I found an amazon basics color changing smart light bulb attached to a lamp my neighbor threw in the apartment dumpster.
-
@MLE_online
Oh cool. A new ESP32 board source.
It's even on a desolderable module.
And ESP32 is more hackable than the Silabs EFR32 in IKEA Trodfri's.
At least until I port the Gekkokapula firmware to the module I pulled form one and get on 2.4GHz FM with one.@ftg I'm not getting anywhere with connecting to the module, however. I've got it wired up to an FTDI device, but esptools fails to connect to it, and I don't know why
-
@MLE_online @RueNahcMohr Cool. Cheaper than making an assembly line. Neat use for it.
@MLE_online Someone could sniff the bluetooth to see what it sends/receives, then create code for phone or PC (if it has bluetooth installed) to mimic transfers. Such a person would probably want a working app to watch, so they know which data each command sends/receives. Without that, it would be difficult. Unless the bulb came with an API, which should make it very easy.
-
@ftg I'm not getting anywhere with connecting to the module, however. I've got it wired up to an FTDI device, but esptools fails to connect to it, and I don't know why
@MLE_online @ftg
There's probably a requirement to pull a particular pin down at power on to enable the ROM loader. -
Ok, it's controlling a BP1838 3 channel dimmable LED driver chip: https://datasheet4u.com/datasheets/BPS/BP1638CJ/1495890
If someone out there is smart and wants to try throwing some code together to see if it will work outside of the amazon ecosystem, let me know and I'll try loading it onto the ESP32
@MLE_online You could probably just throw tasmota32.factory.bin on there but I can’t see anything that says it supports the BP1838. http://ota.tasmota.com/tasmota32/release/
-
@MLE_online I'd be surprised if they took effort to lock people out, but I guess it's possible that they use a blanket approach with code signing, since it *does* represent attack surface
@SnoopJ @MLE_online Even if they set the 'no read' bit, what matters is the processor's approach to it. Some processors will still let you clear that bit (and thus wipe the on-board flash), while others won't, making the stupid thing e-waste (I'm scowling at you to Infineon). I've not done esp32, so I don't know their approach.
-
@projectgus @MLE_online From what I see, its an esp32. which, IS halarious.
-
@scribblesonnapkins @SnoopJ I wouldn't know how to do any of that
@MLE_online @SnoopJ
It's not as complicated as it sounds. Is it something you want to explore? -
It looks like it's specifically one of these
ACK Solution
Espressif offers an easy way for users to build Alexa-connected devices with Espressif’s Alexa Connect Kit (ACK) hardware and software.
Espressif Systems (www.espressif.com)
@MLE_online In case it's of interest to anyone reading this: the datasheet indicates these can be locked down using eFuse bits that "can't be unset" (paraphrase) I would expect these to be set on an IoT device (tho' some of the products I've seen written about here… yeesh. so you never know)
I didn't find info for ESP32 about resetting these, but for AVR chips this has reportedly been possible, with some detail here: https://web.archive.org/web/20210506151334/https://sites.google.com/site/pbykec/projects/index/hvsp
hopefully it gives some helpful clues. -
@scribblesonnapkins @MLE_online it looks like the kind of fault injection you're thinking of was performed on a cousin chip, I would guess the secure boot is pretty much the same across the family of chips and would be susceptible to the same attack:
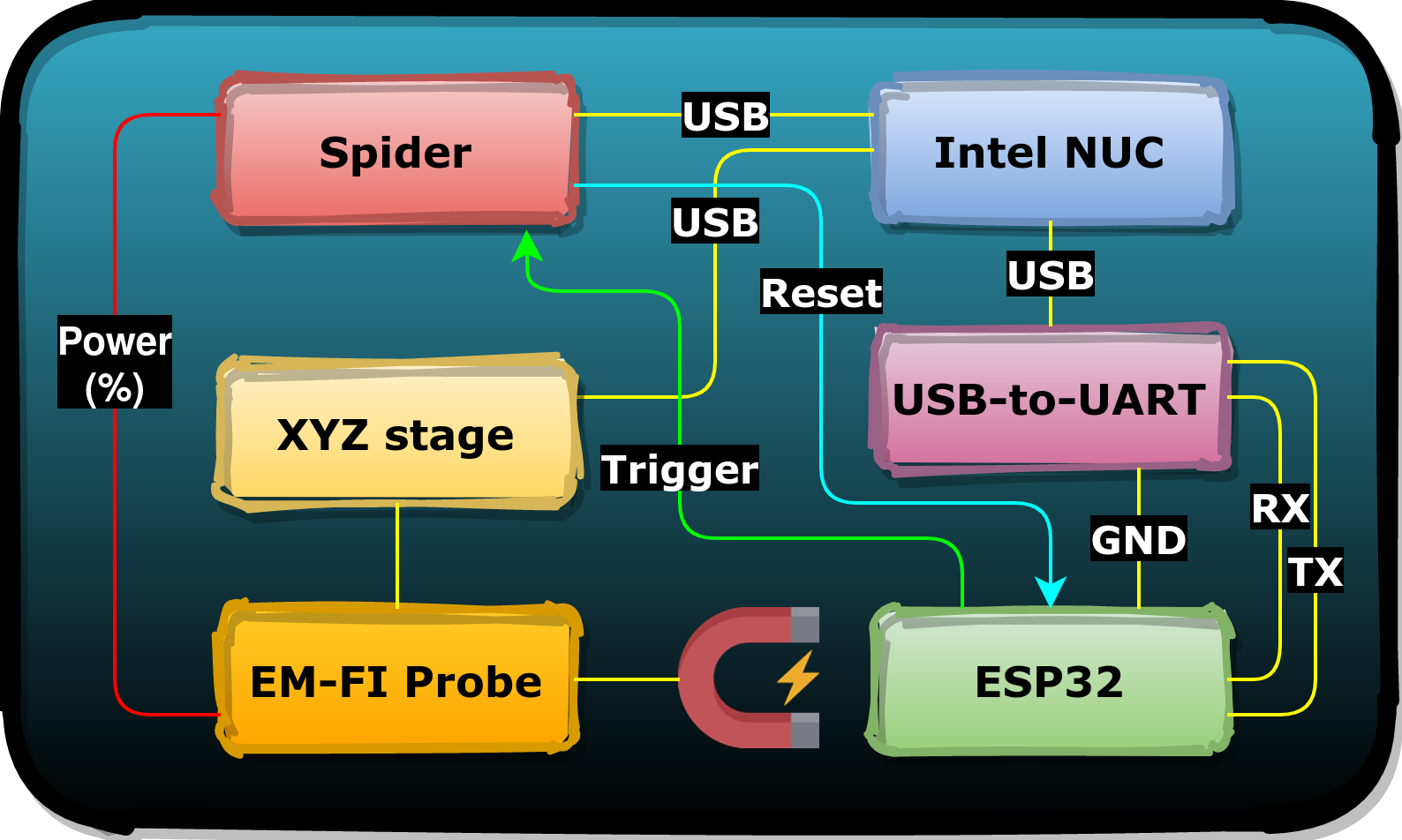
Espressif ESP32: Bypassing Secure Boot using EMFI
Raelize provides top-notch embedded device security serrvices like consultancy, testing, research and training.

(raelize.com)
pretty neat, I like that write-up quite well
@SnoopJ @MLE_online That's one way. There are also fast dips and spikes in the power rails and glitches of other forms.
You can also make micro probes and with the chip decapped probe the chip directly. Those fuses have been know to be made at larger feature sizes.
-
@maehw That seems promising. I'm not really sure where to start though
@MLE_online You'd need to find UART TX/RX + GND + BOOT signal for serial bootloader access. And a USB/serial converter on your PC. But I don't really want to drag you into that rabbit hole. Still got an IoT device on my desk myself.

-
@projectgus @MLE_online the question might be - did they leave an arduino boot loader on it. I'm thinking yes.
-
@vxo @botvolution You should explain what AB 2047 is for people who don't know what that is.
The lawmaker proposing that bill is also proposing to require drivers licenses for ebike. She's on a roll with stupid ideas right now
@MLE_online
Does she have the "Karen" haircut?
@botvolution -
R relay@relay.infosec.exchange shared this topic
