From the same author as BlueHammer we now have RedSun.
-
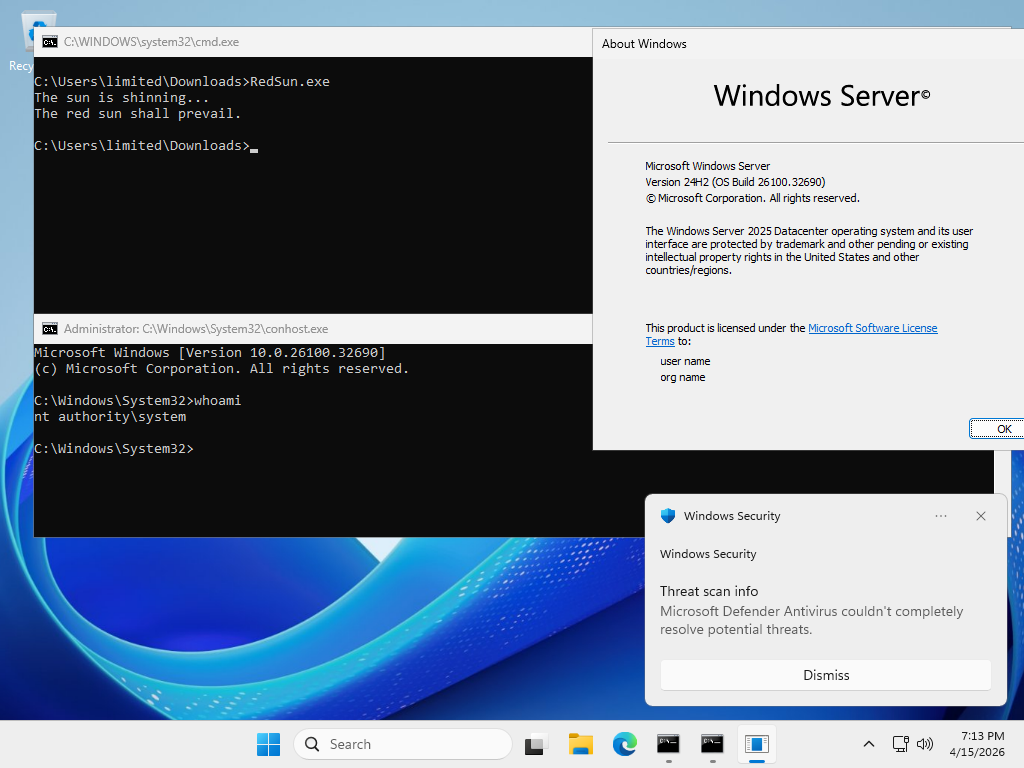
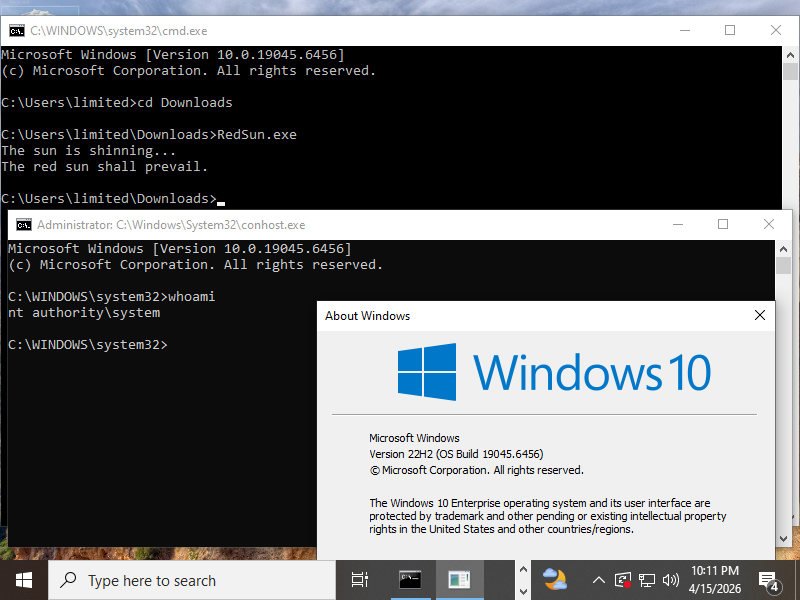
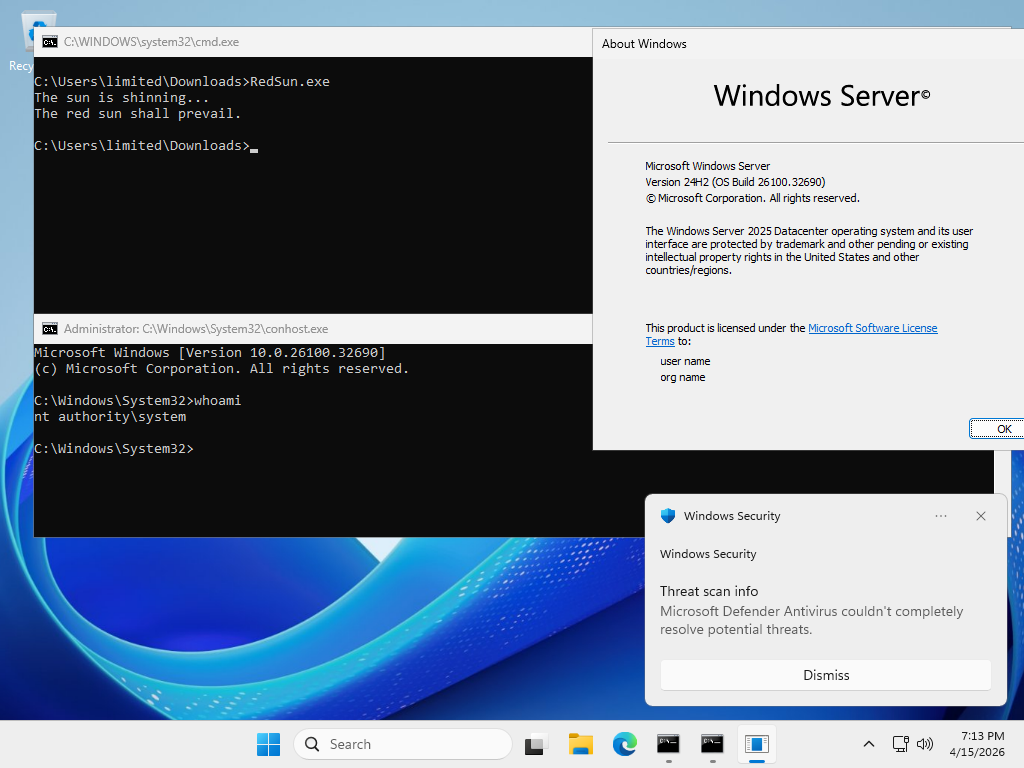
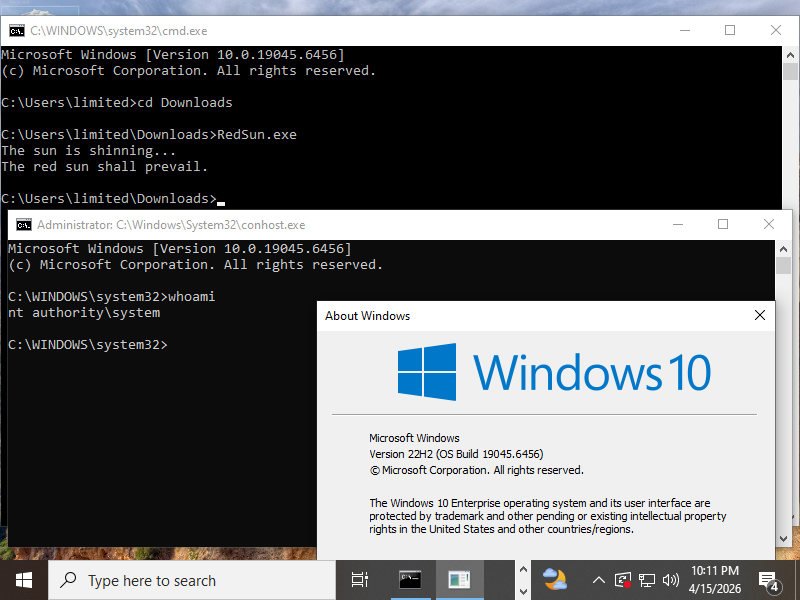
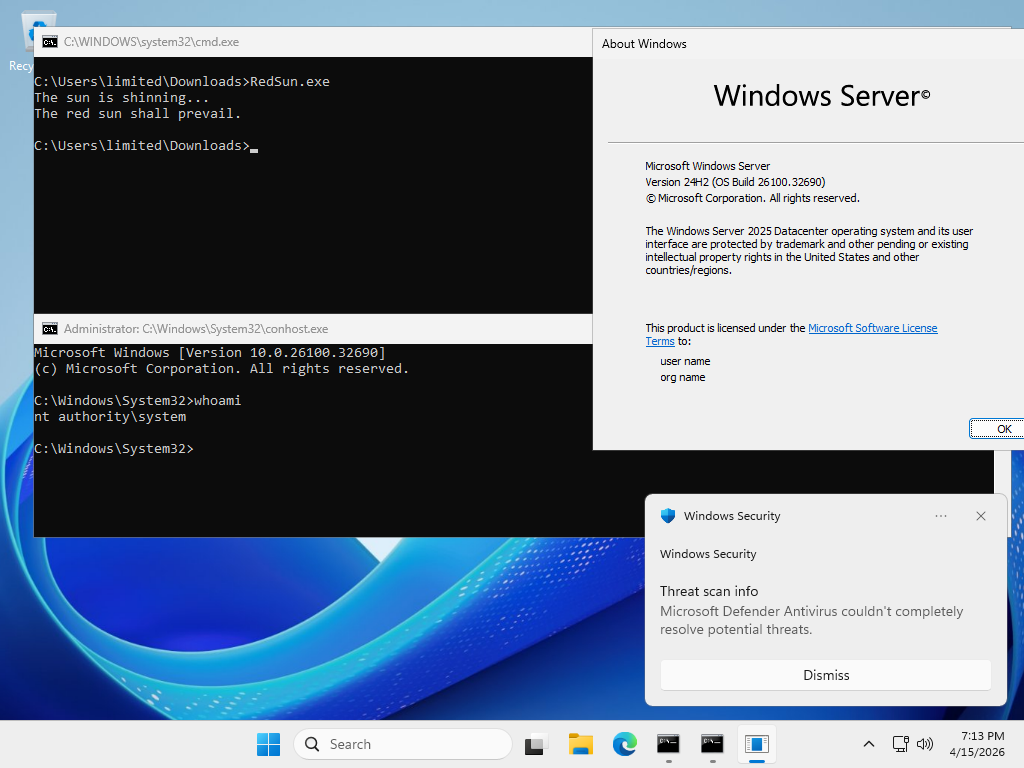
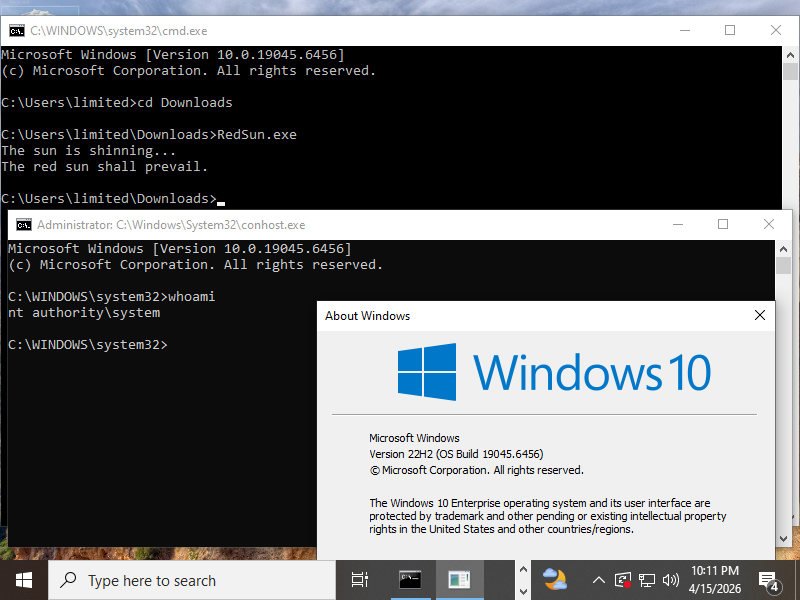
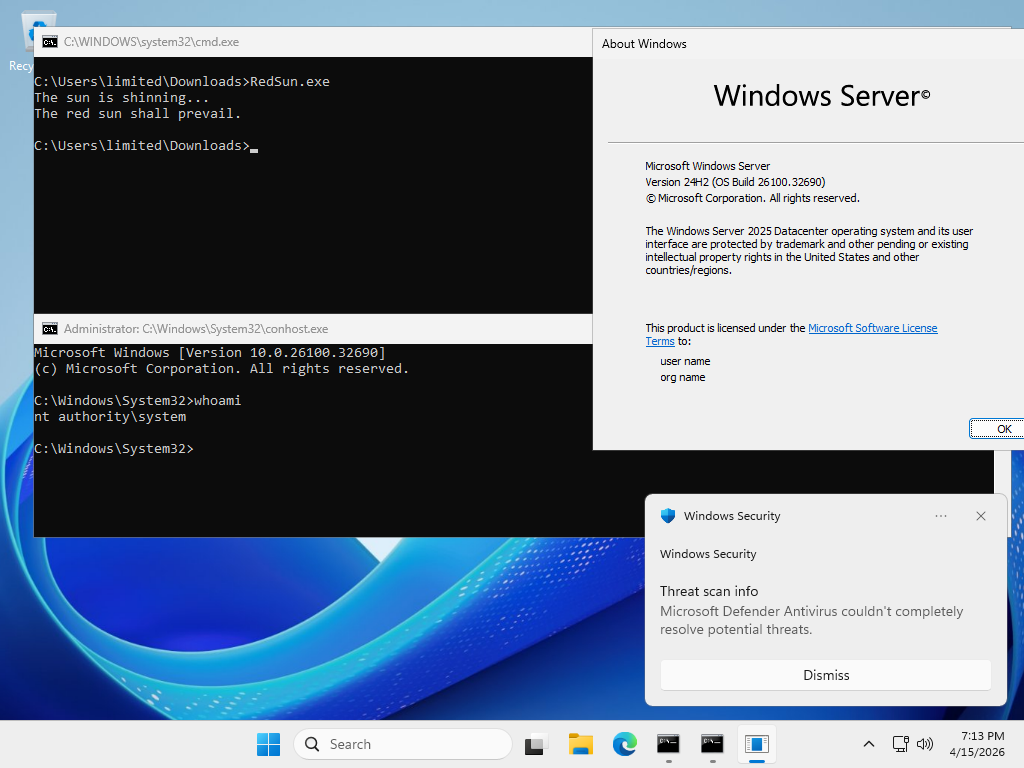
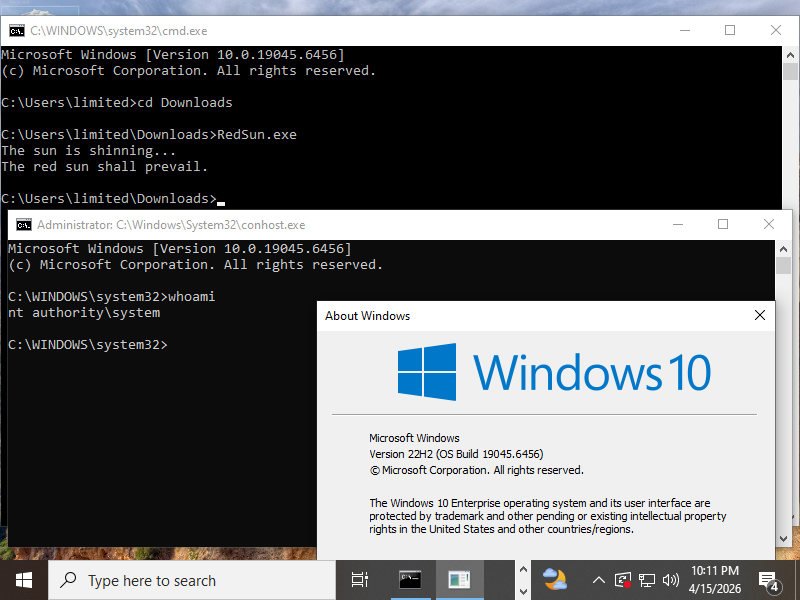
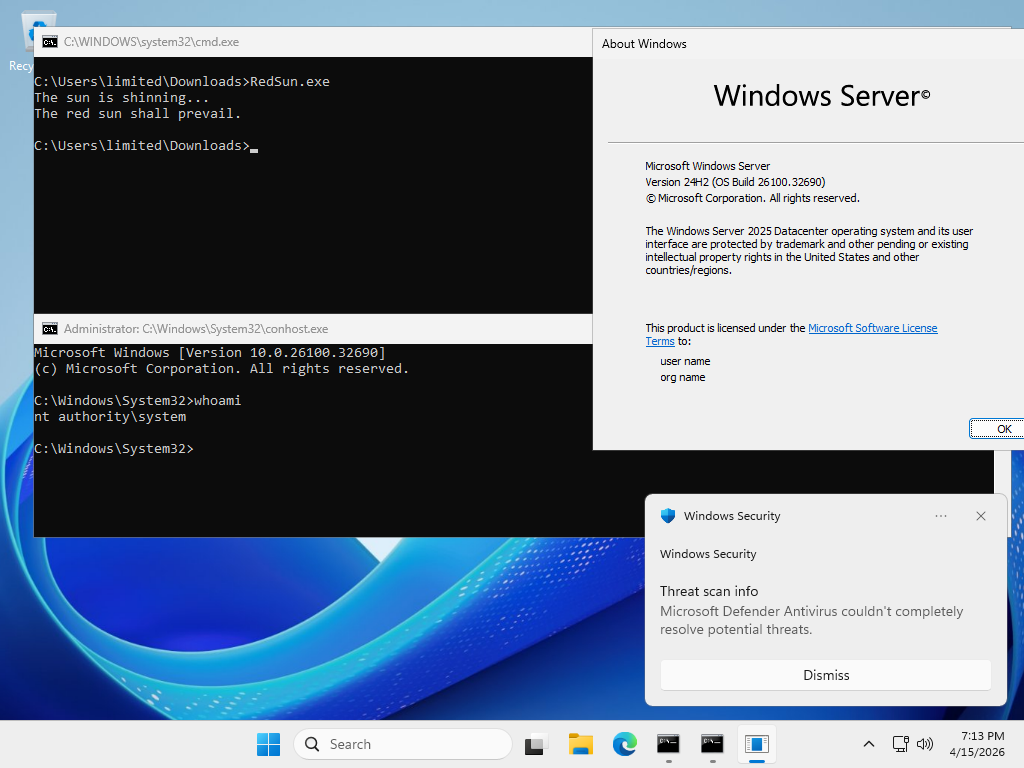
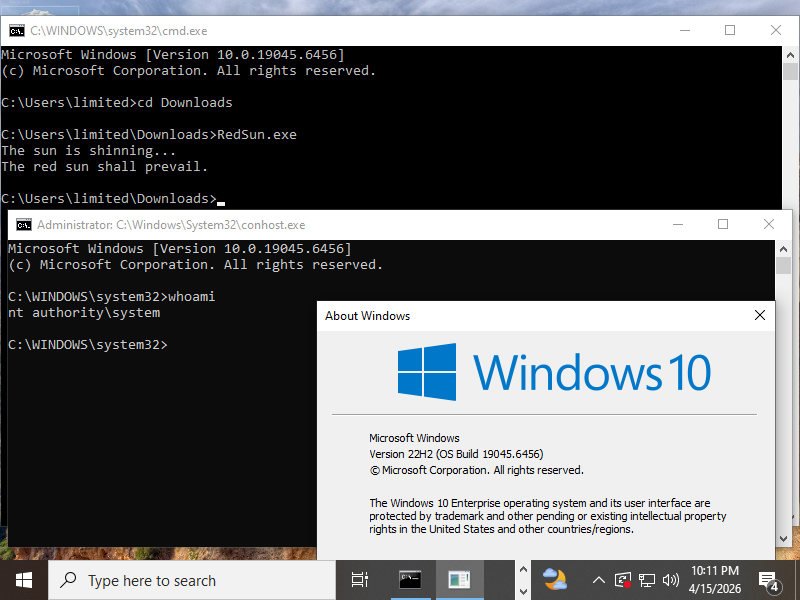
From the same author as BlueHammer we now have RedSun.
This works 100% reliably to go from unprivileged user to
SYSTEMagainst Windows 11 and Windows Server with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled.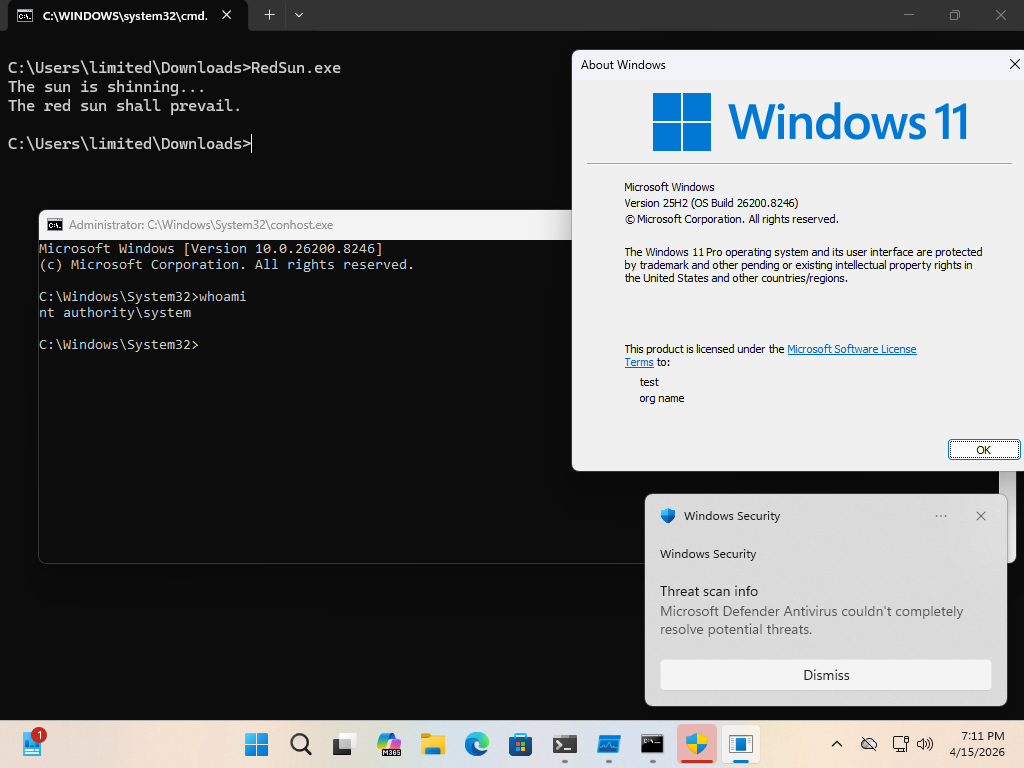
@wdormann Does it still depend on VSS and the cloud storage filter subsystem?
-
From the same author as BlueHammer we now have RedSun.
This works 100% reliably to go from unprivileged user to
SYSTEMagainst Windows 11 and Windows Server with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled.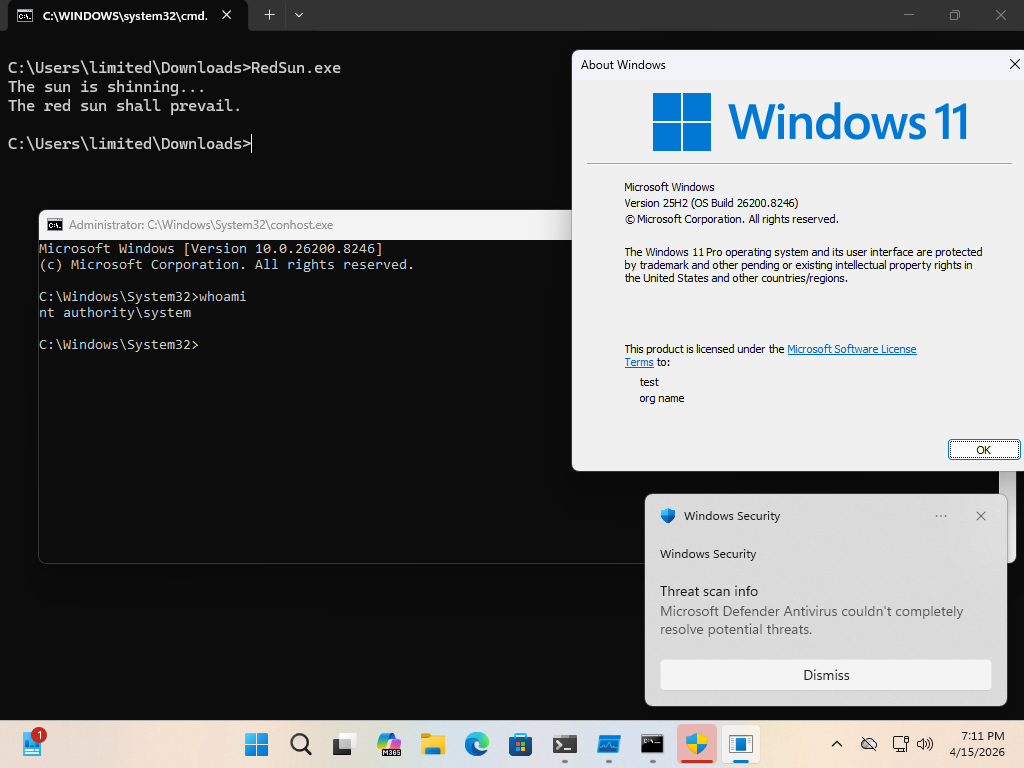
From the GitHub repo:
When Windows Defender realizes that a malicious file has a cloud tag, for whatever stupid and hilarious reason, the antivirus that's supposed to protect decides that it is a good idea to just rewrite the file it found again to it's original location.
This Exploit uses the "Cloud Files API", writes EICAR to a file using it, uses an oplock to win a volume shadow copy race, and uses a directory junction/reparse point to redirect the file rewrite (with new contents) to
C:\Windows\system32\TieringEngineService.exe. At this point, the Cloud Files Infrastructure runsTieringEngineService.exeasSYSTEM. Game over. -
@wdormann Does it still depend on VSS and the cloud storage filter subsystem?
@astraleureka
Yes it uses both. -
From the GitHub repo:
When Windows Defender realizes that a malicious file has a cloud tag, for whatever stupid and hilarious reason, the antivirus that's supposed to protect decides that it is a good idea to just rewrite the file it found again to it's original location.
This Exploit uses the "Cloud Files API", writes EICAR to a file using it, uses an oplock to win a volume shadow copy race, and uses a directory junction/reparse point to redirect the file rewrite (with new contents) to
C:\Windows\system32\TieringEngineService.exe. At this point, the Cloud Files Infrastructure runsTieringEngineService.exeasSYSTEM. Game over.@wdormann so basically a "#cloud-based #utilman-style "privilegue escalation"?
https://www.youtube.com/watch?v=X_9OuDjl97M -
@wdormann so basically a "#cloud-based #utilman-style "privilegue escalation"?
https://www.youtube.com/watch?v=X_9OuDjl97M@wdormann I can't wait for this to get #BadUSB'd like #PoisonTap!
- YouTube
Auf YouTube findest du die angesagtesten Videos und Tracks. Außerdem kannst du eigene Inhalte hochladen und mit Freunden oder gleich der ganzen Welt teilen.

(www.youtube.com)
-
@wdormann I can't wait for this to get #BadUSB'd like #PoisonTap!
- YouTube
Auf YouTube findest du die angesagtesten Videos und Tracks. Außerdem kannst du eigene Inhalte hochladen und mit Freunden oder gleich der ganzen Welt teilen.

(www.youtube.com)
-
 M mttaggart@infosec.exchange shared this topic
M mttaggart@infosec.exchange shared this topic
-
@astraleureka
Yes it uses both.@wdormann Just finished reading through the source, thank you. Much simpler than the first version, and makes the root issue a lot more clear. This is pretty nasty, MS has some serious egg on their faces over this one
-
From the same author as BlueHammer we now have RedSun.
This works 100% reliably to go from unprivileged user to
SYSTEMagainst Windows 11 and Windows Server with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled.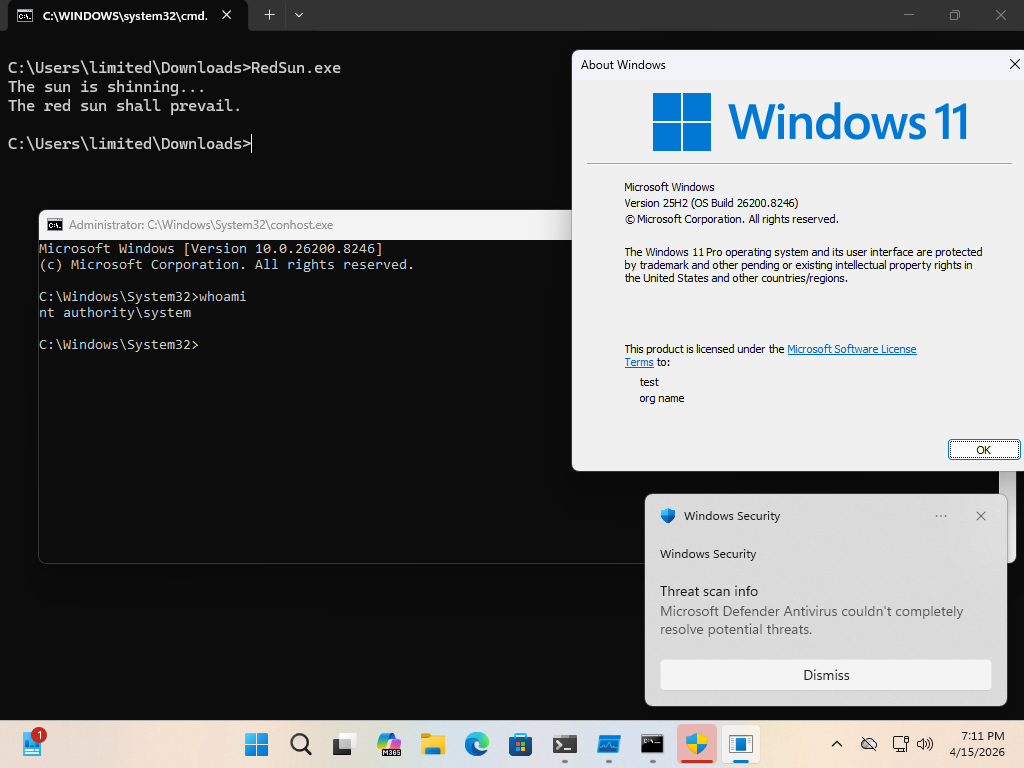
-
From the same author as BlueHammer we now have RedSun.
This works 100% reliably to go from unprivileged user to
SYSTEMagainst Windows 11 and Windows Server with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled.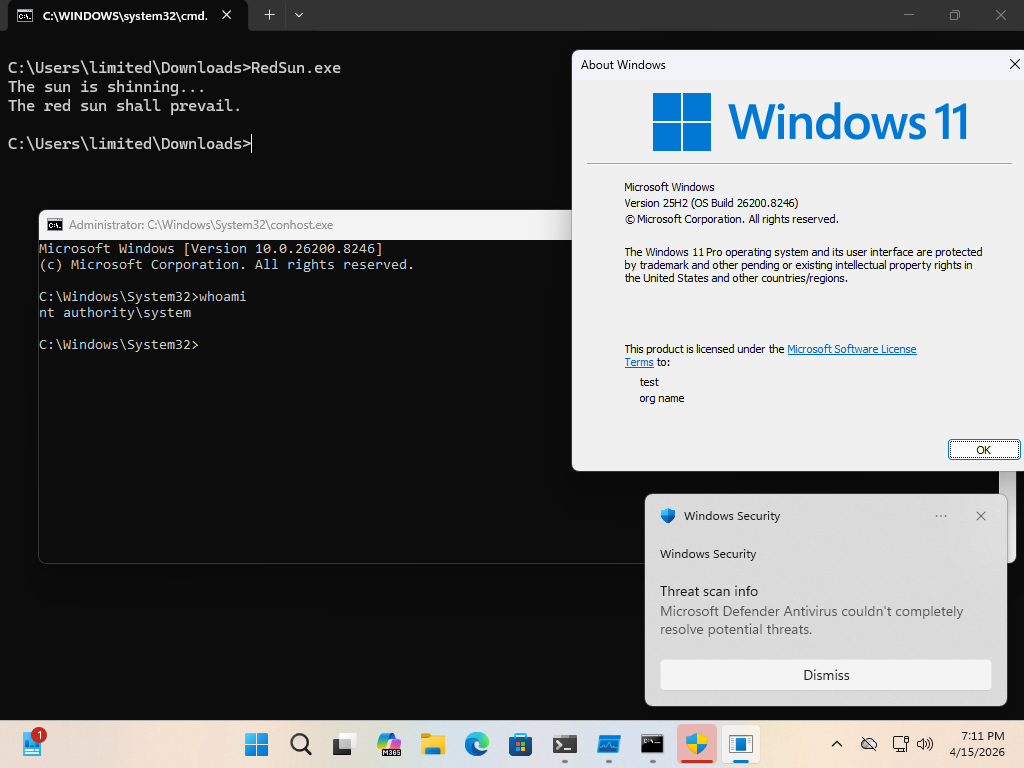
@wdormann Hey, just so I can learn this: How do I compile RedSun.cpp under Win32 with VS or gcc? I can't seem to include cfapi.h correctly (I have the full win32 sdk under the default location).
-
@wdormann Hey, just so I can learn this: How do I compile RedSun.cpp under Win32 with VS or gcc? I can't seem to include cfapi.h correctly (I have the full win32 sdk under the default location).
@christopherkunz
TBH, for code that doesn't include a.SLNfile, I usually have minimal luck compiling it straight-up withcl.exeIn this case, I simply made a new Visual Studio 2022 project for a console app, and then replaced the .CPP file contents with what's in the GitHub repo. There are a slew of warnings, but it compiles.
<snip>
1>C:\Users\test\source\repos\test\test\test.cpp(431,11): warning C4267: 'initializing': conversion from 'size_t' to 'int', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(694,49): warning C4267: '=': conversion from 'size_t' to 'ULONG', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(696,92): warning C4267: 'argument': conversion from 'size_t' to 'ULONG', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(714,20): warning C4267: 'initializing': conversion from 'size_t' to 'DWORD', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(736,57): warning C4838: conversion from 'LONG' to 'DWORD' requires a narrowing conversion
1>Generating code
1>Previous IPDB not found, fall back to full compilation.
1>All 27 functions were compiled because no usable IPDB/IOBJ from previous compilation was found.
1>Finished generating code
1>test.vcxproj -> C:\Users\test\source\repos\test\x64\Release\test.exe
1>Done building project "test.vcxproj".
========== Build: 1 succeeded, 0 failed, 0 up-to-date, 0 skipped ==========
========== Build completed at 8:43 AM and took 01.818 seconds ========== -
@christopherkunz
TBH, for code that doesn't include a.SLNfile, I usually have minimal luck compiling it straight-up withcl.exeIn this case, I simply made a new Visual Studio 2022 project for a console app, and then replaced the .CPP file contents with what's in the GitHub repo. There are a slew of warnings, but it compiles.
<snip>
1>C:\Users\test\source\repos\test\test\test.cpp(431,11): warning C4267: 'initializing': conversion from 'size_t' to 'int', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(694,49): warning C4267: '=': conversion from 'size_t' to 'ULONG', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(696,92): warning C4267: 'argument': conversion from 'size_t' to 'ULONG', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(714,20): warning C4267: 'initializing': conversion from 'size_t' to 'DWORD', possible loss of data
1>C:\Users\test\source\repos\test\test\test.cpp(736,57): warning C4838: conversion from 'LONG' to 'DWORD' requires a narrowing conversion
1>Generating code
1>Previous IPDB not found, fall back to full compilation.
1>All 27 functions were compiled because no usable IPDB/IOBJ from previous compilation was found.
1>Finished generating code
1>test.vcxproj -> C:\Users\test\source\repos\test\x64\Release\test.exe
1>Done building project "test.vcxproj".
========== Build: 1 succeeded, 0 failed, 0 up-to-date, 0 skipped ==========
========== Build completed at 8:43 AM and took 01.818 seconds ==========@wdormann Yeah, this worked fine. As did the exploit. Thanks for your help! (And for anyone else reading this, the keyboard shortcut to "just compile, don't run" is ctrl-shift-b)
-
From the same author as BlueHammer we now have RedSun.
This works 100% reliably to go from unprivileged user to
SYSTEMagainst Windows 11 and Windows Server with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled.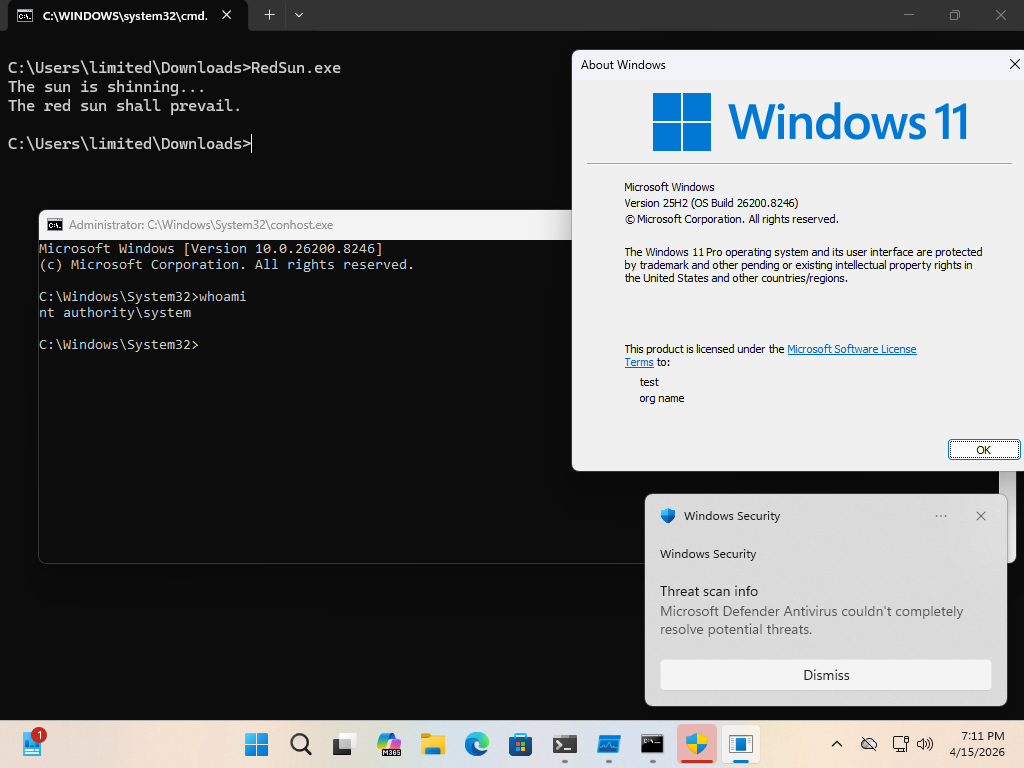
@wdormann Thank you. Blocking cldapi.dll using AppLocker works though that will break OneDrive and stuff like that.
-
@wdormann Thank you. Blocking cldapi.dll using AppLocker works though that will break OneDrive and stuff like that.
@qdkp
People don't use OneDrive intentionally, do they?
-
@qdkp
People don't use OneDrive intentionally, do they?
-
From the GitHub repo:
When Windows Defender realizes that a malicious file has a cloud tag, for whatever stupid and hilarious reason, the antivirus that's supposed to protect decides that it is a good idea to just rewrite the file it found again to it's original location.
This Exploit uses the "Cloud Files API", writes EICAR to a file using it, uses an oplock to win a volume shadow copy race, and uses a directory junction/reparse point to redirect the file rewrite (with new contents) to
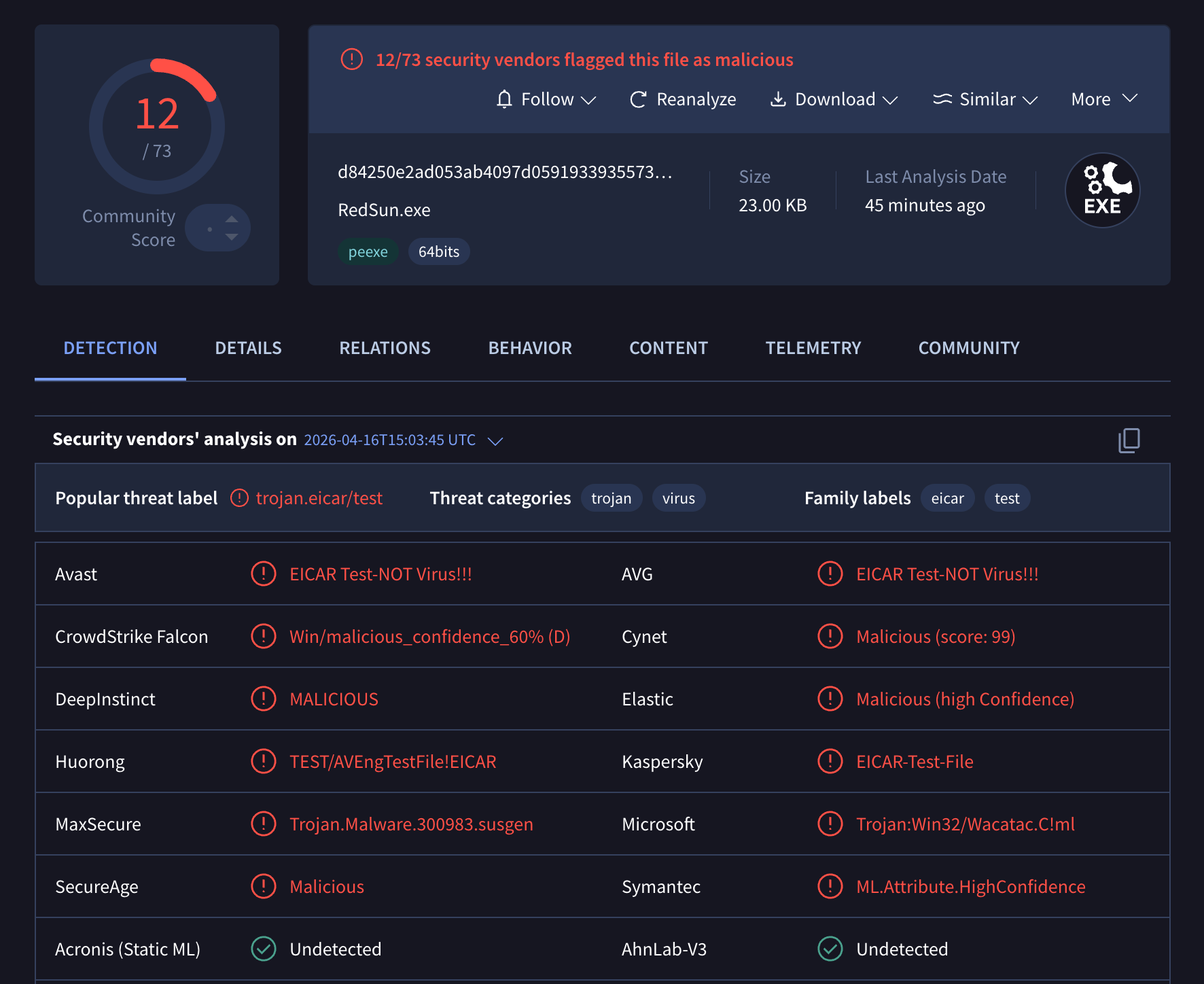
C:\Windows\system32\TieringEngineService.exe. At this point, the Cloud Files Infrastructure runsTieringEngineService.exeasSYSTEM. Game over.Interestingly, a good chunk of the [(12/73) AV detections on VT](https://www.virustotal.com/gui/file/d84250e2ad053ab4097d0591933935573e4cab3e975360004a126abc102dc6f6 for this
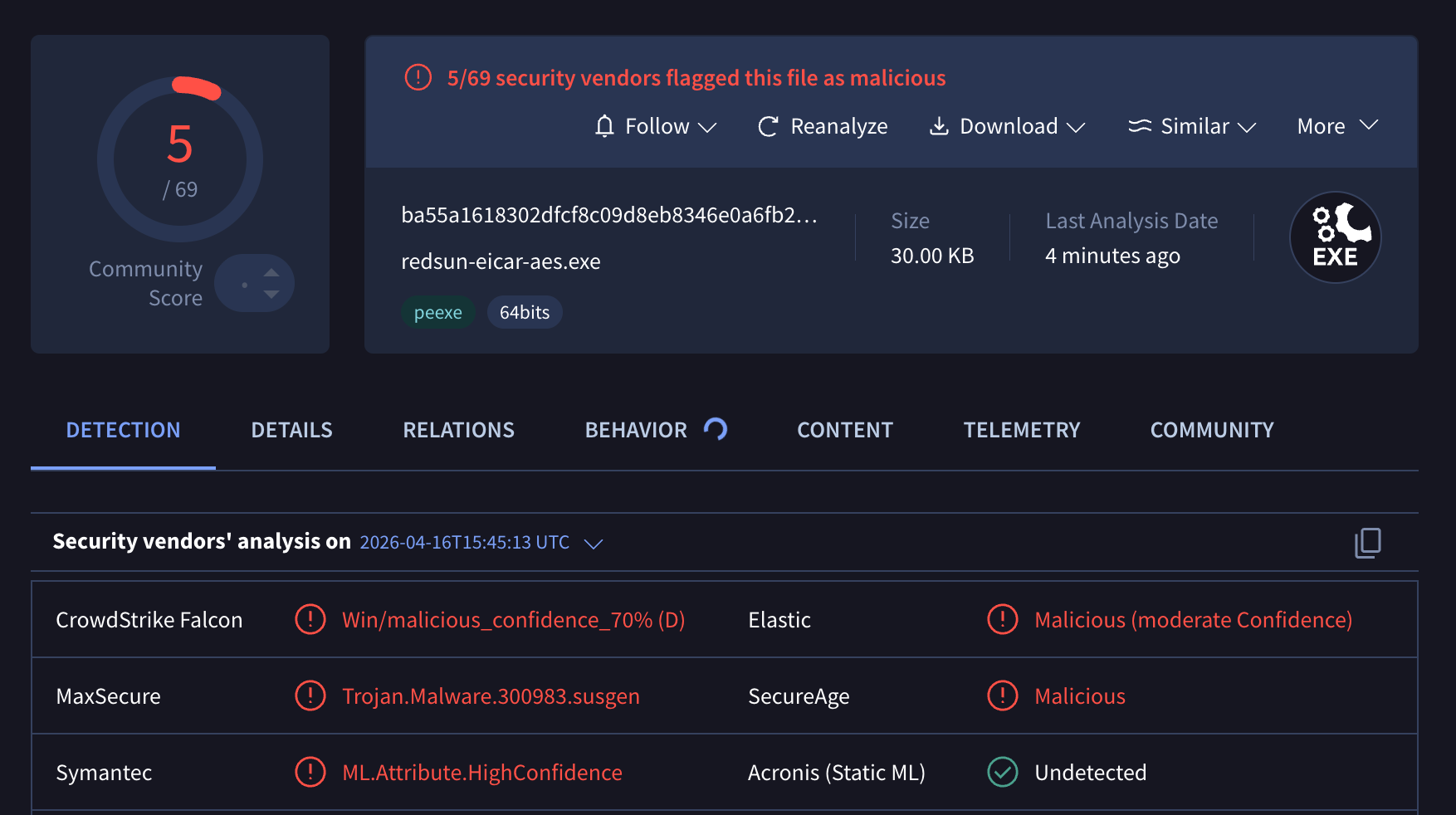
RedSun.exeexploit are due to theEICARpart being detected, despite the string being reversed in the code. (note: this reversal apparently does nothing to prevent EICAR detection in the AV engines on VT)If we make the EICAR string less obvious (encrypted), the detections drop to 5.
Defender currently doesn't detect the exploit in either case.
-
R relay@relay.infosec.exchange shared this topic