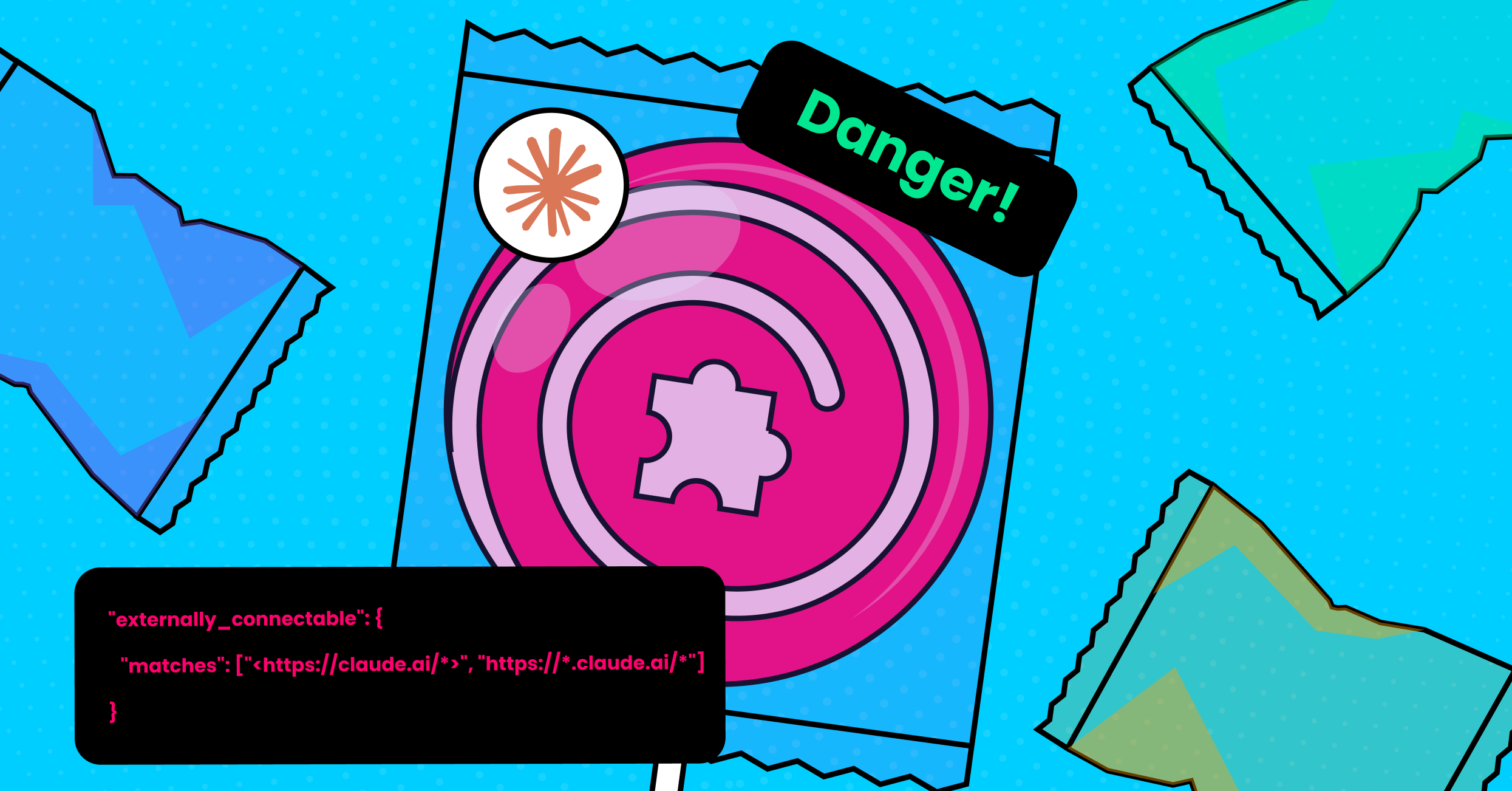
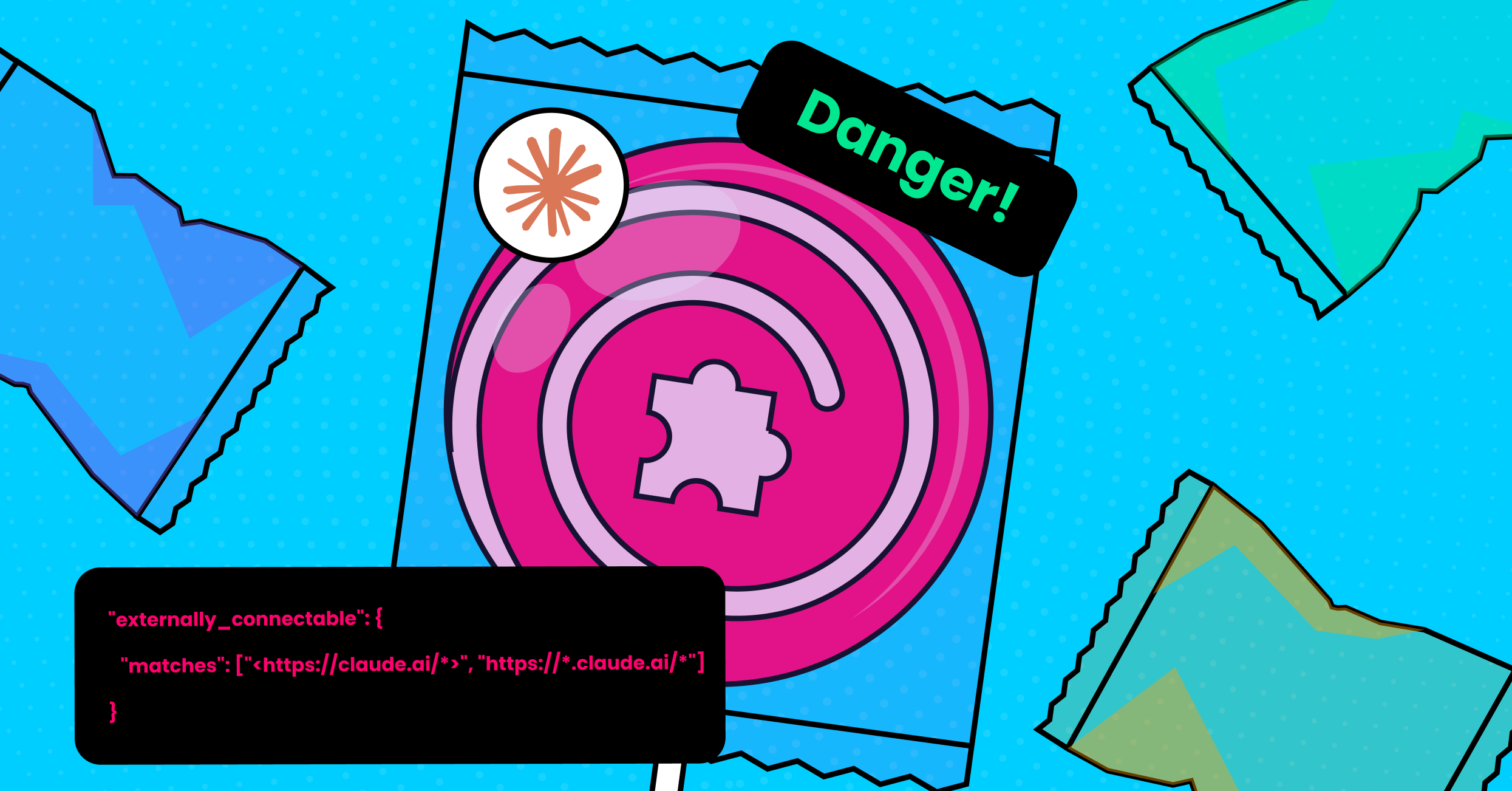
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it?
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
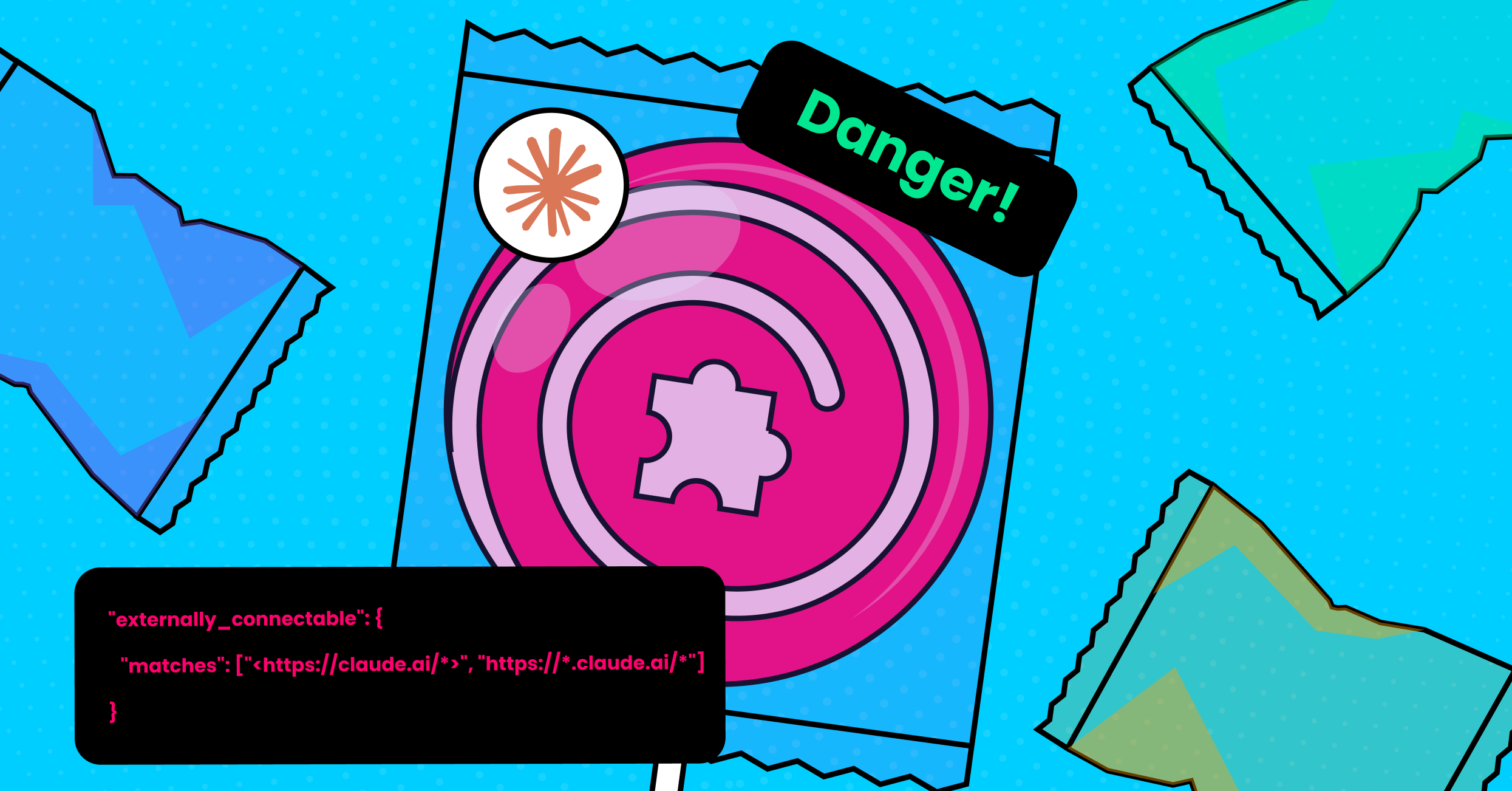
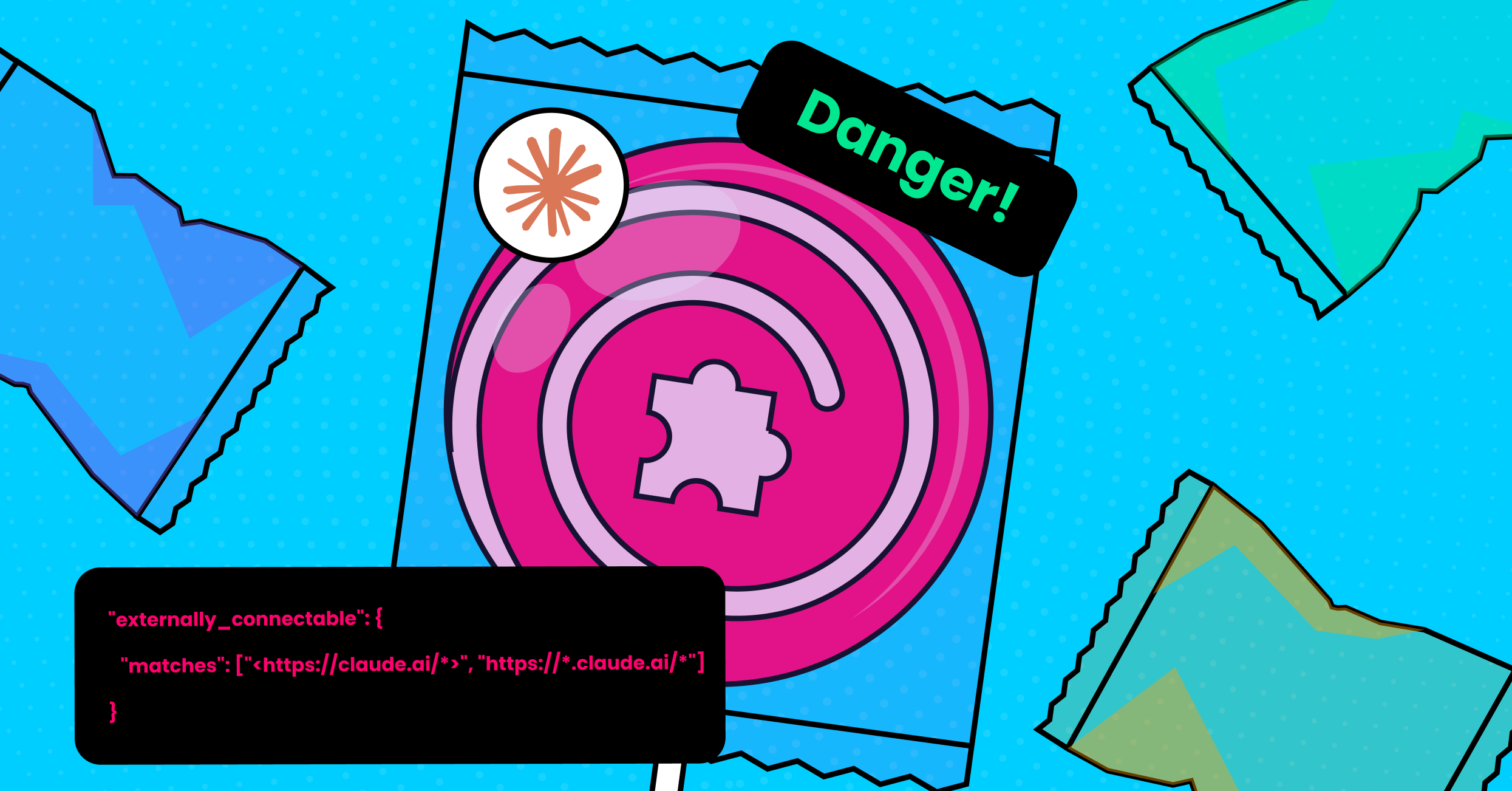
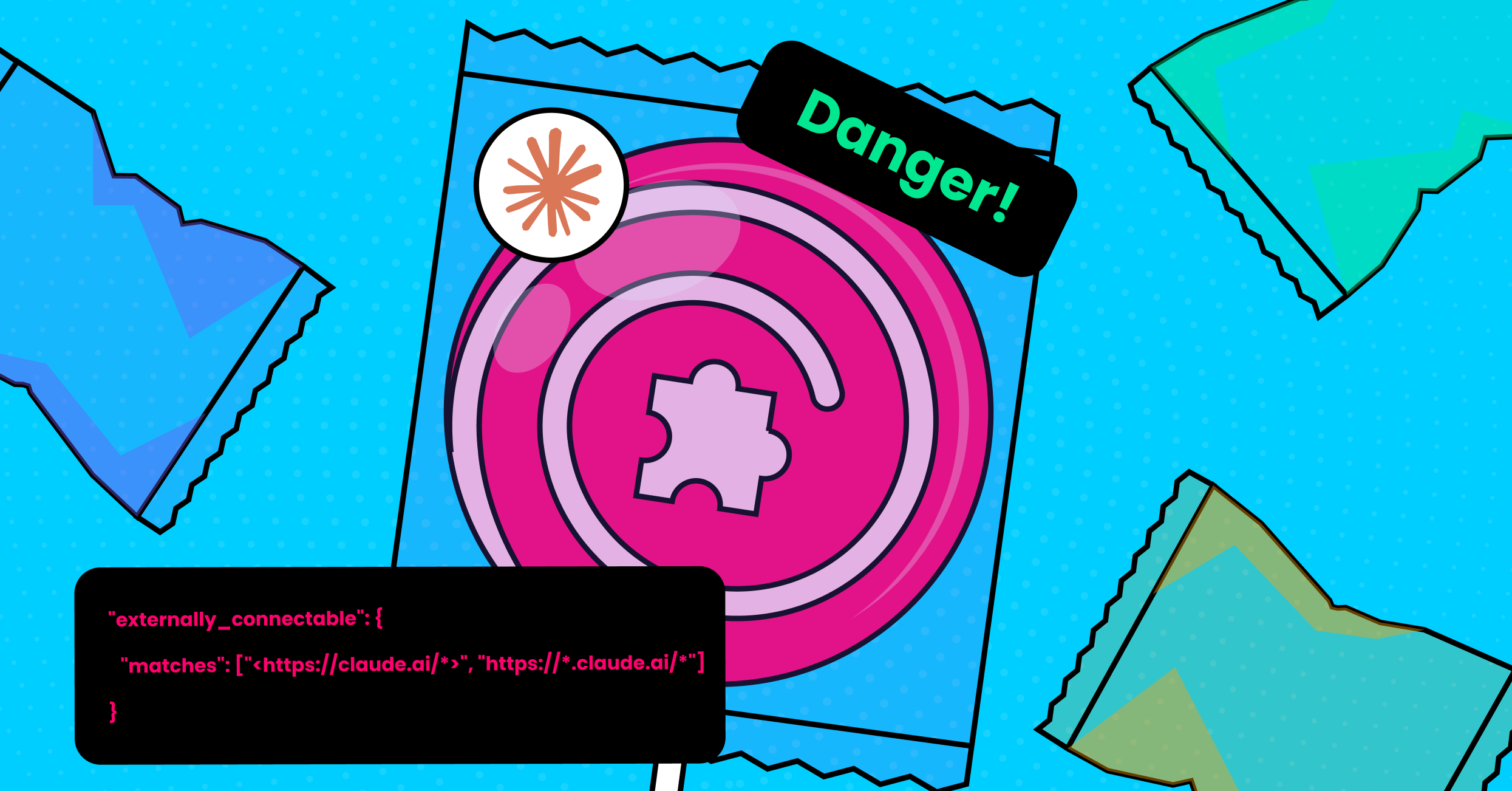
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
2001: I'm afraid I can't do that...
2026: I'm afraid I *can* do that!
"AI"... Service with a smile!
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart @briankrebs Mythos really missed this one, eh?
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart
this calls for the claude emoji:
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart An "AI tool" is vibe coded insecure slop? Who would've thunk

(btw #opencode is insecure crap, too, yet it has a scary amount of users)
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart yikes, extension permissions are such a mess. the name ClaudeBleed is dramatic but the issue is real
-
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart
They can't have vulnerabilities they have mYtHoS -
 E evacide@hachyderm.io shared this topic
R relay@relay.infosec.exchange shared this topic
E evacide@hachyderm.io shared this topic
R relay@relay.infosec.exchange shared this topic -
So the Claude extension allows any other extension to inject JavaScript into claude.ai and run it? Cool cool cool.
Yeah, don't let this one in.
ClaudeBleed: A Flaw In Claude's Browser Extension Allows Any Extension to Hijack It - LayerX
Executive Summary LayerX security researchers have discovered a flaw with Claude’s Chrome extension (“Claude in Chrome”) that allows any extension, even one with no special permissions at all, to effectively hijack Claude’s extension by injecting it with malicious instructions, extract any information that the attacker desires, and get Claude to perform active agentic actions on […]
LayerX (layerxsecurity.com)
@mttaggart Wait, so any extension with zero permission can execute XSS code on any origin? Injecting prompts to claude is the least of my worries then. With that, can't the same extension just steal your github credentials?
-
@mttaggart Wait, so any extension with zero permission can execute XSS code on any origin? Injecting prompts to claude is the least of my worries then. With that, can't the same extension just steal your github credentials?
@mttaggart I looked a bit into it - apparently, Chrome does not require specific permissions beyond agreeing to install the extension, to inject content into the MAIN context of a page.
So, it looks like all of the demonstrated things (stealing emails, exfiltrating repos, etc.) could be done with just a malicious extension, completely skipping the claude step.
The only benefit it gives the attacker is that they can just tell claude what to do for them, instead of having to write (or vibecode) an actual exploit script.So, for the demonstrated exploits, the claude extension doesn't really seem to add any new capabilities beyond what an installed extension can do anyways.
-
@mttaggart I looked a bit into it - apparently, Chrome does not require specific permissions beyond agreeing to install the extension, to inject content into the MAIN context of a page.
So, it looks like all of the demonstrated things (stealing emails, exfiltrating repos, etc.) could be done with just a malicious extension, completely skipping the claude step.
The only benefit it gives the attacker is that they can just tell claude what to do for them, instead of having to write (or vibecode) an actual exploit script.So, for the demonstrated exploits, the claude extension doesn't really seem to add any new capabilities beyond what an installed extension can do anyways.
This post is deleted! -
@mttaggart I looked a bit into it - apparently, Chrome does not require specific permissions beyond agreeing to install the extension, to inject content into the MAIN context of a page.
So, it looks like all of the demonstrated things (stealing emails, exfiltrating repos, etc.) could be done with just a malicious extension, completely skipping the claude step.
The only benefit it gives the attacker is that they can just tell claude what to do for them, instead of having to write (or vibecode) an actual exploit script.So, for the demonstrated exploits, the claude extension doesn't really seem to add any new capabilities beyond what an installed extension can do anyways.
@hweissi The issue here is the security boundary of
externally_connectedbeing broken because of the nature of the extension.Any extension can request the
scriptingpermission to inject JavaScript; that is true. Extensions are a huge security issue, but that's not the full story here.When an extension does so on
claude.ai, the Claude extension'sexternally_connectablemanifest values allow that malicious script to send messages to the Claude extension itself, without explicitly requesting theruntimepermission usually required for message sending. As a result, the injected code can't just watch the DOM—which again, yes, is a thing all extensions can do—, it can send messages to Claude via the extension, gaining access to Claude itself and the data stored therein.Interestingly, it would seem the "fix" from Anthropic to add additional approvals for certain actions is also bypassable.
-
@hweissi The issue here is the security boundary of
externally_connectedbeing broken because of the nature of the extension.Any extension can request the
scriptingpermission to inject JavaScript; that is true. Extensions are a huge security issue, but that's not the full story here.When an extension does so on
claude.ai, the Claude extension'sexternally_connectablemanifest values allow that malicious script to send messages to the Claude extension itself, without explicitly requesting theruntimepermission usually required for message sending. As a result, the injected code can't just watch the DOM—which again, yes, is a thing all extensions can do—, it can send messages to Claude via the extension, gaining access to Claude itself and the data stored therein.Interestingly, it would seem the "fix" from Anthropic to add additional approvals for certain actions is also bypassable.
@mttaggart So does that mean you can essentially get local code execution by communicating with a locally-running claude instance? That would be a bigger issue.
If it's only Claude in the browser, performing clicks for you - i don't think there's a lot of extra capabilities you get, compared to what you have already when you get someone to install the extension.
After all, why communicate with a different browser extension, when you already have a browser extension running?However, still not great sandboxing by anthropic obviously.
