In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!).
-
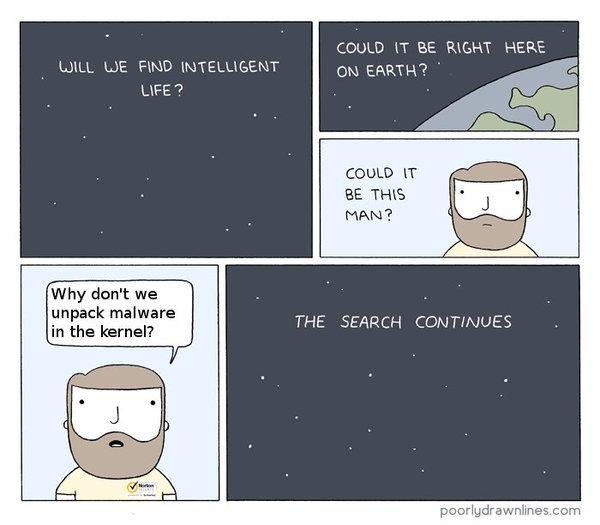
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
-
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
@david_chisnall our company uses BitDefender and basically we have an involuntary 4-day week as Friday at 12PM CET essentially all compute of the company is occupied with a (nested, in VM cases) full-scan for stuff. I never understood how we can self-sabotage us to this degree
-
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
@david_chisnall While I mostly share your views, as a (former) red teamer I have to tell you that endpoint protection is a massive PITA during initial access. They can always be circumvented of course, but a major pain point is that you (as an attacker) can't test the exact configuration that your target(s) run, esp. with cloud analysis that changes by the minute. (A related concept is binary reputation, that will immediately flag unique binaries).
Click Fix and similar, convoluted attacker techniques have evolved exactly because you can't simply deliver malicious executable code to the target environment these days. -
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
-
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
@david_chisnall We’re running SentinelOne on MacBooks. It hasn’t found a malicious file in 12 years but causes all kinds of performance issues and we’re not allowed to turn it off

-
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?
@david_chisnall A few times.
But what is worse, i had to add an exception to malware scanning because i had my code flagged as malware because of retarded shitty antivirus heuristics hammering down anything advanced that used windows kernel API calls.
-
R relay@relay.an.exchange shared this topic