware alternatives.
For Google Home, there are many that use local keyword detection and local voice recognition with Home Assistant. From what I saw, it works wonders (if you get the right hardware).
But for Android? The best I found is an app that requires a persistent notification for the hot word to work. AFAIK Google crippled Android so they are the only ones that can build an app with efficient hot word detection "for security reasons". And no custom ROMs seem to have fixed that or developed alternatives ( including @GrapheneOS ... YET ).
-
@beyondmachines1 my gaming laptop has a physical switch for the webcam (only time I've seen this) - I suppose a second switch for the mic would be extravangant, but maybe one switch could cancel both?
-
@beyondmachines1
That sadly can happen. -
@beyondmachines1 my gaming laptop has a physical switch for the webcam (only time I've seen this) - I suppose a second switch for the mic would be extravangant, but maybe one switch could cancel both?
@mossman Every “business” laptop I've used over the last decade has had a physical slide shutter to cover the webcam, and on many the shutter doubles as a switch to electrically disable the camera
-
@mossman Every “business” laptop I've used over the last decade has had a physical slide shutter to cover the webcam, and on many the shutter doubles as a switch to electrically disable the camera
@krans @beyondmachines1 all my HP corporate/client laptops since ~2020 have had the shutter, but they don't cut power to the webcam (you get a dark grey smudgy image which clearly shows the shutter being opened and closed).
My gaming laptop appears to (and is supposed to) completely disable the webcam when switched, so if the microphone was on the same circuit (as someone else here said theirs does) then that would fix the privacy question.
-
@hobart @beyondmachines1 @pluralistic Siri is correct. It is turned on. You could verify that in the system settings. You have disabled active connections to Bluetooth devices, but passive scanning (and Apple Watch connectivity) is still enabled.
For Bluetooth and WiFi there are basically three modes: Active and connecting (indicated by blue icon in control center), Active bit not connecting (indicated by white icon) and disabled (indicated by gray icon and disabled state in settings).
-
If I understand correctly how this works: There is a small always-on low-power core that is recording everything to a small buffer and doing a small amount of signal processing to see if there's a reasonable chance that you've said the activation phrase. When it detects this trigger, it wakes up the main core, which grabs the buffer and does some more complex signal processing to see if you really (or, at least, with much higher probability) said the activation phrase. If so, it's then forwarded to the thing that processes the command.
If the code on the main core doesn't have microphone access, the core is still woken up, but then the process that tries to check if you really said the activation phrase fails because it can't access the microphone.
There's probably an interesting side channel where a malicious version could (assuming the low-power core doesn't hardcode 'Okay Google') rapidly program different activation phrases to get a reasonably high probability of whether specific things are said.
@david_chisnall @beyondmachines1 Though Joe Average User coud be forgiven for thinking that telling something to turn off means "all off" and not "mostly off," even though "mostly off" is the default for most electronics these days unless you physically cut the power.
-
@david_chisnall @beyondmachines1 Though Joe Average User coud be forgiven for thinking that telling something to turn off means "all off" and not "mostly off," even though "mostly off" is the default for most electronics these days unless you physically cut the power.
@maccruiskeen @beyondmachines1
From a security perspective, they should be equivalent (nothing that can talk to a network sees the microphone data, just a 1-bit wakeup signal). Modulo side channels, of course.
-
@david_chisnall @beyondmachines1 Though Joe Average User coud be forgiven for thinking that telling something to turn off means "all off" and not "mostly off," even though "mostly off" is the default for most electronics these days unless you physically cut the power.
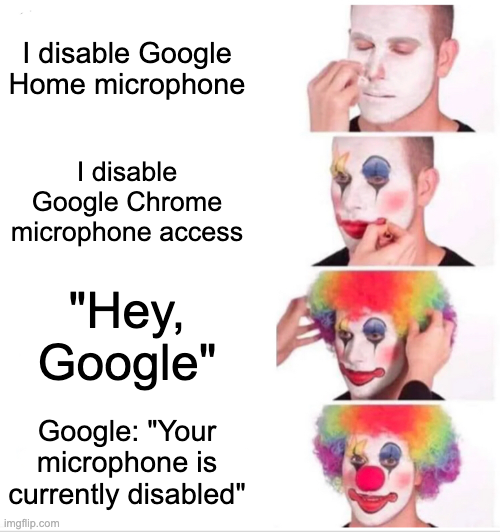
@maccruiskeen @david_chisnall @beyondmachines1
Joe Average User will be thinking:
https://imgflip.com/i/208ldv -
@beyondmachines1 The problem I have is this is behavior I want - because it's proof I am being lied to. If the message were to stop, how would I know?
-
@beyondmachines1 Ah I see your problem, this is a techy thing. To disable microphones in Alexa, Google Home, etc, you need to use a hammer and throw everything into the trash bin outside the house. Be careful what you say outside around the trash bin until the trash is picked up.
You are welcome!
@gbsills @beyondmachines1 You can also disabled the ones in your cell phone the same way: take that hammer and smash your income into thousands of pieces; live on lithium and shards of gorilla glass in your final days alive in the West
-
 E em0nm4stodon@infosec.exchange shared this topic
E em0nm4stodon@infosec.exchange shared this topic