We’ve stumbled across an unknown malware C2 protocol.
-
We’ve stumbled across an unknown malware C2 protocol. Do you know what this is?
 47.83.173.19:5050
47.83.173.19:5050 47.84.203.73:5050
47.84.203.73:5050 xuanwcai[.]com:5050
xuanwcai[.]com:5050 wkaiuahaaxx[.]icu:5050
wkaiuahaaxx[.]icu:5050Characteristic strings in C2 traffic:
Accept: */*frAQBc8Wsa1xVPfvJcrgRYwTiizs2tr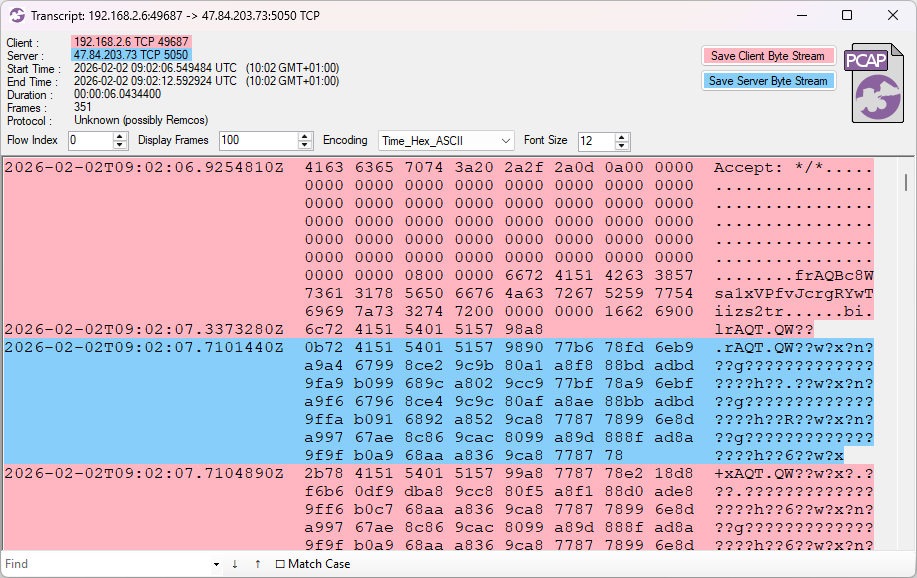
-
We’ve stumbled across an unknown malware C2 protocol. Do you know what this is?
 47.83.173.19:5050
47.83.173.19:5050 47.84.203.73:5050
47.84.203.73:5050 xuanwcai[.]com:5050
xuanwcai[.]com:5050 wkaiuahaaxx[.]icu:5050
wkaiuahaaxx[.]icu:5050Characteristic strings in C2 traffic:
Accept: */*frAQBc8Wsa1xVPfvJcrgRYwTiizs2tr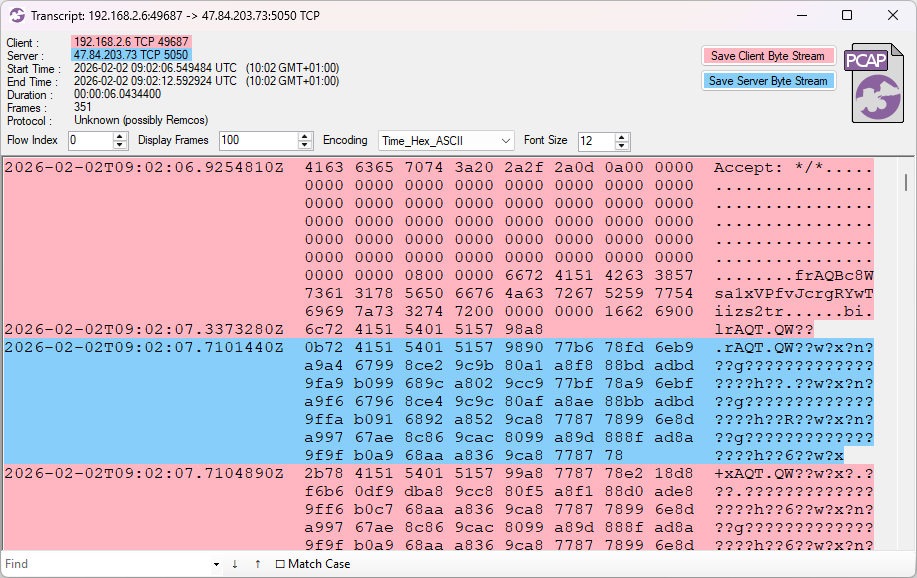
This sample is classified as FatalRAT on JoeSandbox, but the C2 traffic doesn't look like FatalRAT
https://www.joesandbox.com/analysis/1865230/0/html -
This sample is classified as FatalRAT on JoeSandbox, but the C2 traffic doesn't look like FatalRAT
https://www.joesandbox.com/analysis/1865230/0/htmlThis sample is classified as ValleyRAT on ANY.RUN, but the C2 doesn't look like ValleyRAT either
https://app.any.run/tasks/ca8080c4-8dc8-4107-b261-f16a69e5dac1/ -
This sample is classified as ValleyRAT on ANY.RUN, but the C2 doesn't look like ValleyRAT either
https://app.any.run/tasks/ca8080c4-8dc8-4107-b261-f16a69e5dac1/Sample on Triage with the same C2:
https://tria.ge/260207-p7n72aft4c -
Sample on Triage with the same C2:
https://tria.ge/260207-p7n72aft4cFound two more C2 servers with the same
Accept: */*andfrAQBc8Wsa1xVPfvJcrgRYwTiizs2trstrings. These ones run on TCP 5050 as well. 192.253.229.223:5050 (last active December 2025)
192.253.229.223:5050 (last active December 2025) 156.254.20.94:5050 (last active December 2025)
156.254.20.94:5050 (last active December 2025)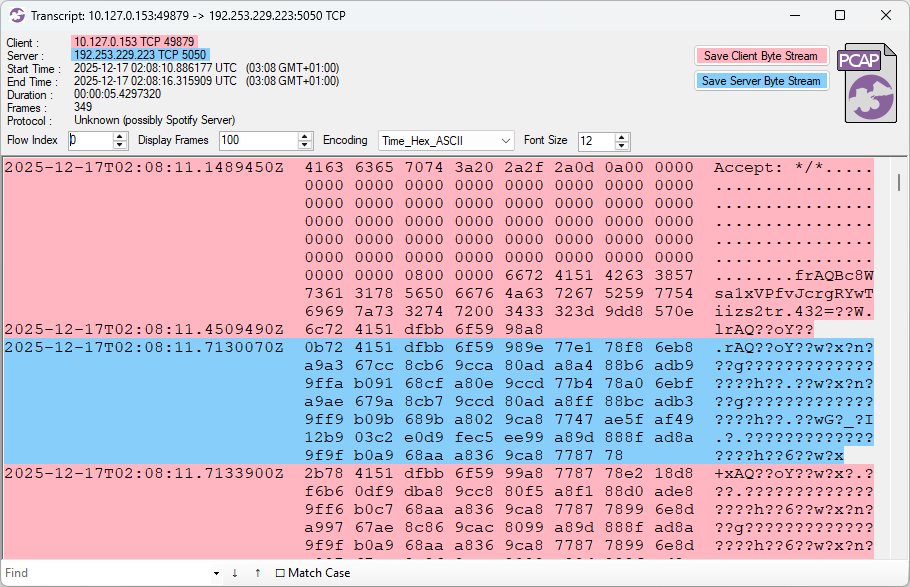
-
Found two more C2 servers with the same
Accept: */*andfrAQBc8Wsa1xVPfvJcrgRYwTiizs2trstrings. These ones run on TCP 5050 as well. 192.253.229.223:5050 (last active December 2025)
192.253.229.223:5050 (last active December 2025) 156.254.20.94:5050 (last active December 2025)
156.254.20.94:5050 (last active December 2025)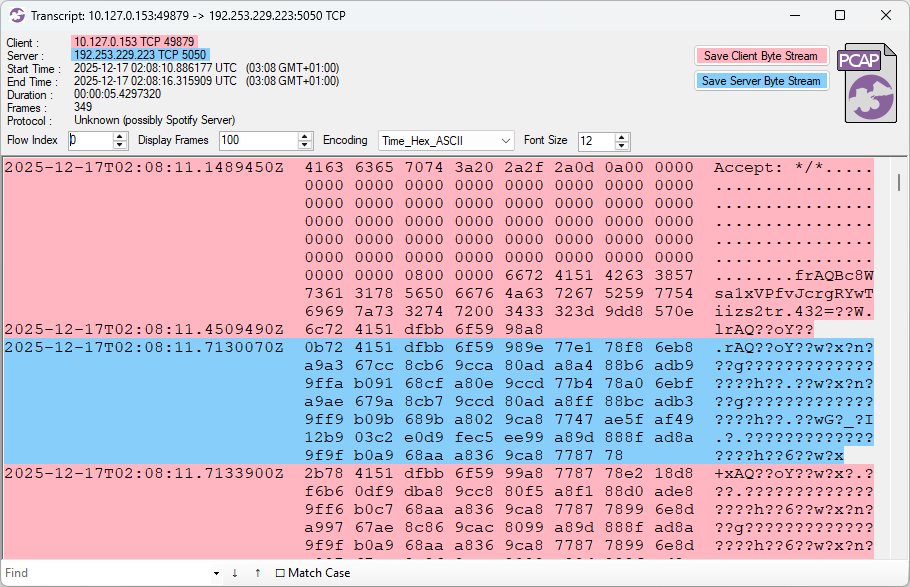
192.253.229.223:5050 on Triage
https://tria.ge/251217-cgb4kafr9y -
192.253.229.223:5050 on Triage
https://tria.ge/251217-cgb4kafr9y156.254.20.94:5050 on ANY.RUN
https://app.any.run/tasks/31811332-56ec-4fff-a134-43a1a699cfc8 -
R relay@relay.infosec.exchange shared this topic
