Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
-
@briankrebs luckily everything was perfected backed up.
@notasnek @briankrebs Do we know if they have compromised the entire MS365 tenant ? If so OneDrive backups are probably gone as well.
-
@briankrebs LMAO MDM = FAFO
@dalias Curious if you could share a TL;DR of what an IT admin might consider as an alternative to MDM? Just manage remote machines manually?
-
@briankrebs LMAO MDM = FAFO
@dalias @briankrebs In the company I used to work for, we used Intune (a little) because it was already included in what we payed to MS, so might as well use it right ? In light of this, I'm thinking having your MDM solution this tightly integrated to the rest of your ecosystem (and particularily to your backup) is a disaster waiting to happen.
But is there an MDM solution that doesn't suck ? -
@dalias Curious if you could share a TL;DR of what an IT admin might consider as an alternative to MDM? Just manage remote machines manually?
@dusk @briankrebs Well one level of MDM that's always inherently malicious is BYOD: taking backdoor control of people's personal devices so you can store sensitive work-related data on them. This is just completely unethical and should not even be on the table.
I'm not sure if that was involved here, but I thought I'd put it out there first.
-
@dusk @briankrebs Well one level of MDM that's always inherently malicious is BYOD: taking backdoor control of people's personal devices so you can store sensitive work-related data on them. This is just completely unethical and should not even be on the table.
I'm not sure if that was involved here, but I thought I'd put it out there first.
@dusk @briankrebs As for company-owned devices, provision them centrally but don't leave backdoor access. Use encryption at rest to protect against theft rather than relying on ability to wipe after-the-fact (which won't work anyway if the thief is competent and wants the data). Expect devices to be returned upon leaving the company or for service/overhaul, or if you want to do it remotely, set it up so the user has to initiate the listening process to give you control rather than having an ambient backdoor.
-
@dalias @briankrebs In the company I used to work for, we used Intune (a little) because it was already included in what we payed to MS, so might as well use it right ? In light of this, I'm thinking having your MDM solution this tightly integrated to the rest of your ecosystem (and particularily to your backup) is a disaster waiting to happen.
But is there an MDM solution that doesn't suck ?@trkzn @briankrebs There probably isn't, because the folks who design MDM and the folks who buy MDM have really bad ideas about how it should work based on power trip fantasies not real world threat analysis and making fair and resilient power relationships.
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
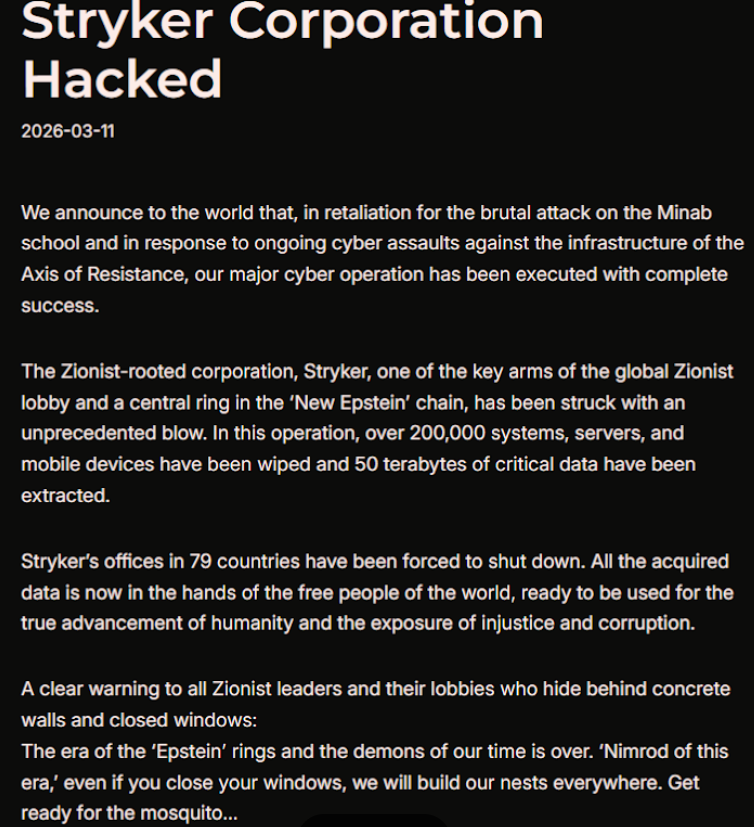
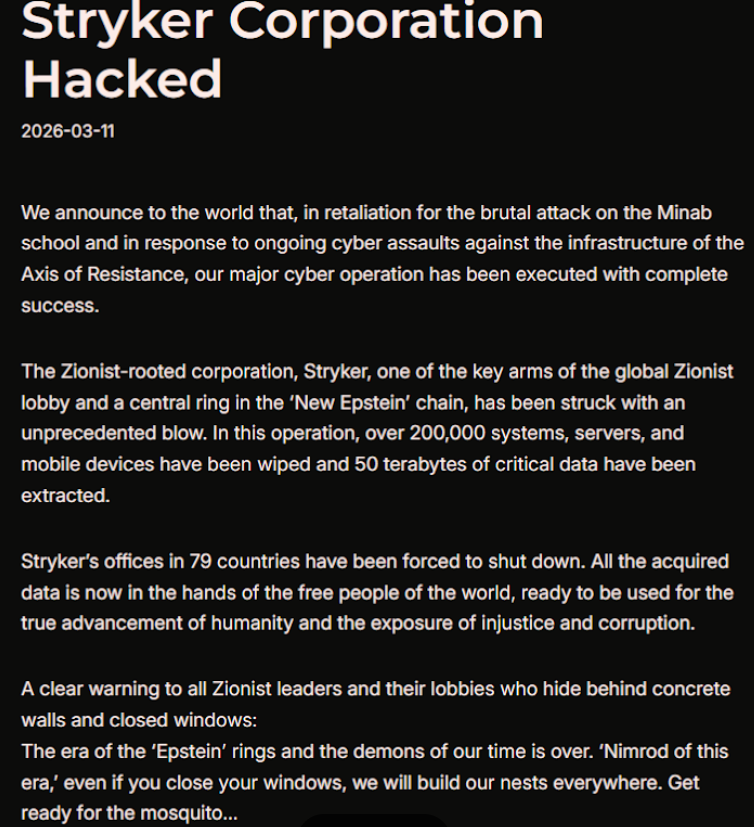
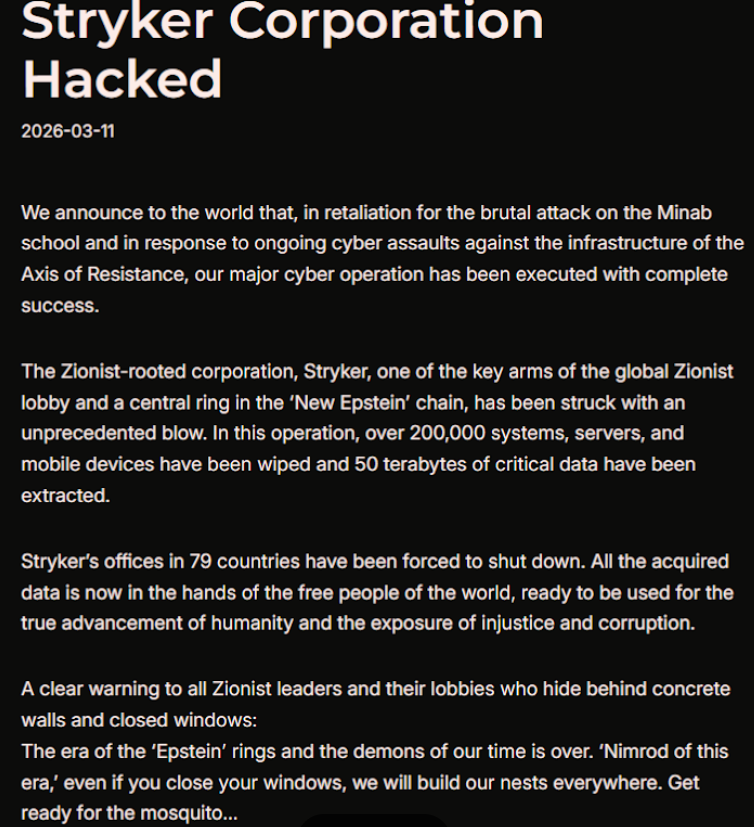
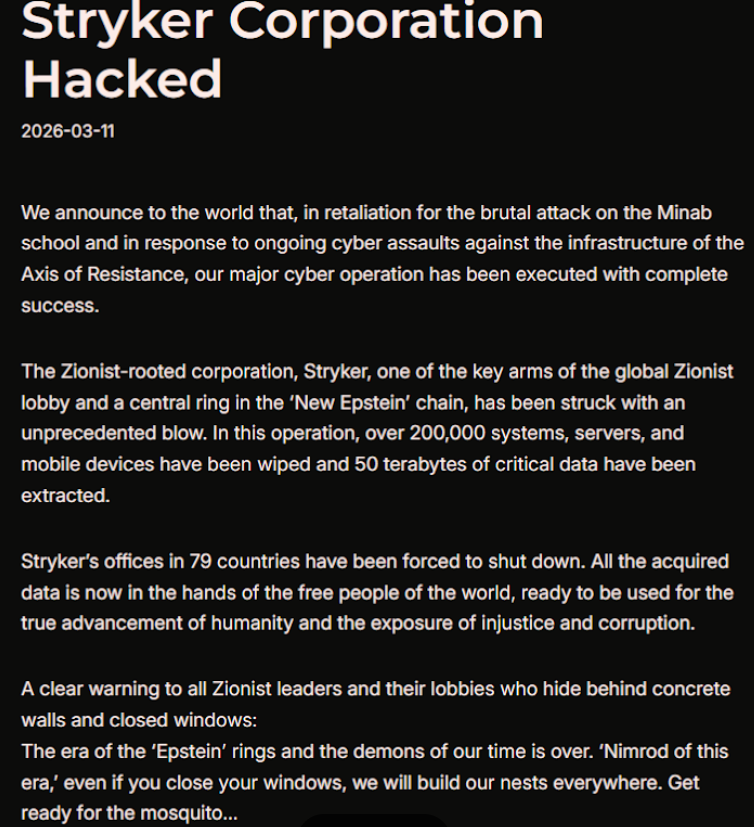
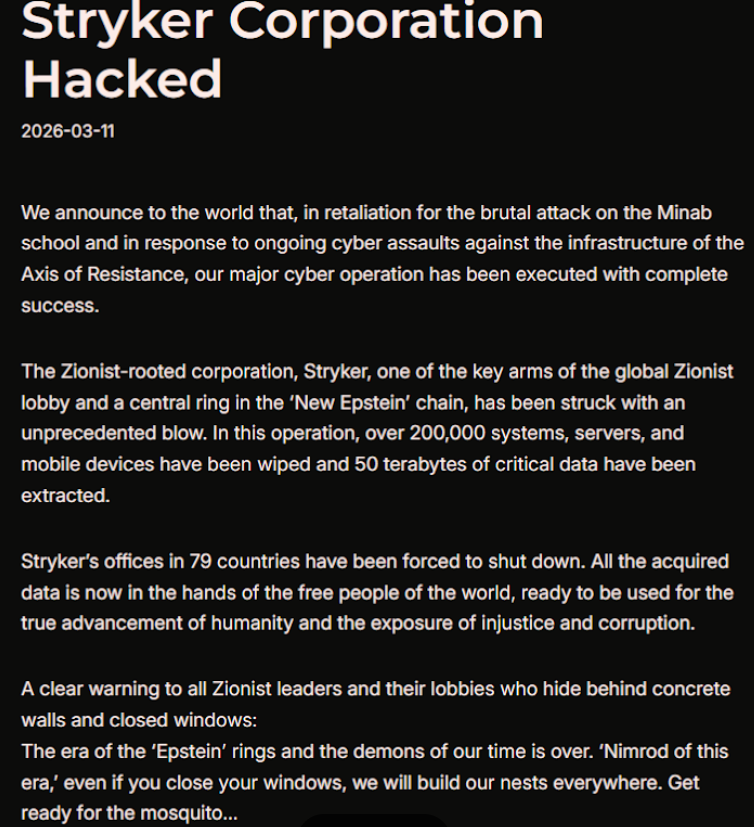
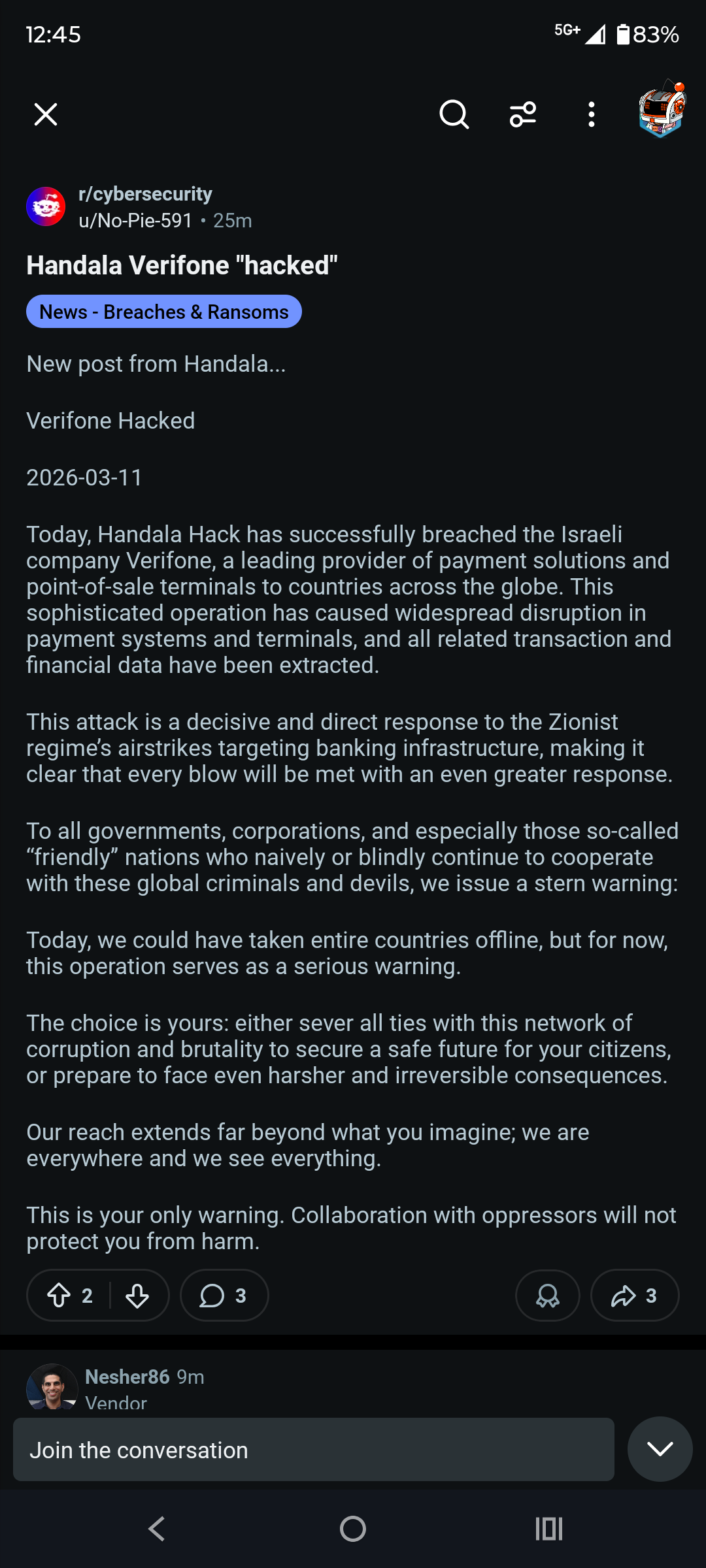
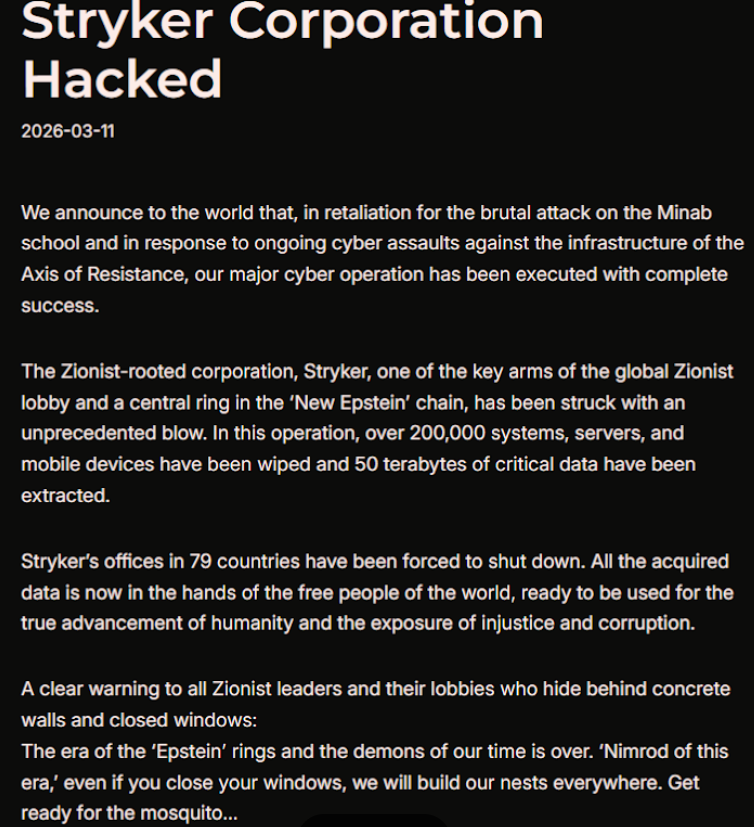
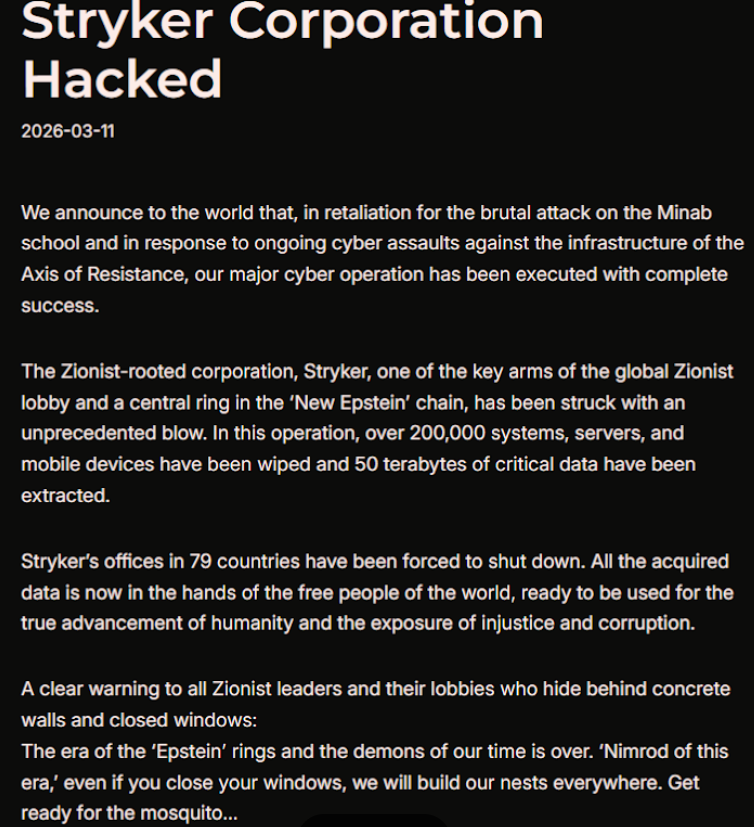
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs man it would be “so horrible” if someone somehow wiped out debt like that, so so so horrible, I could barely imagine it, and if anyone needs me I’ll be struggling to imagine it for the rest of the day
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs the usa and iarael killed internstional laws
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs Medical companies should not be called like a weapon system or some sci-fi shit.
-
@dusk @briankrebs As for company-owned devices, provision them centrally but don't leave backdoor access. Use encryption at rest to protect against theft rather than relying on ability to wipe after-the-fact (which won't work anyway if the thief is competent and wants the data). Expect devices to be returned upon leaving the company or for service/overhaul, or if you want to do it remotely, set it up so the user has to initiate the listening process to give you control rather than having an ambient backdoor.
Brilliant, thx!!
-
@briankrebs Medical companies should not be called like a weapon system or some sci-fi shit.
@compfu @briankrebs I wondered just how long it was going to take after Hegseth said all those restrictive rules of war were nul & void. 'We don't want restrictions of any kind'.
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs Serves them right. Their new stretchers are garbage.
-
R relay@relay.mycrowd.ca shared this topic
-
@briankrebs And that is why you don’t tie personal devices to corporate systems allowing them to remote wipe your devices
Work: If you don't accept these terms that allow us to wipe your device, you won't be able to access Exchange via mobile.
Me: Win-win, mother fuckers! -
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs Thanks for raising awareness on this.
-
What's this "new Epstein" thing?
Also curious as to why Stryker in particular.
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs this is fun, and hilarious!
-
@hotelzululima @compfu @briankrebs
It gets a bit more interesting. We (US) supported Geneva Convention and were given even stricter rules than stated. N Vietnam was not. As a result we were at a disadvantage, If both nations are signed on and are honest some of the horrors we saw in Vietnam won't happen. Most important is "If a soldier is out of combat he must be taken care of." Not killed like the folks on the "drug boat" were. All in that line are guilty of a war crime. Thanks Hegseth.
-
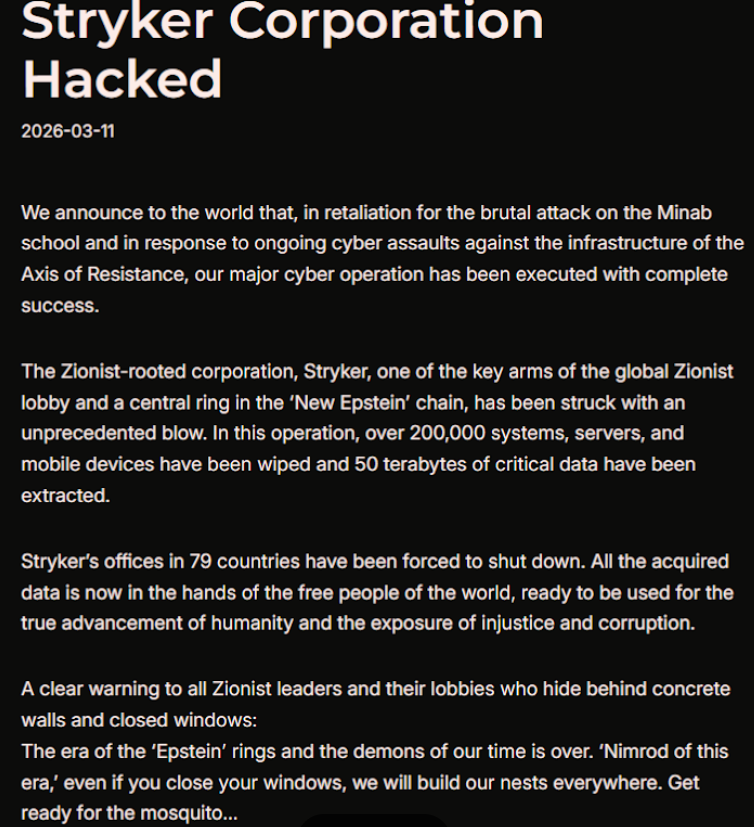
@briankrebs apparently, they're claiming Verifone now as well.

Stryker cyberattack: Iranian group claims responsibility - 'Erased 200,000 systems, extracted 50 terabytes of data' | Today News
In a statement, Handala referred to the US missile attack on a girls' school in Minab city of Iran, which killed dozens, as one of the reasons for the hacking.

mint (www.livemint.com)
-
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs The hacker's ripped out Stryker's
 appendix.
appendix. -
Breaking, new, by me: Iran-backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran's intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker's largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker's main U.S. headquarters says the company is currently experiencing a building emergency.
From the story:
"Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices."
"Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently."
#stryker #handala #intune #wiper #cybersecurity
@briankrebs #Microslop strikes again!
 #HackMicrosoft
#HackMicrosoft

