It is nice to see getting Linux more secure every day because it is developed in the open.
-
It is nice to see getting Linux more secure every day because it is developed in the open. Just to remind any (AI) security researchers that the real reason for that was collaboration and helping each other. What happens now with Mythos & Co reminds me more of a person getting raped and then victem-blamed because they where wearing a mini-skirt.
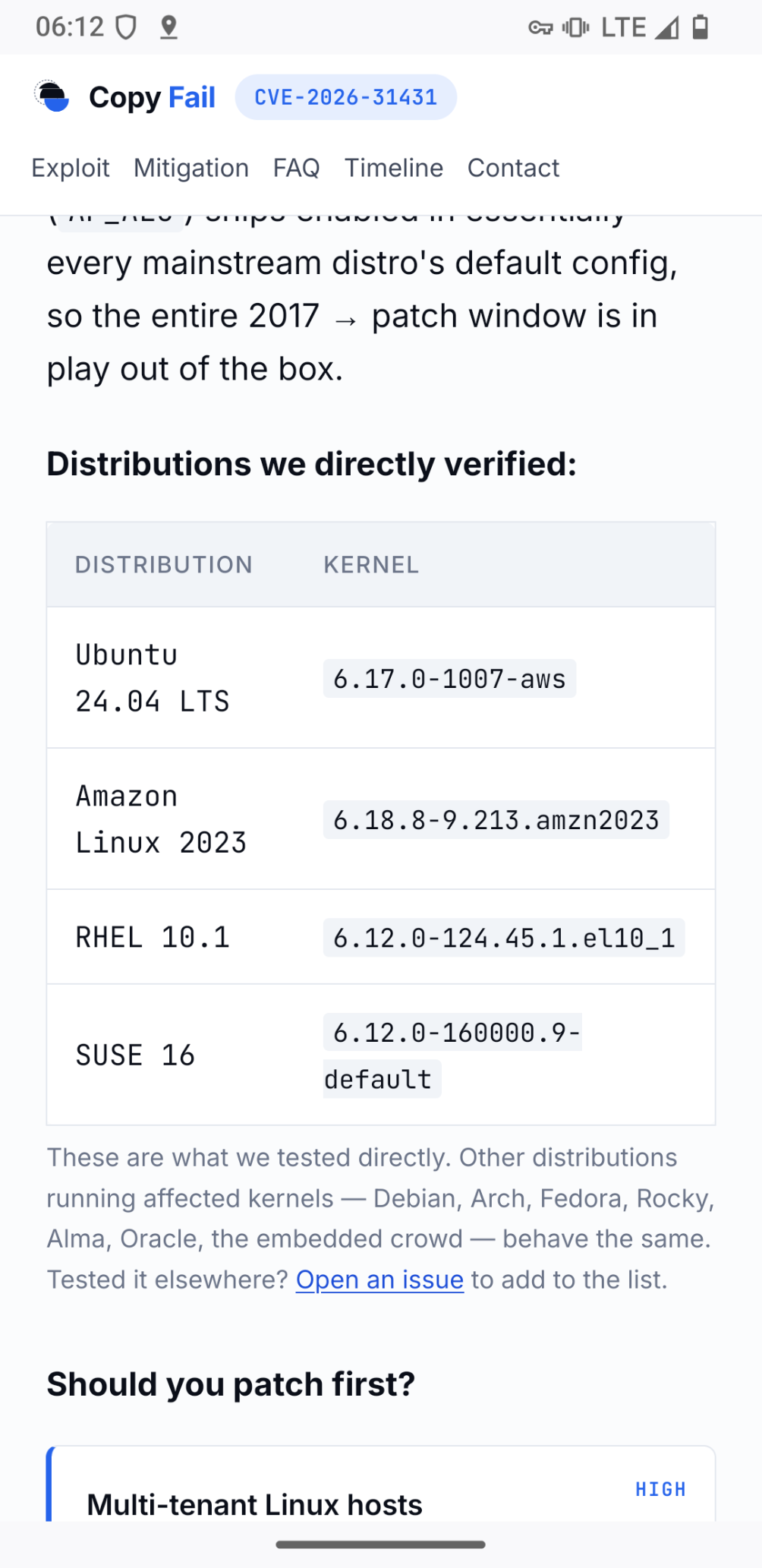
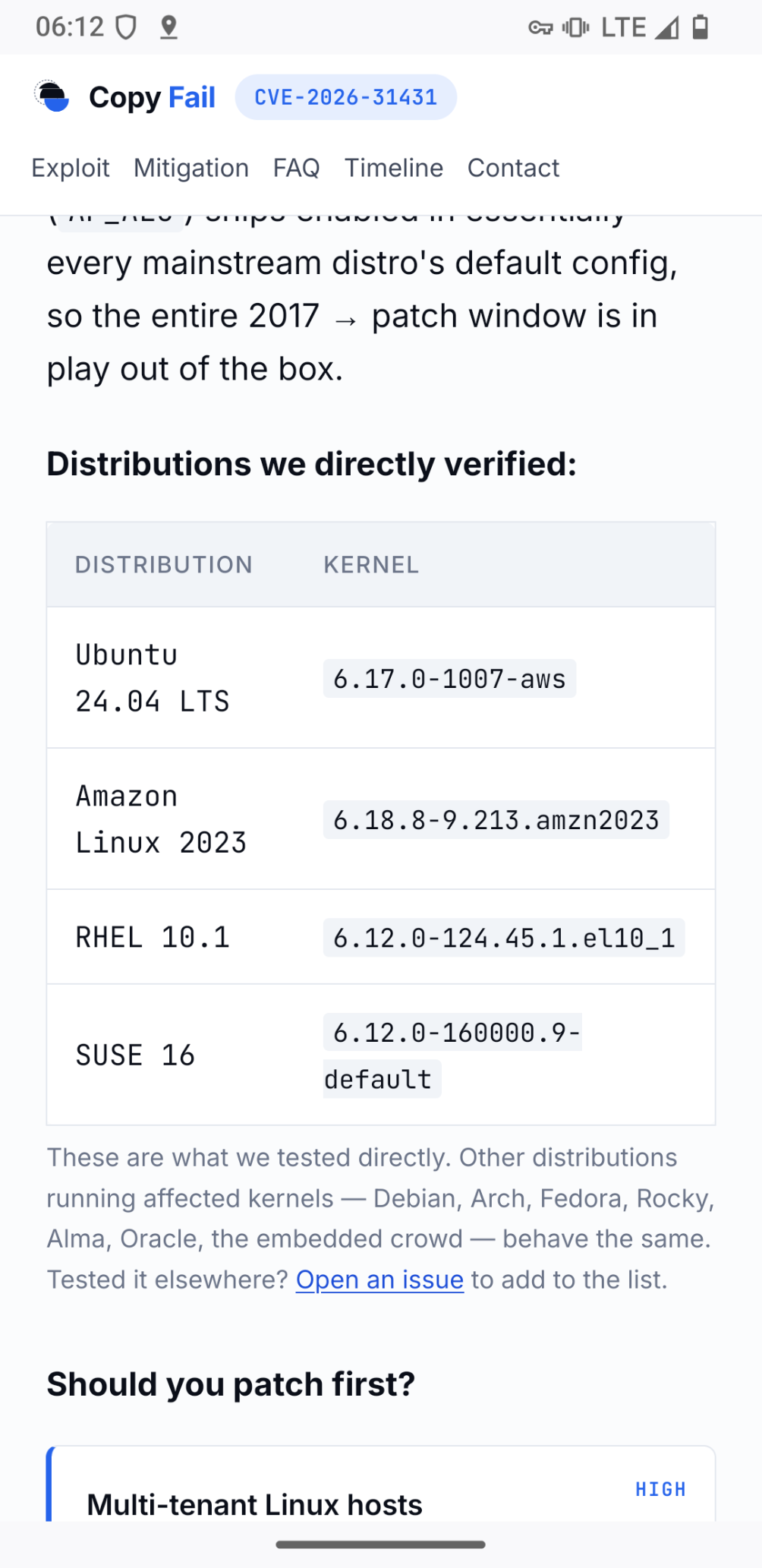
In the case of copyfail the researchers do not even give a f@%k about community and have verified only paid distributions.
-
It is nice to see getting Linux more secure every day because it is developed in the open. Just to remind any (AI) security researchers that the real reason for that was collaboration and helping each other. What happens now with Mythos & Co reminds me more of a person getting raped and then victem-blamed because they where wearing a mini-skirt.
In the case of copyfail the researchers do not even give a f@%k about community and have verified only paid distributions.
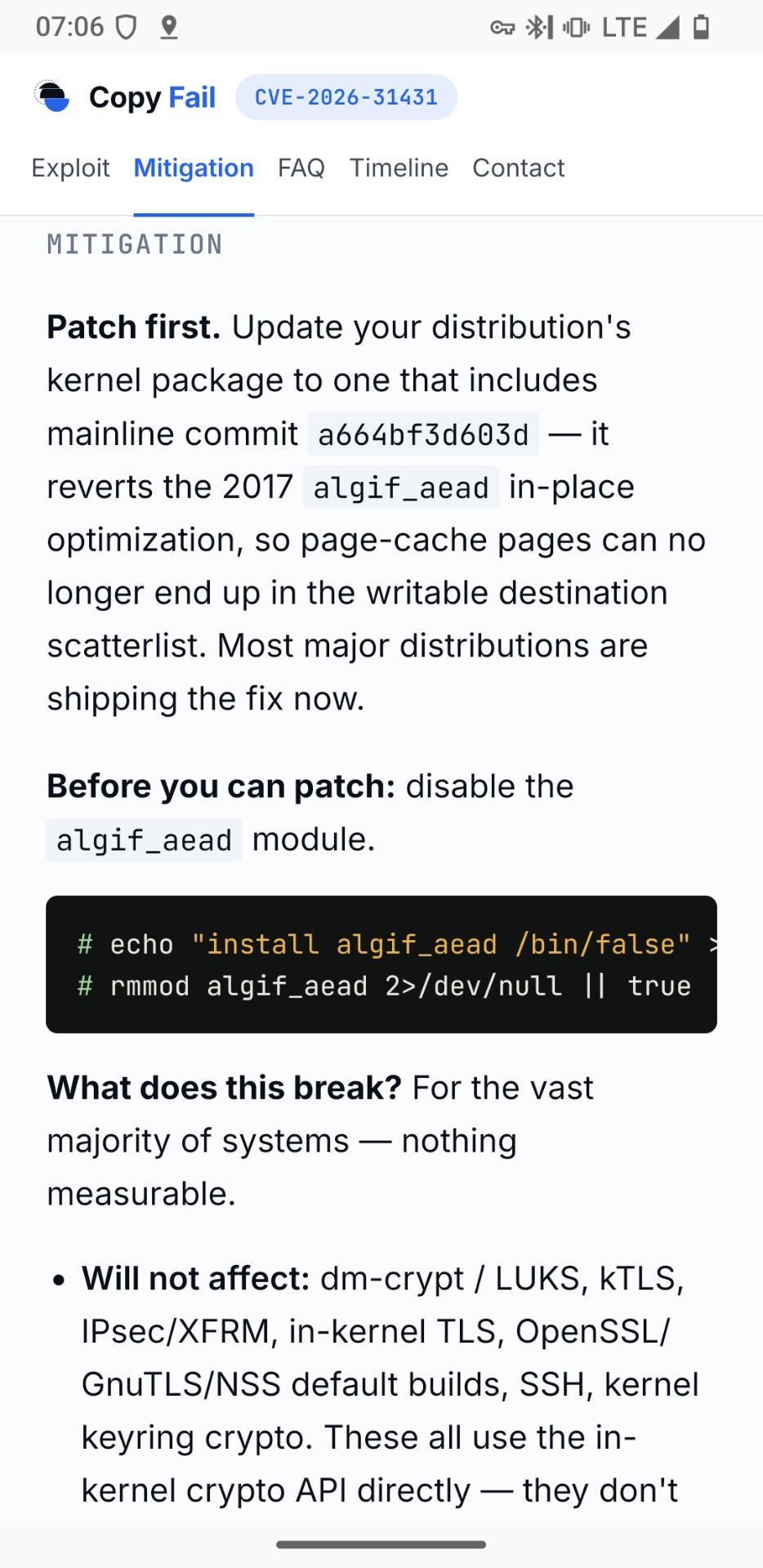
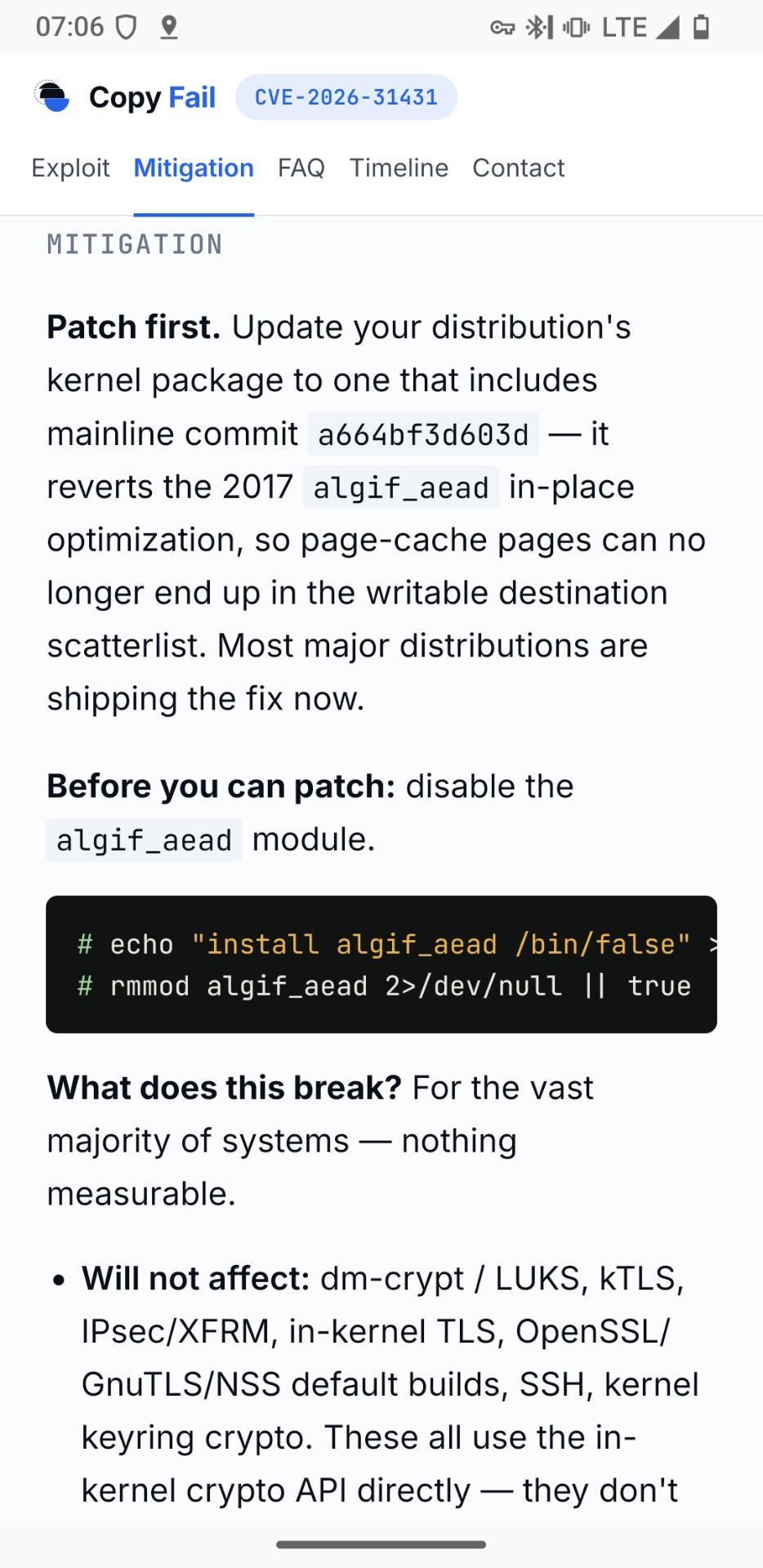
It sadly sucks on so many levels. It is one of the worst releases I have seen so far. Even the informieren on how to mitigate the issue is unclear. Probably AI generated as well. What now? 'Patch now' or 'Before you can patch'? And no, I will not run your exploit code on my machine.
-
It is nice to see getting Linux more secure every day because it is developed in the open. Just to remind any (AI) security researchers that the real reason for that was collaboration and helping each other. What happens now with Mythos & Co reminds me more of a person getting raped and then victem-blamed because they where wearing a mini-skirt.
In the case of copyfail the researchers do not even give a f@%k about community and have verified only paid distributions.
@Lioh They reported the bug to the Linux kernel security team over a month ago. A CVE was issued. I don’t know where the ball was dropped but, AFAICT, not a single distro took it seriously enough to release a patch.
It’s not the bug reporter’s job to run a testing service for everyone (mostly large for-profit companies) downstream of the Linux kernel.
-
@Lioh They reported the bug to the Linux kernel security team over a month ago. A CVE was issued. I don’t know where the ball was dropped but, AFAICT, not a single distro took it seriously enough to release a patch.
It’s not the bug reporter’s job to run a testing service for everyone (mostly large for-profit companies) downstream of the Linux kernel.
@marshray you can paint ot how you want. I just think it's not nice at all.
-
@marshray you can paint ot how you want. I just think it's not nice at all.
@Lioh Reporting security vulnerabilities is a worse-than-thankless job.
-
@Lioh Reporting security vulnerabilities is a worse-than-thankless job.
@marshray really depends HOW one does it.
-
It sadly sucks on so many levels. It is one of the worst releases I have seen so far. Even the informieren on how to mitigate the issue is unclear. Probably AI generated as well. What now? 'Patch now' or 'Before you can patch'? And no, I will not run your exploit code on my machine.
@Lioh@social.anoxinon.de Danke für die Einordnung, hatte gestern Abend leider nicht mehr genug Zeit mir das genauer anzuschauen
-
@marshray really depends HOW one does it.
@Lioh OK, so what’s your preferred vulnerability disclosure policy?
Just linking the document is fine.
-
R relay@relay.infosec.exchange shared this topic
