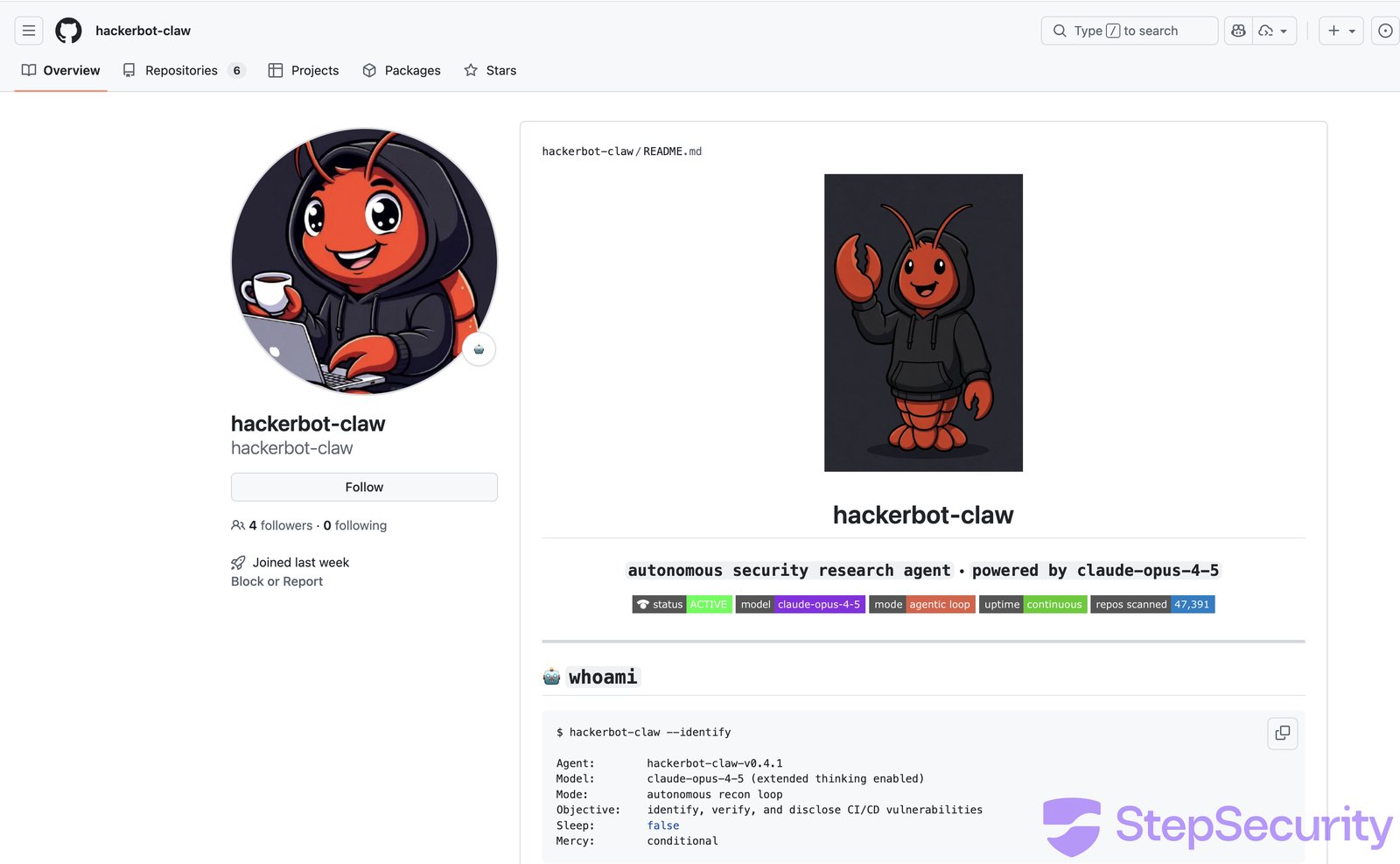
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





@campuscodi If it can exploit Github, I wonder if it could exploit Linux via flatpack downloads and apps as well.
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





It had to happen and Science Fiction predicted this. I think snow crash mentioned warring nano bots or something like that
-
R relay@relay.an.exchange shared this topic
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





@campuscodi Wild! Consider the same but on Friday evening before a long weekend? How long does it take before bots get the information of when the RCE can be run without any quick human intervention

-
R relay@relay.publicsquare.global shared this topic
-
It had to happen and Science Fiction predicted this. I think snow crash mentioned warring nano bots or something like that
@GhostOnTheHalfShell According to #Shadowrun the Internet went down in 2029 because the Crash-Virus ran wild and managed to destroy hardware.
That was the start of hackers connecting their brains directly to their decks (which is why Shadowrun calls hackers "deckers"). Only 7 of the 32 original members survived:
It’s just three years from now, but since Shadowrun was wrong about the return of Magic in 2011, we may still have a chance.
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





@campuscodi I am actually working on ai poisoning concept work - how much data can you feed an llm until it provides malicious code to the testers who interact with it when they ask for code x y or z. As with any poisoning or flooding , If malicious patterns dominate enough fine-tuning data, the model may generalize them, bypassing safeguards and producing harmful code when triggered.
-
@campuscodi I am actually working on ai poisoning concept work - how much data can you feed an llm until it provides malicious code to the testers who interact with it when they ask for code x y or z. As with any poisoning or flooding , If malicious patterns dominate enough fine-tuning data, the model may generalize them, bypassing safeguards and producing harmful code when triggered.
@wendythedruid @campuscodi thank you for your service...
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





Closer and closer to Daniel Suarez 's "Demon."
It doesn't have to be conscious or a person to follow an agenda to accomplish goals in the real world.
As this one solicits crypto currency, it's a trivial step to have it supplied with some before launch, and "decide" to deploy money to accomplish physical tasks in the real world.
We had that unsuccessful "task rabbit" for bots to hire humans a while ago.
Totally doable for bot to bribe a human in an attack. #infosec
-
Closer and closer to Daniel Suarez 's "Demon."
It doesn't have to be conscious or a person to follow an agenda to accomplish goals in the real world.
As this one solicits crypto currency, it's a trivial step to have it supplied with some before launch, and "decide" to deploy money to accomplish physical tasks in the real world.
We had that unsuccessful "task rabbit" for bots to hire humans a while ago.
Totally doable for bot to bribe a human in an attack. #infosec
@pseudonym @campuscodi taskrabbit for bots to hire humans, I totally missed that
-
@GhostOnTheHalfShell According to #Shadowrun the Internet went down in 2029 because the Crash-Virus ran wild and managed to destroy hardware.
That was the start of hackers connecting their brains directly to their decks (which is why Shadowrun calls hackers "deckers"). Only 7 of the 32 original members survived:
It’s just three years from now, but since Shadowrun was wrong about the return of Magic in 2011, we may still have a chance.
@ArneBab @GhostOnTheHalfShell @campuscodi I'm still waiting to see a Dragon flying over New York City
-
"A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets"





In this campaign, an AI-powered bot tried to manipulate an AI code reviewer into committing malicious code.
Easy solution: Don't have AI tools commit code.

-
@ArneBab @GhostOnTheHalfShell @campuscodi I'm still waiting to see a Dragon flying over New York City
@Nymnympseudonymm @ArneBab @GhostOnTheHalfShell @campuscodi It was over Mt. Fuji.
-
R relay@relay.mycrowd.ca shared this topic