https://krypt3ia.wordpress.com/2026/05/13/cyber-supply-chain-attacks-early-internet-to-today/ thing done.
-
@krypt3ia I know you can't include every incident in the post but the Linux Mint one was another good one. Changing the hash on the website was such a nice touch.
-
R relay@relay.infosec.exchange shared this topic
-
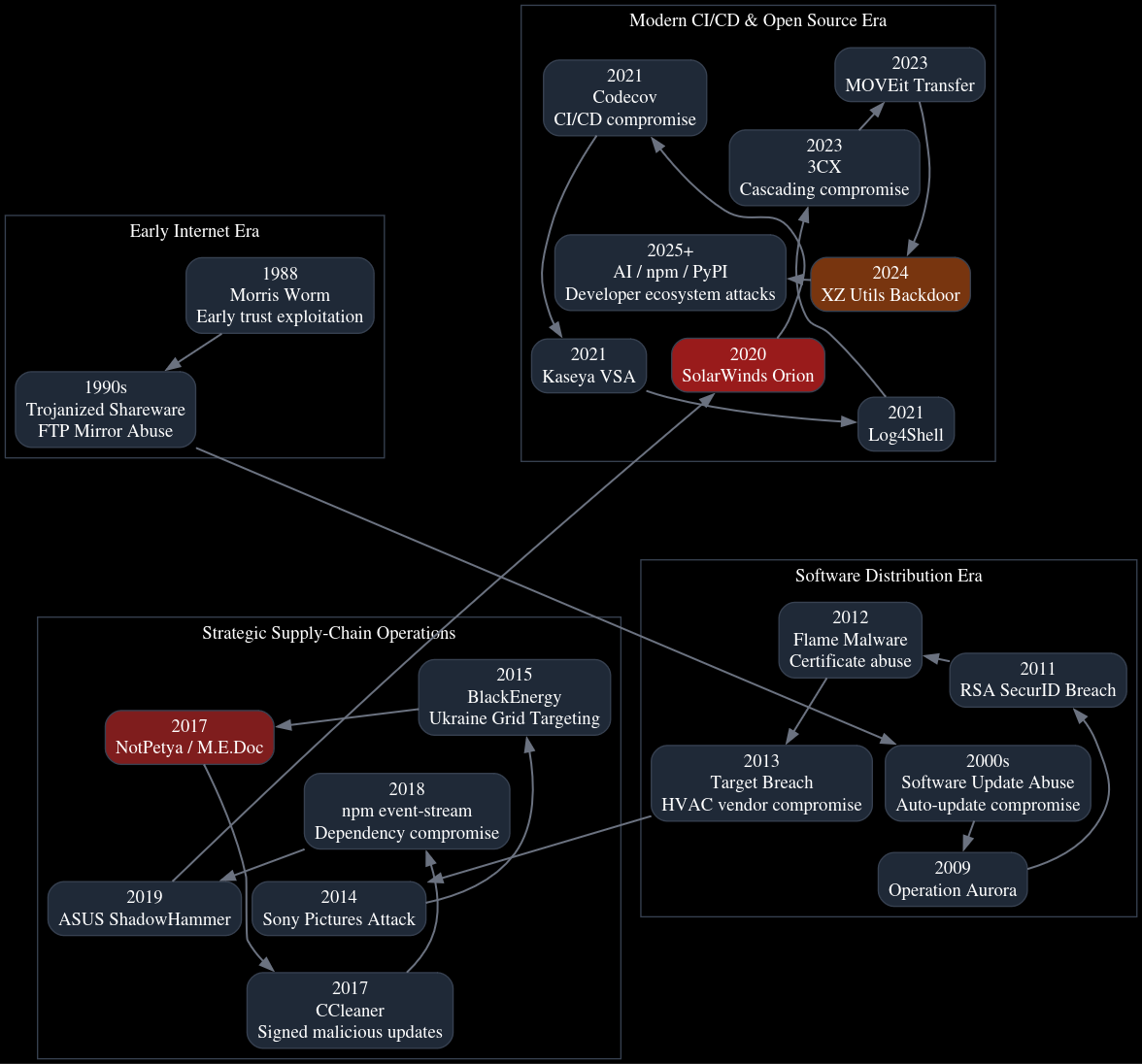
@krypt3ia Great writeup! The visual chart with attacks grouped based on generation/method is also very interesting. Do the colors in the chart (red/orange/grey) represent something? Also, are the arrows in the chart to indicate the chronological order of various attacks -- or do they have some other meaning?
-
@krypt3ia I know you can't include every incident in the post but the Linux Mint one was another good one. Changing the hash on the website was such a nice touch.
-
-
@cR0w @krypt3ia Here's a refresher on #Havex
https://netresec.com/?b=14ABDA4 -
@krypt3ia Great writeup! The visual chart with attacks grouped based on generation/method is also very interesting. Do the colors in the chart (red/orange/grey) represent something? Also, are the arrows in the chart to indicate the chronological order of various attacks -- or do they have some other meaning?
@netresec Chronological and colors, just pretty.