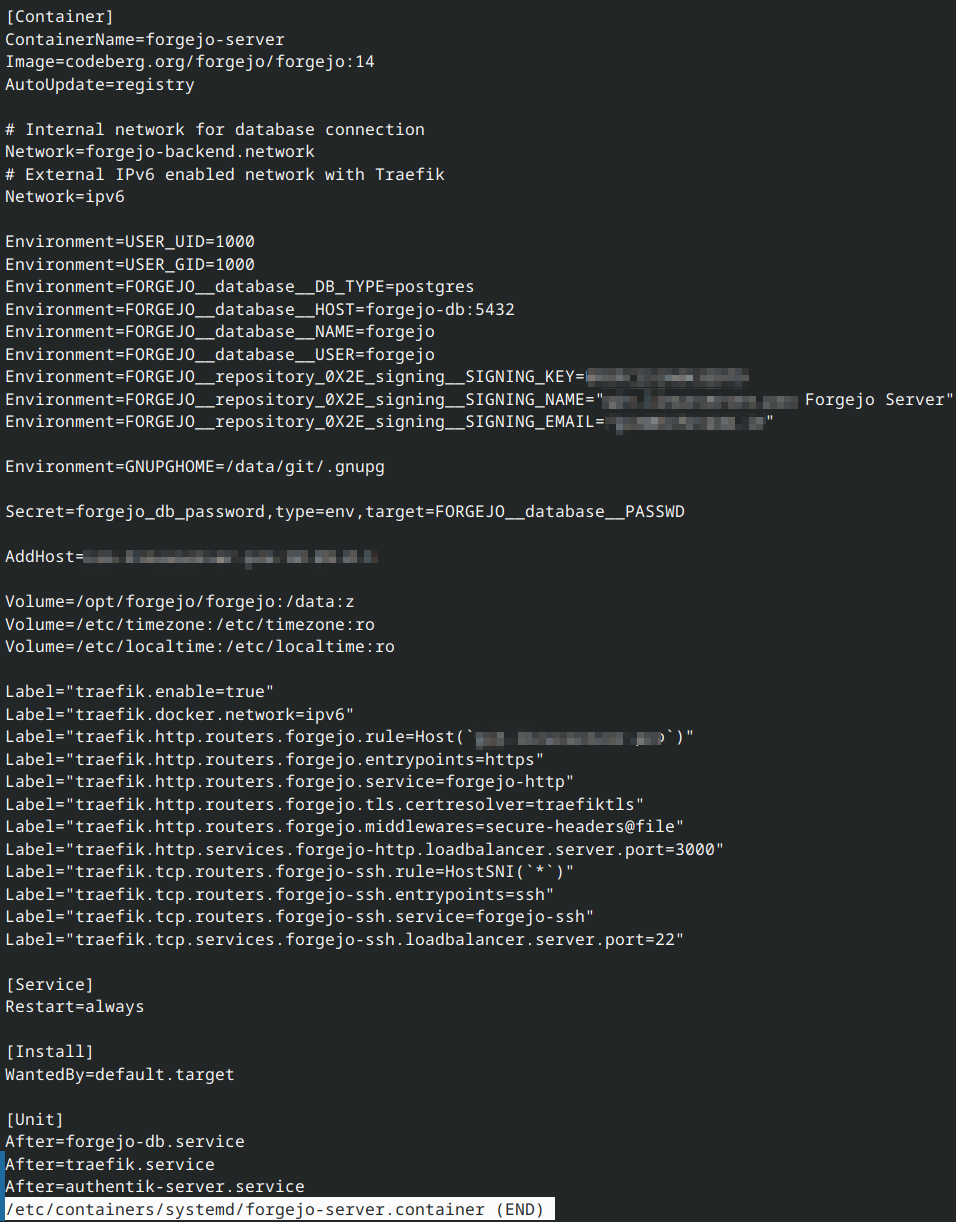
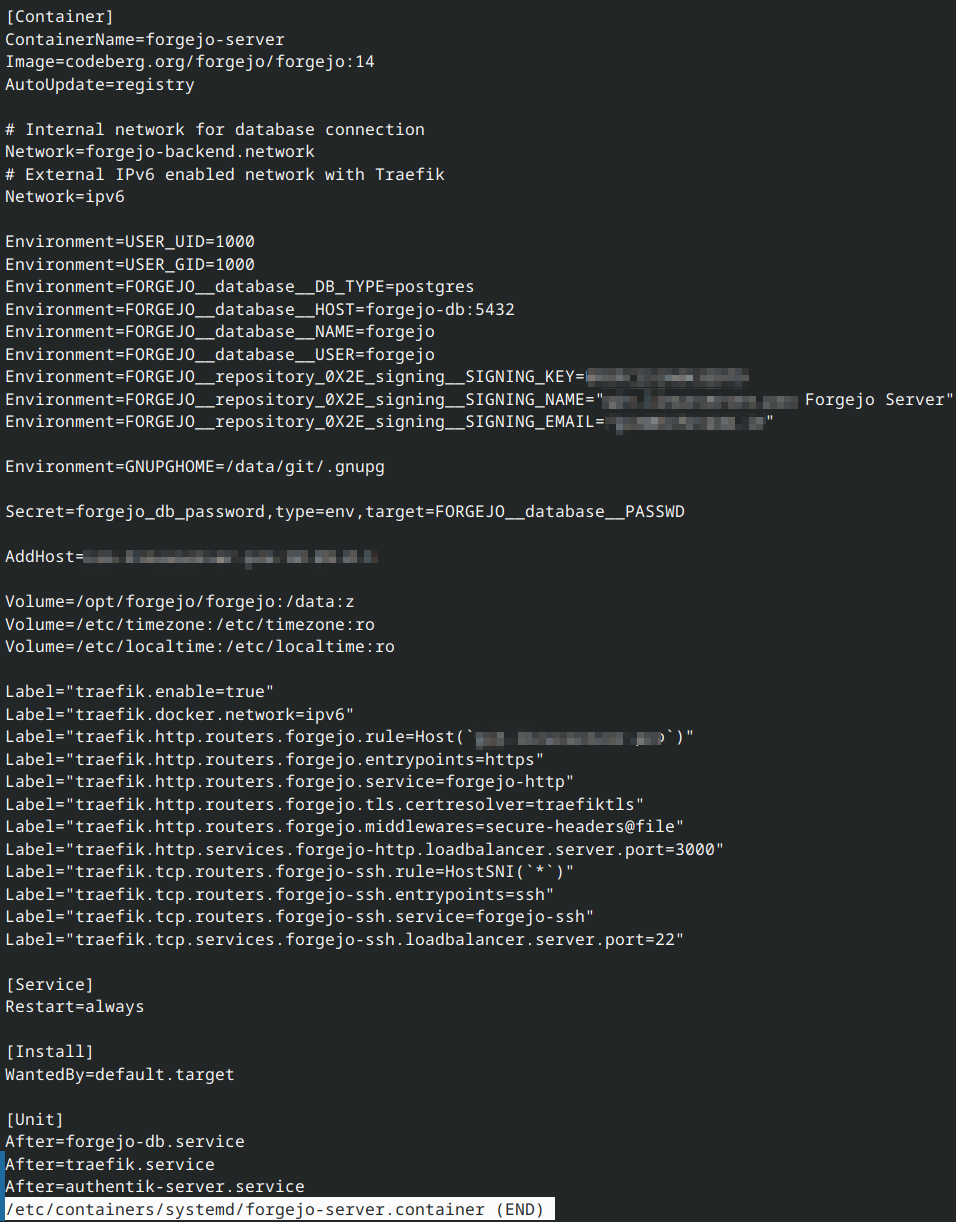
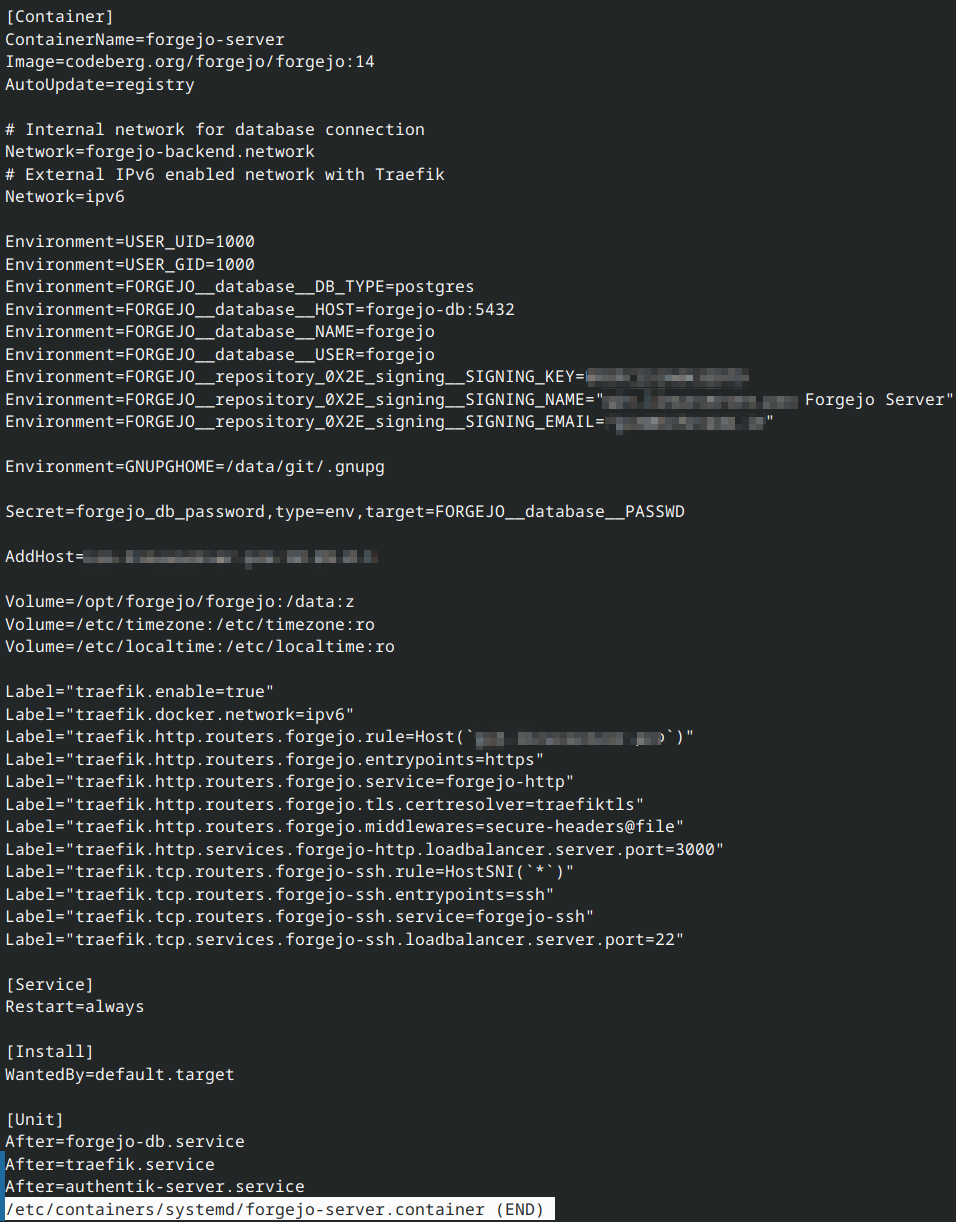
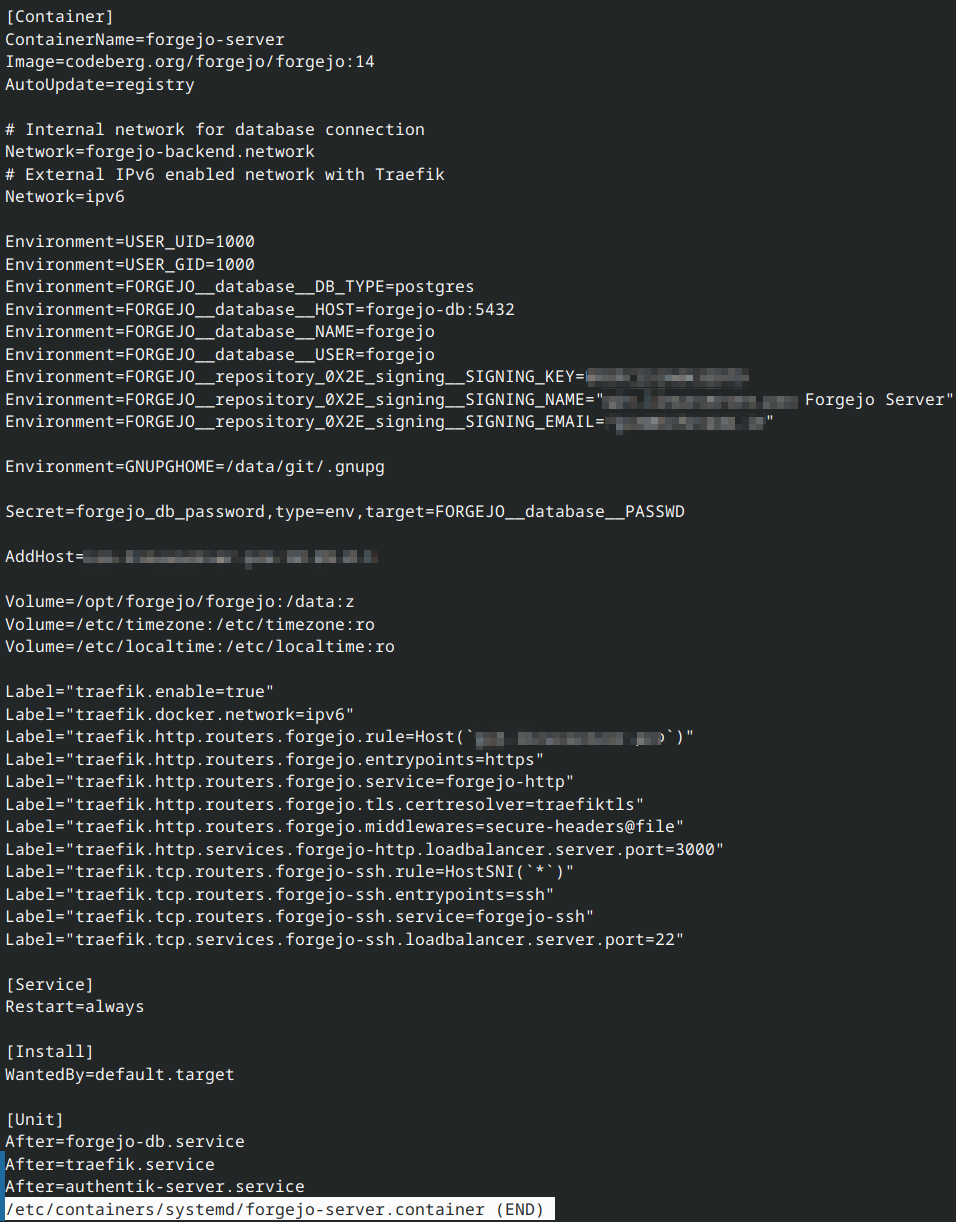
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1.
-
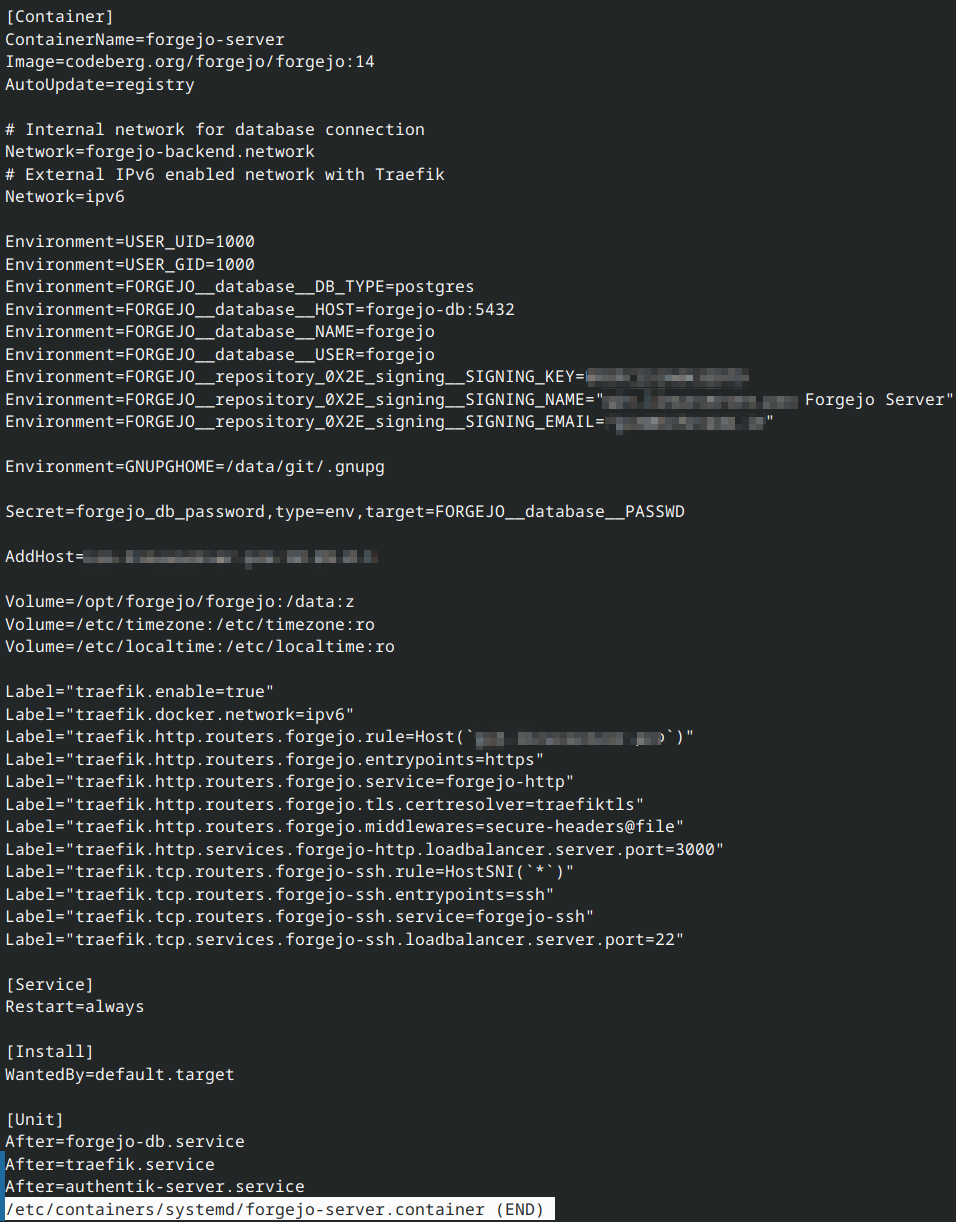
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1. Memory utilization is a bit high, but the system is working absolutely stable for months.
TLS certificates and ingress-routing is handled fully automatically by Traefik and labels, attached to the containers.
Having everything containerized, makes it really easy to clean up
 There's some applications, that I don't even use anymore. Time to clean up.
There's some applications, that I don't even use anymore. Time to clean up.Then I'll continue, replacing the old Authentik installation with Keycloak for my OIDC applications (Forgejo, Wallos etc.)
#linux #redhat #rhel #podman #devops #containers #forgejo #netcup

-
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1. Memory utilization is a bit high, but the system is working absolutely stable for months.
TLS certificates and ingress-routing is handled fully automatically by Traefik and labels, attached to the containers.
Having everything containerized, makes it really easy to clean up
 There's some applications, that I don't even use anymore. Time to clean up.
There's some applications, that I don't even use anymore. Time to clean up.Then I'll continue, replacing the old Authentik installation with Keycloak for my OIDC applications (Forgejo, Wallos etc.)
#linux #redhat #rhel #podman #devops #containers #forgejo #netcup

@Larvitz what hardware are you using?
-
@Larvitz what hardware are you using?
@psyhackological That's a VPS 1000 arm64 from netcup.de. A reasonably cheap VM, running on Ampere Altra CPU cores.
-
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1. Memory utilization is a bit high, but the system is working absolutely stable for months.
TLS certificates and ingress-routing is handled fully automatically by Traefik and labels, attached to the containers.
Having everything containerized, makes it really easy to clean up
 There's some applications, that I don't even use anymore. Time to clean up.
There's some applications, that I don't even use anymore. Time to clean up.Then I'll continue, replacing the old Authentik installation with Keycloak for my OIDC applications (Forgejo, Wallos etc.)
#linux #redhat #rhel #podman #devops #containers #forgejo #netcup

@Larvitz cool setup

Just a small tip, may be useful to you: I use an traefik Addon https://github.com/lukaszraczylo/traefikoidc to use oidc with keycloak even for applications that do not support oauth natively -
@Larvitz cool setup

Just a small tip, may be useful to you: I use an traefik Addon https://github.com/lukaszraczylo/traefikoidc to use oidc with keycloak even for applications that do not support oauth natively@sunscheinwerfer Thanks a lot. Not gonna need a direct integration with Traefik. I just use OIDC to authenticate inside the applications (like forgejo). But good to know, this exists

-
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1. Memory utilization is a bit high, but the system is working absolutely stable for months.
TLS certificates and ingress-routing is handled fully automatically by Traefik and labels, attached to the containers.
Having everything containerized, makes it really easy to clean up
 There's some applications, that I don't even use anymore. Time to clean up.
There's some applications, that I don't even use anymore. Time to clean up.Then I'll continue, replacing the old Authentik installation with Keycloak for my OIDC applications (Forgejo, Wallos etc.)
#linux #redhat #rhel #podman #devops #containers #forgejo #netcup

@Larvitz Why do you replace Authentik with Keycloak? I always found keycloak too heavy, Authentik seemed far easier to handle, especially in a home lab.
And isn't it a lot of hassle to switch all services from one to the other? -
@Larvitz Why do you replace Authentik with Keycloak? I always found keycloak too heavy, Authentik seemed far easier to handle, especially in a home lab.
And isn't it a lot of hassle to switch all services from one to the other?@reep Keycloak WAS heavy before version 20. Now it's a super lightweight, cloud-native application with Quarkus.
My main reason to switch is the better compatibility with Ansible (the collections for Keycloak >20 for automation are just very very good imho)
-
@reep Keycloak WAS heavy before version 20. Now it's a super lightweight, cloud-native application with Quarkus.
My main reason to switch is the better compatibility with Ansible (the collections for Keycloak >20 for automation are just very very good imho)
@Larvitz Thanks a lot! I'm working on my home lab, too. But not that much automation. Wanted to be sure not missing sth. important

-
I run 21 OCI containers with Podman (and Quadlets!) on my ARM aarch64 server on Netcup with Red Hat Enterprise Linux (RHEL) 10.1. Memory utilization is a bit high, but the system is working absolutely stable for months.
TLS certificates and ingress-routing is handled fully automatically by Traefik and labels, attached to the containers.
Having everything containerized, makes it really easy to clean up
 There's some applications, that I don't even use anymore. Time to clean up.
There's some applications, that I don't even use anymore. Time to clean up.Then I'll continue, replacing the old Authentik installation with Keycloak for my OIDC applications (Forgejo, Wallos etc.)
#linux #redhat #rhel #podman #devops #containers #forgejo #netcup

@Larvitz ... I use a similar setup for a couple of services (on netcup, too) - PocketID for passkey-only oauth2 is super lightweight - with oauth2-proxy for those legacy services.
-
@Larvitz ... I use a similar setup for a couple of services (on netcup, too) - PocketID for passkey-only oauth2 is super lightweight - with oauth2-proxy for those legacy services.
@xris oh interesting. Definitely going to take a look at that
 Thank you!
Thank you!
