Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically 👏.
-
@thaodan @fluffykittycat @merill Why?
The keys and such associated with the authenticator app should be in a TPM. Something the bootloader can't touch. It can't get the private key to then send it to whoever.
The bootloader could attack in other ways and get the info you're accessing once logged in, but I don't think it can mess about or bypass the actual security mechanism.
I think they're trying to sell bullshit here so the ignorant support them as they lock us all down.
@crazyeddie @fluffykittycat @merill The bootloader itself isn't the concern but the kernel and what is started afterwards.
It is a factor even if they only use it as an excuse. Most phones don't have a TPM but an ARM trustzone which can run a software TPM. The problem is that modifying or writing isn't possible low level only over the OS or vendor API's provided. -
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

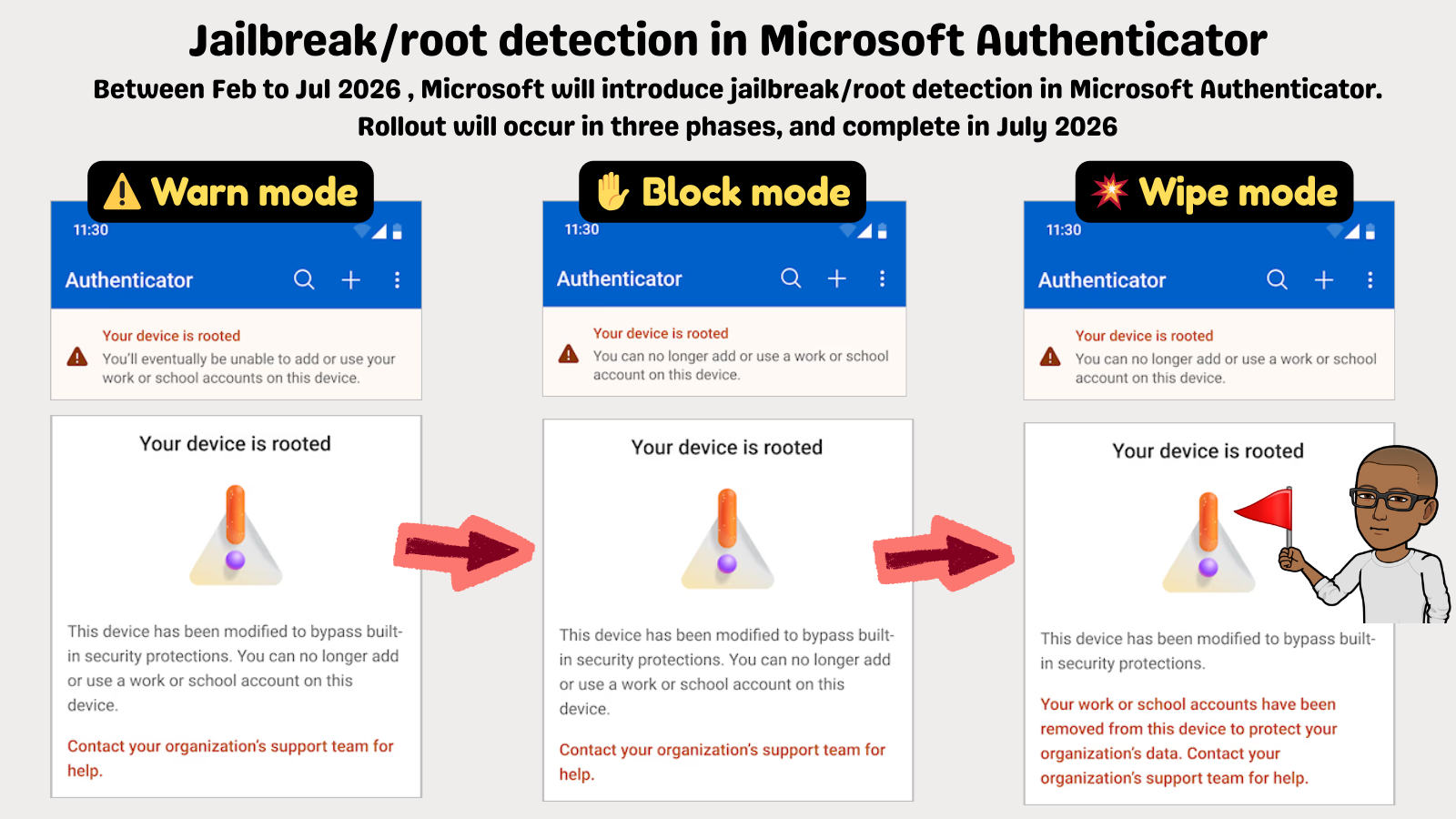
3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill I wonder who of the people complaining here do…
1. … own a rooted / jailbroken phone
2. … have Microsoft Authenticator installed on this phone
3. … do use MS Authenticator in combination with an Azure Active Directory account. -
R relay@relay.infosec.exchange shared this topic
-
@thaodan @fluffykittycat @merill Why?
The keys and such associated with the authenticator app should be in a TPM. Something the bootloader can't touch. It can't get the private key to then send it to whoever.
The bootloader could attack in other ways and get the info you're accessing once logged in, but I don't think it can mess about or bypass the actual security mechanism.
I think they're trying to sell bullshit here so the ignorant support them as they lock us all down.
@crazyeddie @thaodan @merill unlocked bootloaders are a moral imperitive. Not to mention all the ewaste created by locked devices not being repurporsable
-
Soo instead of just rooting a phone one needs now to also deploy 38473894 shady scripts and workarounds to hide it from Microsoft Authenticator?
Congratulation on improving security (NOT).
-
And make your employer pay for it. I got my work phone when I refused to put a similarly shitty 2FA app onto my personal one.
I just said I've a PinePhone with Postmarket OS and I'm not going to buy a new one just for that. + I asked if they'd cover damages for any data deleted because of someone hitting the "wipe phone" button in the MDM that would have come with it accidentally (or on purpose).
The phone was cheaper for them than continuing the discussion btw

-
@merill I'm gonna go out on a limb here and say that users that jailbreak their own private device wouldn't use MS Authenticator, and on company devices jailbreak wasn't allowed anyway.
@silhouette @merill people are expected to put this on their personal devices
-
@merill TIL people actually use the MS authenticator
@Longplay_Games @merill not by choice
-
@silhouette @merill people are expected to put this on their personal devices
@fluffykittycat @merill ah, the famous "use your own private resources for the benefit of the company".
-
@crazyeddie @thaodan @merill unlocked bootloaders are a moral imperitive. Not to mention all the ewaste created by locked devices not being repurporsable
@fluffykittycat @merill @crazyeddie Context? Nobody in the thread said that devices where users can't unlock bootloaders are a good thing.
Users should just be able to relock it. Locking bootloaders doesn't block flashing it just ensures that only code signing with the owner of the keys in the bootloader can be used, the owner of these keys can be the user. -
@fluffykittycat @merill @crazyeddie Context? Nobody in the thread said that devices where users can't unlock bootloaders are a good thing.
Users should just be able to relock it. Locking bootloaders doesn't block flashing it just ensures that only code signing with the owner of the keys in the bootloader can be used, the owner of these keys can be the user.@thaodan @fluffykittycat @merill Yeah, I can't re-lock my phone or I believe even put the bootloader into write-only. Sucks.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill what the fuck. You all really want to kill open computing, don't you.
-
@thaodan @fluffykittycat @merill Yeah, I can't re-lock my phone or I believe even put the bootloader into write-only. Sucks.
@crazyeddie @thaodan @merill yeah, locked bootloaders imply the person who purchased it doesn't get full ownership rights over it
-
@merill magisk module to hide root incoming in 3, 2, 1...
@BernardSheppard @merill it exists
Just not for android 16 -
Wow. So a LOT of you folks are not happy.
The good news is your org can still allow you to use passkeys and other Authenticator apps.
@merill
Wait you were actually saying it as a good thing???? -
@crazyeddie @thaodan @merill yeah, locked bootloaders imply the person who purchased it doesn't get full ownership rights over it
@fluffykittycat @crazyeddie @merill You have to separate the technical from the ideological part. As long as the user has the control for en- and disable the bootloader signature verification they are perfectly fine. There are parts of the device users shouldn't reflash thou such as the radio configuration.
-
@merill I wonder who of the people complaining here do…
1. … own a rooted / jailbroken phone
2. … have Microsoft Authenticator installed on this phone
3. … do use MS Authenticator in combination with an Azure Active Directory account.@kontrollierterWahnwitz@sueden.social anyone meeting criteria 1 who are required to use MS Authenticator for work.
-
Microsoft Authenticator is about to wipe work accounts from jailbroken/rooted phones automatically
 .
.No IT config needed.

3-phase rollout starting Feb 2026:
 ️ Warn →
️ Warn →  Block →
Block →  ️ Wipe
️ WipeLet your help desk and security teams know.
@merill Yikes.
-
@fluffykittycat @crazyeddie @merill You have to separate the technical from the ideological part. As long as the user has the control for en- and disable the bootloader signature verification they are perfectly fine. There are parts of the device users shouldn't reflash thou such as the radio configuration.
@thaodan @crazyeddie @merill why should we expect Microsoft to.honor that? We know they won't
-
@BernardSheppard @merill it exists
Just not for android 16@Kuniti_shino @merill I haven't had need for magisk / shamiko for a while now, but under Android 15, they worked perfectly.
Root, recompile to defeat certificate pinning, MITM, hide root and then using something like http toolkit to work out what an application was doing was pretty straightforward.
Reverse engineering for everyone.
-
@fluffykittycat @merill ah, the famous "use your own private resources for the benefit of the company".
@silhouette@dumbfuckingweb.site @fluffykittycat@furry.engineer @merill@infosec.exchange how else can we call you when you're supposedly sleeping or on vacation?