DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
-
DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
Me: Thanks! Are your distro repos updated to contain the patched version?
DO: lol no
[Edit: to be fair, this is Debian's fault, not DOs (see screenshot). At least DO told me!]
[Edit 2: that specific vuln was quietly fixed on Debian specifically well before this version?? Would be advisable for them to have said that now?
https://infosec.exchange/@tychotithonus/116527548611779862 ]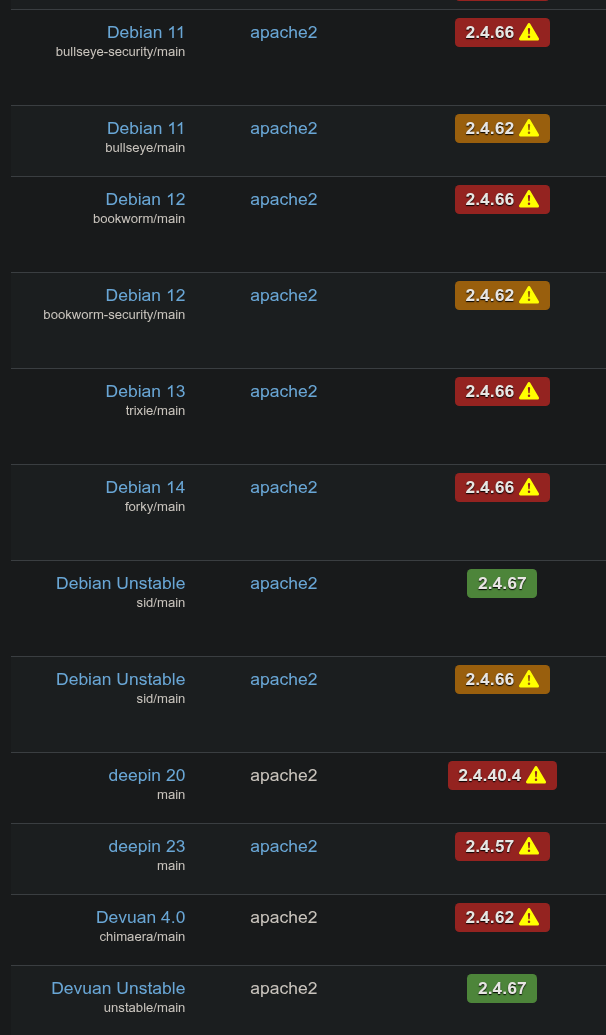
@tychotithonus edge first? Lol
-
DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
Me: Thanks! Are your distro repos updated to contain the patched version?
DO: lol no
[Edit: to be fair, this is Debian's fault, not DOs (see screenshot). At least DO told me!]
[Edit 2: that specific vuln was quietly fixed on Debian specifically well before this version?? Would be advisable for them to have said that now?
https://infosec.exchange/@tychotithonus/116527548611779862 ]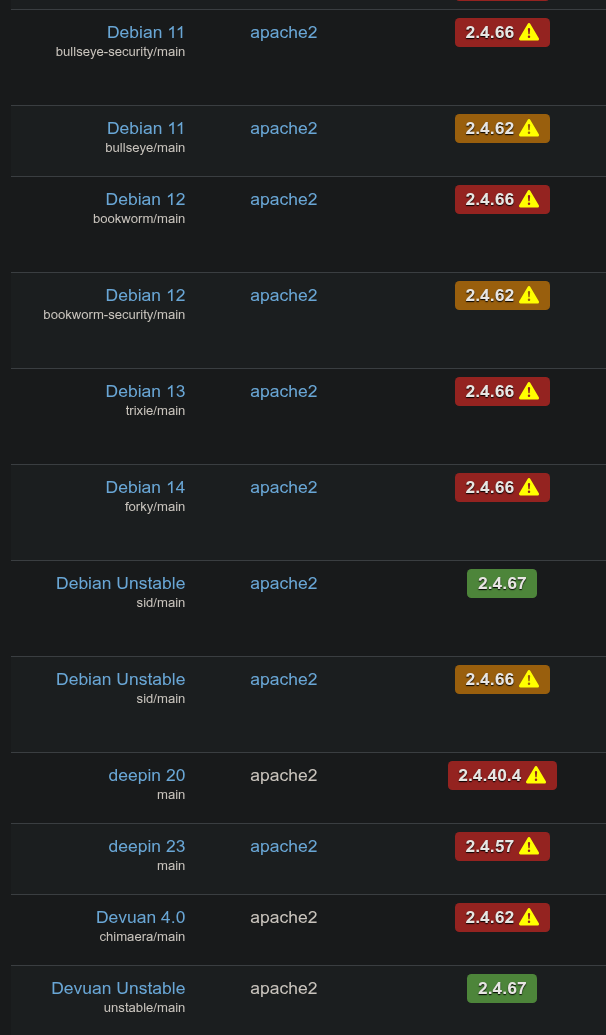
@tychotithonus make sure you have (old)stable-proposed-updates enabled, it's going in that way rather than through stable-security.
-
@tychotithonus make sure you have (old)stable-proposed-updates enabled, it's going in that way rather than through stable-security.
@tychotithonus (Wasn't my decision, but I'm guessing they're a bit twitchy about .67 since the last "bugfix" apache release had a pretty serious regression: https://tracker.debian.org/news/1725501/accepted-apache2-2466-1deb13u2-source-into-proposed-updates/ )
-
@tychotithonus (Wasn't my decision, but I'm guessing they're a bit twitchy about .67 since the last "bugfix" apache release had a pretty serious regression: https://tracker.debian.org/news/1725501/accepted-apache2-2466-1deb13u2-source-into-proposed-updates/ )
@Andres4NY Ah, thanks - I was just going to start asking!
-
DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
Me: Thanks! Are your distro repos updated to contain the patched version?
DO: lol no
[Edit: to be fair, this is Debian's fault, not DOs (see screenshot). At least DO told me!]
[Edit 2: that specific vuln was quietly fixed on Debian specifically well before this version?? Would be advisable for them to have said that now?
https://infosec.exchange/@tychotithonus/116527548611779862 ]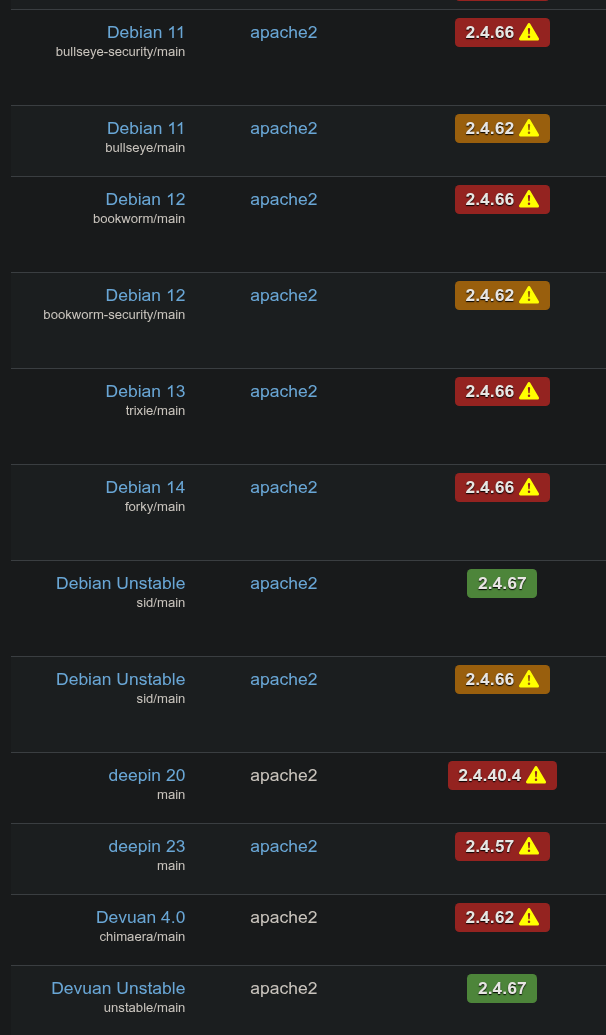
@tychotithonus I just love the Debian security tracker, they manage the flood so good https://security-tracker.debian.org/tracker/CVE-2026-23918
-
DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
Me: Thanks! Are your distro repos updated to contain the patched version?
DO: lol no
[Edit: to be fair, this is Debian's fault, not DOs (see screenshot). At least DO told me!]
[Edit 2: that specific vuln was quietly fixed on Debian specifically well before this version?? Would be advisable for them to have said that now?
https://infosec.exchange/@tychotithonus/116527548611779862 ]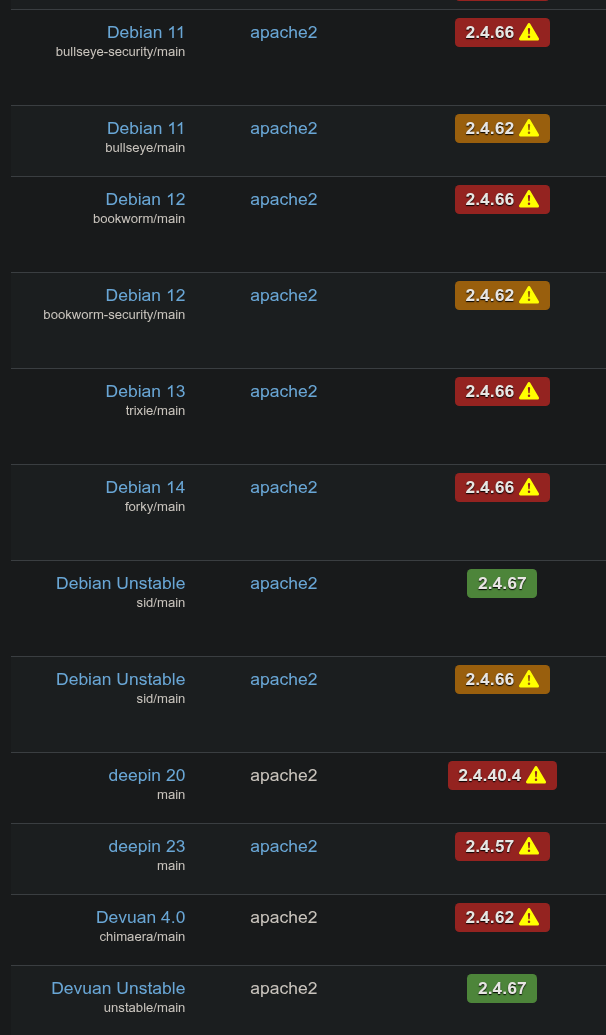
@tychotithonus yeah, that thing.
To my knowledge, the debian 2.4.66 packages already contain the fix. Which they could not link to the CVE as that was not available at the time.
"Responsible disclosure" strikes again.
-
@Andres4NY Ah, thanks - I was just going to start asking!
@Andres4NY Parent post updated, apparently CVE-2026-23918 was fixed much earlier?
-
@Andres4NY Parent post updated, apparently CVE-2026-23918 was fixed much earlier?
@tychotithonus either way:
"Unpacking apache2 (2.4.67-1~deb12u1) over (2.4.66-1~deb12u2) ..."
-
DigitalOcean: Hey that Apache vuln thing needs upgrade on your droplet.
Me: Thanks! Are your distro repos updated to contain the patched version?
DO: lol no
[Edit: to be fair, this is Debian's fault, not DOs (see screenshot). At least DO told me!]
[Edit 2: that specific vuln was quietly fixed on Debian specifically well before this version?? Would be advisable for them to have said that now?
https://infosec.exchange/@tychotithonus/116527548611779862 ]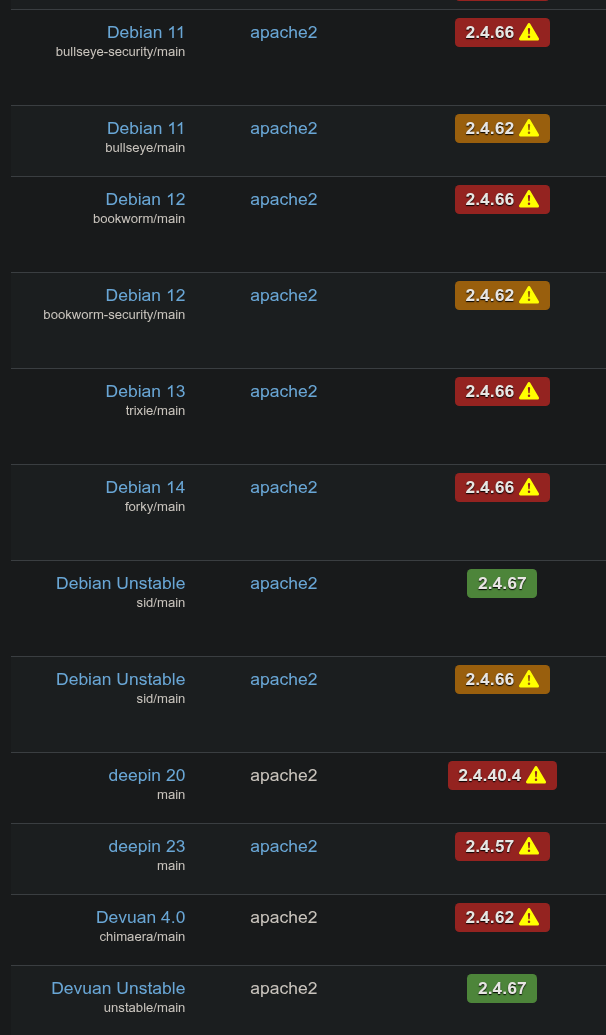
@tychotithonus do you happen to have a link to the info about Debian's .66 already having a fix for this issue?
-
@tychotithonus do you happen to have a link to the info about Debian's .66 already having a fix for this issue?
@gnomon it's in the blog post. Eissing shows the timeline
-
R relay@relay.infosec.exchange shared this topic
